The Oldest Trick in the Book is Still the Best Trick in the Book

Show original YouTube description
Show transcript [en]
because all right hello everyone my name is Chris Horner I am a cyber security engineer with a local consultancy triaxium security which we are now a part of strata information group and very happy about that today my talk is on the oldest trick in the book is still the best trick in the book and what is the oldest trick in the book it's social engineering so in this presentation we're going to cover three main things first we're going to look at the psychology behind social engineering why do even very smart people fall for social engineering then how we as cyber security practitioners create a professional test for our clients professional not a canned one not a generic one not just a
check box but something that can help our clients be able to prepare for and defend against social engineering attempts that in turn helps everybody at the company learn how to recognize and avoid these attacks even in their personal life so let's start by defining social engineering social engineering is using deception to manipulate a person into taking an action that they shouldn't or to reveal some kind of confidential information sometimes this is referred to as social hacking this is not a new attack Vector in fact it's oldest time we all heard the story about the Trojan Horse thousands of years ago so deceit and trickery have always been a part of The Human Experience unfortunately but it's only
been in the last couple of decades that this tactic has actually been given a name so while technology continues to improve and become new apps new technology Stacks are always coming out human psychology though is generally the same and people will tend to operate in the same way and in a predictable fashion and that is why social engineering is actually so dangerous these days technical controls as long as they're set up correctly are generally pretty good but why should an attacker go through all the trouble of identifying and defeating technology when all you have to do is get somebody to open the gates for you from the inside so the Verizon data breach report that
came out this year the latest one showed the 74 percent of attacks Incorporated some kind of social engineering element and this is a really interesting time to be giving this presentation and to have been polishing it off because if you've been paying attention to the news there was a very high profile hack at uh in Las Vegas and the details are still coming out as of this presentation but the group that is claiming responsibility for this attack said the social engineered uh the help desk by using a phone call and I will tell you as somebody who does social engineering campaigns that is a very credible possibility even with technical controls in place it is
possible to do that I know because I've done it so when you're looking at Social Engineering there are typically four kinds of attacks that could take place one is phishing emails texts and phone calls we're probably all familiar with those then there's pre-texting that's pretending to be somebody else to uncover secret information now phishing and pre-texting would take up the majority of attacks that you see and hear about then there's baiting that's exploiting somebody's curiosity that could be dropping USB drives around the building for example hoping somebody picks someone up and plugs it into the computer to see what's on it just out of curiosity or the promise to reveal something secret to somebody and then finally quid pro quo that is
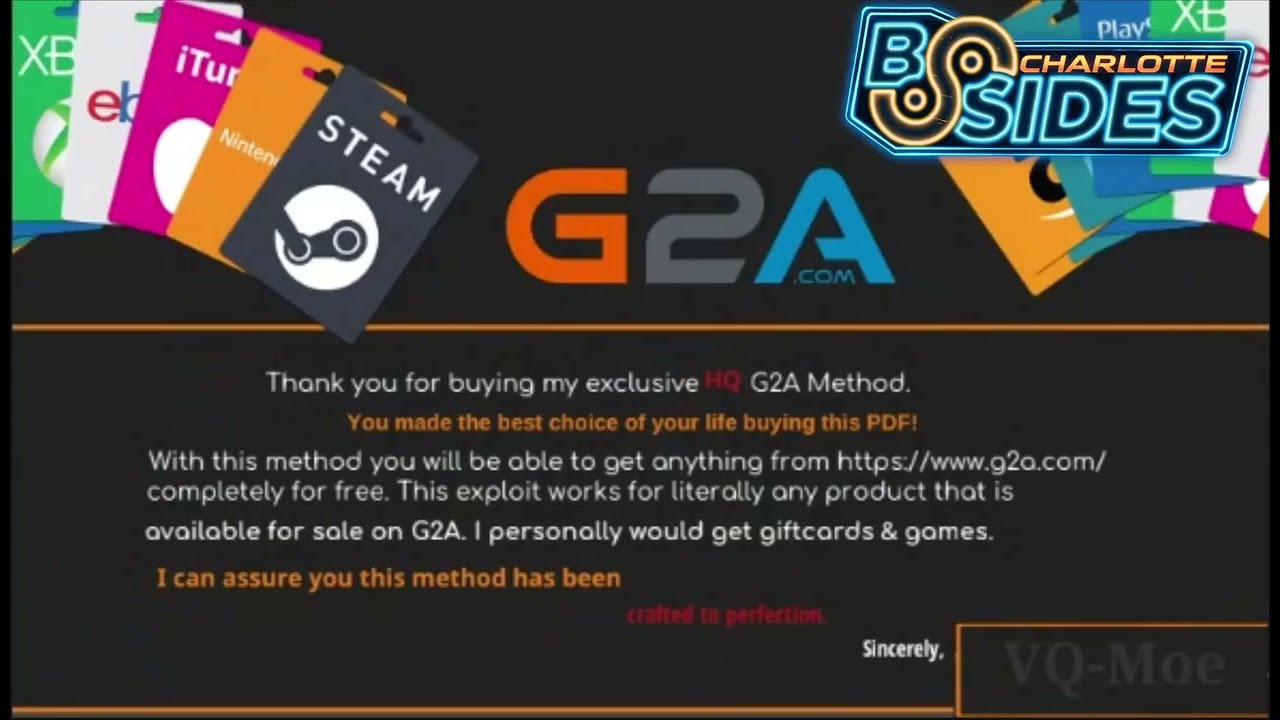
offering something to somebody with the goal of getting something back to you in return so no matter which attack Vector social engineering takes it usually plays on one of these four things with people fear trust curiosity and greed now fear that can play on the fear of missing out fomo it could also Play On Their Fear facing repercussions we see this a lot in phishing emails don't we we've all gotten them uh the ones that say we're going to deduct 47 million dollars out of your bank account if this is a mistake just call this number and give us your bank information we'll fix it or uh we're having trouble delivering the package that you drunk ordered the
other night on Amazon just give us your Amazon account and we'll reroute it for you or we can't verify your Netflix payment so you can't finish Formula One drive to survive this weekend sorry but call us and give us the credit card information we'll make sure that you get your ass access back then they can also play on people's trust in general people want to be helpful now this is even more so at companies if their role is service based curiosity we mentioned it could be the offer to get early access to something or be the first to get some kind of a limited edition thing anything that incentivizes them to listen more and then finally agreed that can be offered
a gift card or some other incentive monetary or not for them to take an action that the attacker is looking for human brains actually operate very much like a computer brains take an input they analyze it it triggers the response which is then manifested in an outward action now scientists that have studied the brain also know that there is something simmering underneath the surface as well all the time and that's our subconscious that's a part of our minds that integrates ideas together what these studies show is that subconscious thoughts actually happen first and then your conscience mind needs time to catch up so if something is out of place or dangerous sense then the conscious mind is activated for more
evaluation and oftentimes we call this a gut feeling how we relate this to social engineering tests are if the details are wrong in the test the game is up before it ever begins and the test doesn't help anybody thing is the converse of that is also true if the details are right it can trigger a subconscious response before your target even knows what's happening and the very best social Engineers are excellent at intercepting this process and triggering that automatic response secondly the other way that humans of course are different from computers is that humans run on emotions and emotional responses can override logic even when somebody knows better we've all done it right haven't we all done
something that we look back and like boy I knew I shouldn't have done that or I wish I hadn't done that computers don't have that problem computers run on logic human beings do not so again the best social Engineers excel at generating an emotional response from their targets because even when there's doubt that can be overridden so with all that in mind let's look at how we create a professional social engineering campaign emphasis on professional the difference between a professional test and a Candor generic one is that the test should be thorough and the ultimate goal is that the recipients reinforce and test their own security mindset and procedures it's a practice drill the military runs
practice drills they're not flying their fighter jet for the first time in combat athletes run practice drills so they know what to do at the event my kid's school runs lockdown practice drills and why do people do this well it's because when crunch time comes people will already know what to do the response will already be ingrained within them so a professional test helps an organization Baseline their employee defense as well as their technical defense because remember security is not just one thing and it also gives direction for them on where to focus for improvements so start with the overall objective what is the objective that the client wants do they want to see if you can capture
credentials is it getting remote access to their system is it physical access to a secure building I like to start with that and work backwards then you look at what tools do you have at your disposal what do you scoped for in your Roe and then remember the details matter and a proper campaign takes a lot of preparation I mean a lot as a matter of fact the more time you spend preparing the more successful you will be and that's why genuine red team engagements go on for months so if you if you're familiar with a technical pen test and if you've taken any of the major certifications pmpt and oscp especially you've heard the word
enumerate until your ears bleed but enumeration is the key to a successful contest because this through enumeration and seeing what's going on that's how you get the lay of the land it allows you to build a holistic picture of what you're dealing with before you ever attack and these same principles actually apply to a social engineering test so on a technical test you can have things like nmap scans website directory scans manually looking at web pages hopefully you're taking notes of what you're seeing right now once you get all of that information you can paint yourself a picture of how everything fits together and this is key in the context of their business every business every industry is
different you don't have to be an expert on how all of those work but you should at least understand the basics and understand how their business operates now for a social engineering test you're less reliant on technical tools but you're more reliant on osun open source intelligence gathering these are free resources no hacking is required to get them but you do have to know how to look for the information so to start with that you can look at things like their main website what messaging or keywords do you see over and over can you find an organization chart can you find the email address format are they using firstname.lastname or first initial last name for example
that detail becomes important later social media of course is a gold mine for osun both for the company and on individual targets scroll through it what are they talking about what are their concerns who do they interact with what other companies do they interact with going through Linkedin especially you can learn job titles the main functions of the business you can also learn their lingo do they have a help desk or service desk again that detail matters and becomes important later are the employees geographically Central or are they spread out that can tell you if you're working with a remote organization or one that could work in office might also clue you into how quick they can communicate once you
start attacking and then what are newsworthy topics in their industry are there mergers are the new advances rolling out and then online documents companies sometimes will post studies they'll have PDF documents out there but look at the metadata for those who wrote it what software did they use was it Mac based or Windows based again that detail can matter tools like power meta can scrape for this and Google dorks can be used to find documents and sometimes documents you wouldn't even believe are out there so once you start taking these notes you'll start percolating an idea and again just like in a technical pen test once you find a new server or gain user access you begin the enumeration process
all over again the difference is this time it's just more targeted from there you can start trying to figure out who are their vendors Google is good for that um I've even done things like an image search on our clients logo one time I found the client's logo that went back to an HR software company which seemed weird right why would it be there well our client had written a testimony about how much they loved the HR software guess what the social engineering campaign became tools like amass or the Harvester they can help you pinpoint some of the tech stack that's in use do they have URLs for a CRM or VPN which one is it
sometimes all you have to do is call and ask uh if I noticed a company that doesn't have any Tech roles on LinkedIn that's a clue they're probably using an MSP so one of the tactics I use is I spoof the number to an MSP that's in their region and I call and I pretend I'm a business development representative hey we're your neighbor over here just wondering if you fire them out any I.T services oh yeah we do oh okay great do you mind if I ask who you use they'll tell me that's awesome thank you is there someplace I could send information about some of our services typical innocent phone call but now I've
got a really good piece of information I've even done that for internal phone numbers um I've spoofed a new employee called a HR number infernal for example that turned up on Ocean hey I'm new I've locked myself out I know this isn't the red Department can you please tell me how to reach the help desk bam then you have the help desk phone number sometimes I've even found internal internets open to the wide open internet there was one client their internet was behind a username and password but for some reason a lot of it was exposed publicly and so I told them of course that so they could close it up after I plundered everything out of it but once
you ID some of these vendors look at their login Pages what colors and fonts do they use what can you mimic how are the fields labeled what disclaimers appear on these pages I'm not a great coder I'm really not that good at writing code for Scratch but you know what I am good at copy and paste I know how to copy and paste color codes I know how to copy and paste font types I know how to copy and paste logos and disclaimers then find then also look at what matters in their industry is there certain compliance requirements that people in Industry have to adhere to HIPAA and medical for example were certifications do employees in that field have to
obtain certain certifications and then what organizations or causes does does the company support are they active in their Community are they proud of some of those achievements see all of this stuff is stuff that can be copied and mimicked because remember you want their subconscious to think that everything is familiar and comfortable or to put it another way it's normal and safe so with those notes you probably have an idea for a campaign at this point and now it's time to pick a URL that you will use as the starting domain for your campaign I like to use the spellings flip-flop letters or adding words or numbers to things so like company name.com for example that could be the client I'll
buy the domain company name hr.com and you'd be surprised how cheap you can do this I've never spent more than twenty dollars for a domain and usually I don't spend more than 12. but even some very high profile company names just adding it or HR to the end of the can be a very easy path to getting a start on your campaign now these are examples of some login pages that we've used in Social Engineering campaigns that we've conducted the one on the left here blue the one in blue this is the same graphic that was used in the company's background on their login page there's a phone company logo down there because there was a news article that they had
been bought out and there was a merger going on employees of that company would have known that and that and then the one on the right the red one asset works that's a real Sales Force app it's used for Fleet Management through osun I discovered our client used that so I copied the color I copied the logo I call I copied the letter coloring and the copyright notice at the bottom this would have been a login page that looked very familiar to recipients of that company last one this is the one that uh I also copied the font type I copied the disclaimer from a real login page that they had I copied the company logo now
this particular company their name was made up of three words in the URL and I bought the exact same name but in one of the words I flip-flopped the A and the E and again it's going to pass a very quick cursory inspection you have to look really close to see that it wasn't the same one but that domain was 12 dollars so now it's time to craft the message and remember the four things we talked about the social engineering attacks tend to prey on fear trust curiosity and greed whichever of those that you choose to use the bottom line is to have quality communication remember people are people they're busy you're busy I'm busy we're
all just trying to get through the day and we'll typically decide very quickly how to deal with what's in front of you right people also feel good when they've accomplished a task so if you give them something and then it's done you get out of their hair it makes people feel good so things you can do install artificial time constraints when you're talking to somebody hey look there's only going to take a second I'm only going to take one minute of your time today I promise or in the email message this absolutely has to be done by week's end and the subject line put action required trying to bump it to the top of their priority list
sympathy also works oh God I sure hope you can help me you know it has just been one of those days do you have a real quick second just to give me a hand people generally will quid pro quo if you do this for me I'll do this for you in return an ego this really works with phone calls and in-person physical pen testing this is where you get somebody to Like You by liking them first AKA people's Pride will come into play too if you can get them to agree to a series of smaller commitments to say yes to easier questions and work your way up to what you actually want people are a lot
more hesitant to backtrack on a road that they've already gone down and again social engineering attackers will utilize those same tactics Remember The Details Matter every detail you put in your campaign either adds up or takes away from the effectiveness so match their email address format like we talked about before how are they using it what is the name is it first name dot last name first initial last name however it is that's what you're going to copy use the correct to lingo we talked before help death versus service desk make it believable bonus points if you can get the email signature and I know if it's our client it's easy enough just to copy it out of their
emails but think like an attacker go a little farther I found success by getting this by emailing the sales department for example pretending I'm interested in what they're offering I get an email back what does it have in it the corporate signature then you can copy it if I'm sending out phishing emails I also watch for out of office bounce backs because again A lot of times those will have the Corpus signature in there too and when you get these details right I have found success and I can tell this from the out of office bounce back with the client's email system is telling the recipient this is from an external Source use caution do not click on
things in here do not provide information and yet it happens anyway this one is an example of an email that we send out matter of fact it goes with that blue screen example we looked at a couple slides ago uh phone system provider vocera was purchased by Striker the integration was almost complete at the time that was in the news so again because that company already used that phone system that would have sounded familiar undoubtedly they would have heard that things were going through a transition so the campaign became hey we need your help verifying information has migrated successfully to ensure uninterrupted service please complete these following steps give me your corporate credentials and update
anything else that needs to be updated at the bottom is concluded with IT service desk at help desk they used his service desk this is another example this was one a company was very involved in the local community and they were big supporters of community initiatives so in the beginning I referenced this is a community initiative we launched last fall that they were proud of again would sound familiar employees would likely recall hearing about that so the campaign became we're setting up a community resource center we want to hear from you as to what causes our importance so we know what's important to you just log in here and let us know next one this one was aimed primarily at
a sales department sales departments live and die by their numbers and they're always looking for an edge to close the deal so in this case I bought the domain clientmaine.dev and I said we're opening up access to a development site you're going to see upcoming enhancements and upgrades to our services but you got to keep it confidential until it all rolls out but go in here and take a look and see what you think and let us know and spoiler alert it worked very well last one uh this is this is one we knew the client was going through a stock to audit based on osun hey security is important here and uh we're trying to
stay compliant with our audits so if you get this email it means you haven't reviewed our updated incident response policy just go ahead and log in here review it take a look and it has to be completed by the end of the week it's mainly because that's when my test ends and I have to tally some numbers for my report so thank you for your prompt attention to this matter
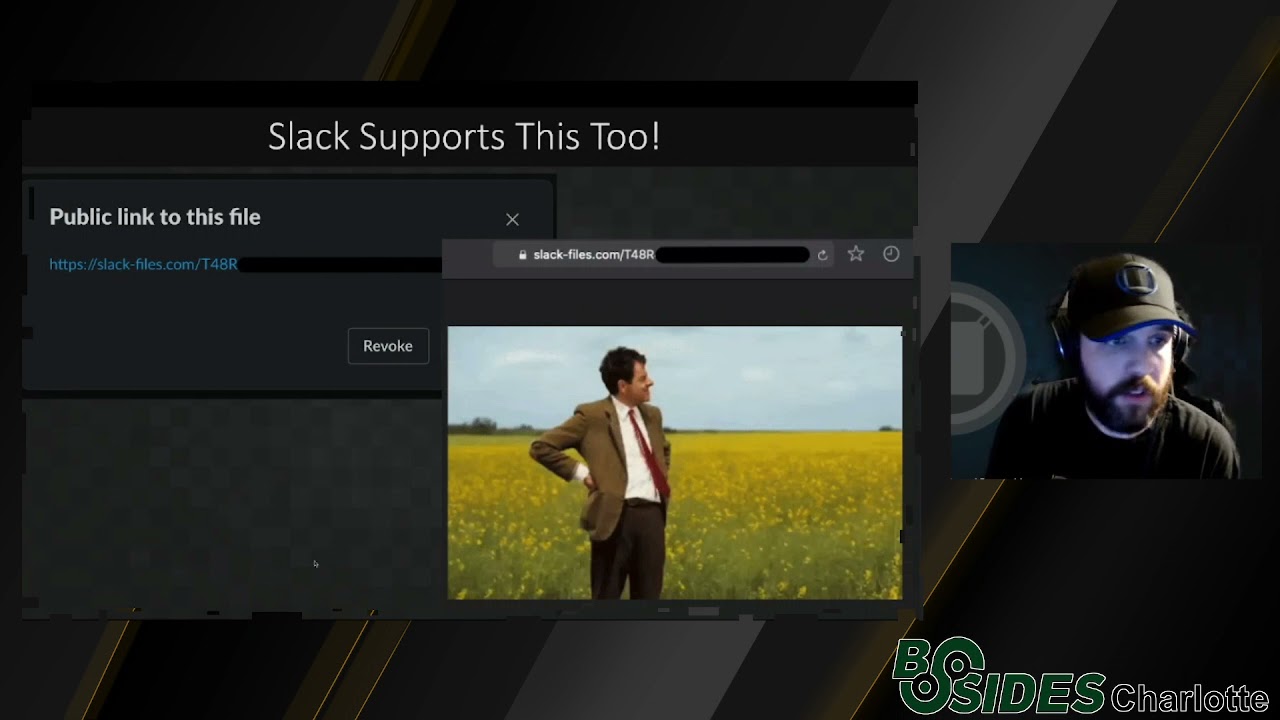
sometimes when searching emails so you're going to get caught up in corporate spam filters and there are ways to disguise the links some of them are more effective than others but this is one of my favorite things to do if you look at these two things at first glance they look exactly the same what's interesting is in internet browsers if you go to the URL bar and you type in HTTPS colon slash slash the app sign in google.com the browser will auto correct it for you and send you to google.com it'll assume that you made a typo where that where that becomes where that comes in handy for social engineering campaigns is that when you set up a domain
that any links you put in there are likely going to be reviewed by a spam filter or are they going to be viewed so you can have reputation problems especially if you just bought the domain for example so what I do is when I put the link in there let's use this example I put https colon slash slash the at sign in google.com but the at sign I sync down to a one point font it then becomes invisible on the screen it looks like a piece of dust and it's very difficult for it to detect but when the spam filter looks at it because it has the ad symbol in there it thinks it's an email address which is a
very common thing in any kind of business correspondence spam Builder doesn't care what the font size is it sees the at google.com and I've beat a lot of high-end spam filters with this trick if you're scoped for fishing which is doing phone call phishing um I like to use spoof card to spoof phone numbers if you have discovered phone numbers during your oath phase the help desk and the incorporate number vendor numbers employees whatever you can be whoever you want to be um there's a lot of obvious ways to use this but some of the uncommon things you can think of again to deliver a more professional test if you're afraid that your emails are going to get caught in a
spam filter or you think you might be you can actually call your targets and say hey we've had some complaints that emails have not gotten through can I send this to you real quick can you just make sure that you get it that's going to tell you if your emails are getting through or not and of course if they are just be ready to let fly right after the right after that phone call with the rest of them if your emails are blocked you have somebody on the phone see if you can get them to manually go to the site or do whatever it is that you're asking them to do but my very favorite thing to do
for fishing is quick assist on Windows this is something I learned at Wild West hacking fest last year quick assist is a very helpful utility that is standard on Windows it is used so people can remote in and help troubleshoot the system it also has a very fatal flaw it does not care what domain the request is coming from that's part of all you don't even have to get anybody's username or password to do it these are screenshots of using quick assist the one on the left is what you see you help somebody when you press that it gives you a code you give that code to the Target they type it in and then you can remotely access
their computer one of my favorite pretexts for this is hey uh I got an alert that security updates are not installing on your system automatically I just need 60 seconds to remote and then take a look real quick once I get in I open a command prompt and type in who am I and ipconfig to prove that I was there and to show impact to the client and then just get off the phone with oh everything looks fine let me keep doing some troubleshooting but that can be a very tricky way to get remote access to somebody's system again it's enabled by default and most companies do not have this disabled so again as professionals it's not just
about getting the credentials or getting access to the system as professionals doing a professional test we should test and quantify business impact that's what our clients pay for that's how we can best help them and especially if we have repeat clients running repeat tests either yearly quarterly whenever we can show documented improvement over time so once we get these credentials uh try them in the email provider VPN CRM firewalls anything that you found external facing during the osun part of your test if you're also conducting an external penetration test at the same time that's great if you're not the engineer on that work work with them and see if you can get access to those
systems what you're trying to look for there is compensating technical controls do they have MFA on those do the applications recognize that logins are trying to come in from a new location conversely if those protections aren't in place what are you able to access what files can you get can you get into their email inbox can you work your way to domain admin on the network and I've Seen It All I've I'm going to share two extreme examples um I had a test a few weeks ago where I got multiple sets of credentials from a phishing campaign and guess what they didn't work anywhere on the external perimeter I also had another test where we did get
multiple sets of credentials we use them to access the company VPN there was no MFA involved we were right there on the internal Network and in 30 minutes we had domain admin now if you're running a check the box test or a generic one it's going to get written as both companies failed the test but I will tell you as somebody who did the deliverables of those companies both of those were extremely different conversations because even though both failed the social engineering test the impact on one was far greater than the other so we're going to spend the last couple minutes talking about how to defend yourself in your organization from this and here's my bottom line rule is the
request normal if something feels wrong to you it is wrong so just ask yourself is the request normal is the email address or domain legitimate if it's asking to go to a website or a website that you know not the one that I've put in those emails or if the if the phone call is suspicious hang up and call the person back even if it's a friend call the person or company back at a number that you know outbound phone calls can be spoofed inbound ones cannot and then cultivate the security culture and here's the wrong way to do it I saw a LinkedIn post recently where an organization started using a Wall of Shame to publicly show who failed the
social engineering test and don't do that just don't do that if if you punish people publicly or embarrass them it's the absolute wrong thing to do do you know what that trains people to do it trains them to hide their mistakes and that can be detrimental to an organization so cultivate open communication have an environment where people feel free to say something if you know when if you see something say something kind of thing bonus points if they self-report I had a client that did that I got credentials through a phishing test and while I was using them they felt funny about it they self-reported to the I.T Department other people had reported that person's
password was changed as I was trying to figure out the way past their MFA and by then it was a smaller company worked out around and the campaign was dead and that's exactly the kind of response you want to see to an attack so train people to protect the business and don't rely on Tech tools alone because Tech tools alone are not going to cut it also have a plan to communicate through the entire organization if an attack is underway or this is how we're going to communicate these kinds of requests make sure that everybody knows that that will help prevent attacks and prevent further compromise if something is going on and then do have to effective technical
controls in place that correspond and complement the human element MFA on everything for example and make it interactive um there are usually two types one is you have to type in a code that's sent and the other ones you just push a button on your phone to allow access but remember how we talked about people and their subconscious just going to autopilot make the process as interactive as possible because that will slow the thought process down and people can think am I already logged in why is it asking me this because I'll tell you as an attacker I can tell if the prompt that is getting sent is a click to approve or they actually have to enter
it and it's just click to approve you know what I do I send that request over and over and over and over until they get sick of their phone being chatty and they just want to shut it up and they approve the request and you would be amazed how often that works and have a layered defense there is no point in pouring all of your time and efforts into making sure nobody can be social engineered if you've got an SSH Port Exposed on the internet that can be accessed with root and password one two three again we've seen stuff like that so having defense in depth have a training program and test these processes and procedures repeatedly
again instill the automatic responses in your team that you want them to use not the ones the attackers want them to use and I know it's very fashionable to make layer eight jokes and call people the weakest link of the organization and I disagree with that and I will tell you if all it takes is an email or a phone call to topple the entire organization the end users there are not the problem security posture is not tied to one single component so if you found something in here interesting and useful share with other people share it with the organization and your teams I always say it takes a village and we can all help each other
to avoid succumbing to these attacks and to raise the bar on how we as Security Professionals conduct social engineering test and when we do it properly everybody is going to win thank you for your time have a great day