It's Malware Time: A Bar Crawl from Skunked Homebrew to Rotten Apples

Show original YouTube description
Show transcript [en]
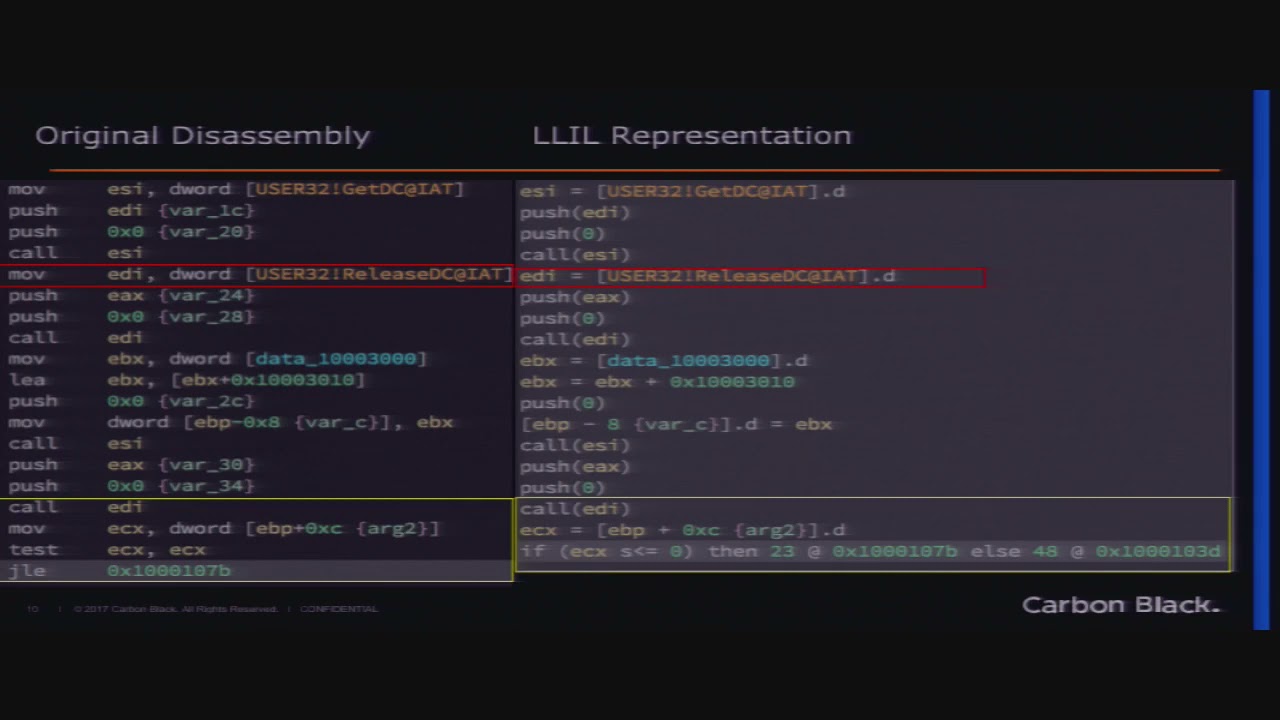
all right so sorry all right uh hi guys i know there was a bit of a schedule change unfortunately the speaker had to swap with me so i'm eric norenberg be talking about some mac malware today i work for carbon black in the threat analysis unit so today we're going to i'm just going to give a little introduction and then i want to talk about how it all started how we found this the process that we went through and we're going to go into a little bit of technical analysis of the malware and i want to talk a little bit about detection prevention because this is so prevalent and then we'll have some time for
question answers so who am i um i've been in the security industry for a while doing digital digital forensics malware reverse engineering some firmware analysis back in the day and some ios programming i've been at carbon black one year as of this week so actually a year ago i was speaking here for carbon black for the first time um i was also a forensic analyst and reverse engineer at dc3 the defense cyber crime center in investigating defense network intrusions so let's talk about how this all started when i was starting to put together this talk i was thinking about the malware and going into the technical analysis and all this and i was like you know that's really interesting but
it was actually kind of more interesting the whole journey that we got there over the last like six months so i'm going to talk about that a little bit more um because we found out about this in november of last year and it was a long journey of um discoveries some mistaken assumptions uh and rabbit holes because if you do malware analysis or any sort of intel stuff you always go down rabbit holes and end up you know fine sometimes you get something at the end and sometimes it's a dead end so back in november of last year my co-worker i'm sitting you know just sitting on the couch in the evening having a manhattan with my husband you
know watching a movie whatever my phone lit up with a slack notification from my co-worker jimmy and he's an avid home brewer so he said uh he was searching for this new stout recipe and i'm sorry this is kind of small i was expecting it to be a little bit more visible but basically he he sent me a message and said i was looking for this stout recipe and this form site took me to a flash update that i think is malware so i was like great that sounds awesome let's look at it and uh so i started looking into the website and in january um so we were we were um i skipped a lot there
wow okay okay um anyway in january we had been looking at it for a while and i was like oh my god i think this is windtail because i'd been looking into windtail malware and it's a basically a an apt malware for mac that bypasses gatekeeper and so um there was this article by um phil stokes from sentinel one and he was talking about this and he included a screenshot of a script that looked so much like this one that um i had seen i was like oh my god jimmy we you know we found something really interesting so this was the script that i found this was the one that from what i had seen
it was this odd799.com marsupials.zip looking into it further i found like kittens.zip and elephants.zip and you know there were all these zips and it was just a very simple bash script basically that um you know pulled down this zip file unzipped it and installed it with open nothing too sophisticated so this was his article and you can see like this was almost like verbatim the same thing that i had seen and this one was kittens dot zip which i also found um but uh basically it was just a the installer it was a fake flash installer as well it wasn't actually an app it was just a command so it was just basically it looked like you were installing that
but really behind the scenes it was just this player.command bash script it had an application icon but when you actually clicked on it it was really just running this bash script and pulled down the payload the second payload via curl typical system utility on max so down the road rabbit hole i went i was like wow i hope these aren't all adware because you know there was this thing in this windtail article maybe it's like you know something more sophisticated maybe this is going to lead to something bigger so my co-worker greg foss said hey why don't we we've got this site uh double docks double like the beer this is a beer site home brewer forum
so he wrote some python using selenium to basically scrape the try to automate collecting these samples so it would go to the site there were a series of redirects so this script would go through these redirects detect when there was a payload that was finally displayed to the user that was this flash update and then it would whenever it found the site it would pull down the url take a screenshot get the source the source of the page and the payload so we collected several just off the very front we were able to pull down several samples however this was january back in november the site was not very sophisticated you could just keep hitting it and pulling more stuff down
so initially back in november i'd pulled down probably like six or seven samples just to see what it was now in january they had gotten a little bit smarter and ended up detecting if the same ip was hitting multiple times within a certain period time period so what greg did was set up a rotating proxy so that he could connect to different vpns have different like rotating ip addresses to try to pull down samples without notifying the uh the website that this was the same person and this worked pretty well for a while so here we are we're like man we found all this really cool stuff right like we got to name this thing
because nobody's ever seen it before this is really exciting the best and worst part malware analysis like it's always like well what are we going to name this thing so the original site that we had seen was double docks double like the beer dubbed eel and uh we had been in this hot debate in in our slack channel at work about ipas because i'm sure all of you know a lot of people have severe very very strong opinions about ipas most people hate them my co-worker brian baskin who may or may not be in here but he's one of the conference staff was going on a rant about how much he hated ipas so i was like well why don't we call it
double ipa and yes i know doubles don't have anything to do with ipas but i just wanted to mess with them so double ipa was born we made a whole slack channel for it you know we were going crazy this was so exciting and then i found schleyer i was like oh man i guess we're gonna have to call this thing schlier there's the uh the article so this was in tago researchers in february of 2018 uh one year prior had actually researched this and found all the things that i'd been finding i was like ah bummer right so bummed can't use a double ipa name but my our boss actually said why don't we
just keep double ipa and make it like a campaign identifier like it's still schler but you know it's the double ipa campaign or something just so we can use it but it was pretty clear that this was an ongoing thing you know for the past year so like all right i'm just going to have to call it slayer so let's look a little bit into the technical details now that you have a bit of the back story so what is it like i said um in february well january they posted this article in february but they initially discovered it back in 2018 we found our samples in november as i said we didn't know what the family was at
the time we didn't have a whole lot of time resources to devote to it so i was kind of keeping up with it hitting it every once in a while i looked in december a little bit looked in january um we didn't really think a whole lot of it cause it's like well it's you know adware we found this one site but then i started looking poking at virustotal and seeing that uh basically on a daily basis there were hundreds of these being uploaded each time it was one sample there was one submission for each of these all of these hashes so we saw an uptick back in february 2019 when we started looking at actual
customer data it's like okay this is actually getting serious we need to look at this a little bit more and when i actually started uh digging into the malware i noticed that there was a kind of a unique privilege escalation technique that um one thing it was not identified in the miter attack framework which my my co-worker jimmy had been doing a lot of attack work and so we thought that was pretty interesting and we actually ended up submitting it to mitre and it doesn't have an id assigned yet but it was accepted so it should be in the next version of the framework so back to greg's collection script we did this initially it was working great but
the malware authors started getting a little bit smarter so in addition to just detecting ip addresses they were detecting ip ranges and so we were vpn hopping still working a little bit but um they started kind of redirecting to this dummy site that was uh ww9.doubledocs.com so we're like okay how do we get around this so he modified his script to detect when this ww9 site came up and said okay we're going to back off we're going to sleep for a while we're going to switch ip switch vpns switch countries sleep for a few minutes and try again so again this worked pretty well um right away we got 50 i mean within like probably a couple
hours we got 15 unique samples so there were a lot of i know you can't see this but there were a lot of duplicate hashes that came out but they were also served from different sites with different names um but like i said you know in the probably i don't know 25 i can't see it uh 20 something hashes there were 15 that were unique so we started digging into those again so i just wanted to see if this will work no that's not gonna work okay um actually i don't know how to play that let's see if i can just move this no well anyway so if you go to doubledocs.com right now this is
actually um the ww9 site you can probably tell even though it's kind of blurry probably you've seen these things before you know when you go maybe you mistype a domain or something and and there's this squatter that's got this like fake search site or whatever so basically it was getting redirected to this so like okay we need to we need to adjust this so i started modifying the script and trying to see if we could um you know get around this but um they had actually started putting captchas in so it was like you have to click you know am i human that kind of thing and they started moving the payloads around so the selenium script wasn't working to
download the payloads anymore unfortunately so again like i said the distribution we found it on this home brewing site but there were tons of hijacked domains that they were using to serve out these ads and what it seems like what it seemed like at the time was that basically when a domain would expire they would squat on it and be able to hijack them to re use it as a redirect to other ad sites so some of these would have five or six redirects until you get to the final payload so for the most part for the most part these were fake adobe flash installers is very common i don't know why people are still installing flash
but also some browser extensions usually they were dmgs or packages we saw isos and zip files and a lot of them if you look in virustotal a lot of them are in torrent files for you know cracked photoshop or cracked you know cracked software and they're bundled in there some of them actually do finally install the software like the real flash some of them don't even bother so lately like last week i was trying to look at this double docs again and now it's only it just keeps redirecting me to to the dummy site so it's not working anymore so i took a look at the page source just out of curiosity and i noticed this uh parking
uh parking crew.net i was like what is parkingcrew.net it was using all this css from there it turns out it's this uh domain uh parking platform that advertisers use for this this exact purpose so it seems to be using that to um distribute over these ad networks and things like that not something i had really looked at before but apparently there are things called domainers that actually just specialize in this so a lot of money in it i guess so this one i thought was really interesting this is one example of the the sites that you would be redirected to so you can see that it's actually detecting you know what your os version is
so that it can customize this page for the user make it look a little bit more believable this one is a you know you're infected start a scan downloader software kind of thing but the thing i thought was interesting was this is the only custom part of this page they actually mirrored all of these links are the actual buy apple care link it'll take you to the mac store these will take you to you know all of the apple sites the legitimate apple sites so only this piece right here is actually the malware or from the malicious the content which um you know just makes it a little bit from a social engineering perspective makes it a little bit more
believable to the user so here's just a sample of some of the many many different sites so you can see like all of these things these are all just you know the various ways that it distributes this all of those flash updates are the same well not same hashes but they're all these malicious schleyer uh packages but they they um display it in a different way to the user depending on which site you get redirected to right and then some of them are these uh actual chrome extensions that it'll display the funny thing is so here's one of the chrome extensions and at first i thought uh whatever it's just taking you to some this is just a
different redirect or something it's taking you this this chrome extension page to to add it for whatever reason and then i noticed oh wait that's actually just a window on top of the malicious site so this is the actual legitimate thing from the chrome store but it's sitting on top of the double docs site so i thought that was pretty funny and some of these samples had some javascript um that were bundled in and had a crypto mining component so this is actually just showing you uh before and after the crypto miner was installed so you can see like you know the cpu usage goes you know skyrockets there's my friend adam my former co-worker in the audience somewhere
so he hit me up the other day he actually left us and we're trying to get he's going to come back i know you're going to come back but he was searching himself in google and he's like hey take a look at this this link down here it was like oh look at that i clicked on it and uh sure enough took me to another schlayer site so uh another co-worker casey had hit me up a couple of times he was like yeah i was searching for you know python 7-zip extract and you know the third result was this funny site i went to it and it's like trying to serve me a fake flash
update so somehow they're they've infiltrated the ad network i guess they're you know uh paying for for google adwords or something like that um but it's funny that it's it's legitimate searches you know it's not searching for anything interesting i tried to figure out a way to um kind of automate this and try to detect these but it's really like one in a million we just happened to over the last few months stumble on four or five of them of these google searches that that pop up this this uh site so let's look at one of the executions like how this actually works um so i'm going to take one sample that is an example
of a dmg version they all pretty much well after the first stage they all pretty much work the same this one in particular creates a hidden directory with a doc command script which similar to the the article the initial article from phil stokes so after this stage some of them are an actual app where it goes through an installer but this one in particular was basically just a bash script after that it's pretty much the same functionality basically you have a first script that decodes and decrypts another script that script decodes another embedded script and the third script is the one that actually does the download of the final stage payload so it'll actually download it download
the zip uh extract the zip and open up the final installer the privileges it actually uses pseudo and some techniques that we'll talk about a little bit the important thing though they're the interesting thing is that all of these payloads every single one of these and i'm talking hundreds a day hundreds of new ones if you look in virustotal every single one of them signed with a valid developer id valid certificate um i actually did talk with apple support we had it uh back and forth and they've been revoking certificates pretty quickly um so it will like neuter this thing but um at the time they weren't revoking any of the actual developer ids so you would have we had one that uh
that i looked into i started just like scraping all of these developer ids i got to like 70 i'm like this is ridiculous um and so one of them was like maxwell brooklyn so all of them were kind of like if you're familiar with domain generation algorithms um kind of in a similar way so that would um generate random domain names they had something where it would generate a random name so sometimes you'll see like a weird name that has a last name for a first name you know and they all look very suspicious but this guy maxwell brooklyn had been signing these things for over a year at this time so i'm like okay
there's definitely something wrong here um and so now uh since then since probably about february they've actually started revoking some of these developer ideas as well but you know it's a total uh cat and mouse game you know you can't uh they can only you know keep up with these things they're just continually generating so hopefully now that they've got apple has started uh what is it called they've notarization so they've implemented notarization that i think is going to be required for 10.15. any apps that are running on 10.15 will have to be notarized by apple which is another step of verification basically so hopefully that'll mitigate some of this so let's take a look at the first
encoded script unfortunately this is going to be a little bit hard to see i was hoping it'd be a little bit bigger but i'll tell you what's going on here basically you've got this encoded and encrypted bit and there's an eval where it has openssl um xxd aes basically it's going to base64 decode first and then ssl decrypt using this password that's here and this password i'll talk about a little bit later but basically it's hardcoded per sample and when i first started looking at this i actually a former co-worker of mine after i posted the the initial kind of notification of it to our customers he said hey i've been tracking this for a while also i've got like 5300 samples
and i think that this password is actually based on kind of a time stamp thing and so i kind of started looking into that as well and you will see that this number increases so it's some sort of uh you know time stamp type of i guess tracking that they're using but um the artifacts down here this is just an example of cb response but you would you know any sort of endpoint thing or like if you run any sort of like process uh tool you'll see the child processes of bash you've got base64 here user bin base64 and user bin openssl so you'll see those each time and this is important as i'll talk later
about the detection so this second script that gets to decoded by that first one is going to you've got another section of base64 code here um it's going to base64 decode that and then it uses xxd if you're not familiar with xd it's a command line hex editor that's on most unix and freebie or bsd based systems it's just basically a command line hex editor that you can use to dump or or modify or manipulate hex so they use this to format and write out the third and final script so this third script is the one that's the it kind of mimics that initial bash script that we saw uh this one this particular sample is is
kind of one of the the more sophisticated ones that has uh some more layers of obfuscation but basically when it comes down to it these are all the same at the end you've got a curl command where it uh basically will pull down the payload that's a zip it's a password-protected zip the password again is hard-coded into these scripts so both the password for the zip and the password for the decryption are both hard-coded and these curl you can't see it here but the curl command line arguments are also interesting it's dash f0l and i'll talk about that a little bit later but this ended up turning out to be a very good behavioral indicator that
was high fidelity for detecting schlayer very specifically so let's just take a look at one of these urls basically for each url you have a c equals which we're calling it like a campaign identifier this one is not unique so we did some some analytics on you know frequency of each campaign identifier not a lot came out of it but we couldn't really find any sort of correlation we were thinking maybe at first this is indicating like who it's targeting or something but you know we just didn't have enough data to really say that there was anything really there um we've got a u equals which this is actually a unique id that's for the victim system it's based
on the i o platform uuid so basically they just run some system commands generate a uuid that they put into this url for tracking again um we've got an s equals which is a session id and this is just a straight u ig uu id gen command just the output of that we've got the o is the mac os version so it actually has the the the full version and the patch level so 10.12.5 in this example and then that encryption key so that it's b equals and there's that encryption key that we saw in the very first sample they actually pass that into this url again probably for tracking of some sort and given that it's based on a timestamp
you know maybe they're using that for you know tracking campaigns i don't know so let's look at this again a little bit more in detail unfortunately you can't really see this very well but this just shows this is just i used a screenshot from our cb defense thing because you can see the whole um if you could actually see this you can see the whole um all the artifacts for each execution of this command but basically this shows the curl command and the the uh particular url that was um that was used and up here um if you could read it you could actually see it says this is a valid has a valid certificate and it's signed by like
becky mayhem or something like that but it actually you know it checks the cert and you can actually see that they are validly signed so this privilege escalation i was going to talk about a little bit more um it actually uses this security off trampoline which is uh used in this uh kind of unique privilege escalation technique that is um talked about uh you can't really see it but you the after effect of this it actually it's a it's a security auth trampoline is set uid root so the uid command is actually called as kind of a artifact of that and this is another thing that is a pretty high fidelity behavioral indicator for this because
it's not something that's commonly seen in environments from the research that we've done so this security auth trampoline set uid is actually part of a call to this deprecated api called authorization execute with privileges so this was actually deprecated by apple many years ago because it's unsafe the problem is people still use it because the secure uh replacement that they put in is very difficult to implement and so most software developers have just stuck with this authorization execute with privileges unfortunately it's very vulnerable to this privilege escalation technique where they can basically authorize with sudo it does actually require the user to authenticate but like we said the most of these things are an installer package so the user is
expecting to install flash the user is used to having to authenticate when doing an installation so don't think too much of it problem is once this is actually executed and authenticated everything after that is basically kind of white listed past gatekeeper so it can once it gets root it's on the system and it can literally download and install anything else it wants this screenshot is actually from a very very good talk by patrick wardle if you're not familiar with him he's a mac os researcher um and the his talk is up on youtube um i definitely recommend it it was from defcon 25 uh it's called death by a thousand installers and you can find it on
youtube on his youtube channel actually on the defcon youtube channel but i definitely recommend it it's very interesting so lastly i wanted to talk a little bit about the detection
i have to talk about attack because you know it's the hotness so um we had you know some of these these techniques like i said we've we've got this privilege escalation technique that's based on this authorization execute with privileges api call and miter will be adding that to the attack framework uh defense invasion and discovery uh again this was the death by a thousand installers you can see like it this flash player installer does actually require the user to authenticate here um and again we see the artifact of this this is security off trampoline that's being executed here by the malware so the behavioral indicators i kind of touched on a little bit the problem with this malware is like i
said with if you just look in virustotal and i i came up with a very good high fidelity search on virustotal based on these behavioral indicators because now with virustitle you can actually just say behavior now that they've got the sandbox stuff implemented you can say behavior open ssl like with command line arguments and things like that so you can actually look for these things and there are so many hashes every day because they're basically my theory is that you know they're uploading one sample for every one of these hashes and just hitting them against these uh antivirus engines until they say okay we've got too many detections we got to flip this put a new cert on it
new developer id you know flip up the hash you know so that we've got a new hash we've got new certs the certs have been you know killed or whatever because when this malware actually executes one of the things that it does in the final stage before it actually finishes installing it will run spctl which is a command that you can use to check the cert of a given binary and so it'll actually run this spctl and say okay is my cert still valid if it's not i'm going to die kill it so if the search not valid it's not going to go through with installation because then it's going to be picked up by the operating system and the
the security controls that are built into mac but anyway so like we saw in the script before though we've got xxd pretty common you know if you run a search across your environment for xxd if you've got developers they're probably maybe using these in scripts they may be using it at the command line pretty common openssl again you know any sort of admin tools if you got you know sysadmins are probably using these in some automation scripts or things like that for certs and whatnot pretty common curl again not as common but you know a lot of developers still use that uid very uncommon as an actual child process and security auth trampoline how often is security auth trampoline
actually loaded as a module from applescript from a user-writable location those things are very uncommon that combination and the actual combination of curl and open ssl or the combination of these three things together you know curl by itself or open ssl or xxd by itself may not be a very good indicator you combine these behaviors into one and it's very uncommon so we decided hey let's actually take a look just let's just take curl so how often is curl used across this is millions millions of computers again think about each of these squares is like one set of computers and the color is how many what percentage of the computers in that group are running curl just curl by
itself so the process name just the process name curl that's it again in the enterprise setting you're going to see this a lot with developers if we take this and like i said again the unique command line arguments of dash f and then 0l you narrow it down to that and we've got that hardly ever used in the endpoints that we actually looked at every single one of these except for one i think it was a vast there was a one one case of a an anti-virus agent downloading a package update or something like that but everything else was all shlair every single one of them so these command line arguments the f is fail
silently probably not too uncommon right zero though use http 1.0 why would somebody want to downgrade http using curl legitimately why would they bother right not very common and then dash l another uncommon one is follow redirects so the combination of these alone i mean this is a very simple combination here curl with the command line arguments of dash f0l and it was extremely high fidelity for identifying slayer across all of our endpoints so this is just gives you an idea you know because you know a lot of a lot of ioc stuff is focused on let's ban hashes or uh domains and things like that but there are so many hashes on a daily basis new hashes that are
developed for this you can't chase them you know you're never going to be successful so you really have to focus on these behavioral uh the unique behavioral indicators so what's the takeaway here basically gatekeeper and xprotect great great security controls on mac but they're not going to protect you from something that's executed by the user you know they're signed installers so they're not going to put pop up that thing this is by a known developer or unknown developer you're going to have to change your security settings to run this no they're signed so it's going to get past that user thinks nothing of it you know adobe flash sure it's from assigned developer but do you really need flash this day
and age probably not most cases if you really have to though you know you can make sure that it's downloaded from adobe and check the cert it's easy to check the certs from the command line on mac os you can very easily say run one command and say yep this was actually signed by adobe systems this is a legitimate um executable or installer there's a huge network of hijacked domains and websites like i said we started chasing all of these domains like all the ones that we were pulling from all these samples that we were finding and it was rotating like and there were just countless numbers of these also and in the evolution of this when we
what we started seeing in february is that they were actually hosting all the final payloads on amazon aws so try blacklisting that in your environment right s3.amu amazon yeah no so you know you're not going to get around blocking these domains when the the final payload is hosted someplace legitimately how they're getting away with that still i don't know but so like i said hash and domain based iocs are of limited use you got to rely on these behavioral indicators so i wanted to put these links up unfortunately it's kind of small but i can post these up on twitter or i'll put a link to them after the talk but i wanted to open it
up for any sort of questions or comments or you know whatever anybody have any questions lemonade you said that yeah yeah okay i love my coworkers even the former ones anybody else yeah so we're actually going to there is uh one of the things up here so i'll just actually mention this so the first three patrick wordle death by a thousand installers definitely recommend it if you're interested in mac security well pretty much anything that he does um the original schlayer blog post were the intego researchers uh and then phil stokes wrote a really good article just basically on how mac malware can bypass gatekeeper in general uh we have our threat intelligence notification it's just a
very short overview of what the malware is if you're actually a carbon black user for some reason or and want more information like specific to the product our user exchange has there's more information on that than on the public blog post and then we also greg wrote a cbr command line parser for this we've got a github page our towel tau tau tools github page on our carbon black github and he actually wrote a script that if you have this in your environment and you happen to be running cbr it'll actually you know go out and pull it all and actually mitigate it for you so all of those the iocs and scripts and stuff are all up on our github
um yeah and there will be a deeper a little bit bigger blog post coming out shortly after this that goes into a little bit more of the detail that i mentioned today so any more questions actor or yeah is something that they've commercialized and they're selling because yeah so he said um is this one bad actor or is this something that's commercialized and they're selling to a lot of people um unfortunately i don't have the resources for the intel to like actually determine that kind of thing um but given the widespread uh nature of it i think it's probably commoditized um you know i don't have any like dark web access or anything like that but
i would guess that because of the ad networks that they're using that parking crew.net and things like that they've probably monetized this and selling it to to people just the sheer expanse of how rampant this is and we're still seeing customers being hit on a daily basis with us daily um so yeah any other questions okay thanks