CiscoSecure
Show transcript [en]
foreign
[Music] all right how's everybody out there we just need the volume yeah can you hear me yeah you're not yep all right all right well first of all how about we give a big round of applause where everybody just did that technical troubleshooting thank you so much thank you so much all right okay so Marilyn uh give me a thumbs up I'm on live you can see my screen good okay let me go ahead and disconnect here from WebEx and then we're going to Showtime okay well first of all greetings to all of you besides Calgary uh from New York City I'm Carlos Diaz uh otherwise known in the industry as difference and um I am excited to be your last
presentation please give me your your energy and your attention I'm privileged to represent Cisco secure which is my employer that I'm working with and then essentially I'm here to bring you not product I'm not going to walk you through product I'm here to give mind share in the spirit of b-sides for practitioners by practitioners okay so essentially I'm going to provide you our philosophy on what we are preparing the defensive Innovation for tomorrow okay a little bit about me my name is Carlos I'm originally from Brooklyn New York uh formerly I'm from the United States Navy worked at places like Google and McAfee my specialty is really to implement uh the productization of defensive products
so we can contend or neutralize threats at global scale okay that's my Twitter handle if you like code go to my GitHub or feel free to chat with me we can create tools open source and help each other out and also be on the lookout for a lot of my posts on LinkedIn where I talk about defense tactics and how to neutralize adversaries okay so I'm bringing you this conversation today it's about mind share it's about you the defender and how we definitely need to achieve defensive outcomes okay so first of all you're probably wondering what outcomes are we talking about when it relates to defense we're going to State the context first with the meaning the
purpose want to introduce to you in 2019 uh an authoritative company out there that is very good at what they do known as McKinsey introduced in the industry a new way of approaching cyber defense it's called the risk-based approach okay and the difference of the risk-based approach is that it's founded on being able to do three things really well the first thing it is fixing the fragmentation between the business alignment and the Defenders down in the front line being able to fix that misalignment that tends to be present in some organizations and the reason why that's important is if the business doesn't align with us the technical Defenders then we can never meet in the
middle and purposely apply the Investments that the company has providing that's the first thing the second thing that risk-based cyber security does is it changes the way we approach defending and designing controls in our Enterprise in other words typically we tend to want to deploy controls all over our Enterprise and we feel that we're not reaching that mature state of Defense because the controls aren't making it across the entire Enterprise risk-based security changes that but allowing us to actually find what is the meaningful focus of specific controls in specific critical assets of the business so we can actually deal with the threats that Target the most vulnerable areas of the Enterprise that's the difference between a maturity model versus a
risk-based approach right and the third part is that this actually gives us a practical way to optimize defensive costs okay and we're going to see what that means a little bit further down the line so I want you to really take this in and after this presentation go read this McKenzie article on risk-based cyber security which is transformational this is pretty much the premise that I want you to walk away with as a Defender your fellow Defender this is the value that this does for me in the Enterprise because it allows me to rigorously prioritize and maximize the efforts as well as the Investments that the company has afforded Me by establishing an appetite for risk in other words our
prioritization is improved because we don't have infinite resources I'm sure you can relate to that and then by establishing an appetite me as a technical person I help my organization establish what is intolerable for their appetite an example here would be it is intolerable to lose productivity in the business yes it is so that being the focus of the high risk then what is the actual threats that I need to be focused on primarily should it be pups potentially unwanted software should it be crypto miners or should it be ransomware and privilege escalation I want you to think about that you've got limited resources risk-based allows me to prioritize ransomware impact because that's where my appetite is in
other words that's intolerable to lose productivity due to a ransomware attack and if we continue to actually approach it that way prioritize and rigorously focusing on the meaningful threats that create impact and the controls that counteract it then we're definitely in a position to spend our resources efficiently and effectively so that's the biggest takeaway I want you to have here today what does risk-based mean it's not a compliance spreadsheet it is a method of thinking of how to optimize the defensive layers each and every one of us has to design our security systems for okay so that's risk-based um cyber security so initially you possibly wait um thinking it's like is there a practical approach
in order to achieve that risk-based uh cyber security approach yes and I'd like to introduce you to something called TBS time-based security okay so this would be the Practical philosophy of how we can achieve effective risk-based cyber security TBS was actually published in the 1990s by Mr Wynn schwartow okay and essentially he and his team and some other luminaries intruded the department of defense's systems thousands of times even though the Department of Defense is uh Investments was massive they had millions of dollars of IDs as firewalls Etc but Mr schwartzow actually tested the defenses of all of those Investments how well the Department of Defense had prevention enabled how well they could detect and how would they respond after
detecting that's known as the pdnr aspect of time-based security now I want you to understand the cliff notes of time-based security time-based security is not about Computing the amount of time an adversary takes to achieve their sequence no time-based security is about how much time does an effective security system give you to respond and remove the threat and time-based security is in our world everywhere and this is an example of time-based security in the physical world of house um buildings are designed when you look at a door or a wall and the chemical composition of those particular elements they are resistant against fires which is the meaningful risk where loss of life could be established so the
time-based security metric that you're seeing there in those blue and green columns is letting anyone know if they position the walls in the door frames in a particular architectural pattern how much time do those particular Elements by the people in such rooms until the fire spreads and there's loss of life this is real world value that's how buildings are built our homes are built so TBS is not a theoretical aspect it is a meaningful framework that tells us how to design an effective security system and the formula that you see in there with the green smiley face that's what every Defender like you and me is aiming to design with our firewalls our proxies our endpoint security Investments and it
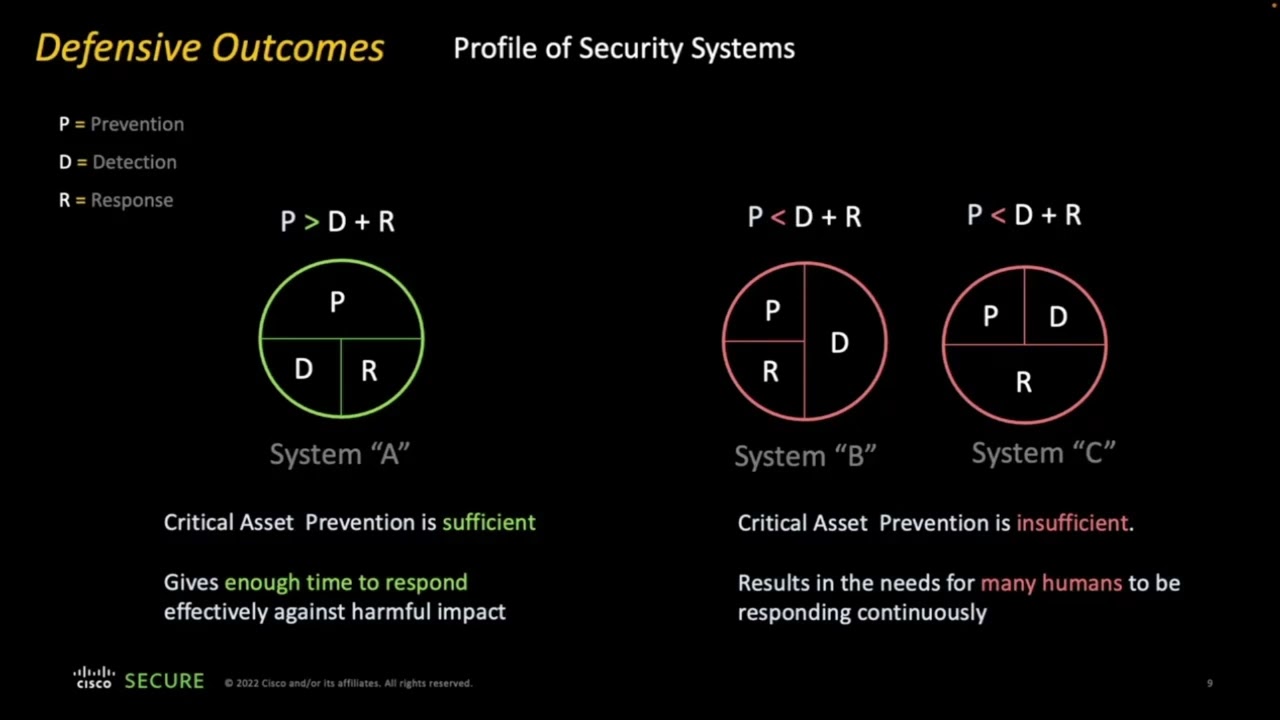
tells us that when protection is greater than D plus r combined then we have an effective security system notice what I was saying there prevention must be greater than the detection response in our example with the graphic it means that the firewall that the wall composition can sustain that fire enough time for people to know that there's a fire going on and they can walk out the building in contrast TBS tells us that an ineffective system is one whose prevention is less than detection and response combined this is why it's important to know that if we're pursuing meaningful defensible outcomes first we need to know what the final outcomes mean as the system that we're designing and I'm going to give
you one last example here of profiles of the systems that we're all building and it's very natural and I'm demonstrating to you three types of systems three profiles on the left hand side you're seeing system a that is a TBS design uh system one where prevention is greater than b plus r that's an effective security system in system B you're possibly CNS it's a system that is designed to detect most of the time but there isn't much preventing much response and the outcome there shows us again with TBS it's an ineffective security system but why is it ineffective it's because it's not giving you enough time to respond effectively you're reacting too much now if you have this type of system in
your Enterprise then the only thing we need to understand is that if you have system B and C you require a lot of humans to constantly respond effectively and so we go back to the risk-baser process telling us optimizing the defensive layers we don't have infinite resources we want to be able to have enough prevention walls that give us enough time to respond efficiently with whatever resources we have in the Enterprise so TBS effectively gives us a way to understand that the defensive outcomes we design have to be manifested in the system that we're showing here in the green circle excellent so time-based security is done so if now we know how to design a system then we need to ask
ourselves well who actually does this kind of work okay we're going to spend a little bit of time now enabling ourselves the defender because in order to get those outcomes done the person that leads these outcomes is the defender and they're on a journey to defend in that Journey they have to be able to put together portfolios that have prevention controls detection controls and responsive controls and essentially if they can harmonize that orchestrated in a balanced approach then they'll be able to prevent things to anticipate the adversary they will be able to detect and identify the presence of the adversary confidently and if and when they identify it they'll be able to respond by confronting the adversary
with the effective actions that are needed and we're going to see an example here I'm not just bringing you text I'm going to get down to code and show you an example okay so this effectively shows us that the outcomes of pdnr are driven by the defender in order to successfully defend but let's talk about how does the defender actually achieve this what is the essential things that they need how are they approaching it mentally and this slide would represent to you that no Defender can successfully defend by using prevention technology or detection technology or response technology without having an understanding of the threat it is impossible if they don't have an understanding of the threat all they see is isolated
symptoms but they need to have understanding in order to comprehend the systematic impact from the threats they have this understanding then they can coordinate the technical interventions across their Enterprise with I.T that are required to defend if they know how to coordinate after having an understanding they can communicate and express the urgency and the severity by which the incident response needs to be conducted during the attack they have the understanding they can validate the threat intelligence and corroborated to establish The credibility of the particular risk being manifested this is the intimate relationship between the defender contacts and we're about to see the technology the main thing for you to take away from this slide is Defenders need to be
provided concrete understanding so they can actually defend and there's only one thing that improves understanding context and that's how outcomes are pursued with context I'd like to outline here why context is so important because context allows the Defenders to actually make the first move evaluate and understand where they're going to put their defenses against the adversary to the greater impact they take the right actions ahead of time they're reacting less and they're actually neutralizing High severity situations without those actually causing a lot of impact but these actions that Defenders take what are they well here's an example you can have many products that are giving you the ability to create responsive actions you can block things you can
restrict permissions you can restore credentials you can disable having a product that gives you these actions as capabilities is not enough to effectively defend because the most important thing to know is the capabilities that are afforded to you by a product you must know when to use those things before the attack during the attack or after the attack and an example here would be if you restrict privileges if you restrict privileges before the attack then you are effectively reducing the attack surface but if you're restricting privileges during the attack then you're no longer proactive you're actually reacting and conducting containment that's the key here of this intimate relationship between context technology and expressiveness how do we express an
effective defensive plan let's get right into it now here's context in what it needs to be context has to be something that formulates the scenario but it must introduce terms that allow Defenders to understand the scenario and evaluate this scenario and here's a day in the life of all of us we're seeing here in the scenario these circles with question marks that represents the discrete indicators that you're processing every day hashes IPS register Keys Etc you receive these on a daily basis you don't always have context you need a scenario in order to understand how those particular data points are actually intertwined now with the scenario that we're seeing here with Visual Basic script macros
let's actually begin to explore terms that are needed from the scenario and this is what you're most comfortably uh recognizing today in the industry such as kill chains miter attack Etc we organize the same discrete data points with terms like initial access execution and persistence but what did those things offer in us they're giving us understanding that there is a sequence in an attack an attacker has to progress through particular objectives and if we further look at the arrows of Direction the letters know what is the actual attack path that these data points are involved in this effectively shows us that without context it is nearly impossible to take effective actions with discrete data points so what is the key takeaway now
from Context that has given us when it's telling us one thing Defenders when they have a good understanding they can characterize the threat and if they can characterize it they can express the actions to be taken against it and then they can express those actions then they will be logically able to conduct the actions to neutralize it and that brings us into how do they evaluate those actions that they need to take here's the same progression but this time we're going to add the security defenses that a Defender has actually purchased in this particular area okay and these green Shields represent products that have preventive capabilities they can disrupt they can block they can neutralize things and the
Blue Shield represents passive Technologies or capabilities they just observe they just attack they're not capable of blocking so with this very same attack sequence the attack the attacker could continue to come through but the defender can now begin to evaluate how to take the first action perhaps with an application change control program as we're seeing there a Defender can restrict which applications execute a particular types of files in some organizations maybe you don't have this ability to actually you know enact such an action well perhaps you have an antivirus or an Epp and hopefully if you have threat intelligence then that particular product can disrupt item number two okay in some of the areas you may not be able
to implement highly restrictive policies your organization might be more aggressive in blocking at the network layer with firewalls or proxies then in that situation the proxy can interrupt this doesn't represent the eradication of the threat but it demonstrates that you're capable of disrupting the objective of the threat now once you receive this you kick it into your response mode and go back to the endpoints to neutralize items number one and two at a bare minimum you must always as a Defender have situational awareness and that's what edrs are really fantastic at they can't block but they can actually record it's the equivalent of your surveillance camera being turned on monitoring your house and its entry
points and then if we understand all these aspects we can mix and match and combine flexibly the types of actions that it takes once we have the context about the scenario and we understand the terms or the characteristics of the threat okay so I just saved all of you a lot of time study and defense in one slide and I hope you appreciate this but let's go a step further it's one thing to have context and being able to understand threats the defender has to again communicate and express their knowledge of these threats so that they can coordinate across the Enterprise and it's challenging to do that with stakeholders at the executive level or stakeholders at the Tactical
level or even peers who you're supposed to be working with in I.T it's a tough job well I'm going to show you a way of how you can actually Express these situations and it always starts with a scenario hypothesis right and this is going to be exciting now for all of you that like code so here's a hypothesis right a compiler executable achieves credential theft within memory you're doing this with memory so you might hear industry terms like filest attacks right so credential theft within memory from a process in Windows called lsas.exe and that results in unauthorized privileged use in other words the credentials that are stored in that process can be used across the Enterprise because they're
stolen right so this represents back to mckinsey's risk-based cyber security it is intolerable should you actually have attackers going throughout your environment in an unauthorized manner impersonating your privileged users okay so we're tying those two together here's an example of a real world threat yes it's mini cats but the importance is that the scenario counts for any type of program that looks to achieve this by abusing lsas so here's the source code letting you know there's a Windows API system called open process and this is a source code so you actually can go use this awesome tool called code search so you can see source code at scale from millions of repositories but essentially this is the code
that is called a system call open process and then on the top we're seeing SE debug that is a very special privilege that allows programs to actually read the remote memory of another process okay as you walk the memory you cannot achieve that without having that privilege and using this system call great so this is a real world weapon let's actually see how to understand and characterize this weapon and express the defensive actions that are needed against this hypothesis so we're going to introduce you to a structured thinking model which is called the expressive threat capabilities model I am an endpoint engineer here at Cisco and in other places where I've been and I'm representing to you the way uh my
colleagues and I see the battlefield of an endpoint this is the same for Linux Mac or Windows this represents 13 specific dimensions inside of a computer system that an attacker must be able to abuse so that they can conduct an attack look at that visualization it's extremely important to see that attackers have to work really hard the myth that they they can actually achieve things really well they can only achieve things you know one time of of the uh percentage of their attacks this is not true this shows us that the Defenders have immense abilities to disrupt the tax once it arrives in the computer system so this effectively represents the attack capability progression the
more than attacker can use one of these entities the more intense the attacker will be so that now brings us to the next point we need a way to characterize or represent the offensive actions from the adversary and we call those the intensity range naturally if we have the intensity range representing the attacker we need to represent ourselves as the Defenders we are in the counteract range and in the counteract range we represent the abilities or capabilities that a Defender is capable of taking during the attack so you probably have heard this uh in school that every action causes an equal and opposite reaction that's exactly the inspiration for this particular model so let's see it in
action practically back to the credential um you know I guess theft binary the first thing that the binary needs to do is execute and by default of where it's executed those dotted lines are showing you that the program that executes inherits the identity the group that that identity is assigned to and the privilege that is assigned to that Identity or group but notice most importantly entity number eight the system call showed you open process that's the first thing that needs to happen if that program conducts the system call because it has the right Privileges and it succeeds then the program will be able to read the memory and once they are in the memory they can
now begin to enumerate the running processes they're walking into memory neighborhood knocking on doors in that neighborhood and saying are you L SAS are you lsats when they find lsats now they'll begin to enumerate the credentials so this hypothesis as you're seeing it right there effectively is represented from how the adversary designs the program in this manner that we're visualizing for you okay so the next part of how to use the expressive threat capabilities model is actually based on walking the attack like here execute focusing on the number of the entity that is the highest in this case the system call and you must take a defensive action you must take a defensive action as Carlos an
experienced Defender I'm going to take the restrictive action and I'm going to try to apply it to the privilege because if I remove that privilege I know that the system call will not be successful and here's an example of how to do it applied with Native technology that we have in most of our environments if you've never seen this particular GPO setting it comes from the user writes assignments and this is the default state in every single one of our Enterprises this the privilege called I'm sorry the outrights assignment debug privileges by default is configured as it comes out of the box enabling administrators to have this privilege so one way to now restrict is to change
the default administrators to the appropriate group that is allowed to do this type of deep technical troubleshooting such as your service desk or perhaps your Enterprise admins if you effectively change that setting you have reduced the attack surface from any user that has admin rights and the general population significantly in otherwise leading us to know that the system call will not be successful by any program that chooses to do that so if we do that essentially no one can walk the memory except the designated and approved staff like technical escalation support staff okay so you keep using this model you'll notice that in the read and enumerate you can now use a less intensive approach of
blocking or restricting things in your Enterprise you can now add a compensary um control such as something like an EDR that detects um you know thinks for you so you can contextually enrich the investigation and one approach that you can do it if you don't have an EDR is going back again to the native technology and you can apply these three settings number one start logging every single process that executes in your environment number two add the command line arguments of process executable but number three is the key that is the gem of divisibility the quality you're going to get the adjust token uh privileges aspect this tells you when SE debug is probably going to be used by any process as
executed so just by doing that you have successfully given yourself lots of disability of processes that are attempting to do nefarious things in your Enterprise very low cost this brings us back to McKinsey when they talked about optimizing the defensive layers I showed you two ways that if you don't have commercial products you can do it straight with active directory and gpos to start improving your particular particular situation in accordance to this hypothesis great so this particular model now has told us well our defensive plan against this hypothesis is comprised of restricting and detecting so let's double down on that we said earlier that having the technological capabilities doesn't always allow us to know what is going to be the ultimate
effect so here I just want to highlight is the defender once they have the capability they must do this assessment in relation to the attack life cycle that is before it happens during its occurrence and after it's happened so if you apply these settings that I just talked about in the before you have this type of attack happen then you're effectively being preventive meaning you're proactive but again if you do this during the attack you're no longer enjoying enjoying the productivity of this you're actually reacting and you're containing as you're going through the anxiety of an attack so this table is mainly to emphasize is that having technological capability is insufficient to defend you must know how to apply
them for the particular outcome that you want to give to your organization and if we put all of this together what does this tell us this tells us that technology must afford the defender a flexible and granular access we want to block things we want to restrict things we want to interrupt we want to disable we want to observe Etc we need technology to accommodate these very flexible needs because we have to formulate defensive plans and the most important takeaway Defenders must have a way to evaluate when they're going to use this for the final outcome so all in summary this is telling us a couple of things this is telling us that defending is basically rooted by having
significant understanding but even after you have significant understanding through context Defenders have to go through a massive effort in expressing how the threat manifests itself and how they're going to contend it so that they can conduct this enterprise-wide defense that the organization needs right so that covers our expressiveness so we're almost done here what are the key takeaways that you should have today from us Cisco secure right risk-based security it's going to allow for precision and pragmatic implementations as you can see I am a technical person I show you either Pro or very in-depth debuggers today no today's session is not about that but I can go in depth of Designing technical interventions by thinking in risk-based
approaches we learned that time-based security it's a fantastic framework that you should actually um check out because it allows you to measure the effectiveness of your program and this is important because if you're spending five million dollars in prevention and another five million dollars in detection and perhaps you spend another 2 million in response you're likely going to want to understand what is the value that is being derived from those investment TBS can help you establish effective security system design okay next we learned that Defenders require context but most importantly context is not just context is King it is the foundation of how we can effectively defend without it we can take actions but we don't know
how effective our efforts will be last but not least I want to emphasize that the role of Technology as we're assessing tools open source commercial off the shelf open cost Etc we need granular and flexible usage of controls because as you just saw depending on the attack's life cycle whether it's before during or after we may not be in a position to maximize our defensive action plans so technology must accommodate that need of using technical controls in very flexible ways to control the environment okay and so with all of that said I want to thank you besides Calgary you're a very vibrant security community uh I am out there in Twitter I can be available anytime through Linkedin





