Extortion, Chaos and Needless Busywork: Vendor Risk Management

Show original YouTube description
Show transcript [en]
good afternoon my name is jim nitterauer i am director of information security from greylock i hope you can hear me and this talk is entitled extortion chaos and needless busy work aka vendor risk management so how many sure sure russell's gonna interrupt all right
cool all right now we've got all the formalities out of the way all right so what we're going to talk about today we're going to talk about who who am i what is vendor risk management kind of give you a brief overview of what that is why did i decide to do this talk other than the fact that russell begged me to do it and said it was going to be the best one here and i don't believe that for a minute he was just trying to sweet talk me what are the framework requirements why do we even do vendor risk management in the first place we're going to talk about some real world stories from my
current position in a former position we're going to talk about what really matters for vendor risk management and we're going to talk about what how to fix that problem and get some input from folks here in the room because i don't know all the answers all i can do is relay what i see and what i see the problems being so a little bit about me i started an internet business in pensacola florida back in 1996 it was one of the first web hosting companies in the united states a company called creative data concepts it became grid south networks i merged with app river i've worked for app river and zix for about 15 years i've been involved in
infosec probably longer than some of you have been alive but infosec wasn't a thing back then so we just called it hey we were just doing sus admin stuff right so but i've spoken at quite a number of different conferences all different areas my expertise was in dns when i was working for app river system engineer on their security team and then also on their spam filtering so a little bit about my background but what is vendor risk management what why is it important how many of you are involved in compliance or security and you have to do vendor risk management that you're a vendor and you have to provide that for your customers or they ask it from you
everybody right pretty much everybody does that why do you do it
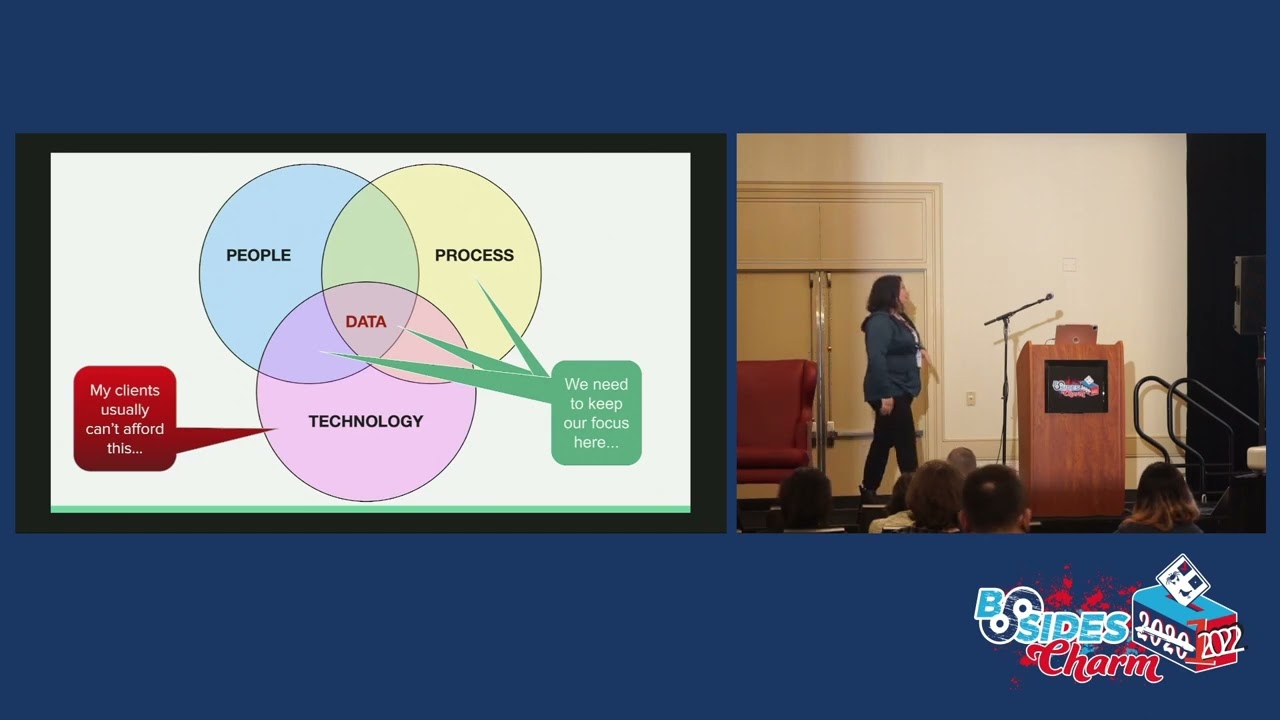
that's that's exactly it right nobody knows why do we do this right what what is vendor risk management right it's it's the ongoing process of identifying managing and monitoring risks associated with a vendor or supplier the problem is a lot of us are security minded and those risks are more than just security related risks those risks deal with security obviously but they also deal with health and safety compliance risk reputational risks financial risk operational risk things that deal with strategic movement for your business most organizations refer to this special publication 837 when they're looking at how to do risk management or they look at the iso 31000 framework for their risk management guidelines then this documents are available for
free if you want to get the iso documents you have to subscribe to those and pay for them so they do have a cost involved with them but all these different risks go into determining how a vendor is going to impact your business or how you as a vendor are going to impact your customers business right so that's why we do this you know everybody has a service level agreement or a master service agreement that they provide for their customers you have an expectation of service from your vendors and we do this risk management process to help understand where the shortfalls and where the things that we have to look at to make sure that our business
can meet our expectations and that the customer's expectations are being met if it's the other way around so what what is what what isn't vendor risk management well it's not a hey you got to fill out this questionnaire thing it's not a completed security form it's not a security score from a particular vendor when i'm talking about those vendors we're going to get into we're not going to mention one that's in the room but his is a little bit different his is a little bit more useful than what most of them are but there's a number of them out there bit site security scorecard iss all of those vendors will give you a security rating
based on what they see on the public internet based on your business we'll talk about that in a little bit going forward vendor risk management is not one size fits all you cannot say here's my process and every vendor has to do this process come hell or high water if you don't do it i'm going to stop my feet yell and scream and make you do it that's not good to risk management right the process has to be different it's not checking a box why do a lot of people do it you said because they ask us to okay just because they ask just because they say jump off the bridge are you gonna do it
right i mean that's what it comes down to right you have to figure out what makes sense for your business to provide for your customers and what makes sense for your customer or your vendors to provide to you and it's not a once a year exercise because risk varies over time right think of what what just happened overseas recently right all of the stuff going on in ukraine do you think people are waiting a year to reassess the risk with their suppliers in the ukraine or people that are related to that they better not be or their business is going to be in bad shape right so following a compliance framework that says you have to do a
vendor risk assessment every year is foolishness if you're living in a world that changes in real time many organizations do a lot of things like outsource their vendor risk management to a third party and these third parties in many cases simply grab a bunch of questionnaires throw it at you as the vendor get you to fill it out then they broker that data back to their client their client pays them a shitload of money to do that and you did all the work for them right so that's one of the problems that i that i faced and what i want to look at here is how do we rank risk and this is something that a lot of
people don't uh don't do effectively they don't look at how risk is ranked and way we look at risk from a an organizational management perspective is risks are based on two things they're based on their current state and then they're based on some sort of future state so a spread and the the likelihood what we do is we consider the likelihood that a risk will be realized and then we look at the impact of that realization of a risk and then we would take a chart like this and and give different ratings how much likelihood or how much impact there could be the organization and every risk would get a score based on that and fall
somewhere in these quadrants on this risk matrix now the the delta looking at a risk the way it is today versus the way it is when it's mitigated would dictate how much money you want to spend or how much how many controls you want to put in place to reduce that risk to an acceptable level and i think one of the things that i like to emphasize when i talk is that people have this false sense that security is an absolute thing it is not all right but i ask people how much security is enough does anybody know the answer to that question just enough the answer is just enough and why is that well that's because you don't want
to spend more to secure your organization than it takes to reduce the risk to a level that's acceptable to your organization why would you do that you don't do it at home you don't have doors that have a man trap and 16 levels of facial recognition to get into the house you could protect your house to that level you're laughing like that's funny but that's what we do in infosec we protect things to the nth level without really assessing what the risk is to protect right we don't look at the risk and protect to the risk to get the the um to get the risk down to a level that's acceptable business we try to eliminate
the risk you cannot eliminate risk so when people in security say security is a thing it's not security is relative to the risk that a business is willing to live with and every business is willing to live with a different level of risk so that's this is how we we rank risk we look at the cost of reducing your risk from its current state to its potential better state that's a control that we would put in place either some sort of administrative or technical control and that those come at a cost we evaluate the cost of the risk to the business so we know that each of these different levels if the risk is realized let's say
it's an impact of severe well maybe a severe risk has an impact of five million dollars a year in revenue to your business okay so to reduce that severe risk down to maybe a moderate risk which might say oh it's a loss of a hundred thousand dollars if that risk is realized right so you've got a big spread there that difference in quantitative value dictates how much you should spend to reduce that risk to that level and if you're going to spend more than that then it's not worth reducing the risk to that level to the business does that make sense okay so why did i do this talk well a few years ago i was working
happily as a security engineer for app river in 2019 app river got acquired by zix corporation and they came in and said you have to do all the security and compliance you have to do a sock 2 report you have to do sarbanes-oxley audits you have to do a pci audit and you've got nobody to do it so jim you're elected to help get us on that track so i moved from my engineering department over to the it department worked under the cio and worked directly with the ciso and my goal was to bring app river into the same compliance that zix had well one of the things that zix was getting from a lot of their customers was a lot
of security questionnaires a lot of interaction with customers making sure that we were meeting their vendor risk management needs and what ended up happening was i was dealing with third parties that were asking me to fill out a 500 question survey when you see the you know the quote up there from kendra nothing says welcome back to work like a 500 question questionnaire from a customer how many have gotten ones like that none yeah you've gotten them right how many of you have like a sock two report or an iso report right do you think the vendor looked at that and even cared no they just said here's the questionnaire fill it out you do the work for us right
so that was the kind of stuff that got me going and looking at this whole process because it doesn't scale when you've got 20 or 30 customers maybe you can do it you know app river had 40 000 customers and they're all starting to ask us for one-off surveys of different types from different vendors some that they made up themselves some that were bought from third parties but none of them were the same and it created a process that just didn't work so what we ended up seeing was we were not meeting customer demands quickly enough sales people were up our butt to get the things done because they want the sale the customer's not going to do the sale
until the security questionnaires are answered so we had them barking at us customers are then starting to use security scores instead of looking at overall vendor risk management and they weren't giving us time to get these things done we're just wasting a lot of time and not getting a lot of success with the customer so we changed things up a bit and i'm going to talk to you about how how we did that but first i want to show you why a lot of people do these things i asked the question why in the beginning well this is some of the requirements why do people do these vendor risk management assessments anyway they're typically required for sock too they're required
for pci they're required for iso and also for a cmmc compliance which follows a government standard there you have to have some sort of vendor risk management in place to be able to validate that you're actually vetting your vendors and keeping them at a certain standard and what what the the problem is these need to be scoped by the business that's doing the assessment so it depends on the type of business that you're running it depends on the type of business that your vendor runs what they're supplying to you what kind of access they have to data what kind of access they have to your infrastructure there's a lot of questions that go into this
i set this up here so i can reach it easier and if you look at for example the sock 2 requirements this is just a couple of them that have a requirement to do vendor risk assessments and when you're looking at the sock 2 criteria if you see the cc that's called the common criteria so that's required for all sock 2 reports in a sock 2 framework you can there's 5 trust principles that you can do an audit on security is required and you can pick any one of the other four uh in this case the privacy trust principle also has a requirement for uh some additional commitments from your vendors so these are required for 2 in order to
pass a sock to audit iso 27001 has similar but more restrictive requirements they're more general because iso certification is built for any kind of business it's not built for just a tech business it's built for any type of business manufacturing service whatever so you have to do a lot of interpretation and if you look through the um clauses that are in the iso 27002 series this is just one of about seven of them that are in there and it tells you the different things that are required as part of a an ongoing vendor risk management program and a lot of them you wouldn't even think of doing right some of them deal with um illegal
regulations making sure that your vendors are following what their legal requirements are what other third parties do your vendors use do they use outside contractors right and you're a lot of you might be in the government space and sometimes you're not allowed to do business with a vendor that uses uh contractors that are outside that are not u.s citizens right there's some requirements for those kinds of things so you have to be careful about that when you're doing your your reviews so let's talk about a few real world stories here i want to relate some of the experiences that we had when i was working at six and when i ended up inheriting the cso's responsibilities at
that company part of my duties like i said earlier involved dealing with customer requests and for security data about the company and the services that we were providing and i quickly learned that the current processes did not scale our customers were sending us proprietary questionnaires hiring third-party organizations like archer and other things to sending us a form log in do this thing and i was some weeks i would get 5 10 15 of these things now keep in mind we already had a sock 2 type 2 report a sock 3 certificate which is a sock 3 certificate just says you have a sock 2 report and we're not giving you the whole report they're kind of useless uh
they have a we also had an iso certification and a pci aoc for a service provider organization from an outside auditor so it's key it's an outside auditor somebody has already attested to the fact that we did all of these things we would lead with these documents and we still receive requests and typically these requests will take one to two days minimum to complete per customer and that just did not scale we didn't have the staff to do that so the first thing we implemented was a development of a diligence kit where we took all of these documents created a few other more detailed security documents put them into this diligence kit and we also provided um
if you look up there it's got a list of what was in there but we put in what was called a gap letter or security statement every quarter of the cso or myself would write all of the changes that happened across the organization that was in scope for the audit and put that into this letter they got our pen test report summaries all the things that they needed to make a reasonable assumption that we were doing the things we needed to do to protect their data we would give this to customers as well as had on our website a whole raft of different things about what we did from a security perspective for each of the different
services so that they could look at that and based on that knowledge then they would have a reasonable assurance that they could do business with us but the key thing that we did is we adjusted our master services agreement so that on our website if you looked at our master service agreement we told them flat out we do not answer security questionnaires people would demand that from us we would point them back to the msa and say we don't answer them they would pound their feet and stomp their feet and pound their fists and say you got to answer this and i said why we've given you everything that we have and in many cases these questionnaires
would simply be a rehash of the entire sock 2 framework asking us exactly the same questions that are covered in that whole sock 2 report in a much greater detail and they were just too lazy to open the document and fill it out themselves so we got the point where we just wouldn't do it for them what we ended up doing was telling them here's you have our security documentation and what we want you to do is we want you to fill out what you need out of your questionnaire and then schedule another meeting with us we'll sit down with you and go over any gaps or questions that you have and at that point then we're done you should have
all the information you need to make sure that your assessment's done you can prove the auditors that you've done it and we've given you everything that you need to make sure that you're comfortable doing business with us and the problem we that we also saw was that we that most businesses once we did provide those questionnaires they never looked at them they get thrown in a folder stuck somewhere when their sock 2 audit came up they would throw it at the auditor the order so you did your vendor risk assessment great we're done you passed right so that was a big problem we did not like that they didn't like it and it was a complete waste of time for
both parties involved and this is just a view of the cable contents of a typical sock ii report this happens to be graylog's sock 2 report from the other year on the left is a table of contents and you can see typically these are rather long reports several hundred pages typically this is a short one by most standards and on the right what you see is one of the common controls and it's broken down so that you see what the control is what the policies are that are in place or procedures how they were tested by the auditor and then what the results were for each of those tests so as you can see it's pretty detailed and there's
typically depending on the number of trust services criteria that you look at there's probably three or four hundred items in a sock to report that you could be evaluated on depending on the scope of the of the audit so another problem we ran across is these questionnaires we we basically again they were they were the rehash of the sock 2 framework in a spreadsheet format fill out the spreadsheet what i ended up doing for most of them it took me five minutes because i would put in the first answer csoc2 report select all the column control d close save email and sooner or later the customers learned that they needed to read our sock 2
report because i was not going to take the time to fill out their questionnaire that was already answered in the sock 2 report but a lot of customers would not do that some of them would throw their weight around the problem is some of these customers are very small they might have been kind of three five thousand dollars a year in recurring revenue others were really large and wanted much more attention but at the same time we had to build a process that that scaled and that's what we ran into was figuring out how to do that so that we could service those 40 000 customers with the same level of um of presentation that we were giving to
the bigger customers now some customers did use something that was called a sig or cig light i don't know if you've heard of that document it's something that's put out by shared assessments you can buy a subscription to it it runs about six thousand dollars a year uh but it's a spreadsheet that um gives you basically a breakdown of all the security things that you could have within an organization but it's it's um it has macros in it so that you can actually if it doesn't apply to your organization it pulls all of those things out that don't apply and you can provide that as a standardized format for customers so we did fill that out
and we did do that for customers but that's a one-time thing you fill it out once and then give it to your customers just like you would a sock to report and we did have a case where one of our customers this was in the finance area they hired a third party risk assessment company do a risk assessment of us didn't tell us they were doing this i get an email like on a thursday afternoon the email comes in from this third party and it says here's what you're going to do for us and it listed out you're going to spend 40 hours in the next eight weeks interviewing all of your internal stakeholders so the people that run the
services the service owners within the company you're going to provide artifacts for evidence and you're going to do all of these things to help us provide this documentation for our customer and i looked at this thing and i'm like you're basically wanting us to redo an entire audit just so you can do this vendor risk management process for your customer this thing's moving here a little bit for your customer so i emailed them back and i said basically let's schedule a meeting we got on that meeting and they started going through their little spiel and i said let's hold on here a second first we're not doing any of that they're like why you have to so we don't
have to do any of that you're not paying for it we don't have the resources to do it and this customer is giving us like six grand a year in recurring revenue we're going to spend more money doing this audit that you guys are forcing on us because you're doing this for this third party that we would make in a year from that customer so we ended up going i told them i told them the same thing i said here's what i'll do you fill out the questionnaire based on the stock 2 report that i give you we'll schedule a couple more meetings and i'll answer any of the gaps that you have in that
process and then you can go back to your customer and give them all the data they want but that's all we're doing and they're like well you have to do this so go back to your customer so we called the customer and just told them we're not doing that because well we paid this company so it's not my problem you paid a company based on what they said they were going to get you get done and where you didn't agree to that we don't have a contract with you to do that and we're not doing those things for you so it ended up that we got through the whole process we kept the customer the customer was happy with
what we gave them they learned a lesson by not hiring this third party to do it for them and everybody ended up being better off but you know most people won't stand up to these third-party vendors and we'll just say oh you got to do all these things well you have to look at the bottom line how does it impact your bottom line and how is it helping your business grow versus how is it detracting from your business and the problem with these kinds of things that we found is we want to be spending our time improving our processes building better security and yet we're chasing off after filling out stupid questionnaires for customers that will never look at them
again in their life so that was one of the that was really an awakening moment for us and the last thing that came up um here for us was talking about a company called bitsight we get it and i don't want to bash the vendor because i'll i'll caveat this with the idea that what bitsight and what some of these companies do has value but the way they run their business and the way they try to bring on new customers is not conducive to growing that business they provide a very valuable service if you wish to subscribe to it they give you a risk score a security score if you will based on everything they find on the
internet that's public facing so imagine you go to showdan you scan the internet for ip addresses you look at aaron for all the ips that are swiped to a company ripe all of these different icann organizations that manage ip addresses then you go find all those resources and you run all of these different scans against them you compile all that data and you give them a score and that's what they're doing here the problem is we got this from a customer the customer said oh your score was i don't know let's i'll throw out a number 750 and they wanted a score of well i used 650 and they wanted to score 750. well to
get to that point we had to see the data so we contact bidsight well you can see the data but we'll only let you see it for 30 days after that you have to pay for it okay what's the cost 60 grand a year to access the data so that we can service this customer and get the score down to a level where they're going to continue to do business with us so we got on there for the 30-day trial we found out that all of the stuff that they had assigned to us as our company owning was not necessarily true we found about a third of the domain names that they associated with our company weren't even ours they
were other companies elsewhere in the country ip addresses that have been used by our company 10 years ago that hadn't been fixed through yes sir yes you're perceptive yeah so you hit that on the head there but um in any case you know that we go through all of the inventory found i p addresses things that weren't even ours that were lowering our security score so we tracked the hours it took and it took about 200 hours for three members of our security team to go through all the data that they had compiled to reduce it down to what was really ours by then the 30 days was gone and now they were wanting us to subscribe to their service so we
could see the data and the vulnerabilities so we could remediate them to get the score into a level where our customer would see that it was acceptable the other problem with it is they give you a score based on the entirety of the organization and the service that this customer was buying was a very small sub-segment of that ip space that had very little public footprint very little exposure if you had just taken the score of that one it would have been at the top of the level but they didn't give you that opportunity so then we come to find out you're allowed to go in there and set up a profile and tell them well which
things do you want to count toward your public score and not so the reality of it is the scores that you're seeing from bitsight are seriously massaged by the people that are getting in there and buying that data so they're only exposing the things that they want you to see everything else is hidden it's under the counter it's behind the scenes that doesn't matter that doesn't impact our public services all of those you know all those old apache servers all that centos six crap that's running back there somewhere else that doesn't matter that's not not important so they only show you the score you want to see but in our case we we weren't a customer so we had no
insight and no ability to change it so all we could do is work on the last report we had and remediate the things well the other problem was their cadence for readjusting your score is very slow so we could go and remediate 15 things in a day and two months later they would reevaluate and lower the raise the score based on the changes they wouldn't evaluate it right away so it was a very tough tough situation for us and was a tough situation for any business that has so imagine bitsight has a customer they have 20 vendors they want all 20 vendors to have a score of 700 or better and most of them don't well now
bitsite's got a way to extort 20 vendors to come on and be customers to get at their data so they can chase after this one customer that wants this score at this level it's just not a very good situation it's just not it's not tenable because beyond the fact that there's bid site there's about four other providers and they all charge about the same amount of money every year to do these things you've got security scorecard you've got iss and just a bit on iss
everybody has a credit score right everybody knows what credit score is developed through i think michigan state or university of michigan and it's the standard for how people's credits rating goes well that same organization is now developing what's called the iss security score and every company in the world is going to get one of those scores and this company is going to be the security reporting agency for the basically for the entire world so watch out it's coming and it ain't cheap to get involved with it so if you can find your iss score and start to lower it now i would start doing that before it gets uh too expensive to get in there and get at
it if you're a publicly traded company it's even worse because the iss score is part of your what's called esg rating how many of you look at yahoo finance and look at stock prices and that sort of thing on there one of the one of the values for most companies in there in the lower right hand side is called an esg rating it's environmental social and governance rating and it's a third party attestation as to how well the company's doing in those three areas through a large set of criteria and stock traders and investors and all of that use those esg scores to determine which stocks they purchase or which funds they invest in so
if you're in a publicly traded company that's a big deal and the last thing we came across in this whole vendor risk management thing is believe it or not there's companies that will automate the security questionnaire answers that your customers are asking from you you can pay these third-party companies money they'll fill out the questionnaires on your behalf send them off to your customers and your customers will get the answers that they provide based on your input so it's pretty bad when we've created a system that you have to hire somebody that's an outside third party to provide these answers to customers just to meet a need it just seems completely ridiculous to me that these
kinds of things happen and this is the way the process works so so how do we get to to what really matters i mean i'll i'll pose the question what what when you're doing a vendor risk management what what matters to you and your business there's a question to answer asking for for input here okay that's one area yep anything else sagan yeah yeah so access the data right what happens to the data or how about i use you for five years as a vendor and then i no longer use you what do you do with my data after we sever that relationship right or you know how much access do you have to our data center how much access do you
have to our customer data how much access do you have our source code if you're a manufacturing company and what's your lead time on the parts to fulfill my orders how's what's that look like over time right looking at a key performance indicator kind of things like that do these questionnaires and do this does the vendor risk management process address any of that so in my mind a lot of this vendor risk management has become a money maker for the vendors that offer those services and they don't really do a great service for the companies that are supposed to be looking at real risk right i mean look at what's going on now for example we have a
a small internet business and we provide internet service in a small part of downtown we cannot buy routers we cannot buy switches there's nothing nothing there now how many people if you go back and look at their vendor risk management of those vendors three years ago or a year ago would have said yeah i worry about whether they can supply my needs nobody's right they're all looking at security related things and now we can't as a business make money because this vendor can't supply us with things that we need because they can't get the parts that they need to fulfill their orders so it's more than just looking at do you have routers and firewalls and do
you have you know do you rotate your passwords and you do quarterly reviews and that sort of thing there's much more to this process and that's that's my point of this whole talk is really to get people to think about how that impacts your business short term and long term and how can we get around that and get at those answers and can you solve those problems no but at least you're aware if you know if you know that this company's financial status isn't such that they could buy enough parts to fulfill the order you might want to find another vendor right but are people uncovering that in these vendor risk management exercises i would say probably not
right so what should we be doing how can we do it better how can we make this process so that we can still meet the needs for compliance and yet help our business actually get some beneficial data out of the time that we put into doing these assessments any ideas russell's got all kinds
now that are ideas what they're calling people they will share their reports from their stock yep
something that i've yep to implement is creating that questionnaire but having someone on my team try to find all the answers
yes in some ways but again it doesn't scale right so it goes on to the next you segue into the next thing there was i don't know if anybody listens to the cso series uh david spark and his group out in california do the cso series every week podcast really good information if you're in security and compliance if you're dealing at managerial levels but this guy nick selby was on there he's the chief security officer at paxos trust and they were talking about this very topic right and his his statement here is really kind of kind of confounding it said this is how we should be doing instead the second half instead we have spreadsheets from hell that are created
by accountants delivered by auditors to measure cybersecurity risk none of these people have anything to do with risk or the assessment of the risk so what can we do to make this easier so and it can't be more than 10 questions tops that's his his take on it right so really what it comes down to is doing what russell said you provide a portal to give people access to your documentation your your sock reports your iso reports maybe you have a sig form that's filled out maybe you have a specific security document that talks about some more details about the controls about a particular service but then you have to go and figure out how if i'm if i'm
vetting a vendor how can i ask them the right questions that are relevant to the scope of the services that they're providing for me and i have actually an example of that i pulled it up on the new i don't want to be active let's see i pull up the questionnaire that he had here and if you look at it it's you know it's got some basic information you obviously have to know who to contact at the vendor the vendor name that sort of thing then they ask first question what services does the vendor provide right i mean obviously if you if you're delivering boxes to somebody via truck you don't have to care much about a whole lot of the
security questions that that vendor might be exposed to then they ask a bit and this is specific to um their type of business yes but what kind of encryption happens here what kind of storage architecture do you use vpns how do you handle lease privilege how do you handle static credentials how do you handle secrets so credentials within code and then how do you handle your policies and your programs do you have secure coding training give us a little details on that now in this case they have a requirement for linter which is used in code compiling and then do they do you do static security scanning of your code you do dependency scanning and then they looks at a couple of
questions that they have is really only 20 questions but that's that's all they ask and then if there's more questions they may dive into a little bit more detail with that vendor on these things but they're not going through that whole 200 300 question ordeal for them somebody could fill this out probably in 15 minutes and get it back to them right and this is pretty benign and pretty easy to do so this is where we have to go we have to tailor the questions that we ask our vendors to what that vendor provides for us and what the risk is to the business right i mean you know if they're providing bottled water to our business
you know all i need all i care about is how do they vet their employees that are coming into my office space that's really all i care about if the water doesn't show up it's not the end of the world i can drink water out of the spigot right i mean i wouldn't spend more than five minutes vetting that vendor now if this is a vendor that's you know bringing in outside consultants to work in our you know pci environment and they're logging in and connecting remotely and doing all those sorts of things i'm going to vet that vendor a whole lot harder but again one size does not fit all so that's that's really the point of getting at
this the vendor risk management process has become this hey we're the we're the managers of the company you guys that in it and you guys in in security and auditing have to do this thing this way and if anybody deviates from that then tell them to go screw off and they have to do this thing and it's like it just doesn't work and we have to get to the point where we're assessing the real risk of the vendor because i i would say that we're missing a lot of the big risks we're not covering the real risks that matter with every vendor right if we're spending all this time we're just pulling the wool over our eyes saying
we're doing a process we're doing a good thing but when you know what hits the fan somebody's going to go back and look did you assess this vendor correctly and maybe we should have done a little better job doing this so that's really the point of this whole talk and i i don't have anything else as far as content here but getting to the last last slide here how do we fix the problem these are just thoughts questions thoughts i can put this back on full screen because it's showing a little screen there we go so getting it getting it the whole idea how do we get past just checking a box for compliance right
that's why we do it that's why we have to do it but the reality is why we have to do it is because we want our businesses to prosper we want our businesses to know what the risks are when it's operating we want to be able to have a plan to get around those risks if something critical happens to the business it's not about just compliance it's about the impact and the down the road path that it has on the business our security scores all that matter i would say probably not there's more to risk than just looking at security scores now again going back we're all in security so that's probably top of mind
but there's a lot more to it than that what happens with those questionnaires what value do third party vendors provide some do good good work some don't you know russell brought up the idea of having a portal where you can provide that information and we we use one of those at greylock and it works out very well when customers ask for something i give them a log into the portal it provides them all of their information and then we meet after that and go over any other questions and concerns that they have what are the five to ten key questions you can ask as a risk assessor to get at the at the level of of um
[Music] sophistication of somebody's risk program or of their security program in general you know how do we stop evaluating these audits the audits that we're doing i mean they cost a lot of money you know a stock two ought to 25 30 000 for a small company it's not that's not penis it's plus the time to get the audit done you know a pci audit could cost that much or more depending on the scope of the audit and by then by your customers not valuing that or not understanding what those audits mean we're just wasting that money as well you know some vendors simply presume uh the businesses are going to purchase their services because they come to
market i mean you know we got rsa coming up in in uh june right how many of those vendors will we create something new you got to have this thing to be able to secure your network right or your your business probably not you know and some how do we make how do we make these processes efficient and scalable i mean if you've got four or five vendors no big deal but if you start having 40 000 customers asking you for your security posture you know that that's a big deal and i think amazon and some of those companies do it well and i doubt that they would they would submit to anybody asking them a security
question they're going to go here it is on our website this is what you get you get what you get and it's there but they do a dang good job of putting it out there so that's all i have but if anybody has any questions comments i'm here for a few more minutes i'm got 20 minutes left so back there um
so you're doing like pre-audit assessments to get them prepared oh full audits okay cool yep
okay okay so you're certifying the auditors okay
um
um
it depends on the vendor and i guess my whole point is you know the sock 2 sets a baseline that should give you a an overall assessment of security posture so that you can spend the time asking the very questions that you're asking right the deeper questions instead of making somebody go back and say do you do these things you've got that already covered you've got the baseline you've got a good solid here's what we do generally here's our policies procedures our governance now if you have more technical questions and that's where i was going with creating a more service oriented security statement about a particular service so let's say it's encrypted email we use xyz encryption the the
data is stored in this format the keys are stored here here's how we do access control getting at the meat of all of those questions that you would be concerned about right
yeah and the problem i saw with a lot of them was people would purchase something like one of the services we offered was spam filtering well they would offer what kind of encryption do you for spam filtering none it's i mean this question is not relevant right so so the question has to be tailored to an understanding of the services and that's where the disconnect is the people asking the questions don't understand the technical implications of a service so they just throw some really technical survey at somebody and the person looking at goes this makes no sense from the context of the service that we're providing to you in this case
yes
is
middle to lower and i think it just shows you that you paid attention to it and you've covered the basics you've got the governance in place you've addressed the security you're concerned about those things and now maybe the implementation of more technical controls has to have a little bit more scrutiny like what you're talking about but if you don't even have a basic you know understanding of how to do the basics from a sock 2 perspective or an iso perspective they're not going to have a clue about the other things and even if they have all those technical controls in place the business operations are going to be such a mess that i wouldn't trust them to begin with
right i mean it doesn't matter how encrypted the data is if they don't take care of their laptops or if they don't take care of their governance process or if their hr processes aren't solid so i guess i see it as kind of a tiered approach and that's sort of like the five layers of maturity and you know and that and that are is it repeatable is it you know all of those things and really sock two is kind of in that one and a half to two and a half range on that scale that's kind of the way i see it and most businesses that are small vendors can't afford to even get to that right and that's and
now you've got things like cmmc compliance that are going to come down the pike so anybody that's doing you know work for government contractors going to have to do that you're not going to have an option and once they certify the auditors it's going to come pretty quickly so i hope i answered your question but and i'm not saying it's you know i'm not saying that stock 2 is the only thing that matters but it's really it's about building the trust to a level that's here now we can dig into the stuff that really matters as opposed to saying well do you do this thing and this thing in this thing well yeah we do all that
stuff so let's now get on to what really matters and separate us from just the basic business operations anything else i appreciate your time looks like we're already open they're not over i've got 10 minutes left but anybody have any other questions comments concerns
a number uh
yeah and i'll tell you one that's better if you go look at risk um security scorecard that's much better much better detail much better relevancy so yeah but it is good for that and if you get the value out of it that's what matters right
that they need to step up their game
that's a question that that has to be answered by the people that run your company right they have to understand what is at risk tolerance what are they willing to live with what risks are they willing to take and if you come to them and say hey you know this guy's running a server out of his basement on a you know a cable modem with no security not behind a firewall it's got our critical you know pii for our employees on it and your upper management doesn't see that as a serious risk then i think it's a hopeless case um but you've got to train you've got to train the upper management the executives in the company to look at
risk that they they own the risk and they don't know it right a lot of businesses the the upper level management doesn't understand that they own the risk and there's that whole area of due diligence and due care right and once they're aware you've done the due diligence you've found the risk now they know about it if they don't exercise due care they're negligent or could be criminally liable for anything that happens because of that and i don't say that to be like oh it's black and white it's not but it's a serious serious attention needs to be given to those risks that you present how do you present them well i don't have it in this slide deck but
go look up how to do a bow tie risk assessment so you would go and find a list of risks and pick every risk and then put it through this bow tie exercise and it's a good way to communicate to your c-level folks what happens if a risk is realized what are the controls we have in place now what kinds of things could stop that risk from happening if that risk is realized the center of the bow tie what does it take to recover from that risk and then how do we measure that risk over time is it getting lower or higher and we look at that over the long haul and that's the language that they
like to understand right they look at key performance indicators they look at dollar values to the business reputational risk they don't care about technical things if you talk to them in technical terms the c-level folks are never going to respond to that right they they they care about dollars and reputation so if you can convert it to that i think you'll you'll get some leeway and getting them to pay attention to it how do you get your vendor to up their score i mean i don't know that's again that's for your company to decide but you know my case i look at them and i i look at we we have minimum standards and if they don't meet those standards we'll
look at the exception to try and figure out what it is is it really a big risk or is it just some oh hey one off you got this company over here that's lowered your score to this level but again we don't look solely at those security scores either right we need to know that there's somebody in that company that understands that they're managing risk they're managing security for that organization all right i don't have anything else any other questions
[Applause] hmm [Music]