The Cat and Mouse Game! EDR and XDR
Show transcript [en]
[Music]
[Music] thanks everyone i'm always excited to hang out at b-sides and um and obviously been a presenter at both b-sides edmonton and calgary so i love the the atmosphere i love what it's all about um this session is really about cat mouse it's a little bit of perspective around edr um and xdr and um you know i love you know the whole thing with liam nielsen right i've acquired a set of skills over my career and you know let me find you and i'm gonna well we're gonna we're gonna be able to figure out what's going on you may not be able to find anybody to take care of them but um but the exercise here should be
interesting if you've not been through this before all right so um i know this one's a little bit dated but it's it's one of my favorite ones out there not piece of and i like just to frame it before we get into the meat or the details of things but um and you know i start this a lot so some people may have heard this before from me uh in in another talk but not pietja is interesting in itself because it had a lot of different components to it um it's also uh i believe supply chain driven as well but um but the the interesting things with not piercia was is that you know all all it needed is one area within the
organization to get in so you could patch 99 of everything and they find one and uh you know the game begins and um and with this particular um attack it it not only you know popped a box that exploited the vulnerability with this within smb but once it was on it then it used mimi cats like um capabilities to harvest credentials and then log into all the systems that you may have patched anyways um and so um it's interesting because you've got lateral movement you've got endpoint activity you've got perimeter stuff that you've got to bypass you've got exploits that are taking advantage of a vulnerability there's lots of different pieces here and think about it
the adversary needs to be writing a lot of these in order to be successful so we have an opportunity to mitigate these types of things because all we have to do typically is you know belt one out of the air and the game is over and so when you when we're going through this think about if you had not pietcha ii or something similar right um and so there's a couple of questions you're going to ask or be asked and that is do we have protection mechanism in place to mitigate risk um and have i been targeted and if i have been targeted this is really what we're gonna dig do i really understand the story now
we're not gonna uh you know do not piece i'm just gonna provide an example of data points that you might think are good enough or you've got a good idea of what might be happening but in fact there's more to the story and you're probably into what's happening is you might mitigate what you believe is the risk but you see constant reoccurrence of the threat um and it's a the cycle game right that you're continually finding a little bit more mitigating it the adversary is getting past that or has another way of doing it or there's multiple elements that you haven't discovered um and there are obviously opportunities for for the adversary to continue um as we go through this think about
this other element called low cards exchange principle um and you know i'm a big believer in this so this is forensic science this is the sherlock holmes of france and basically what he says is it's impossible for a criminal as an example to go into a crime scene or leave a crime scene without without either leaving something behind or taking something from it and therefore there there is an opportunity to discover those elements and and get a night they've been there um and so think about this it could be well hair follicle maybe not mine at least not up here but maybe down here right like a hair falls into a fiber carpet and maybe it's a tiny piece of
hair and it looks like the fiber carpet um very difficult to find but if you have the right tools in place you can certainly find that then you might have some dna and then based on dna you might question individuals they might say they've never been there ever in their entire life and maybe you have a dna bank with their information and there's a match and now you know they've lied to you now that doesn't mean that they've committed the crime that just means that they were there most likely at a period of time and maybe you need to do additional scrutiny or investigation and so when we think about systems exactly the same thing right it could be
residual it could be a registry entry it could be a mutex on a box it could be uh a an ip address or a flow um that that took place at a particular point in time but really trying to collect all that data it's tough it's a tough game especially with kovitt now everything's remote and so it even gets harder right everybody's working from home but ultimately the data exists now if you don't have access to the data as an example dns data dns is being queried all the time in order to operate if dns data is being sent to an isp when the user is remote well if that's where it starts that's a
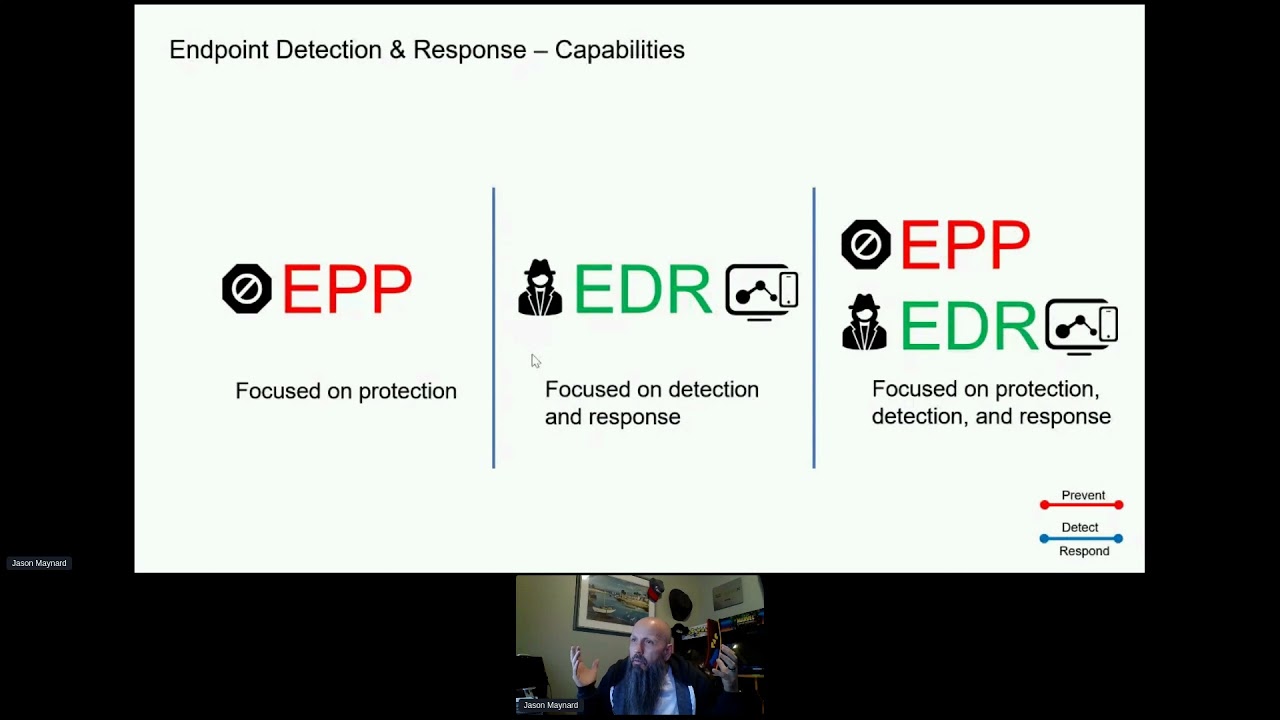
missing piece of the puzzle you don't have and so you certainly want to try to centralize that data collection regardless of where the asset or individual is it's in the data center on premise and the cloud doesn't matter you want to be able to have data the data is the new gold right or the new oil right endpoint detection response so this is specifically an area we're going to focus on and then we're going to showcase the value of edr and what edr provides but it doesn't provide the whole story and that's the problem and we'll walk through this so endpoint protection um or epp it it is what we used to have right traditional av and it might have
firewalling components it might have usb check and all that kind of stuff right so that's that's kind of the epp market and that's where most traditional av vendors have sat and then you had this new market with endpoint detection response and at the start of this this was more complementary to your epp so it wouldn't replace your av functionality typically it would be there to enhance it to provide advanced maybe threat protection but it but but its main focus was around detection and response right what happens when a file is executed on an asset right what what exactly happens and we're going to talk about that and then you've seen this you know people started questioning why do we
have epp and edr why can't we have a consolidated offering and now you see this emerging a market around epp and edr now really coming together and quite honestly i think it's being led by the edr vendors right the edr vendors that started in the edr space are really driving this because they're very good in that area and now they're adding the you know the traditional epp functionality to their platforms so that's kind of where we're at most people are really looking at this area in consolidation but if they have an investment in epp um they may just add edr as uh the uh the stop gap and then look at maybe consolidation once the um
either the product matures into what they might have on epp or or they might wait for the epp to expire right the life of the subscription that they might have and so when you look at capabilities this is going to get a little bit detailed here but when you look at edr and epp i i really don't care too much about the epp portion i'm not saying they're not valuable but as threat hunters and defenders you know that stuff's batting the easy stuff out of the air right that that's that that's commodity-based stuff for the most part what i want to get into is some more of the advanced capabilities right the things that really going to
differentiate me when an incident happens right that's going to give me the tools and power to really figure out what's what's happening and i'm going to add the human element to it so you've got things like you know quick easy shot 256 matching right so you want a global database that you can reference um and do quick checks right that's easy commodity based stuff so to speak right static analysis so this is examining the pe headers uh looks for dll imports the heuristics engines are usually here as well you got malware file analysis this where we get into dynamic analysis right grab a file throw it in the sandbox detonate it and look at what it's actually doing
and then based on the behaviors of that uh i might have a good indication of of of risk there and therefore maybe want to block or mitigate that vendor threat intelligence cloud obviously a third party and the vendor itself are going to hopefully further enrich the the technologies and platforms that you're using to defend and edr is no exception here all right as we start moving up the stack we're going to start getting into a little bit more advanced capabilities um and so exploit prevention so randomized memory structure so if if for example there's a an exploit within firefox the memory location that's where i'm going to jump to to run my arbitrary code to exploit the system
if that's randomized uh it's not going to work right it's going to mitigate that risk i would want something like that it's going to also help with fileless malware so things that run in memory right not resident on disk that you can scan you've got malicious activity protection or behavioral analysis so this starts getting into things like if for example um something happens on the you haven't been able to detect it with other means and it starts encrypting the drive at large volume right and and the file names are you know common all of a sudden then you you could detect that you might lose a couple files but you can kill that process um and ultimately stop the encryption of
the drive this is an example of malicious activity protection and behavioral analysis av engine obviously going to be there again the commodity based stuff fuzzy fingerprinting this is going to help with polymorphic type uh threats cloud-based ioc so this is again further enriching um uh what you know and so what what do you mean by cloud-based indications of compromise well if you can document the command line that's passed to powershell that command line provides information that information can trigger a cloud-based ioc or even a defensive capability on the box and at least alert you if it didn't mitigate it um and so that's where you can get into some cloud-based intelligence as well device flow correlation so this one's um
i always use the analogy you are who you you hang with right and and i remember being told that when i was younger and i'm i'm thinking maybe everybody here has been been told that unless it's just me but um but um but the point here is is that if you have a file as an example that's making a connection to a known bad ip well then even if you haven't detected the file is bad there's a good indication that it is bad and um and therefore you could you certainly can start mitigating the risk there system protection um so this is where we get into uh process injection and making sure you know that exploitation is not
going to take place you've got script protection that um you know if there's a script-based type attack you want to mitigate and then be overall behavioral protection so the other one was analysis and malicious activity protection this one starts looking at um as i mentioned earlier files registry network events so a collection of all of those capabilities and then maybe there's an indication of compromise so device flow correlation is more around negativity and really center around that behavioral protection expands that to include more elements and then you get into things like continuous protection so retrospection um and that's back in time um and so what that means is is that if uh in fact you do have a file that comes
in that is able to bypass any of your controls um you might get an intelligence later to know it's bad and so the good thing about that is is you're gonna hopefully block all net new the challenge with that is does it tell you about something that came in 30 you know 30 days ago seven days ago five days ago whatever it might be right there'll be a time limit and how far it might go back but the goal here is is that you want it to tell you that wait a minute five days ago we seen this file this file actually at the time was unknown we now see it as bad we've quarantined
it but it was in the environment you might want to do additional forensics on that asset you want to observe behavior of clean and unknown files on the system so this is one of the challenges i see right is that if you're only looking at malicious files what about clean to clean processes or unknown processes that are that are on the system itself they may turn bad later and so if you're not um you may miss that can i quarantine obviously mitigating control and then observe interactions between files to determine suspicious activities uh as a whole and then watch network traffic and isolate c2 and data exfiltration elements and then advanced response forensics snapshots endpoint isolation
being able to use things like os query and do advanced searching and then automation these are typical uh capabilities that you might want to consider when you're looking at epp then they're plus and minuses that um i might have missed or add but it gives you an idea of that and then ultimately threat responds um and we're going to talk more about threat response in a second so what i thought i'd do is actually let's just go through a very simple uh investigation together let's hang out um and and walk through this and think about this in your environment think about this like not of two and so what's gonna happen is is that you're gonna get a uh
a uh help desk ticket maybe right because somebody had discovered this command prompt and i keep looking this way just so you know this is where my other monitor is so i'm just bouncing between the two and my videos here i couldn't hear what you said well you're not supposed to be listening siri um but anyways um so you've got this ticket that shows a screenshot so the kudos to to whoever sent this maybe this is an individual an hr and they sent this to you because they saw it and they were like what's this um which is great now what is a little bit about probably well the file name because you can see that here
about the operating system because it's a corporate asset and you know it's jack tripper i might be dating myself there if anybody knows jack but jack tripper is the user and we know that the user has claimed that they have no idea how this was launched they have no idea so that's what we know so what do you do what's our next step do we just look to block the files right or do we want to really find out what happened and this is where edr really comes in and so what we do is is that we have a timeline and again it doesn't matter how a vendor displays the data it's just how to get to the same result
doesn't really matter but you have resume.exe so the first thing you'll get is a sha and now i have a shot 256. so i now can use that information to query all kinds of product right that i have in my environment from one vendor multiple vendors there might be a little bit of work to do that um or maybe it's pretty easy depends right but now i know the shot 256 i know it was created i know there's a retrospective event the creation would be highlighted and in this case it's powershell so as uh as a you know investigator an analyst a defender red team it doesn't matter who you are purple team right this is at
this point now interesting right powershell is responsible for resume.exe and so if you scroll back a little bit you will see information about powershell and powershell's telling us that actually the command line argument passed was that it went to red.space gives us the port number now many people might say 8080 we don't wouldn't even let that outbound think awesome right that's exactly what you want to do right if that's not a web-based port that you support then you probably shouldn't let it go outbound anyway right and restrict it based on porter application problem with application here is it's http and it would have got out if you're just doing application control um so again proxy could help here but
what happens if they're off premise and this is where it happened do you have the same levels of controls there as you do on-premise i would say most organizations don't um and so there's a great risk that this could happen um but anyways so they went to red dot space port 8080 they downloaded a uh a payload called resume.exe and it executed the process so we know that and so that's awesome that's that's if great information and then we get a cloud-based ioc as an example that says that this was actually a macro from a word file that launched powershell right again this this helps with all that command line insight that you're being that's being captured and shared
and so um that's pretty nasty so far we don't know what the impact is to the organization but we know that this is definitely uh nefarious right it's bad um and and so when we scroll back we know windward powershell macro uh sorry windward macro power shell resume or sorry red.space resume.exe and then start the process we know that already within a few minutes i'll just check here yeah within a few minutes now it might take a tiny bit longer but you get the idea we've got some great insight that your traditional av may not provide you right it tells you whether or not the shot was bad or if it was quarantine or blocked
and you might have the ability to go right click and mitigate the risk but would you stop reinfection here i'm going to say you're not because you don't know where the source is you know that there's a word document involved and so there's some risk there and as we go along as we go along um we want to know a little bit more right nobody here wants to stop at this point in time or you shouldn't now you might say this is more information that i get today and that's fair but this might be a great way of showing why it's very important to invest in something like edr now we'll continue the journey but what do
you think we want to do next anyone okay everyone else is on mute and i don't see the chat or questions at the moment so i'm assuming everyone's saying i want to know how windward got launched that's that would be interesting to me and so therefore we would want to see what launched windward and we'd scroll in our timeline and we'll see the relationship between windward and explorer.exe and look at this we see the command line windward.exe c users john doe desktop resume doc m ah doc m that's macro wait a minute that aligns to what we got from a cloud-based ioc um interesting right but now we know what the source of it is
and so that's great because now we know um resume doc m was executed somehow and then explorer does its thing to get wind word ready and then a macro gets launched and then powershell gets invoked and then goes to ret.space and then downloads resume.exe and then starts that process and we don't even know what happens after because we're not going this way we're going backwards at this point in time but that we would have to go forward to figure out what happened was her data exfiltration um did it move laterally all of that stuff and you might say well wait a minute if i had a good product that would have mitigated the risk you're right it would
have and i don't know good product is the right answer here because every product is going to fail meaning nobody's going to provide 100 prevention and therefore i need a tool to be able to tell me the whole story i can't just you know think i'm going to block everything and again you might say well wait a minute this one looks pretty easy that maybe it could have been blocked right it would it would have maybe in most products but then i wouldn't have a story to tell you right um so we need to let it execute fully in order to show the path but as i go along here the next thing is what what's the next thing
anyone is anyone screaming in caps we need to figure out how resume doc m got launched how did it get launched was it the usb key the user just went in and clicked it was it something on the file share or did it come through outlook through email created by outlook now look at the story we have we know now imagine telling and building your root cause you're saying okay we know we got an email we don't know who it's from yet right there's some some questions i might but i know i got an email jack tripper open the email there is a document in the email it got past our email security controls double click the doc m macro is
enabled which launched powershell that went to red.space downloaded resume.exe and executed the process that's what i know that's empowerment that's giving you the tools that you need to figure it out now can you get this all through automation not today right there's still a human element that's required this is where the analyst comes in that's where the value is so that's great insight of what's happened so far and in summary we know what's happened here but let's just jump into the actual file that we're going to reference in a sandbox environment i'm using the example some people might know the screenshot or not it doesn't really matter your sandbox is a sandbox if you can provide telemetry and information
about the file being executed it's it's more data the point here is is that there's information here that's valuable um a couple of things one is um i get to know how it was executed a couple things that i might want in a sandbox is things like an exit node in canada why well malware writers especially at high-end commercial enterprise accounts and um public sector uh high-profiled customers have been attacked and they are looking specifically for a canadian exit node so they're they're basically looking wait a minute i'm not going to detonate if i'm not coming in in canada uh or out of canada um and so if you detonate that in a different sandbox there's a good chance you're not
going to see anything because it goes benign if it finds out that it has an ipv it's very trivial but it's something that adds a little bit of value but the goal here is to see the behavioral indicators now right away i see poison ivy default mutex okay so now i know what family it's from right and there's some other things that it calls out from a behavioral perspective you've got dns data tcp ip streams extracted domains processes artifacts registry keys created keys modified keys deleted keys file activity all good stuff if there's reference to miner even better right now i can come into mitre uh and see wait a minute here's something um that
is um is um uh maybe has persistence and what technique not only the tactic but what technique might have been used and also some mitigating controls right that's that's valuable as well um the other element here this is this is a behavioral uh indicator and what what's interesting here is first off it's poison ivy right and remote access uh trojan so it gives me some insight of what might be happening here and and obviously some additional insight into where i should be looking um and so they talk about remote command shell right key logging screenshot captures file management encrypted communications those are all good things but it also calls out a a mutex specifically now you might say well wait a minute uh
what is a mutant or a mutex well it it helps a system not execute something that already has say outlook running right if outlook's already running you can create a mutant and it ensures that you're not installing or executing that code adversaries use it a lot right because what they don't want to do is create noise if they've already got something on the system and it's working they don't want to you know invoke anything else and so um they wouldn't actually execute here because the process is already taken care of right they've already got something running but for you as a defender analyst red team or blue teamer red purple team or whatever it is right
um whatever your role might be because in canada people wear many many hats um i can take that information and maybe i can query across a fleet of assets very quickly remember i talked about residual that piece of hair that falls out in the fiber this is one of those pieces of hair right we didn't get that information of everything we've done up to this point we we have not got this information at all now we have it we can query all of our systems and maybe we find two more systems that have impacted maybe resume.exe is not there maybe that shot 256 doesn't exist anymore right the adversary has manipulated the file and so the shot 256 doesn't even match
but they're using maybe the same uh mutant name um across uh their attacks um the way that they attack systems right maybe that's still this common between anything that they do right they're not thinking about changing that more systems and this is what i meant earlier that it that reinfection typically happens because there's missing elements in your investigation and so from that what you could do is because there's a response capability to this right is maybe take a forensic snap upon compromise maybe that's one of the things you want to do late the computer so if the technology is smart enough to tell you that there was a compromise of some sort um maybe automate the isolation of the
asset and restrict it where it can go um submit it to sandbox upon detection again just take that sample and submit it detonate it and get all the analysis ready and done for the analyst to review move a computer into a new group right so pivot the compute computer into a group with additional isolation capabilities or control or additional engines that might be running um to help further mitigate or understand what might be happening and so you want to drive those outcomes typically through automation and you can do that with a lot of endpoint detection response capabilities you don't need to move further up the stack and have a soar or some other tools to do that now
sort and or xdr is going to expand we'll talk a little bit about xdr in a minute so what we know is outlook.exe um brought in resume doc m the user clicked it macro was launched um which opened powershell that went to red.space that downloaded resume.exe and executed the payload right um and so we've got some other elements we've got file shars we've got domain right we've got ip address we've got port numbers we've got a mutex we've got um insight into the actual behavior of the um the the the malware in this case right remote command shell key logger etc artifacts um you've got um antivirus so just some basic flags on the behavioral side that are being
triggered you've got some persistence um and then you've got miter attack framework um you've got miter um and it talks about you know um the persistence around making sure registry entries and the the file will all automatically start up uh when windows reboots as an example um you've got some network information you know scripts were involved macros powershell and you know the threat source so at this point the threat source is outlook.exe so awesome right and some of you might be saying you know that's amazing i i can't do that today some of yous might be saying yeah we do this every day there's no magic here so far um and you're right edrs are all going to fall in line to
this right they're going to provide this type of insight some are going to do things better in some areas and then others are going to do worse or whatever right like it's give or take but if you're not doing it something you certainly want to do because we could have found two more assets just by that os query across the fleet of assets alone just two more assets that might have been compromised and then based on that we may have expanded so what about the rest of the story so things like what email did it come in on is that relevant or important i think it is right who sent the email anyone else impacted
how do i ensure we have defenses in place uh in other defensive technologies to mitigate that risk right i want a layered approach if i can take that shaw and make sure that i just you know send that out to all my defensive capabilities i can look at a shot and block then i want to do that so this is where extended detection and response comes in and i'm just looking at time just to make sure it's been a while since um i actually have done um something like uh this particular deck but extended detection response capabilities is um is is now taking edr and and injecting it with legal steroids i don't know if
that's a real thing but it's it's it's using edr edr's still going to be part of the puzzle but it's not enough right it's not enough of the story so what i want to do is be able to turn my entire fleet of technologies that i have from a defensive capability into maybe data ponds right i know data lakes people are driving towards data lakes but data lakes cost money right they cost money and so if i'm you know wouldn't it be nice if these things that i think are pawns because there's email security there's endpoint security there's network insight there's ips's and next gen firewall all these little pawns that exist if i have an api
based platform that can query them and build a river system that attaches them um you know that's pretty valuable so i've got things like malware and ips events security intelligence events i got flow alarms miles email dns sandboxing you've got web ip addresses endpoints forensics actionable intelligence so the ability to to take action systemic response based on a collective of information tactics and techniques right lining with mitre is always a good thing you want automation you want orchestration help accelerate your time to respond um and it doesn't mean the analysts disappears just because you've mitigated a risk right it's good you're under control and the tools may have provided a ton of telemetry or data but you need a human
to go in there and interpret that data and what it means to the organization so that's where the the big value is you let the tools go ahead and run it in a sandbox right remember the day when you in networking when you created a vlan you thought you were amazed built routing and you've got two vlans talking to each other and you're like whoa i'm magical right nobody can do this the alerts you get right how many times have you been chasing alerts that were false positives sucks right it sucks right you create a vlan you get routing that and then you never want to touch them again same thing with investigations if 90 of your
investigations result in no real value to the business that sucks so a lot of that a lot of those mundane processes can be automated and so now right but what if we actually did a little bit um investigation here and so we take the file name and we pick the sha here too right if we had xdr we may have even started here we may not have started on the endpoint itself and and i did that query and so what we'll end up seeing is some relationships and so this is this here it could be powershell as an example um this is in in this case is resume.exe we see a single target we see the file pass
and this might align very much to what we've already discovered or know so you might be saying well wait a minute you're not showing me anything different you're right but what happens now if we take rec dot space and we do an investigation so now we see a domain obviously we've got some relationship between power shell and the domain why well remember it went out there and pulled that file resume.exe down that infected this asset but we now see two other hosts that are talking to that domain now you know you might say well why isn't resume where's the relationship with resume.exe and those users well the adversary may have changed something in that file that that match does not
happen anymore and that file name may have changed and so red.space are looking or sorry resume.exe looking that up where the shot 256 looking that up may have no relevance in this the the the thing that's similar is the the red dot space now there might be another file so you you would further investigate that piece um and then resume can we know that that's an element right through our investigation and and so let's have a look at resume doc m for a minute and you might say well how do i know that if you didn't start with edr you're right i might not know that um and um and so the goal here with xdr
would be is that if if this is what i i see let me just go back once here just just one second let me go back if this is what i know right now what i might want to do is pivot into this this file right maybe i want to view it in a sandboxed environment maybe i need to go to edr to get additional telemetry in insight right um so you should be able to expand your investigation at any point from here right um and but whatever we figured out resume.m is involved here and so we do a quick query and so we see there's the relationship of outlook in this in this file
we also see the relationship to that endpoint so this really confirms that first story that we've seen right this is everything that we know um in our initial investigation the difference here now is that i've got two more assets that i have to further investigate that's more to the story as i mentioned earlier but as i go along here i can get the message ids from that shot 256 or that resume cam and now i got the message ids and i can see jason at victim.com and jack victim.com they both received messages so see this is interesting because now i know that jason may not have executed the resume doc m yet and so there's a problem waiting to
happen now jason's a pretty smart guy so i don't think he'll i'm just kidding i'll be clicking all day um but here's some more insight i've got some ips i've got the subject name i've got the domain oh wait a new domain here that was part of that email message so again i might want to add that to my investigation i also have an url that was embedded here again more information and it's showing as gray so means it's got an unknown disposition this one here should be orange or yellow i guess suspicious right and red is obviously bad and green is is um is a clean process and this is why it's important to monitor clean processes as
well i've got an ip here that actually has went out and went to this url what so i've got some network based host and it could be a user machine that i don't have an agent on right because that's another challenge with endpoint detection response is you're only as good as the agent you're installed on or sorry asset that you're installed on if you don't have an asset that can install the agent but still makes a request outbound um you probably want to know that in this case i know there's an ip that made a connection to that url and now i have also the email address of the sender you see how creative i am the effort i
put into these these sessions right bad i know it's sad but that's all i got guys but anyways you know who sent it so look at all the data i've got now i've got all this rich data that i can now use to either add additional controls elsewhere where well maybe i block muhahaha at bad.com or block that domain completely from receiving emails so that's one right um i can add those urls or domains that i've just determined as maybe back to that conclusion because there's more to the story but then we'll be here for another hour or two but now i can add them to some type of control a proxy a next-gen firewall
some cloud-based control that has proxy or dns layer protection right there's lots of different areas i can add saying block that url block that domain block that sender coming in block that shot 256 now you can see our layered approach so now they've got to change a whole lot of things right it's not just going and changing a sha they've got to worry about the domain they're coming from they've got to worry about the urls that they've embedded in the email they've got to worry about the file right and now it's being detected so like i said earlier they have to be right in multiple different areas you as a defender only have to be right in a few maybe
only one right it could be as simple as it tries to go to cnc and you block it and it's done they can't get access to the system now it doesn't mean it's still not compromised it certainly is and it and if if that control is not there when it when it's on prem and goes off-prem guess what it's gonna connect to cnc but you want that control as much as possible to float with with anybody right no matter where they are but you get the idea and so now what we got is the ability to take action as i mentioned earlier if there's a file i might want to pivot so in this case here
if this was a new asset maybe up here as an example i might want to isolate forensic snapshot do some automated orchestration capabilities driven out of here now you can do it based on events but you can also do it based on decisions a human has made based on the investigation and instead of running into the running the file into a sandbox and grabbing it and then uploading it you don't have to worry about all that or blocking it in email you don't have to create it change control allows you to implement this this mitigating control and you block it in email done right automatically through the tool same thing with um actionable data right so if i want to
well they're both actionable so but if i want to maybe search this file run it in a sandbox as i mentioned earlier there's a collection of capabilities that you you can imagine that you'd want to do from here that you should be able to do you shouldn't have to open a ticket ask another team to go ahead and implement these changes not not for these things right um and maybe you even want an approval process so if you're going to isolate this host maybe it goes through a chain of command and automatically sends an email to somebody and they have to hit approve before the isolation takes place um but these are things that you
probably want to consider so there's certainly more to the story here right so we've got we have two more targeted endpoints that that are like a traditional user-based system we have two targeted internal email users we have an additional uh email domains urls and ips we also have answers to those two questions so that that one question uh we know that we've been compromised right have we been company yes we've been compromised so we know that answer and then finally do we have defensive capabilities in play and based on the intelligence that i'm seeing here in xdr things that are red means that i've got a mitigating control meaning that i have intelligence that knows this is bad and if pro
understands that these are bad because they're taking in the same feed data then i know i'm mitigating that capability exists or i've driven an outcome based on my investigation to enforce that mitigating control um and so now i i do know i have defensive capabilities so this is how you can help stop that reinfection right is truly understanding the story because if you didn't you would admit first piece and this piece here would have been um missed and you know what it would be a new file a new shot and the process would start all over again and it will continue to do so until you figure out exactly what's actually happening so that's it it's game over you guys win
the mouse trap set and the adversary's gonna get caught i guess i don't know but definitely it's giving you a little bit of an advantage that you may not have had so that's all i have i'm gonna see let me just see can i see let me just put that can i see okay now i can see the the window let me see if there's any questions or comments yeah so complexity you're right like this is complex there's no way of sugarcoating it it is complex there's no magic button there's no magic technology no no vendor that's going to be able to provide all of these answers now what you want to do is simplify the
capture where you need to go streamline that process to um you know empower the analog to add value is there tools you would recommend to use for sandboxing portion um you know there's there's all kinds of tools out there i think most people know i work for a vendor so i try not to to get into recommendations of a product um but i would just encourage you to do your your research talk to your peers there's a lot really good products out there the biggest thing to consider around products in general in general is the complexity that that you end up with all these different capabilities if you look at security security industry has you know i think last time there's 900
or a thousand vendors and i've heard numbers of 1500 to 3 000 vendors in security if you look at if you look at network systems storage you're talking about a few dozen maybe two two dozen right most people can count most major networking vendors most major system vendors or most storage vendors try to name the security vendors in the space and i've done this in the past where i've made something up i was at a a customer location and i said you know what have you ever heard and i was just trying to make a point and i learned something very much in that that session i said look at have you heard about this
product called security ninja and i don't know if you know uh i think douglas and i have chatted about this joke before around security ninja in the sandboxing tool or something like that right but anyways i i talked about it does sandboxing it does endpoint detection response does all and i said who in this room's heard of it and i had someone raise their hand and i said no i just made it up like i just me like 100 made it up um and um but then i i felt oh wait the person on the spot like really bad in front of a room about like 30 people and then so i retracted a little bit by saying maybe
it's true maybe the product does exist and i don't know about it um but that's the security space so there's a lot of complexity there and so as long as you evaluate that and you're able to work through that then any product will work
um is there tools you recommend yeah that's very useful thanks brad and we're coming up to the end i'll probably get kicked out curious no they don't they don't have network connectivity so they are safe um but i know the new versions of these now actually do plug to the cloud so you can play the games you don't have to store them locally so um that's funny um plug in security ninja so yeah there you go right um so there might have been a product there but i don't do it anymore because i'm just too worried that someone's going to say it exists and i'm making it up um that's awesome there's multiple different things
how is xdr better than soar yeah that's it i think what you're seeing is xdr also has soar um right there is automation and orchestration as part of uh you know many of the the xdrs that are you know it's again there's a lot of marketing terms xdr soar sassy xero trust um [Music] there's some meat to it but there's a certainly a marketing spin on a lot of that stuff um but i think xdr includes the orchestration and automation and response cool all right guys have a good rest of your b-side