Security Engineering != (Admin || Analyst || Responder)
Show original YouTube description
Show transcript [en]
hey great to be here and i really appreciate uh you guys listen to my art our talk right so i have the awesome privilege of working with lou infiltrate and uh we are going to talk about secure how security engineers is its own unique skill set and it doesn't uh it has overlap but it is not exact to all these things so uh your standard disclaimer uh forward forward-looking statement uh legal liability etc goes here uh but hey who am i i'm craig bowser i've been doing security for over 20 years in various dod and civilian contractors and agencies and such i have some letters after my name that means something to hr folks and
i go by reswab 10 on my twitter account and i blog very occasionally and it's been too long so i'll try and get that updated but that's me hi i'm luke goon i've been a security engineer for several dec years now i started in information technology in the defense contracting industry i did a lot of things such as system administration software development and still ended up into cyber security and security uh uh engineering uh i have a couple of searches as well my twitter handle is infiltrate and my email is logon7 gmail.com because i'm too lazy to do a website or a blog so that's me in a nutshell uh and uh we um again we're glad to talk to
you guys about security engineering today so this is what we're going to cover uh we're going to talk about hey what is security engineering what are some of the roles that go with it uh we're going to introduce yet another framework because we know you guys love frameworks i mean who doesn't love frameworks right well i'm not sure i i have frameworks all over the place and yeah posters posters full of frameworks yes notebooks yes so we'll talk a little bit about what the job market is for security engineers how to become educated you know the certifications that go with that and then we'll talk about look forward a little bit about what are some of the current challenges
and the future challenges that security engineers uh are facing but first louis you kind of give us a definition of what uh security engineering is about you know it's been it's been something where we look at everybody's definition of security engineering and we see something that's coming so this is really more common to what we believe security engineering is and that is security engineering is the process of designing and incorporating security controls into an information system and making that a part of the system's internal capabilities right and then you want to say well what does a security engineer do uh the security engineer is an experienced professional and we will elaborate on that a little
bit later in the talk that designs and implements uh strategies and systems to protect infrastructure from cyber attacks threats and vulnerabilities that is the overall definition of security engineering and engineer that we would like to expound on for today exactly but real you know where did this come from right remember years ago security was sort of like its own thing or it wasn't even a thing it wasn't yeah we were relegated to the bottom floor in the closet down in the lower level of the corporate building right right you know with you know i t and everything else but security was not its own thing so you know we came from where do we come
from you know from back in the 90s with with uh what was the cpu what what did you have back then lou you know as far as your i had a gateway i think it was a 35 megahertz sx intel processor sx86 processor yes you're flying did you have a little turbo button where it's like you know oh i can no that was that was the dx model that the sx didn't have the turbo model okay right so you know that little turbo that's like hitting the you know i'm not sure if it actually maybe it did do something but it you know made you feel good to push the button think you're processing faster
but really what we were facing back then we had you know infrastructure like firewalls proxies were around you know remember you know network web proxies were coming into ids was you know introduced uh antivirus was around because you know we even back then we had viruses they didn't move on their own but they were you know not then at least not a lot uh so what we also facing we're facing you know corporate snooping uh uh bbs kind of snooping and attacks and passing of things uh but our our it infrastructure is very basic those websites email online servicing aol anybody actually i didn't have aol i did it i hated it even then what did we call it all hell
so so yeah what is it no huh no no go ahead yeah i was just i was just remarking that yeah so i remember uh what was security engineering back then right it again wasn't on its own but we had i remember i was in the air force at that time i was part of a team called scope network and our job was to go to uh air force bases and help optimize and troubleshoot their networks and so we would show up at a base and spend two weeks basically doing whatever uh the the com squadron the communication squadron needed and so we would just go in and some days some jobs excuse me some places it was hey we we
have this new router it's our it's our it's our point of presence router it's our border router and we just we don't have we needed you know we need some help because we just don't have the time you know funny thing is back then they didn't they didn't have they didn't have enough people and enough time to do everything they want guess what hasn't changed in 20 years uh you still don't have enough people enough time to do everything you want but so we would go in and help them do that sometimes it was uh rebuilding their uh domain structure in nt4 i don't know how many of you remember nt4 that was a thing um and you know
there's still the concept of domains and some you know and that sometimes we would completely redo their domains all of these things required engineering to figure out well how is this going to affect the network how do we plan uh to ensure that that it not only has minimal impact negative but that on monday morning when or the next morning when these changes were implemented the entire base was able to come up and be not only functional and operational but actually more efficient because we've done something to improve the efficiency of the network overall and so the concept of security engineering wasn't necessarily written out it was just hey go fix this but really that's what we're doing because we're
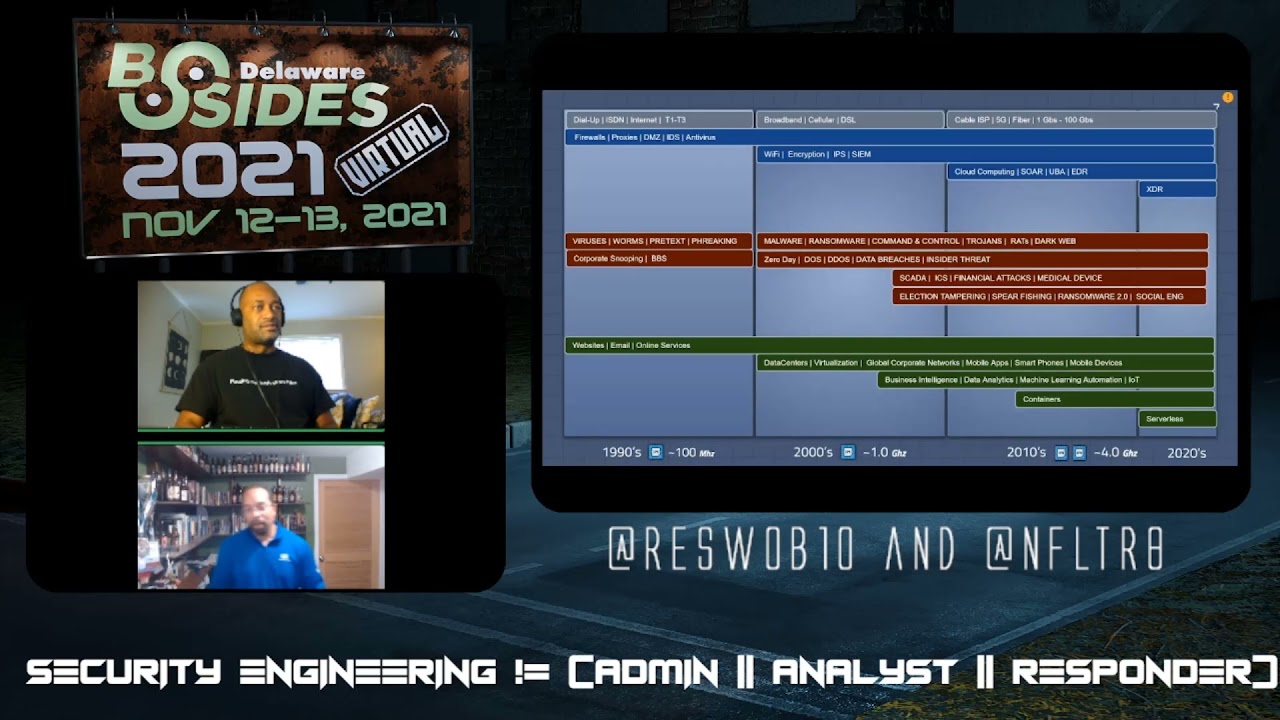
not only making the network we're working together with the operations to secure and efficient make the network efficient to add to that yeah as you can see here in our slide the threat profile that continues to grow over over the decades and as you can see not only the threat profiling the technology and the networking technology these things grow over time in our and our profiles become more complex as we are in today so uh reason why you know i really like that the the fact that you know we started you know basically here at the at the 3600 level we're now to multi-core levels and artificial intelligence and data breaches and things like that that whole threat
landscape has increased over the decades here and it's just a short span this is like 30 years right and and here we are full online services full cloud mobile integration and things like that those things i think we will we will see that over time that made the information technology and the security uh cyber security uh industry grow and expand and to come into terms of where we have that all these roles under the cyber security umbrella and and and so on and so forth but what has really emerged recently has been the the security industry the security engineering industry at this point uh yeah and yeah as lou said you know security engineering just has gotten
more complex as as we have you know continue to add all of these things while still taking into account the old stuff that's still around slammer's still around right you go listen on on uh you know on on the scene report you on the wild internet and you'll still see slant the slammer where i'm trying to infiltrate you scary it's been 15 plus years but you know things never die so so craig let's talk about the security engineering uh roles here yeah yeah we're i mean so you know where do you go to get into this right how do you start right where did where did we all start i talked a little bit about where i started i
started you know a system admin i started as a network admin doing optimization troubleshooting and understanding the roles but i mean the you know beginning into this you know is a number of different ways whether you start from networking whether you start as a server admin where do you start in i t support all of these provide some of that foundation i mean the whole point of this slide i think that we really want you to take away from them this is from cyberseek by the way uh the whole point of this slide is that cyber security engineering security engineering is not net is not a beginner role this is not an entry-level position because you need
to understand the so many foundational aspects of your environment of of the network environment to really uh do that well so you know where you start from your feeder rolls and you move into a sort of entry level you know junior roles of doing cyber security analysts and incident response and uh and maybe you know focusing on um you know vulnerability management and then as you move into more of a mid-level journeyman role of of maybe izone izone glass incident responders analyst maybe a consultant may be doing pen testing or vulnerability um you know exploration or research right those all these skills build on each other to be you know allow you to be a cyber
security engineer overall and you know don't mind these numbers we'll talk more in depth about jobs and and salaries later on in the slide i'm sorry later on in the presentation but you know understand hey this is you know the engineer is not something you just walk off the street and say yeah i'm going to be a cyber security engineer because you there's so many things that build on that so what does that look like well first is the you know some of these ideas some of the roles that go into it is you know the concept of an isso issc information security officer where you understand regulations compliance you understand how to write and read and apply policies and monitor
your environment for adherence to those policies and then you move over to the concept of of an architect a security architect and what this role implies or entails is the actual design of network configurations of security of applications and designing applications utilizing applications configuring applications securely policy absolutely understanding uh and being able to take a policy and figure out how that actually applies in your environment falls in this role near these guys these architects they're thinking one to five years out they're thinking hey what what is this new tool what is this new technology how does that work in my environment and how does i make sure it works securely and then from there there's the security analyst part where
these guys these are your eyes on glass we're familiar with this role they understand and they monitor the state of the security posture of your environment and they're analyzing reacting to deviations from that secure state and that you know we're investigating incidents and by the way i mean obviously this is a very high level slide you can go way down in the weeds on each of these rolls but where i'm talking about here and as deviate from security is the network server admin roles that is you know where these guys are responsible for ensuring our environments operate they ensure that traffic and users and tools are working available and that uh that there's uptime that things are efficient
that everything's accessible and so what we have is that security engineer that overlaps all of these and sometimes and those of you who are in smaller organizations you wear many of these hats all at the same time or you're switching in and out as you're doing uh going throughout your day but in general you're looking at the engineer he's implementing the architect plans he's partnering with the engineers and the admins you're ensuring your analysts can do their job and you're enabling the isso to work with compliance so so what you're saying craig is the security engineer is the great compromising role we work with everybody we work a lot with everything from the from the sea level down to the analysts
and even the user absolutely we cross uh we cross all those planes and we'll talk about that a little bit here like where we have the hard skills and the soft skills so what working with all of those people all of those users hey what in the heart you know where do we what do we need to be able to do what's our hands-on keyboard task you know if you're you know so for in the infosec part you need to understand security policies best practices understand comprehend what vulnerabilities and exploits uh that that leverage those vulnerabilities how tools both attack tools and defense tools work and how to detect and protect your network how to detect the bad things how
to detect the attack tools how to find the vulnerabilities on your network and how to prevent attacks or at the very least what's mandatory what do they say you know if you can't prevent you must detect you have to do one or the other uh and ideally both then from just you have then you have to understand from a operating point of view the server administrator roles understanding how authentication authorization works in your environment along with just the configurations you know that that's such as uh such a small sample of all the things that go into you know whether it's it's uh databases or web servers or applications or operating systems or or well i'll talk about cloud separately
but i mean that you know that's just an example but of anything you gotta understand author can authentication authorization because that's such a huge part of security but then you know just tie into that uh scripting and programming these are skills that are absolutely required in today's environment because where you can't get where it's not provided necessarily by a tool that you may have to actually you know wrap you grab your your scripting skills and go do something and then you talk about hey network architecture talk about absolutely needing to understand this skill because you're dealing all the time with protocols you're dealing uh with their tools of the network and the communication many right what what do we see many
exploits they take advantage of weaknesses in these in these tools in uh in protocols or in how things communicate and so understanding why uh you know dns flood attacks why they and how they work under help enables you to then architect your or at least engineer your network take understand what the architect is doing to protect your network so you can engineer uh an implementation to protect your network from those things and finally you know recently recently being like what 10 years but you know in the you know you know recently you know we have all the cloud stuff that we now have to understand because even though the the concepts are similar they works
like they may work slightly differently they may be um you know some of that is abstract away from us where we may not see the the bits and bytes that flow at the you know underneath the virtualization that we are in inside but we still have to understand what that layer is and how they work together to provide us the containers of how serverless works and why it works so we can then protect it but hard skills are only one side of the coin uh and soft skills you know are are as as much required as anything if not you know equal and so when you're an engineer you're doing a lot of writing because you're
reporting on what you're doing you're reporting on how things work you're reporting on what should be done and so documenting what you've done memos to uh co-workers memos to management uh detailing where you should go recommendations that they're in uh taking notes because you're gonna be in meetings a lot because you're gonna get called hey we're we got a new project coming out and we need you to be in this meeting we need you to figure out what to do so you're going to be taking notes a lot of times on on those uh about what's going on so that's an important skill to have project management time management absolutely because your projects are not going to
be sort of hey you know install this operating system install this application there your projects are going to be multi-week multi-month tasks and goals where you're going to have to know how you know manage different tasks and the timelines and dependencies and manage your time for each uh and not maybe not just your time but moving into people you have to work you know understand how to manage teams or work within teams to uh get your tasks done when is there dependencies on other people so being excuse me diplomatic in that sense are is super critical hey performance under pressure these are mul these you will be responsible for multi-million dollar projects maybe or multi-thousand
dollar projects but you know definitely uh you're gonna be responsible for projects that could be uh you know your where your company your organization is like hey if this doesn't get done we're sunk right so you have to be able to perform under that pressure under people micromanaging you or you know being you know like you know similar under a microscope and you have to work all sorts of people so that means you can't just say well i don't want to work with this person because i don't like them i don't like their uh you know i don't like their clothes i don't like the fact i don't like the fact that they're a giants fan
um i don't like the fact that they're a dallas fan actually if you're a dallas fan i don't work with you but you know if but you know if you know whatever it is you got to be inclusive uh of of everybody so right that's that's part of that skill so you know business skills hey when you're doing the project understanding what the cost is understanding how to estimate that cost to project that cost roi um and knowing when you're going to get a return on investment you may have to work with sales if you're a sales engineer that's absolutely part of security engineering i you know the role i'm in now i'm required to get on
pre-sales and discuss how with customers how they may implement or how this tool would help them or this service would help them and so that's uh that's a skill that's important and critical to develop now ultimately you have to be a problem solver you're going to get called in on meetings or called unexpectedly hey such and such broke why and that's all you're going to have and so if you are uh you need to be able to think about what services and protocols and configurations should be there to kind of logically trace back why something broke and so that's going to be a very key skill uh so lou thinking about how you got to where you
are in your security engineer career right where some of these things really stood out to you that you really said oh yeah that that was something i had to develop well definitely the hard skills um uh were were key to my beginning in information technology but i want to touch on something a little bit more recent with that in the soft skills category was that uh in in and we look at this this from like you said a project management perspective and things like that but you know as over time these these industries develop right so we were dealing with project managers and budget and things like that from working with that but now we have team
project things in in in methodology such as waterfall and agile and things like that that we now are a part of at the table so learning that that transition over the time was really integral to to to my soft skills uh set up as well i mean i like you i'm not a big fan of documentation but you know the most of my time i was i was actually writing administrative documents and disaster recovery documents and and documenting technical procedures or incident handling procedures over over the over the course of any any of my job sets right so those key things of learning how to make sure that we write we're good at technical writing
we're good at and making sure that we understand uh uh processes and things like that to recover or to to implement or to make sure like you said if we get hit by a bus or something uh somebody else can take that documentation and run with their project so those are the main so some of the the constant levels uh soft skills that i i had to uh to really hone in on over time and and that is over time it got really easier with that as far as the hard skill set man i started off with application development i started well for hardware integration especially with videos and stuff and i did all uh the majority part
of my system administration and then as we started to get attacks and in in incidents and stuff like that that really kind of kick-started you know understanding like you said about operating systems understanding about uh applications and things like that and and some of the network typology that you mentioned you you really get an appreciation for that when you now have to go in there and figure out how to to integrate an ids into a system or to a network or into a corporation so that hard skill sets of of getting that experience initially in in your field uh really pays off when you you transition into a security engineering role uh absolutely so um
so how do you know what are some ways that we get there right how do we get to this point and there's as you know as i implied with the cyberseek uh there that's one option that's one path but you know really where you know where can we you know how what's the path what are some of the other paths some of the other ways to to move into this field or if you're in this field continue to advance in it so let's just be honest bottom line you know first thing is that there's there's schools right you can go to uh colleges you can go to uh um tech schools uh if you're in the
military a lot of military has really really been focused on providing training for their troops uh in it and in high tech uh skill sets and career fields and so there's a number of different uh schools that have security engineering degrees and so that gives you a great leg up in the industry uh both bachelor's and master's and masters obviously is something you want to pursue if you are already in the field and want to improve your you know your uh your skill sets and your capabilities there there's training companies sans is a one that obviously comes to mind quickly but there's uh udemy there's linkedin learning there's boot camps as well that uh operate in a similar fashion to say
you know see issp boot camps but for longer times uh we and by the way we have a bunch of links at the end of this slide presentation which will share out uh that hat you know that you can then do further uh research on your own uh there's uh other formal training can be vendor specific and this is not something to uh uh to to kind of blow off you say well if it's vendor specific then am i only qualified uh for that vendor no i would say that you're not why because uh the concepts that they teach are going to apply no matter what so if you're talking about you know building a dmz
with cisco products you can still build a dmz with palo alto or juniper or some other tool but it's just obviously knowing what you know the difference in the commands and the process the concept of what a dmz is and why it's important applies no matter what tool that you are using to do that so formal training is great because it increases your knowledge in general for the field as well as increases your skill set for something specific for maybe the current job you're on or the current job you're trying to go for and then finally you can uh you can just be self-taught as well and that's uh that's important and there's number of ways you can teach
yourself to either get as you're getting into the field or once you're in the field improve your skill sets uh then i want to bring up just the national initiative for cyber security careers and studies website uh which is by the way a horrible name because it's way too complete you know but never left um sorry um nevertheless uh you know they have i think the best way is to to really call it out is they have a specific um uh key uh uh key measurements or key skill sets that they break out different uh different different job details so for instance what's pictured here is a cyber defense infrastructure support specialist and they break this down and they say hey
you should have these abilities and this knowledge and this skills and these are all the the different things and they bring it's a great way to say hey what do i need to know for this type of job now they don't necessarily have a security engineer but you definitely can kind of as you look through it you look through these at least these three security architect information systems security developer you see that the skills and the abilities and the knowledge in these really help you um you know with um really help you with uh uh you know doing actually security engineering and then finally once you start uh well finally with this as far as prepping and
moving into the career uh there if you once you're in the career you know you're looking for some of that you know those certification those letters after your name that hr departments like uh so you know there's a number of of actual certs that really actually apply to engineering and so you could have you know from the cssp once you get that you can get the specialty of engineering uh the scissor the c uh scissor plus from comptia uh is definitely a plot applicable if you have the opportunity to take stance training there's the gced or the gdsa of great uh great classes and great uh certifications for engineering because they look at security from the
enterprise point of view and uh you know and then you also can work through those vendor certs i have some examples from cisco here so all of that brings us to what we want to talk about our new framework right the one that we know that we're presenting so so security in general likes to talk about the cia triad confidentiality integrity and availability but we're saying hey if you're an engineer your your framework should be slightly broader than that lou you want to uh dive into this so yeah uh we we we were talking about this as we developed the the presentation of what what are some of the areas where we can can can look at things from a security
engineer perspective from from other perspectives as as we defined this roll out right so we we we saw that there are at least three good areas that we should look at in during our jobs or doing your job or working on a project or working on on a service or something like that and that those key areas are rely into security which we will talk about as a as as both the concept and the the indicators the performance indicators beyond that operations things that that we do when we try to put a tool or service into a production and the business side of things how do we work with uh our our sea levels our directors all the way
down to the the but the business people or or or the uh the the vendors that we're dealing with for a set service or product so it kind of comes out to be the sob like the cia triad you know so uh we thought that would be kind of catchy and and we want to introduce this into this talk so that we can get feedback on this you know do you think this is a good way for us forward you know should we look at formalizing this into some kind of a framework uh that's that's well known and can be used in curriculums and and applications going forward so let's talk about the security aspect of first so
you go on to the next slide there mr mr uh uh mr reese yeah i know it's a little a little bit of a network delay there all right so our first first uh part of the framework is security and again if we're putting in a service or a platform or we're doing something uh that involves a security engineering project even though we're not may not be the lead on it the first thing is is that what is the function provided from a from a securities perspective or from a business perspective is this something that we're protecting the environment with is it something that is we're monitoring and logging information with for incidents or or or threadings or
reports or something like that or is this something that we need to uh report on metrics things things like number of attacks or something like that right so that's the function that we think of when we talk about the security uh is this product of service compliant and does it adhere to the security standards of course you know there are a lot of security standards out there especially uh um uh international ones right so uh some of our vendors that we have even the cloud services do comply with um uh these standards and some of these may even uh uh claim to comply with compliance standards such as nis 853 um is this a technology or service that
we're looking and and finally and we'll talk about this in the other triads as well what are the performance indicators that we need to be aware of for this product is it something that's going to elevate our situational awareness in in certain areas of our our company or corporation is this something that can mitigate threats is this something that can make our life or work easier uh so on and so forth so there are a lot of um okay what we would call kpis that we're going to look at in in certain areas as the framework develops so that is uh mostly the security framework and again still a work in progress so you know if you think there's something
we can add here in that area feel free to contact us on it as we look at operations we look at the day-to-day uh resources needed to effectively administer or work the tool a service right so again if we're if we're moving to aws or something like that who's in charge of the administration part of this this project what teams are involved is it networking teams is it is it uh the security engineering team security operations team is it is it some other teams uh or business teams that are trying to put their applications into the into the uh aws infrastructure there so we we always need to know uh what what uh teams and
organizations are involved and also will be impacted if something goes down or if a service is uh interrupted or something like that that impact of the organization is is a key critical you know are we putting in something that will affect our our business operations are we putting in something that can affect financial reporting or something like that and finally um again you know is this something where we need to track the the amount of hours needed to to uh mo to to operate this tool or the resources needed to operate this tool or is it something that we can put in the cloud and let it run automatically and check it you know once
a week or something like that so um the impact of the organization is is kind of critical to operations because you always want to think about that when you're putting in a service or or or platform next finally we have the business side of things and in the business side of things we we definitely want to understand who are our stakeholders is it the is it the vice president is it the directors the program managers as the people who signed the ultimate check they are now in as as we've seen in our experience are now coming to the table and allowing the security engineering and cisos to sit in and have be a part of these technical
conversations as or or or operational conversations if you will uh now so we're not necessarily relying on all the sea level to sit up there in the in the high table and talk and then just kind of uh trickle down information to us but we are looking at at those things from a stakeholder perspective this the stakeholders are very important identifying them and working with them as as you begin this project or service and then of course of all things costs is this going to be a capital cost is this going to be in budget cost is this going to be a special situational cost is it going to be something where we're going to have to
worry about getting insurance for as as you know ransomware uh these days are are causing all kinds of insurance headaches in in the uh in our industry uh but as we as we uh look at ways to mitigate some of these threats the costs are a very important thing and it's something that you can understand as a security engineer and also these days something that you will be at the table with uh when you're looking at vendors and that's why we talk about vendor maturity vendor maturity is is something where if we're looking at the cisco's the amazons and and the dells and all that stuff or we're looking at the networking services of cloud providers and things like that we
want to know how mature they are you know and that may help us in our decision if they are a five-star partner or gold star partner uh that may help us uh in our decisions to to implement certain tools and and capabilities again we look at these things and we can relate to our stakeholders our returns on investments and our mean time to detect resolve and contain as a key performance indicator uh that we can report uh hopefully over the short term and the long term and the life of the project as well and then we also want to look at the operating expense as we mentioned before you know is this costing us extra
resources to operate these tools or is this something we can absorb into the general uh operating expense uh going forward such as data center cost or or service costs in cloud uh costs in amazon so those are the three major areas that we think when we think of the the the security engineering triad we kind of look at uh my example even though not complete uh does uh represent a typical security engineering project to where if if your networking team says hey we're moving from one gigabit to 10 gigabit or hundred gigabit networks how is it going to affect you guys um uh uh security stack and so um real and again this slide is
incomplete and i do apologize but i will talk to it uh so at first and foremost we look at the impact across those three tri uh triad areas and then we look at the key performance indicators right so it from a security perspective uh moving if we have legacy tools that are rated at a gigabyte and cannot process uh network traffic more than a gigabyte then we're going to obviously have to upgrade those tools and or figure out if there are new tools or something like that that can we can add into the security stack to do that the operations side of the triad will probably affect more of the of the security operations team in this
instance because we we will have to make sure that uh all of their uh tools and resources are able to also handle the additional uh traffic that that we're looking at uh going up to right so in the case of the sim you know if we have a salmon in place uh the actual network traffic will generate more logs will generate more more uh resources and things more data for us to look at over the long haul into our tools so that may provide impact our operations team and overwhelm them to a certain point of maybe impacting the tool in a reverse in an adverse manner uh all in all the the the thing uh uh
for the business triad is is excuse me the business side of the of the s triad is that is this a out of cycle cost or is this something we can put into our um our annual budget cost right you know what is that going to be if we're going to have to go from a generation 1 palo alto to generation 5 palo alto because it's rated at 100 gigabits per second now are we going to have to uh put in something maybe like a packet broker to help us manage traffic to the security stack so as you can see there there's a there's a a nice example even though not complete of how we can
utilize the security uh engineering triad and as for a project that uh that will impact the uh the corporation at large so again i i do apologize that this slide is not complete but uh uh hopefully you're doing a great job you did a great job talking through it and i think i don't i think everyone understands it's a great example of how this security truck the the tribe we're talking about really applies to your environment to what your projects are you know the it's like what is the roi at the end of this right are we making sure that from a security engineering point of view we've increased roi we always hear about security being a cost sync yet this is
where we have to understand that we uh in communicating what we've done and how the end result is that we've actually uh increased the roi uh we have reduced uh maybe we've reduced the increasing i'm sorry maybe we've increased the roi by reducing our liability uh what are these a lot of these breaches that happen today what's one of the things they want to know did we have was security configured properly and the more that we can show as security engineers that is configured properly and things are working and we've engineered for um observability and coverage the more we can reduce liability in that sense and so that's a really solid example of of that so moving through uh moving on
you know we have what is the need for security engineers going forward we just gave this very very high it's really high right uh you know some quotes from some articles that were you know we recently read it's like hey it's one of the three key thing hires to make now and the right we all know security right there's a number of different stats on how many jobs opening in security overall but engineers are part of that and sometimes we focus on hey we need more analysts we need more pen testers we need more incident responders but if you don't also complement those hires with engineers you're going to be in trouble because who's going to make
sure that those other uh capabilities those other skill sets can do their job as well as the engineers uh there's the executive order which i know is more you know american government united states government but i but it i think the trickle-down effect of this executive order is going to be felt for years and you know because it directs the government uh to go implement zero trust implement mfa implement a war and advanced logging and retention and pcap collection and a number of other things and ron guller was right he's you know he called out he said hey this executive order you can't just hire analysts you gotta hire security engineers because someone's gotta figure out how to
implement zero trust and it's not gonna be the guy that's doing eyes on keyboard he needs to have eyes on keyboard and this other these other tasks are huge and require the kind of network and security engineering uh that go into this working with the admins working with network operators working with management working with compliance offers security engineers will be needed to do these things and lou you took a look at uh you know some of the jobs out there right um uh yeah yeah yeah there were a couple there were several sites out there that we looked at but we wanted to pull uh just something locally here and and and these two sites dyson indeed had the the
metrics no problem i had the metrics for for the regional area here and we also want to give a shout out to delaware where b size delaware is uh they have 40 at the time of this writing uh which was last week they had 42 cyber security engineering jobs available so if you live in a metro denver delaware area you're a cyber security engineer there might be something out there for you but um delaware area but on the other hand people of delaware might have some issue with that one right yeah but shout out to my metro delaware area you know i'm i'm here to but yeah as you can see in the in the
region over 11 000 jobs from indeed and over at 7 000 jobs from dice uh you can see an uh average salary for a in engineering uh cyber security engineer is about 134 000 dollars the low end was about 108 as a 2000 uh as of this year and then the high end was around 155. so it's not saying it's lucrative but you know hey you're not at the executive tax level yet so pretty good stuff i believe and and maybe with the high cost of living around here the this little this little salary could help but yeah uh definitely a lot of opportunities here uh do check your your sites you know there we we picked dyson
indeed because of the mattress poll directly from the website but there are a lot of other jobs out there right and you know when you talk about you know covet and and the lockdown and no matter you know where you stand on the issue and as far as your personal uh viewpoints that the realization is that it has changed how we work and because it's changed how we work it's changed the some of the challenges that we have to deal with in cyber security and and then specifically to this talk engineering right there's been you know working from home increasing phishing scams uh teleconferencing you have you know data breaches you have zoom bombing right
things that we didn't necessarily have to deal with when everyone was in the office uh counteracting you know the spread of misinformation about your company right how all right we're not just we're not talking about controversial topics that are in the news we're talking about hey did you hear that such company had a breach and it that's not true it goes you know that can spread very quickly uh and where you if you're in the office that kind of information might not be spread as fast uh because you have more control over what happens within your company so uh so all of these things absolutely impact um you know the the the security of where we are now
but what's coming down the pipe right i already talked about the executive order but you think about all of the things that are even in general whether it's in the government uh in the us government or commercial or or international zero trust is the thing that's gonna happen that's moving forward no matter where you are we see an increase in automation that is without a doubt coming down that is coming down the pipe and increasing soar xdr uh whatever tools you want to call it we are trying to use automation to offset the skill set and the lack of people we're as well as making our current people more efficient right remove that all of
that basic stuff the stuff the day-to-day ordinary routine task automate that stuff we don't need we don't need to do that if it's mind-numbing uh alert fatigue is real i mean you think i think i think you have a new theme for a new t-shirt oh to make that i think you do i'm probably sure that's already been done if it doesn't have that somebody else or yeah um but right you know um but those are you know you think about as we increase with you know natural disasters and pandemics how do we make sure that we have um you know going forward how do we make sure that that we have continuous operations resiliency yep resiliency
right for whether you know first really came about i remember the stories coming out of a hurricane katrina and you know some of the both the successes and failures of that of out of even 9 11 successes and failures of resiliency planning right what happens if your headquarters goes down how fast can you uh may you know re reconstitute or even resume business so that's you know going forward we you know engineering security engineering is going to be critical as we have new tools new capabilities new threats uh coming down the pipe quantum computing uh lu i don't even understand quantum computing i can barely spell it um but yet that's we're going to have to
engineer that into our environments you know next year 10 years i don't know yeah so yeah quantum computing is going to going to be something where the computational uh power will go exponentially up to the next level allowing those people to for the first the biggest application of that is is uh reverse ciphering right so that's the biggest application of that but there are also other applications in terms of of of biometric computings and things like that but yeah again learning what's coming down the the pipe as you will is going to be key to another area of security engineering you always got to be not only in the cells of the of this uss
enterprise but you got to be on bridge looking you know down the the black holes that are coming your way so yeah the security engineering aspects of the next generation stuff i mean we didn't even talk about some of these things in depth because of time but uh it is important that the the security engineers have education have understanding have experience and and now there are avenues out there where you can go to school for security engineering and go and participate in trainings for good engineering specifically just for that yeah and and and learn those things going forward so yeah so with that that's our talk uh we would love feedback on the framework on uh you
know what we missed uh or what we included so this is our contact information feel free to hit us up on any of those uh i am not on all the socials so uh but i am on those uh email and twitter uh so uh and infiltrate may be more social than i am but uh that that's where we can be reached so any questions in the last minute or so that we have before they kick us out and we've been monitoring chat q a so is it lobby oh yeah track and qua i like that the car yeah oh okay they do love our acronym hey that's great that's great that's great yes um
uh there was a there was a uh uh a a link to another certification certified associate capm provided by bob uh project management so i mean that you know that definitely can help uh you know because again that's a great skill set to have uh you know something i need to look into as i i manage more and more projects so yeah and then i think hashtag metro delaware is going to be here at this conference y'all so you heard it from us first there you go all right so i think that's time uh yeah it was great talking with you um and uh look uh glad we could uh share this time with you hope you guys got some good
stuff out of it so yes yes me too me too great uh back to our illustrious command controller





