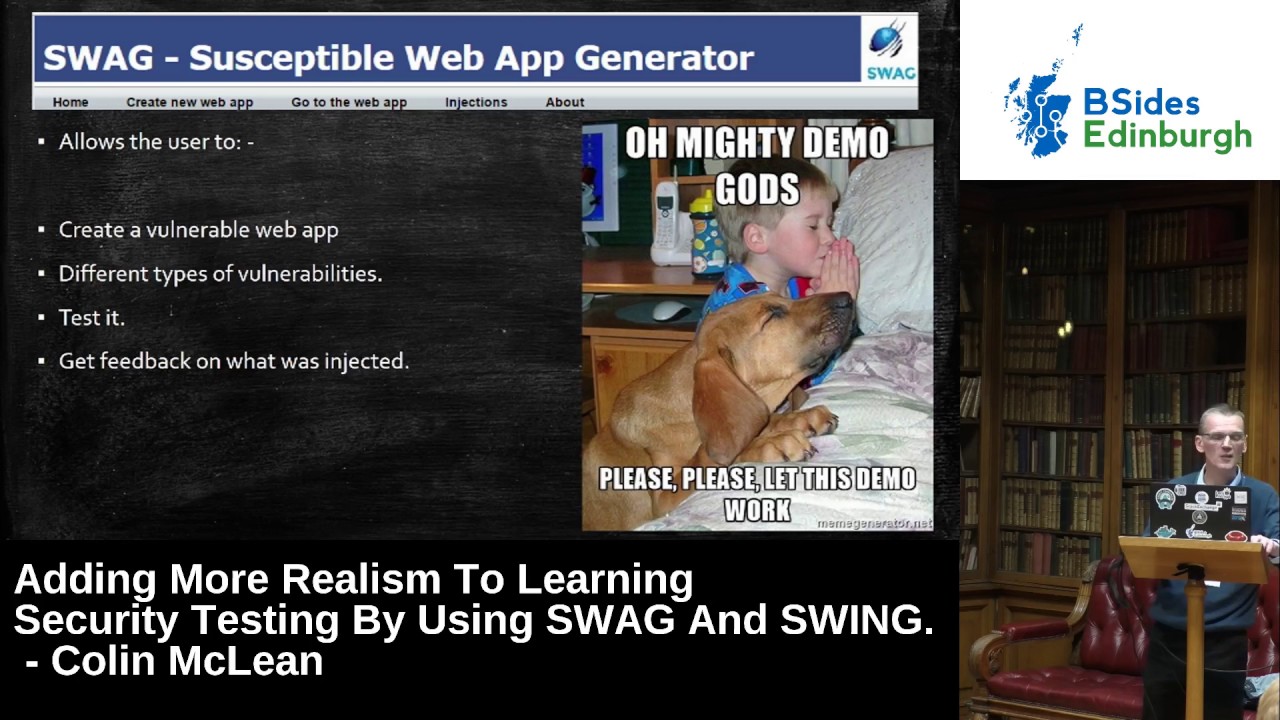
Adding More Realism To Learning Security Testing By Using SWAG And Swing by Colin McLean
Show transcript [en]
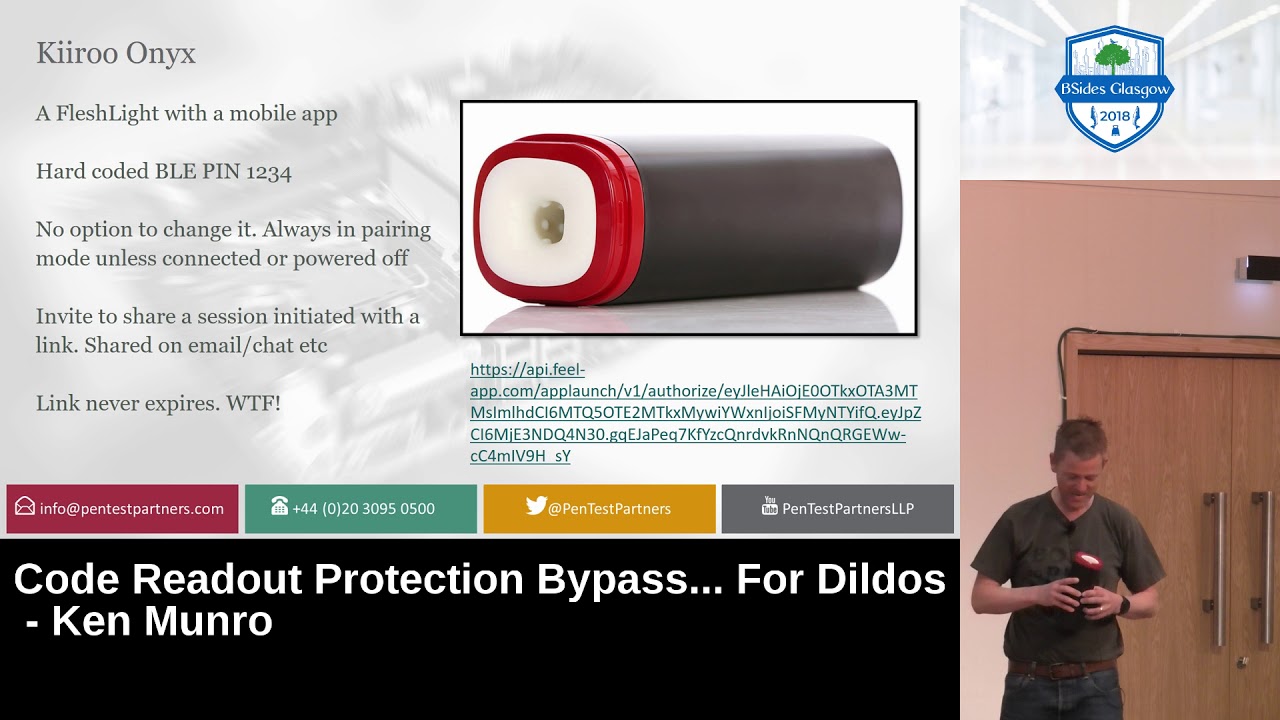
thank you yeah just introduced myself I've been there elation herbal tea for 27 years quite a later time with my degrees in mechanical engineering so as total mechanical things away back kind of move through networking programming no one ethical hacking probably this somebody's I get bored every couple years and want to kind of go do something else everybody who is we are thankful being the program chatter art party for their to go up in degree so smug in swing and what are they but basically a couple tools that I've created for using were classes in Alberta first one susceptible web application generator slug codenames slug I was thinking damn vulnerable a little bit overused in hacking so I
moved it away from their second one susceptible windows network generator swing so the docs base with all about what are they why I created them and we're out the going there's a hell of a lot future what can these applications ethical have been Albert a well I always advertise ourselves as we are vocational we're trying to aim at the job market make things as real as we possibly can however teaching security testing web application testing or infrastructure testing it can be difficult it's additional where that have done it and some of some of you who've been an opportune before a recognized a few faces will recognize those that essentially what i do is a clear at some
kind of target whether it's web applications on a network and hand out the same target to everyone and what happens is students will collaborate somebody will find a trick some deal find an administrative password then they go in the pub and kill the mix and it takes away a lot of the challenge and so it's pretty easy to do that it's much harder to make a general to make it very challenging and it's also topic of students practice and feedback all my students want to be fantastical so they want to test a network find out what this should have found and then try another one try another once again you know what was a different destiny I
also try and challenge security that students in and security as much as a possibly can it brings more than just the technical skills and I think Agatha is more about other things than just the technical skills things like exposure to methodologies project management skills experimentation skills I think a problem when people have more things by getting them wrong then getting them right the first time so as Native students the environment where they have to test things they can break things and get it wrong and then hopefully get it right but the other thing is think outside the box and so many people said thing is you can't teach think outside the box skills and they may or may not be a right but
you can certainly put students in the situation that they have to think outside the box 22 when so that's really what I want to do so walking it swag this good slug version one its kind of this was conceived last July and corfu I had 18 18 nights in corfu and I way by the pool in the morning and I drunk lots of alcohol and afternoon but in the meantime you know when the Sun was the hottest I spent to it I wish there was every day right in this application not sure my partner was too enamored me gone and holiday and walk in but once the geek fall was a geek so looking at web
application security testing and a lot you'll recognize these applications brilliant applications done vulnerable web app written by Ryan Durst known for years great application mythology abhi walk and also web caught the fantastic trade and applications as a lot of challenges and them growing it however they're not really will stick web applications so you cannot perform a methodology against damn vulnerable Weber that's not its design it's not its function so it's not vocational with anyway because someone getting a job at the end of this would be a fine a methodology to your website reporting the findings so it's but that's just not end there also second with solutions are out there students are like the rest of us will
take a shortcut so if you can go online find the solutions then students i'll do that and a lot little clip well i would have found it anyway but the method out the experimentation skills that they're getting it wrong kind of skills that you that your lamb and also once you've done DV wa it's done you can chuck it into been basic one so here's the desire sensory so know what classes or 40 50 students i want an individual and real-life website as much as possible for each student or several for each student and the one them to form a fill test using the methodology and then do the further here the documentation at the park at the end every student hates
doing that but tough the sweat so we'll both you must document in the real life or real world so a one would realize that application students can attack and it won't lots of them and I want them to be vulnerable in different ways I don't really want them to be tied down when you're rather than any anything like this if you get something that's tied down it's really good an object quadrants you're not really 11 very much so want them to be very vulnerable rather than under long haul so what I did on the balcony in corfu was I googled for applications so that will tell you factually MySQL PHP applications and see what's out there
and there's lots of websites free student projects com which I take it our student projects that you can download and submit as a course look don't ever do that because same thing of a technical term for these applications but I could only think of shite the person they are absolutely awful you're terrible applications Phil voges Philip Boyes and in many cases the filter genes as well also be incredibly careful of using any of these and the documentation is just they fail a document with it many of them no don't do that so anyway I started downloading them I did most of these applications that have died avoided I fight to fix the code that's number one I'd to make it work what's
the functional it wasn't there I've also kind of turn them into a lot of things you see home what school which is I think it's very relevant to this building I feel like them you know I feel that any of the magic wand in this building isn't bad but anyway so these are the applications of data wouldn't use so we've got school manager system we've got them a jeweler store in here which have some din to recast Feliz jewel jewelry store online career guidance and they've also got a medical service specialist whether promoted to the castle to a doctor I've got a student information system a clinic our web poll manager and of course no student can
survive without pizza so I thought I'd being a pizza or the system as well so these are basically what I would like them the contrabass applications eight of them the coded in different styles which is great so it definitely could in styles most of her endless each of these applications has also got lots of different inherent vulnerabilities cross-site scripting there's probably that cane in each of them which is which is fine no has what we want there's still not enough you know so I needed to do a little better scripting so give me a good excuse to learn about a Python so here's here's that the very first version use this for student assessment so you see it generates random websites
for student assessments but just go through each of the parts individually in here you can see we've got a student what's all six names in an eight it's created a copy of the jewelry website for that student copy of food website for that student so creates a copy of one of them at random then injects random vulnerable both its end to that student way back and then all the injected volumes of all stays involved for me so when I'm marking I can see what each student was facing but also as part of feedback I can send them the bread and say here's what you should have found so a nice a little bit of feedback for them and I think feedback
is really important in this this case here's the current injected vulnerable face I have not injected cross-site scripting because they've been so many so many of the men they're pointless likes nice little a believe it but things like super when Jackson proxy request forgery a lot of what is in the some that been injected after your folks so things like director drive-ins out of there or it's not there some are random will create some or less so for example each of the Advocate applications have got an odd mineral game as well as the standard user login so for the admin log n I've created a password based on actually txt file some are random so for
example with super injection countermeasures there these are these are a very basic one a lot more now so it's going to pick one of these you see that this one is it says we just felt about when it was one or select on union in there so that's all done at random just a little bit of detail how I've done this it's really not rocket science all I've done is going through the PHP cool in certain places and normalized it so for example anything that I login I've used dollar username and password in the PHP and then I put an include file underneath so the cancer measures the sequel injection there are from that file and my script basically creates
that file so it's not really rocket science there's also a look within the code we're putting tags so my script dog steps through from the tags and replace the tags with whatever I wanted random on this was the feedback that was created for a student's pretty basic tip again where I must have known as much better now but you can see in here that got hidden source codes messages user enumerations possible admin password is service in this case so you can see a useful feedback but what the student should have found when you put them are going through it so use them 10 14 assessment what reasonably well probably too many vulnerabilities but I've got a
lot of good feedback from the students in there and kind of also dealt a little bit now but given students of practice platform is not this is not really fulfilling what I want to do here I would I would like some kind of self-contained application where students can create things and instant will get feedback and maybe a little better training in there as well so smug version 2 i'll give you a little demo this in a minute but very very simple web interface why is the student to create a vulnerable web app with definitely different types of all of the most days then taste it I get feedback on it so I have a nice day today my laptop fried at
eleven o'clock this morning thanks to mari anything Rudy for your laptop so let's hope that this works so I've got this running if I Salim rise to get it running in a tiny core virtual machines so the entire thing is rained about 250 Meg ceux qui tam it quite amusing screen here will be the truth right so this is essential here you see all those you create a random vulnerable web app for testing purposes pretty straightforward if I create a new web up and I've done it with a kind of base I can see all vulnerable is a rare no vulnerable is present or run the vulnerabilities so I'll just do once they run the
vulnerabilities but in here I want to make sure that a definitely of sequel injection in there so I can make sure that these are definitely on or I could have said no sequel injection yeah so can do that create the web app that's the robot generated there's a little bit of information is the bottom you've been given a user account hot club is the username password and sat Bob your task is to test it so you can call the web up I'm able go so that's that one you can log in here and do a full test of it well back a bit at the end and then go into the injections and this is a less
than that one that's been injected just all getting some of them there's a cookie that can be reversed that's the way it's been created directly frozen zone a volt going a bit simple injection there's a countermeasure is used as a bit forcible admin passwords this is not an easy one but that's obviously in the debt ceiling that I've used so next a nice and simple we're black we create another one all vulnerabilities robot this is my hope random kind of comes in oh yeah you just knew it was run the balloon of creating seen one so yeah that's created another one so it's a web file manager in there can be used on as we see each point if you go back and see
what was injected so I it basically means that student can sit in practice and practice and practice and practice and also individual vulnerable is so someone wants to become an ex gotten sequel injection they're nikka just create site after site with different countermeasures one what's the things we doing this ten ton of things to do is immoral think about it there are more things to do number one outcome the shooting the force that are about to come in see what their phone and trying to make it better more based web apps I've got that another sex that I've downloaded that I could fit in fairly easily I've medium wall so the saints currently very very vulnerable more
vulnerabilities we're talking to a number of people at security and live suggested vulnerable is that could be two ends or I'll put their own web server configuration vulnerable is there's no reason that I can't add in the environment as well I've also got an honors project student David who's done a great job start the year I told him this is what I'm going to do here's your possible is he disappeared that I hadn't seen him for a bit for months and he came Barton when he showed me all these things is implemented so there's lots of things when they're like passwords throttling and so many things he's actually got a training system in near as well so I will be incorporating the
house stuff into this as well before releasing it swing kind of ribbon rather the world alone the same kind of thing infrastructure been testing classes I give out a network latissimus you all the same all these things about same network they collaborate so how to make this more challenging I had the idea let's try and create a random Network generator done it in pyro Cheryl power is absolutely fabulous you go online most most of my code is joining together routines that I find light it really has a copy and paste job I feel like a student just going online copy and paste a couple lines in between it but there are two routines for creating a domain controller you know a
simple routine you should download and call it you know so that's my code I feel that virus but whatever but this was invited application a definite vulnerable network for every student 2008 server and 127 so the general have to share rose and cue clients it's multistage partial application but the batch files in there all we do is really control thanks so I mean in a minute the reason it has to be multi stage is because you know what windows like you trying to steal anything properly then you must reboot your machine so it's a bit of a pain so it's hard to be multi stage so a state essentially for the windows 2008 server four stages stage 1
2 3 and 4 stage 1 and this way values and that's things like tons off the firewall on UAC just the mixture of the scripts runs run okay sets IP address and the windows have you ever set the machine name then you must be bit you've got new options so that's stage one and then reboots and run stage to set the opposite to be in control stage three starts to do a bit more positive things like adding and users look we know a lot more detail in a minute also as in computers dns and still somewhere when the services as many as i can get away with without asking me to reboot and then install some patches reboots stage
for the stalls some more windows services configures the services and also install some third-party software so going to go through each of these part exactly to these parts and any file controls also i've gotten any file with everything in here for example the domain name uat you ad target com also things like organizing organization details and they've also good things like the department's for groups within the network and things like usernames that being random were created I know so once that I'm going to use for passwords for creating for users so adamant random users see any other in random users I've got minimum possible paths or the length of maximum but I've been a percentage of users with
dictionary words passports so in here I've got forty percent that can be controlled I've also got users with dictionary force numbers so forty percent the users addiction for numbers and I've said twenty percent I'm going to have good passwords that are very random and then creates each of the groups so but human resources legal finance engineering sales etc and if there's users who are in the admin group that I've got good passwords these are up there admin users were pretty much uncrackable passwords and also three users in here that being created they have in administrative group that got crackable passwords and here I've got I think of their it's 102 102 users have created and it dumps all this their file
so that i can I can take it away when I'm marking here's a deal in the random users exceeded anything that's happened that any of the number one our dog Athena was created with a dictionary password the next one is additionally fast word for a number down he ever got a very difficult possible to crack but also we've got an admin with a bad password n here n da lamp whose password as in the dictionary and that one's there's an admin was a difficult passport so it just kind of goes through that hchildress through that and also i got pageant patches up to a random day or specified date so i can say patch the
server up to a year ago or if it'll do it randomly and the way i did this was i used the third part of packaging that they knows all these patches as msu files and it's very nice that means i can do this nore stopped because again windows when you do in a patch what should we start with some so the very last one restarts okay also installs when the services using powershell and creatively easy to install windows services so you see the kind of thing Sutton's install and dhcp tftp smtp just however many services i can do end there at the end of all this is that kind of sample output that you see in the windows 2008
server that we've got all the groups have created in here that will use HR and IT legal whole pile of computers the near of dummies computers if you're looking each of the groups we've got users that have been created in there and also the administrator as you can see there's a number of a menace it has been created in there as well configure the services what I try to do for each of the services I've created one PI Rochelle file that sets up the service secure and one insecure so for example in there I've got dns this one allows is doing transfer which is not good so that's that's a vulnerable one evident key sort of SNMP we've got a public
greed Illinois and there as well so there's 2i or side my program i can set to run the moist select one of them or always making vulnerable depends on how we want to configure it I didn't flip out the applications find this package am called up deploy quite often own internet as free up before it's been around for years and years but it still works really really well I've only got a think I've got to FTP servers in here that my application users but allows you to please snap short system so you snapshot the system and by that I mean services registry files the kind of things a snapshot or not then you install what you want and it may be
apache web server with a website and all the configuration in there and then you post snapshot it and it creates an msf file of everything that you've done that changed so i can set up say apache server in 20 different vulnerable ways with a different msi file for each of them and then see it at random choose that one or choose that one or choose that one so so brilliant a lot of application it's about 15 years old i've got's quite shocked you're still works but it's a little bit slow but hey once it's created is created yes and what fine is really to create different categories in there so every student will have an ftp server a vision
or the intersection party web server or different types of services in there so anti procedure on a little bit complicated a little bit complicated i'm using a vm run command comes with vmware the syntax is a little bit awkward but once you crack for syntax then it's answer and creatively easy to use it allows you to run a vm revert to snapshot it allows you to create shared folders to copy things over to the vm allows you to run things on the vm as well as you know from a kind of single command on your base operating system so this is a century of what this create net what script does I've created for kind of beer bones operating system vm
server one beer points nothing done to at all so this is unclear as a nap short called booted so all over the initial part that might smell does just built up to four VMs and the signal or happy then copy everything over on to vm server one in a folder then a copy batch files onto each of the virtual machines and run all these bad spells in each p.m. now explain why you need to do that in a minute but this is my situation we've got to service to clients we've got go runnin on them and what Gordon that does essentially it sets the IP address now if you set the IP address then we can
communicate with all four of them can communicate with each other and in this case I'm using server one as a controller okay so that's essentially what it does is certain way and then the first controller will go through my four stages of creating that the link and for all the users with all the services etc etc once it's finished at the very end okapis required files to the secondary controller and each of the clients and then the cause we've got fixed IP addresses we can pierce exec enter them and say no checking action and essentially what happens is the secondary controller will be set up sets opposite to be in control none of that so it does all that as well the
client will join the domain logon is a certain user and the same with a client to so reasonably complicated procedure but you know it will straightforward paint on a future work in this again number one Clinton network traffic with an idea that I've got that I think it would be nice if we could see every five minutes get the user to do something or specify beforehand and from a random 10-point get a user to click on the link go get always use a cop in an email and settle in thentis and use something like respond on or something and you know harshest ugly so what of it areas in there more windows services and each
other and want more configurations in Windows tweaks lots of them as well more third-party applications so whatwhat's of them to do and of course then you start thinking well i can add in virtual rules as well so we're going to we're gonna add in look the whole wall I don't virtual Ritter ever you said you haven't got a linux server organ are there no one except so obvious thing that all certainly possible the time to do it is we're going to take a while but lots and lots of things ender combining the two of them this was canet an idea what HUD I've got a module done in fort here called been tested where the students in
traditionally have been given some kind of target that the op the attack and again we've all got the same target so had the idea what combine all this but not creating four different virtual machines pre create everything in there so all the usernames all the services everything required for each student so student one will have this set up student to go of the set up students will have all these and the way I'm doing at the moment you built up the first vm which has a web server you choose your name from their head submit and it's set up the environment for you and the veggie way so it means that every single student has got a different
web application they've got different usernames and passwords and services at students are working on this current like some of you in front of me I'm working on a common one it'll be really interesting to see the feedback that will get from this so I can kind of change it again more and more father work involved in here I was thinking that we could of the same set of the M so you built before the MS let's em office to swag you can see I want to create a network with two hundred users ten percent as more crap parcels native percent than the good passwords I want numerous services and then heck goal so it's very very similar front end and it
will go away and generate it and then the kind of injected that the volume of office the solutions are there as well so students if you want to practice there you go you know help yourself I like the instant feedback of that I think is is the real good 11-point honest so something up certainly find of useful utilities I will be releasing them as soon as i get time to get my arse in gear and do it properly if I said we want to add in the honest projects stuff in prove there's a lot a bit stuff in there but future what goal or you know any of you are partly students in subject or norse projects
core [ __ ] in this anyway thank you for what was then a rattle sit very quick all over Martin's instructions that we all need to go to the pub [Applause] that's got a 25 minute for questions will help you beverly hospital seen it
yes yes a whole you know that's again another future what there could possibly be done and i am thinking again that would make a great on this project for somebody doing that you know one of the big issues would stop this about one of the big issues i know someone else at another university who's trying to do the same kind of thing and they are trying to set this fantastic framework saying as i haven't seen any out group from that it doesn't watch it and there's two years down the line there's nothing there so my idea was definitely a let's make it work number one and then let's get clever with that number two so
yeah I totally agree can't be done it would be excellent anyone wants to do an honest project I'd be delighted if you did that but yeah just a quick quick little look at this is this is essentially a spring running to begin mer it's all running a single virtual machine i'll just briefly show you this is the syntax in here for the vm run command see it's awkwar-- awkward-- if your vm run without the snapshot vm run start an evil shared folders and you see underneath forgot I'd share folder set share folder state etc then underneath that is basically like a copy of an oval one so sent does it all but awkward but keep going through
from there is visit we just kind of create network the whole phone takes a bit 45 minutes to run so I certainly don't want to show you them all up but you can see it's run vmware it will then restore the snapshot then the files are all copied over so you can see all the files copied up so that's all done from the single batch file which has made my life pretty much pretty easy most of it but that's nice essentially the vehicles through sorry i want to show you that as well since I point it is more certainly an issue at windows 2008 server from import and passwords etc has a secure string in there which is Midwife a bit
easier because my application doesn't import text passwords imports a strength like this and I'm hoping that I can Kenna it's going to make it difficult you give hacking students a challenge like this the new reverse engineer it right enough so I've got an issue in there well I'm trying as much as I can to try and hide that and if I can think of a bit an idea they know will but as it is yeah it's difficult however I mean would you really go through that process of you know do the digital forensics is your boredom virtual machine you cracker absolutely in a pen testament good yeah yes Decker yeah you're the Hawkins student alia thang thang in all the ways
that you can submit that's good I'm not saying that's about like I said there's a good thing you know that's thinking outside the box yeah you're definitely right however I still think a lot of these things a student spent that when's the time doing that then just crack are doing the paint test you know oh you're right you're right but I still think you be quicker to advantest you know well i'm doing the digital forensic job of doing something really incredible cause i'll just good point i do pain test so I've got to tell you the answers to your coupons well don't we reason you're here cheese I was expecting operative graduates to told me because I
was still got jobs garda you guys you've got the right to told me you've got a job they've got a lion Viet an example [Music] yeah which is very possible absolutely setting a vegetarian what the idea is diff infection the company with a lot of colleges it should be a walk with us but hey that's not really the testator this is to be one the traditional application I'd like to take all these e applications and find on the run on water and educate me quite a while because the code is not really exactly which is fine no yeah
yeah I'm not a victim if ago we invented on on your documentation that's all wrong but that's awesome yeah procedure palace you know it soon as we just certainly where people to project regeneration a set yourself before and you don't example 11 another wonderful people don't get also solo material contact three that accompanies people who are budgets and puppies who said they chose it will give you suggestions and see a bit better because but my number one I get that is education but number two are great for whatever company HTC and we're ever take care and use other people to stop me if I could said at the [ __ ] said well and you're
going to you immediately I want and take works often and your baby LOL application center yes yeah I said most of you can't yes yeah so if you want a copy give me show you this in today to do it I find a wiggle in your walk dog don't use your Lots as always it everything plays it all the Western a 50p yeah you're right i guess i could imagine wantin more papers I foundation heads up to this weather is correct youtube or I keep my fav future what I mean if I can get 20 people to deal with mr. Jackson a [ __ ] or nests that would be fun fantastic good there are so many things to be done with it
you know oh yeah good yeah I've been that would be really nice then again I think that shows what Martin's go to a company because I want my students the base weapon you know so affiliate happens the end it's going to kill them we've done this in the past is that we were asked before there would you like our students to test your website and the people with math websites will say no the person whose website has put it down secure as the person is going to all Yelp it low to be able to give you so behind as the students and there's no vulnerable and then it like handing over all the bodies in it and it's all
destroyed for the students to start off with that they're not fighting an innocent so yeah I can see there's been kicking on by a company and then doing that yeah definitely Jeff one okay that's a hopeful winter a week something hopeful people good well you know we would outfit and do do do anything with it because I don't think us that there are people who've got this idea out there but I've not seen any results you know great up with an idea and twine on it for three years that no I want something to watch so thank you [Applause] you