2022 Keynote
Show transcript [en]
I'm going to do this are you ready okay cool we're going to start a little early sorry uh but I um Greg is a uh principal Cloud security researcher with la lace workk Labs uh where he focuses on large scale data science and threat research intending to help secure customers Cloud environments uh fost has led the research team built and ran a Global Security operations program consulted in red teaming and worked as um as security analyst for federal government in previous roles and um is all around a great person in the community I added that um uh in his free time he spends time with his wife two children and is an avid Runner and swimmer so please
welcome the keynote today Greg Fox [Applause]
there's power there too yeah Power
perfect I think this is the first conference I've ever been to I don't need an adapter this is amazing try it try it this is unheard of you guys are too prepared all right see if oh there we
go all right perfect well thank you all so much for for joining us today um man I can't I can't uh even begin to express how nice it is to actually be in person for for this event uh I I remember talking to you guys when you were first planning this you know through years ago and then all of a sudden you know everything changed and we had to go online and you guys you guys did that and you know actually converted very successfully um you know we all had no clue what was going on uh so so Props to you guys and especially pulling this together you know getting us all back together here this year so let's give a
round of applause to all the organizers uh such a great events man talk about a venue too this is cool this is this is way too fancy I'm here to class it down a bit so be perfect well so you know this uh this talk the fun part of the keynote is I didn't have to submit an abstract so this is going to be like an amalgamation of random stuff that I just find very interesting so hopefully you do as well and so uh so you know uh eron's introduced me um for those of you that don't know me uh I'm a principal Cloud security researcher with lace work uh I'm also an advisor at uh multiple
startups a couple of them here in Colorado which very happy about um you know all that I think is you know on on the surface the job fun stuff but I think one of the more fun parts of what I do nowadays is I working with a lot of people who are getting into the space and trying to Mentor people who are trying to learn uh and grow and and come out uh into this industry because it's a hard industry and so that's why I'm going to start with you know why are all of us here right on a Saturday why are we spending our time working uh you know trying to learn about uh how to do our
jobs better how to secure things better and I think uh it comes down to one thing at least for me we're all pretty passionate about this right this is something that's important to us uh that I think you know we would probably do at least I know I know I would probably do this even if I wasn't being paid for it so I think that's why a lot of us are dedicating our free time over the weekend we could be at home doing whatever to being out here learning um and so you know I uh applaud all of you who've come out here to listen to me ramble um because I think it's I think
it really speaks volumes to you know how passionate important uh you know these people in this room are to this industry because it's hard uh many of you guys know AJ good friend of a lot of a lot of us here and I I found this quote really good I think he hits the nail on the head um you know starting in cyber security is very hard it's not an easy field uh I talked to a lot of people who want to come into this field because there's money in it and stuff like that and I always tell them like cool go to sales or something because you're going to burn out uh if you're not actually
interested in this you're not actually willing to go above and beyond uh because that's what it takes to be really good at this um especially nowadays you know we uh have had our world shifted all of us and and all of us in this room are much more fortunate than a lot of people who didn't have the ability to go work from home and go log in and just you know work work on the computer all day so it affected a lot of people in a lot of significant ways um you know now we're dealing with a whole other kind of tumultuous times we have we have the war going on which is affecting a lot of things uh our economy
now we're definitely seeing that impact there and people's lives are being being shifted and then of course you know terrible mass shooting just about every day in Colorado all of this is really affecting a lot of things and uh you know not just uh you know not just in uh the personalizes but cyber security as well is all going to be impacted by all of these events um especially as it starts impacting the economy um you know as we saw recently there's been a lot of companies affected a lot of individuals affected by this uh you know our company as well recently had to lay some great people off uh it's unfortunate and if you haven't seen the site it's pretty
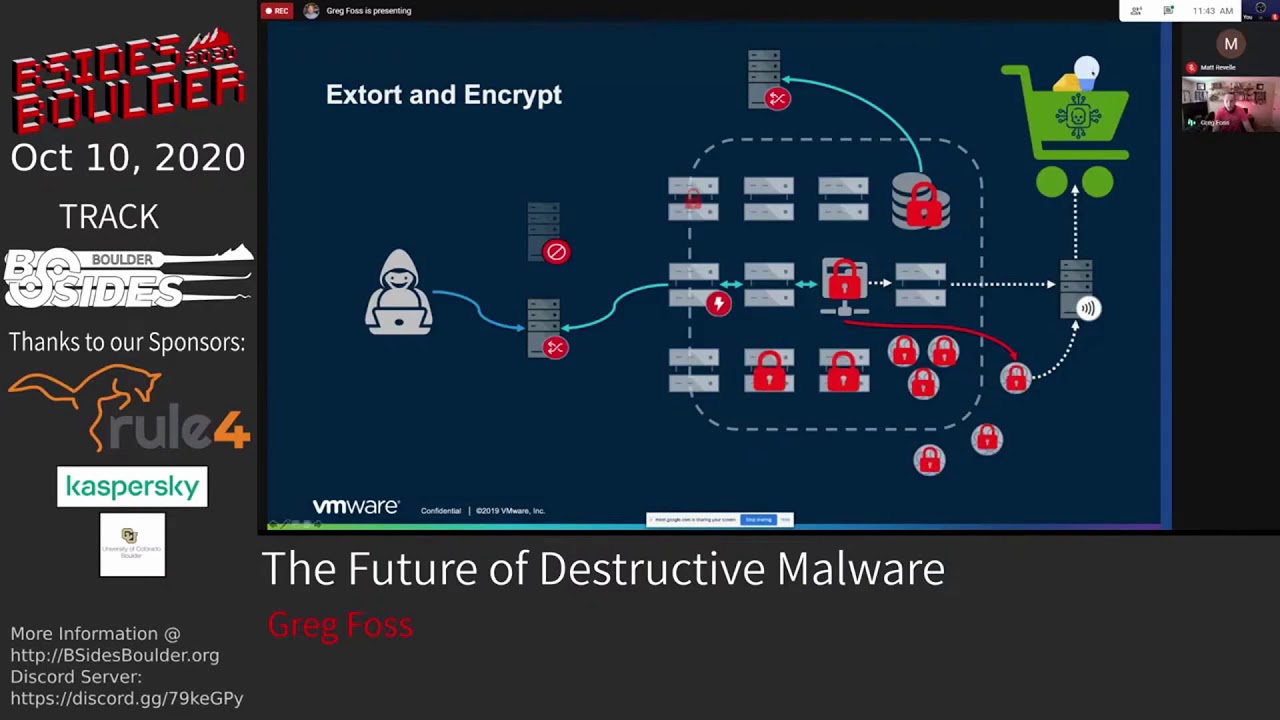
eye opening layoffs.fyi uh man there's a ton of companies out there that have cut a lot of very very good people recently a lot of comp companies have completely gone under and um you know it's it's kind of heavy way to start this talk I promise it's not all like this but it does lead into the main topic I do want to hit on which is cyber crime uh you know for years we've had so many people focus solely on advanced persistent threats and and all that kind of stuff but the thing is like most companies cannot detect or prevent cyber crime basic script Kitty stuff uh is getting by just about most companies that a lot of us who work with a lot of
different companies see on a daily basis um so that's kind of the focus I want to talk about today is is cyber crime in general and uh really centering around how technology and some of the improvements that are being made uh in sort of the whole underground scene are making it easily much more accessible for people who might not have been uh into cyber crime before so what am I actually talking about here well how many of you have heard uh from many people that my business doesn't do anything important we're not going to be impacted by hackers we don't have sensitive data like all the time people say that they're like we're a school we're you
know whatever you know we're hosting providers streaming we do these kind of things the thing is uh hackers are very opportunistically driven a lot of this is just gaining infrastructure gaining ground so that they can perform other attacks down the line so when you look at all these different types of businesses I I really like showing people how attackers view their business and it's eye openening to some people you know schools this is a prime target for emails uh and emails from educational institutions get by a lot of filters uh very prime target and we'll actually show some numbers about why this is so key in a bit hosting of course Anonymous infrastructure if you
can compromise assets you can stage your your malware your command and control infrastructure on other people's computers kind of gets you in the clear a bit what about streaming well that seems like a good denial of service platform to me e-commerce how many people have heard of Mage card you know the credit card skimmers injecting JavaScript stealing credit cards when people are paying for things online social media anyone here do red teaming that's the first place we go we're trying to figure out who to Target who's going to have access to things uh everything's out there now you don't even have to do much work to figure out what tools the company uses who works
there and everything else in between image hosting well you can store your malware there you can store payloads sometimes steganography if you want to do hidden messages and and that kind of stuff big one that's uh scared me recently is these managed uh service Prov providers pivot Points all of them have access into companies they have credentials they're whitelisted you know all these things where you're already purposefully putting blind spots into what they do because you don't want to trip your alarms uh because these people are logging in anyways through legitimate means perfect Avenue for attackers and we've seen that uh come to fruition recently in a couple very prominent attacks um so you know just
just setting the stage with these are the kind of things we should be telling people when they say they don't think they're a Target because everyone is even personal accounts right anyone see this tweet when it came out brutal brutal right especially for those of us in Cloud security this is happening every single day to people uh and hopefully not at this scale like there's a thing called guard rails that you can put in in AWS so all of a sudden if your systems are going wire and your uh your billing is going through the roof you can at least stop it um but pretty scary I mean this guy uh you know ended up
being charge $45,000 for someone going into their systems and installing crypto miners uh the real kicker here too is the attacker only made like $800 from this attack which I mean man but if you're using someone else's computers like the cost benefit doesn't matter uh We've even seen somewh people are spinning up landas that do like crypto mining even more exponentially uh you know uh costs that come along with that um but also incredibly inefficient I don't know why they would even do that there's a lot more better uses for lambas for attackers but still oh that's a good oh man that is a very good point I think that's like 25 cents today so it's
even worse man that's a very good point well and so you know that that brings us to um you know ic3 always tracks uh the losses associated with these types of attacks and I I was like just showing the scale at which uh these these uh crimes are very successful and these are just the ones that are known and reported to uh to these institutions there's a lot more that that don't even fall into uh you know these these lists here but as you can see uh just last year the total was 6.9 billion do uh in losses due to cyber crime in general now this kind of encompasses everything this isn't just you know one type of cyber
crime or another but uh significant uh amount of money being lost here every every single day um and every year it's just about doubling they're expecting this to double again uh this year which is terrifying so one of the real uh kind of core components of this is business email compromise um you know business email compromise is one of the most successful by far uh forms of attacks that we're seeing today uh business email compromise alone accounted for 2.4 billion losses uh in 2021 and that's just what's known right uh and that's from businesses let alone the personal impact personal accounts that are targeted um because this affects everyone in different ways um basically just you know committing scams trying to
get people to send money and it's crazy to think that this much money can be generated a lot from like gift cards and things like that uh some of these companies that that do those types of attacks end up making just million doll uh you know like uh hundreds of millions dollars just their single company in a year uh and they have little like actual businesses uh that do like cold calling and stuff like that but then they also have these illegitimate factions so that when they're audited they can point to here's here's our legitimate business and they have everyone else kind of hide uh what they're actually doing in that other side of the of the building um but
often times are trying to go for large transfers of money in one time um you know uh really uh trying to get people to transfer money out of the company just by submitting fake uh forms for purchase uh orders and things of that nature and then targeting individuals uh for gift card scams I mean like all of us are affected who in here uh knows someone who's been affected by a gift card scan and fell for it quite a few people I have family members that have that have fallen for it it and the sad thing is we always find out about it too late they tell us after the fact after they've already sent like three grand in
in cards to somebody so it's sad it's a very uh kind of terrible scheme that affects people especially the most vulnerable people uh and then romance scams this is a whole other level of evil these people are are terrible uh the the scams they commit some of these go on for years um you know a few of us were just had a conference where someone dove very deep into this and it kind of open my eyes to just kind of how terrible some of these people are uh to the extent of you know some of them are actually practicing Juju and committing very crazy uh ritualistic kind of uh kind of things with money and stuff like
that in order to ensure their scams are uh successful um really kind of interesting when you look at like the people behind this so uh there's one group if you want to learn more about this called the Yahoo boys who uh it's kind of terrifying when you look into like what do in order to ensure their scams are successful in these kind of JuJu rituals and and things like that but there's a lot of documentaries out there where you can look into and and learn more about this but business email compromise uh is one of the biggest problems I think our industry is is kind of facing today but the stats from it are pretty
interesting right so uh one of the things we've been doing is collecting a lot of the the numbers for uh what's for sale on online forums uh so one of the things I I like doing is going and scraping this content and uh automating the collection of seeing you know what's for sale what's the dollar value how much is out there um and the real interesting thing here you know we're talking about educational institutions uh you can see they made up 35% of email uh compromises that were for sale so this is basically someone gains access to an email account or a set of email accounts or even an entire company companies uh email servers and
then offers these up for sale online uh and over here you can see the pricing as well based on each uh essentially uh provider but what's real interesting here is those educational institutions there's a lot of reasons behind it they kind of Market it as like you can get discounts on things it gets by spam filters you know all all those kind of things that lead to it being one of the more prominent uh items for sale on these forums um of course uh the pricing is very cheap you know for around $5 to $10 you can purchase access to someone's email account uh and then you can use that for whatever you want you can go
through their uh list of contacts you can spam all them you can use this to Target other companies and things like that um just infinite kind of uses that attackers will find just for email accounts and these are very abundant if you look uh if you do any crime whereare research the big one I think um the that I that I really want to highlight you know with this whole talk right is just like these cyber crime markets have really changed the game over the last few years uh lowering the bar making it so people who have no clue what they're doing have access to these tools and techniques and resources in order to commit some pretty uh serious crimes um
you know right now you could purchase these emails you could purchase access to systems you can rent access to a ransomware service you can rent a command and control server you don't have to know anything about how to launch these attacks or do anything they come with step-by-step guides uh you know we saw recently with the Conti leaks uh they actually had a training program for onboarding new people and they even told them that this was like a legitimate job and people didn't really realize until they were there uh so they had a very high turnover because of that which is kind of hilarious but uh but when you look at these com these uh
groups a lot of them operate like legitimate businesses they have someone at the top they have people kind of directors running different parts of the operation uh and I think the K Elites is one that you know really uh highlights this because uh due to the the War uh going on in Ukraine right now they were split right they had one group that was in Russia and they all of a sudden came out publicly and said we support Russia and we're going to you know attack Americans or anyone who you know goes against Russia and then the ukrainians over there also team members were like [ __ ] that we're going to dox all your
stuff online and they did and so we got to learn a lot about how these groups operate in terms of business structure so it's real interesting but the scary thing for us is like this really lowers the bar and makes it easy for a lot of people to get into this space who might otherwise not uh not be able to or not have the knowledge to do so uh which brings me to initial access Brokers any here here of uh initial access Brokers these are essentially these groups that uh or individuals mostly that go and compromised assets they as the name States their uh you know main goal is just gaining access to things whether it's personal resources
corporate resources things of that nature and then they just turn around and sell it uh online often for very cheap some of these you can buy access to uh you know personal assets for around $10 um you know this has been going on for a long time the big part uh the big change I think is the resale of corporate access uh you know we've seen that going for you know many thousands of dollarss depending on the company we even saw a few years ago there were three different antivirus firms that were offered up uh for sale online access into their environment uh they also sold their source code uh which is also a very common happening in these
groups so what do these look like right they come in all sorts of different shapes and sizes and forms uh you can see this one this was initially posted in uh 2018 this group is still operating by the way the Genesis store uh you you know they just keep shifting infrastructure and whatnot uh but essentially they sell access in a lot of different ways um you know they'll have browser fingerprinting they'll have logs that have been exfiltrated from environments they'll have just St uh straight credentials remote desktop SSH things like that um you know and sometimes they'll even just have rats where you can just log into systems that are shelled uh especially web servers
the web shells where they'll provide credentials to to access um and the breakdown of these is kind of interesting this is a different store this is a dedicated actual Marketplace and you can see the breakdown of the assets that they have for sale uh quite a few assets as well so C panel access uh into various servers leads uh that's commonly emails so that's like email lists uh and leads are basically what spammers will take so they have a Target list to go after um SSH RDP SMTP is the big one uh because then they can relay their spam they can do all sorts of things that allow them to commit uh you know more acts of Fraud and and things
of that nature but it just you know goes down from there and this is only growing uh every time we find one of these stores or one one gets taken down uh like five more pop up and so it's actually like become like a full-time job just trying to trace all these and and keep on top of them uh because they're always changing and they're always improving and there's always new uh upand cominging stores that are coming out with more and more more offerings at cheaper rates um but the big one I'm real interested in uh coming from lace work is uh these Cloud uh providers access so you know essentially selling access into AWS gcp Azure things
like that giving them access to the management plane itself um and the funny thing is like attackers have no clue how to properly leverage of this they just go deploy crypto Miners and stuff uh but that's the thing I think will change over time as people start getting more familiar with capabilities of what is possible uh when you access Cloud environments directly which is which is kind of scary uh but these marketplaces are are real interesting this is kind of what one of them looks like um so you can see here they give you a breakdown of kind of what assets are for sale so this is a remote desktop uh protocol Market uh and basically they give you
information on like does this have admin rights uh you know is this blacklisted from like already spam and and that kind of stuff uh you know what's the operating system version they even give you a couple octets of the IP address which is interesting uh you know what country and and all that kind of stuff and all of these forums or all these marketplaces essentially run kind of in the same format as this um and you can see very cheap very cheap to purchase access to these systems uh because then you get into this compromized asset and you basically you know now have a clean system where you can go and commit more more ax crime from and so that's
something we're seeing uh growing exponentially just about every day now when we started looking at uh you know who's selling these and where uh what the pricing is what was real interesting we were looking into RDP we found Amazon was actually the number one uh compromised uh Cloud at least management type of uh assets that were for sale for RDP uh which surprised me I would have guessed Azure uh first and foremost but apparently tons of people use AWS to run Windows which is kind just kind of funny to me but uh interesting thing here when you look at the pricing uh most these assets are available between like5 and $10 these ones that are much more
expensive uh that kind of skews it uh those are usually corporate access which kind of really extends the price on these but still relatively cheap uh this one I think was $300 to gain access to a corporate uh one a system within a corporate infrastructure now SSH offered up much in the same way uh but a lot more variability a lot of different providers uh as you might have guessed with this one digital ocean by Far and Away number one provider uh I like to call it a provider at least um because how many people in here have done any ir and not come across a digital ocean server right so it's I mean something about it the
attackers love it just as much as uh the customers so uh and AWS of course this one makes more sense to me than the RDP uh but you know those two make up about half of the assets that are offered up for salees so just real kind of interesting um you know breakdown of uh you know what's for sale the pricing things like that uh and we did do a lot deeper dive into this so if you want I can give you a link to our our report where we kind of covered uh this in more detail uh if you want to dig into some of these stats and and learn more about kind of how how these operate did you
purch uh let's talk when it's not recorded and yeah yeah exactly well that's the thing right right so operating in this it's it is a good question because you know what what line is safe to cross when researching these kind of things you know and and that's something you know we try and stay above board uh when when doing this um but man like there's a lot that can be learned should you know access to be purchased and and things like that um this one of those things we have to weigh the costs of like do we want to risk ourselves and stuff um because that contrary to popular belief cryptocurrency is not at all private uh and it's extremely easily
traceable uh even through tumblers now some of the Tumblers are actually operated by some of the companies that do tracing so uh take that for what what you will um you know when you when you do some of this research you always want to be very careful make sure never touching anything from your direct IP um you know all those kind of things to to make sure you're not uh implicated um because just recently you know very popular uh Forum The Raid forums uh primarily was like script kitties and stuff for a long time but then they started having some heavy content on there there was Alibaba access to uh their systems was offered up uh on there
and not just for sale they just leaked everything um so once these really high-profile sort of breaches ended up on there uh all of a sudden it caught the uh fed's attention and now that server is taken down the kid who was running it is in jail um and he was a kid too which is you know kind of fitting um given that the whole site if you ever looked at is weird you got like a default anime kind of picture for your profile um real interesting site but uh but essentially you know now it's taken down the uh the uh federal law enforcement actually operated it as a honeypop for a couple months in in that
kind of interm when they took it over so so you know all of these when you're investigating these be very careful um but back to uh you know how how these are are offered for sale um what you're looking at here is this is a bot uh that I wrote to just automatically collect all all of this data and so when new systems show up for sale online we get alerts and slack uh to notify us about these and we get pricing data and all that kind of parsed out and sent to us so this is just one market um and here you can see you know offering up access to to AWS credentials um and these are
kind of the main ones I I tend to alert on just given our our business model and our focus on cloud security um but there's a lot more where this comes from and it's mixed in uh even in some of these more script Kitty forms there is some interesting content that gets posted there uh but the real interesting stuff is the ones that you have to get into kind of the underground groups and that's where it comes to you know do you have to prove yourself do you have to show things do you have to purchase access and then that starts getting into that gray area where where it gets a little more concerning but the Hosting account
resale so looking at like all these Cloud providers pretty interesting we we were guessing AWS would be much higher on this list but no HostGator by Far and Away was one of the main hosting providers offered up for sale uh and and you know we're talking about hosting providers here I'm looking at like that management plane so this would be like access to your GoDaddy account and and things like that um so blue host you know made up the other kind of quarter of that um but the pricing for these extremely cheap uh especially WordPress access I mean WordPress sites are compromised like like there's probably 10 that got popped just in the last five
minutes um and so you know a lot of the investigations all of us do we go back to oh this was on a WordPress site compromised hosting malware all that kind of stuff um but you know for those that don't have like web hacking skills or the ability to gain access to these um they can just purchase access and then they can do what they want with with access to these hosting providers um so just kind of interesting you know this is more data you can check out uh you know within our report if you want to learn learn more about kind of the breakdown and uh you know the business kind of behind this like how these
attackers operate and things like that but the funny thing to me is the lack of creativity in all these attackers all of them just deploy crypto miners uh you know like like q and I talk about this quite a bit because we track we track a lot of the same same actors and they all just go in and deploy cryptominers a lot of their malware is just bash scripts and Python and just basic stuff not even like encrypted uh the most creative is they'll have Big B 64 encoded strings that will turn into a script and execute and it's nothing uh too creative right uh cuz all of us are like looking at this from another angle
it's like man like what could you do in terms of impact if you getting access to a cloud environment so this is one of the things we like to simulate within our lab is like what are kind of the scary things that could happen uh and so this is one I think is pretty scary we haven't seen any attackers do this scenario yet but um I I think it's a matter of time till people figure it out they still go after you know just encrypting assets directly like you know Linux and windows servers and just going the easy route and just encrypting those assets um you know lately we've seen VMware targeted in a big way they get
into the esxi server and just encrypt everything directly um and so you know that's one just rampant like all over the place happening all the time um plus with all these new vulnerabilities coming out uh in their software it's uh all too common occurrence but I want to talk about AWS specifically and S3 so a lot of people do store quite a bit of data in S3 so let's take a look at our little S3 buckets here I'm to show you kind of what a ransomware attack on S3 looks like uh so right here we have our of course sensitive customer documents probably in a public S3 bucket to make it more real world applicable right um
but essentially you know we see we have our files and stuff and let's just test it out we'll download one of these make sure we can read read this file so there we go we got our Viking helmet I chose a Viking helmet because we have a b bunch of Icelandic folks that we work with and like all about the Viking culture and so uh so cool we can get access to our content here looks good well let's go ahead and execute our ransomware let's say we stole some credentials from a mobile application uh which is a very common occurrence as well um pretty simple attack takes not much time to execute and as you can see it's just a basic
bash script so essentially what I'm doing is I'm generating a customer managed key encrypting all of the content uh on the Fly while I transfer it to another bucket so as it's being transferred uh it's actively being encrypted and uh removed from the previous bucket also go through and erase all backups now this will work assuming uh they aren't using the cold storage and and things like that but essentially you can see here's all of the uh key material that's generated locally none of this ever touches Amazon servers so there's no way Amazon can help you with this either uh I also downloaded one file just to make sure I could read it during the test um but
essentially when we run this uh you know we have our uh our new ransomware bucket which is where all of these files have been moved to so let's refresh this page and see what this looks like now there we go so now we have our original bucket still there but we also have this new one oh weird fun fact with this too if you transfer between uh zones it's extremely costly as well so talk about adding insult to injury so so the only thing left in the original bucket is now a ransom note so of course the victim can go download this and see oh great like where' everything go now there's a ransom note I have to pay X
doll uh to this Bitcoin address so pretty pretty scary scenario and now if we go take a look at the new bucket let me fast forward a bit we'll see uh you know what happens when you actually try and access uh these resources so here's uh the same file we downloaded before let's try and download it oh invalid key not accessible the only thing you can access within this bucket is the ransom note itself um so you know pretty pretty uh tricky attack but the scary thing is how easy this is to execute um part partly why I'm surprised we haven't seen adversaries do this given uh just how open a lot of these S3 buckets are uh
and how easily uh this attack can be executed so as you can see they could access the ransom note um so pretty scary right there's no way uh to really recover from this without paying that Ransom um unless you do have cold storage and and you do have your files actually backed up which we know everyone does that right all these people we talk to they're very good about that they back everything up all the time um we can go over here and actually take a look at the key that's generated we can see there's the key ID but status pending import so you don't have access to it there's literally nothing you can do here to decrypt this content um so so
pretty scary uh you know in terms of like the potential of these types of attacks and this is just S3 there's a lot of other iterations you do for the databases for various other cloud services I mean Amazon itself uh has anyone here looked at how many just apis Amazon has that you can interact with you want to take a guess throw some numbers out oh close yeah yeah I think like last I looked it was like 7500 or something like that like it's crazy and then that's the documented ones so so pretty pretty crazy right now we did write a recovery script for this the thing is it only works if you have the keys so um so
it's not like one we could just go cover for people impacted by this you have to have those keys but this basically takes all the content decrypts it and moves it back to the original bucket um but in uh essence of time I'm going to skip past like looking at the details of that but I just wanted to highlight um you know just how easy some of these attacks are and uh you know the the devastating impact that they can have um which brings me to kind of the main point of of this talk like what I really want to focus on here is the fact that like uh so many of these things are just very
accessible to people nowadays like when a lot of us were were coming up in this industry we didn't have much like we had to go find people we had to like prove ourselves to get into inner circles with people uh you know we couldn't just Google things we couldn't go on these forums and just download things and and run them without having any clue was happening um nowadays that's exactly what happens people just go out there and they're like I want to hack X and they're like here's how you do it here's the YouTube tutorial here's like and they just have access to all these things um and it it's really lowered the bar to entry uh and this has had a
significant impact on cyber crime itself but instead of talking about uh you know like how um you know some of those tools and stuff because a lot of us you know see Cobalt strike and and all those kind of things they're very readily accessible this is one I I like highlighting because it shows uh you know the impact that that minimal amounts of data on these forums can have uh in their wrong hands uh so anyone remember the EA hack uh about a year year ago um pretty devastating the real kicker behind this is that they were able to gain access to uh EA directly by purchasing cookies from an online forum for $10 um so pretty pretty uh uh successful
purchase for these uh adversaries so what they did was they bought uh cookies which uh gave them access to an employees slack uh account and so basically the way it works is with uh the slack profile you can load that and it basically emulates the um you know the individual that the the profile was stolen from so you can just go on as them and if your company doesn't have these sessions timing out which most companies don't how often do you have to relog in slack right most people don't don't have to like at all it just persists so uh the attackers were able to get in there and then they socially engineered the internal it folks to give
them more access in into the company uh and from there they're able to gain access to the source code for FIFA uh FIFA 21 and real interesting thing with that if you get into the cyber crime scene there's a whole underground cyber crime scene around FIFA coins because you can make actual real money from those and so they also found out a way to generate FIFA coins by having the source code uh so you know additional insult to injury here but also they had the full source code they tried selling it I don't think anyone actually bought it because they're like why why would I buy Source Code for FIFA uh but still devastating public impact for ea uh you
know devastating impact for those uh you know all those people affected but all it cost them was $10 on a cyber crime forum and just a little creativity and and time well we've talked quite a bit about uh you know General cyber crime I want to talk about something more fun this is a a toy anyone here have one of these yeah nice see it's scary in here right look at all this stuff we could mess with I didn't so I brought mine too I promise I'm not going to mess with things but uh for those of you that that don't know uh what this is this is uh probably my new favorite toy uh for a
lot of reasons because uh it just has so many tools built into it you basically a soft to find radio has RFID reader writer NFC Reader writer it can do infrared has I button uh USB uh hid so you can plug this in and execute the taxs uh all sorts of different things uh there's there's a uh GPO board where you can do Wi-Fi stuff with it uh I mean it's just like lots of potential and the reason I think this is so impactful like a lot of these tools have existed for a long time you know we have uh you know various like like procm where you can go clone hid cards and stuff like that uh
we have the hack RF where you can do a lot of the sub one gigahertz kind of a tax but not everything is included in one tiny little package like this that all of us can just put in our pockets and do very nefarious stuff with that has a very open uh Community that's constantly updating things too like I was just looking at this yesterday and they have an entire database of all the amiibos uh so my son loved that I like hey you want that one let's just load it and uh so uh as as this community is being uh built out there's going to be a lot more uh codes that are added to this
a lot of these you don't even have to intercept the uh the transmissions in order to replay them because people are sharing these online uh there's all sorts of uh uh scripts uh tied to this as well I actually wrote a script which I'll show you here in a bit which is kind of scary um but there's tons of uh capabilities in here that allow people that have no clue how this stuff actually works to just download these things put it on their flipper and run it which is super fun my wife hates it by the way and I'll show you why um but so this is the one of the scripts I wrote I actually did this just uh the
other day um but basically um you hear of open sesame there's like a a tool where you could basically uh brute force uh garage door codes well so I just put one of those on the flipper and I was trying this out of my house and it works very well uh and extremely fast um so we'll just execute boom opens the part I didn't show here is it actually opened my neighbor's door too uh like oh like so and the fun thing is some of these you can't undo like you can't close with some of the some of the things I'll show you in a bit um but the thing is I mean the this kind of tool in the hands of
someone with nefarious purposes is extremely scary right uh cuz all of a sudden they just like download this thing and they can go break into someone's house um and there's a lot of other protocols it interacts with anyone here see how these play with Teslas this is my favorite part this is why my wife hates it so so check this out uh and so Teslas they have uh the sub one gigahertz uh codes for the charge ports so basically when you push the button it opens the charge port well now you can just go walk by a Tesla hit the button pop their charge port pretty fun right it's kind of scary in the wrong hands
though CU you could go out pop the charge port and like pour water in there or something uh you know if someone wanted to really mess with someone um for me I've just been riding around on my longboard and like popping Teslas and it's just funny it's just like super funny to me I know I'm still a child but uh but the scary part so say we want to be more impactful with this right uh well Tesla's uh I don't know how many of you know this but it doesn't use like a normal fob like like cars you can capture key fobs too for cars except most modern cars use rolling codes so you're not going to be able to replay it
and actually get in older cars some of them it will work but the Tesla card uh it's just an NFC card so we can clone it uh so with that you can actually em emulate it uh the problem is I haven't actually been able to get into the car with it yet I don't know if it's something I'm doing wrong or it doesn't have uh you know it's not actually doing an additional component that's missing here uh so that's good at least you can't completely clone this this key and get in cuz you think about like you know when you go and have a valet park your car well what if they just clone your
your card key and then you want to steal it and then uh other interesting thing with Teslas recently you can't do really Bluetooth attacks with this uh but I'm sure everyone saw the Bluetooth uh key replication attack with Teslas because you just come near one and it picks up the signal from your phone now all you need is someone with a receiver near you in the building just just replaying that to someone outside and they can steal your car um although all of this said I wouldn't mess with a Tesla cuz it records all angles at all times so you're like definitely going to get caught um but still interesting but this is another one I found interesting too
so you know when you get like credit cards if you get a new credit card in the mail and they send it in a little envelope well someone just like you know wants to uh steal your credit card uh from your envelope you know you you could this actually works from quite a distance away too uh with some cards but there's scripts that are run as well on top of this so not only can we emulate the code which you can see here we could go replay this code um but we can actually get the full credit card number as well blanked it out for obvious purchas purposes but uh pretty scary right um you know if you leave NFC
enabled on your phone you could do the same sort of attack just bumping into somebody um so so pretty impactful again no skill required I didn't write anything to do to do this it's just built in uh and just very easy to do and shredding credit cards right oh yeah that's good cards shredded you can't you can't get any data off of it well as long as that chip is still intact you can still read the data so one more thing for us to worry about you know when you shred your card and uh you know making sure that you actually destroy those electronic components uh within the card as well uh or else someone could still get your
credit card um so pretty scary right uh these kind of tools in the hands of someone nefarious uh could be could be relatively impactful now this one kind of freaked me out a bit um you know uh we we recently went on a Disney cruise and uh to do anything on the cruise you have these these wristbands and that's how you pay for things that's how you you know get in and out of things you can check into your room with it and stuff like that uh the real scary part is uh so on the cruise they had an area where you can drop your kids off and they go run around and stuff and it's
protected you know they have a a thing where you have to check in with one of these uh and it just verifies that you're the parent of this child well what if someone clones one of these and you know has bad intentions pretty scary you know especially because you can read and write with this you could write it to another wristband that looks like this check in uh pretty pretty terrifying kind of stuff and the thing is this is where everything's headed everything's headed to these touchless kind of payments and things like that so these kind of tools uh you know all it's a toy really but very impactful in the wrong in the wrong
hands so lower lower the bar right it's easy to be a criminal these days cyber cyber criminal 101 um you know there's not much of a bar really for for a lot of these kind of devastating attacks um but for me I just like using it as a toy like I my uh friends and I clone all their pool keys so we can get in all the pools in the area and stuff which is fun um you know this was super fun when we were out at uh lunch um about a week or two ago and I was just messing with this uh so you can uh it has a um RF so I was
trying to change one TV cuz there was a game on and all these people were super invested and so I was like oh this would be funny I didn't I didn't realize I didn't realize it would change all of the TVs except one so so I put on like a movie and all these people started booing and this is great I'm just sitting there like putting it back in my pocket um so I mean there's two Avenues right like I tend to try and be on the harmless side but uh still still pretty pretty impactful in the wrong hands um but you know with that uh you know I think with this crowd I don't I don't
want to try and tell you anything you don't know I just want say like you know even with all the stuff we're kind of facing right now with the economy War like all all these things right like you know just just all of us in here need to really try and do what we can to make a a positive difference and you know try and uh try and help people not fall victim to some of the things we talked about today and I think part of that's just the understanding that like you know what what's capable and and you know what what uh you know the risks that are out there um and so with that
you thank you all very much and uh welcome to bides Boulder [Applause] exciting know and I think I have time for questions oh perfect if anyone has has any
questions mhm the
o so like uh for like RDP access and stuff like that yeah i' say quite a bit of them uh you know show Dan's pretty good at mapping out and like um giving a good number of like hosts that are available and things like that um you know there are some things you could do to correlate and figure out like more which assets might be affected um that's kind of the nice thing some of these forums actually give you a lot of information um there's one I didn't show on here uh but one of them actually uh they specialize in compromising websites and they actually give you the websites that are compromised it's just listed in
the Forum uh all you have to do is log in to access those uh so that's one that we scrape and we cross compare with customers so if we have a customer show up in there we can proactively notify them um but yeah I mean it's uh I'd say it's a pretty direct correlation with what's available on showan
y you could fight one duck size horse or 100 duck sized horses which would you pick if I could fight one duck sized horse or 100 size duck oh man I don't know I think I'd take my chances with the one I man anyone here been bit by a duck that hurts it sucks bad man and big one I don't know I I feel like I could maybe run away or something I don't know that's that's a good question I like it for these marketplaces are you seeing a lot of them on like the dark web or the clear net cuz I know raid forms was on the clear net I'm curious like what the majority of them you're seeing like
where those are yeah that's a good question so oh yeah yeah so so the question is um you know are are a lot of these uh marketplaces that were investing ating on the dark net or the clear net and the answer is actually the clear net like a ton of these are very Brazen very just open you don't have to use tour to access them um like most of the forums are are going to be on the clear they do have uh tour addresses as well um but most of them are just directly accessible now the when you get into like some of the scarier forums those are definitely dark web um you know that's that's the kind of stuff
where like when you have to be invited uh those kind of things there's a trick there too uh so since we have time I'll tell you my my little trick for this uh one of the things I do when I try and get into the forums that are restricted and you have to have a vouch or you have to be a known contributor or something well a lot of them have very bad uh security of their sites so you can oftentimes index the users so that's one of the things I'll do is I'll find all the usern names and then I go to the clear fors and I see I do a cross compare and I sort them by reputation
and posts and things like that so I can go and see okay who has a good reputation on this forum but they don't have an account over here and then I just go to that site and I say I'm that person I reference their blogs and like they don't check anything they just like let you in um so that's one trick you you can use um and it works like surprisingly well for like all these hackers that uh are very Anonymous and whatnot um but yeah yeah a lot of it's just very clear and in the open and and like raid forms you know just perfectly out there in the open um you know that
was one of the sites uh cuz this was one I was scraping of course uh but the fun thing is they just had an RSS feed so like you have to log in or anything you just have it send you the updates from the site so a lot of these sites will do that as well um and especially the ones that are operating more by like the teenagers and stuff that we see who are who are getting rolled on eventually do you have any uh recommendations for uh best practices related to your data like how to collect in the tool sets that you utilize yeah that's that's a good question actually and I think I have a slide in here I
wasn't sure on time so I uh pulled this one out but um this is kind of the high level setup I've been running with in terms of like scraping data from these kind of things the main thing is like just not touching anything directly um you know everything you want to do you want to go through a VPN of some kind uh to at least have some layer of abstraction most of these I do hit through tour as well um but in general you can see kind of the breakdown here uh I use time based event bridge to trigger when I run these uh scripts and and Trigger the scraping uh but essentially they all
operate in kind of the same way you know we'll go out and hit hacking forums marketplaces we hit all the ransomware leak sites as well uh we also hit various chat uh groups so like telegram Discord uh we go into various irc's uh there's a funny one one IRC we broke into um they uh once we started chatting with some of the guys in there they found out uh not who we were but they found out we were not uh in their in their little group and uh they figured we were security researchers and they actually gave us their resume uh just like it was weird and like he showed his GitHub and stuff and was like
dude like it weird and uh it funny from there we were able to get to their Instagram and found a bunch of crazy stuff like they had like pictures of them doing drugs and stuff on there and just like man like how what do these people do like where you don't get in trouble for this kind of stuff like I guess there's a very high bar you have to hit to uh to show up on the fed's radar but um but yeah in general so we do a lot of scraping of those uh I use a combination of selenium uh I use um various Lambda functions um we also have RSS feeds really depends on what we're
targeting and scraping how how we're going to pull from I always try and go for the easiest first so like most of them just have an RSS feed that's my favorite um but you know in general uh all of it's coming through uh at least a a VPN um you know to make sure we're not giving away who we are and things like that and then we store everything in S3 process it we also cross compare with our uh other thread Intel providers um the reason I do this is we find a lot of data before the thread Intel providers will will let us know about it because they do that curation component um so a
lot of that too will sit on it and wait and see if theyve validated it because they have a lot more insight than we do into this stuff but for us it's like if we want to quickly find out about major breaches or new Cloud accounts for sale that's kind of why we do it this way um but the thread Intel providers they're very good at enriching this data and giving more context around it and uh verifying that it's something legitimate um but then we pipe it out to we have our own threat feeds that we push it to uh We Gather metrics which we kind of talked about briefly um you know within the reports and things uh but then we
also have the alerts that we showed uh you know piping into slack when interesting stuff shows up and so that's kind of the high level of of how we do some of this collection um yeah the main thing is just don't touch anything in the clear and set up wholly separate like email accounts and jabber addresses and things like that to uh do any sort of communication um and also with telegram uh you can tie telegram to burner phone numbers um so that's what we do there too um so you don't want anything tied back to anything like actually associated with your identity question opinion on on stuff when it comes to the pacity of all this
open source stuff and so easy to do these things um there's dedicated real nation state hackers there's there's all this stuff which one currently do you think actually has a bigger sway on the security industry is it the vast provis you know the vast quantity of this happening or is it more of like the individual targeted highly specialized attack which one do you think kind of weighs out more heavily currently and uh for a business and then also just for the world in general that's that's a great question you know the um so weighing uh you know who is more impactful I think in terms of like say a nation state adversary or crime War groups uh I I would say
there's kind of two sides to it right uh if you're talking to marketing then of course nation state they're all oh Russia China you know that kind of stuff but the reality of it I I would say truly most impactful would be crime Weare groups uh because it's profit driven opportunistically um motivated um you know and they're just going after any Avenue to make money which really makes them kind of a scary adversary because they don't care who they target they don't care who they hurt um and it's something we're more likely to be hit by than saying nation state um nation states are definitely to go after you if you have more of that sense of
data um you know like back to uh this slide you know like a lot of these folks tend to look at it that way right like oh you know we don't have data Russia would be interested in right um but even so I think nation states might Target them for infrastructure um because you know all the all the people saying oh just block Russia your firewalls and stuff cool when's the last time they've directly touched anything in America never like they always proxy their traffic and so you know that's that's why I think like um you it really comes back to uh protecting yourself against the basic crime Weare is where I think people should really focus uh initially
um because right now we're doing a terrible job at that too so your data capture through that process do you would you say involves the E selenium oh so so how much of the data capture do we capture through selenium uh you know I'd say probably uh 75% of it or so um because I because they actually do purchase things like Cloud flare and stuff like that which are very good at blocking Bots and so we have to find uh ways to act as much like an actual person when visiting those sites as possible because if you just hit them with a with your basic Bots and stuff like that and you know you have Python
and your user agent string you're going to get blocked immediately uh but if you're using a real browser and you do things like have add-ons you make sure javascript's enabled there's all sorts of steps uh I've gone through to kind of make sure um you know those things are in place uh just because I've run into blocking on on various forums Che cyp Cyprus oh steroids oh thank you I'll definitely have to do that so anything to make it easier uh well with that I think we're out of time so thank you all very [Applause] much thanks for all the questions guys that was great uh we got about five minutes is until the next talk so if you
want to head to the restroom grab another drink uh refill water you know all that great stuff and then we'll be back in here so thank you