Not Your Grandpa's Password Policy
Show original YouTube description
Show transcript [en]
so who here likes to change their password on an arbitrarily regular basis anyway you you so might not be the talk for you because what I'm gonna do is talk about how to get away from that but first a little bit about me I have worked in IT and security for a number of years in a number of different roles about the last eight years has been primarily security leading the security team at pure storage out in Mountain View California I also took a brief stint in the middle of that to go to law school practice law and whatnot which is in two relevant but it was interesting and I volunteered besides SF though so just a little bit
of an overview I'm not gonna bore you with deep technical details what I'm gonna do is I'm gonna cover password cracking concepts and how we my team use them to implement this approach that I'm going to talk about I'm gonna provide an overview and a framework for how you can get started doing this exact same thing and then go over the like how we actually implemented it the results we saw with a few specifics to get past the speed bumps all of those slides and notes and scripts and some more hints are available on the github page that's up it's linked up there so so why right so the main thing is that it's fun so
many of us I don't know how many blue teamers are in the room but that's what my team does we deal with incidents and events and fighting fires day in and day out and when we're not doing that we're often making people do things that they don't necessarily want to do like change their password like have their screen lock out when when the screensaver pops on things of that nature so this is a way to get a get rid of that one thing by kind of being a hero and making people not do something that they don't want to do and so you also kind of get ahead of the red teamers that you're gonna face so if you ever have any pin
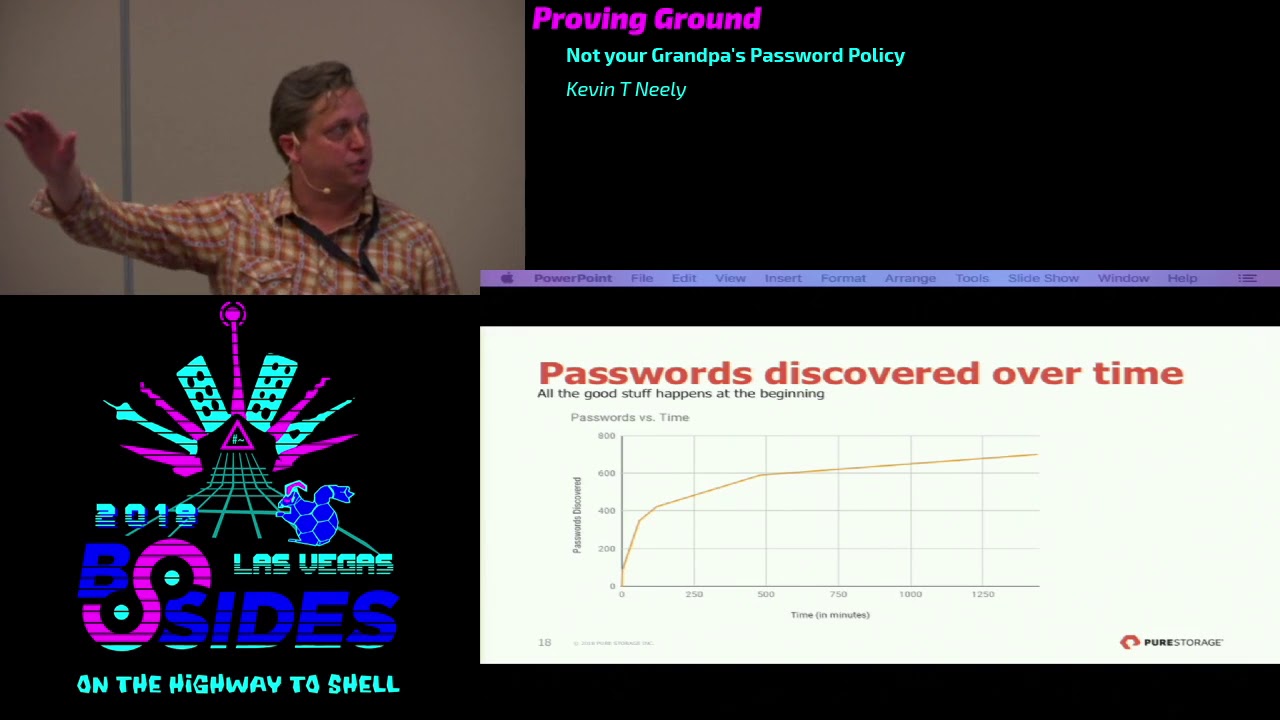
testing gigs that come in and test your defenses there's a way to get a little bit ahead of that and it's proven really effective so one of the difficult things of a soup to nuts security program is that measuring security awareness is very difficult and what this does is not only improve the strength of people's passwords decrease the risk of the come to the company but also over time people learn what a strong password is and what is it and you can measure this so what you see here is we've been doing this for about two years and you see that steadily quarter after quarter the number the percentage I'm sorry of people that we
employees whose passwords we've cracked has gone down now you'll notice in the first couple of columns the the raw numbers going up we Pierce Sarge as a start-up or was a startup and so we were growing extremely rapidly so we were in you know getting more people but that was mostly because they all new hires and so we do find that a fair percentage of the raw passwords that are cracked are new hires so people end up learning this and we're doing it because this type of password policy doesn't really work well right so this is I took this off of the internet I mean this is everybody seen this most of us probably agree that it doesn't really work that
well so they give you these requirements they have character type requirements but at the end of the day that password policy says the first one is not okay but the second one is and and the reality is that both of those are just as easy to discover or guess as the other one so there's no reason for that policy it's not it's not effective and I think I saw a couple nods in the audience but I think I'm not the only one that thinks this so there's a number of people on InfoSec twitter that they kind of agrees with it so I said you know but no we're not going to force people to change their passwords so how
did we do this so has anyone cracked passwords before used tools like that a few people excellent excellent so my goal is to like basically have you able to do this tonight but there's a couple things that you have to prepare so you've got to have some sort of CPU or GPU usage that you can use so you've got to have a mount of raw horse power but I'm going to show you that it's not that significant you need to collect some word lists or dictionaries or something like that and this can be things like the stuff from Troy hunt they he releases or the latest note from Krebs and so those are previously cracked passwords that have been
released to the wild or just word lists and English dictionaries and then also understand your your audience or your user base because things like where they are in the world or the language they speak or their culture both the corporate culture or the the kind of local culture so if you if your target is mostly in the Bay Area like mine you know words like Stanford and and San Francisco and Golden Gate pop up but if they're out somewhere else then different local words are common and you've got to have some sort of tool so these are a couple of them that I've used in the past we landed on hash cat for no more reason and I kind of started
with using it wanted to use it was in all of the hash cat team doing attract me if you can at Def Con so we use that but John the Ripper is equally good there and there's also a lot of cross-training there so you learn one you can kind of understand the rules very quickly in the other and then one of used in the past it's quite a while ago was Cain and Abel it's a Window System and this one was a lot of fun back in the day when all of our workstations were on the same collision domain because it would sniff the traffic and actually pick the hashes up off that wire and just start cracking
away it's not really under development anymore but it was pretty fun so so what we do is we spend about seven days doing this testing process and the first thing we do is extract the NTDs get out of Active Directory using a live domain controller but creating shadow volume copy and extracting that out again that procedure step-by-step is documented on the github so like get you going you just need admin credentials in your set or you know red teaming mini cats and that that works too and then we spend a couple days brute-forcing up to eight characters and then a couple more days using word lists and rules followed by some mass processing which is like
targeted brute-forcing followed up kind of around a seven when we're starting to get diminishing returns and we feel like I think we've got enough this quarter we start sending out the notifications tell people that they've got to change their passwords and you've got two weeks to do it so I'm going go over each one of those a little bit so the brute force you want is again super straightforward and the reason we do it is even though we've got a setting of say nine characters in our our Active Directory settings the realities admins can override that right and you may have legacy sis service accounts that are still being used or something along those lines but the big
occurrence is someone walks up the help desk says hey and he changed my password help desk admin right clicks on their name and they and they can type in anything and they override the policy we also use this since it takes about two days for us to get through eight characters at the key space we also use this time to prepare the next steps we might find we might have in the last quarter discovered a new tool there might have been a talk at a different besides about a I've got this novel approach or someone had a new idea they want to prepare that for their word lists and the rules so the word list I
kind of went over this already or just basically dictionaries and then you can use tools like word Smith that will generate that kind of pop culture that local culture information which is a really cool tool to just quickly generate a tailored word list for your area and then so but that's not going to do it by itself right imagine an English dictionary probably you don't have hopefully you don't have any character passwords that are just all lowercase characters right so then you've got to apply these rules and this is what the tool does for you the tool will take those rules and do things like substitute an O for a zero or double up the word or something like that there's
a lot of different rules to toggle or to truncate or to append to duplicate and so you have a lot it's really a tool kit that you can use when you're using hash cat to crack the passwords and then we use the mask so it's like I said are basically kind of in two ways one it's it's a tailored brute force so in my example up here what we found is that people like to create passwords with really common patterns right so they will say uppercase a bunch of lowercase and append a couple numbers so that they meet that policy right so you do that and then you by narrowing that key space to this pattern you will notice an
echoing you'll notice I'm not going so you'll notice that you you can go through a lot of that key space very quickly and without hitting a lot of the password combinations that are very unlikely for people to use another thing you can do is a and or prepend a shorter mask to your common word so you'll see that we get things like with our company name in there with a bang one two three so these types of methods work pretty well when you're approaching it that way so I've got some examples up here for each one of those but it's a little bit of an eye chart there's more detailed explanation in the notes so this is more of a slide
for you to review but I thought it might be fun to kind of show you what that looks like so I've got an example here and then at the top you see the command line and I'm using an attack mode of three which just means brute force I've got user names in the in the hash file so I've got to tell tell hash cat that so not actually thinking that that's part of the hash and 1000 means it's Active Directory I put in your results in a specific file it's helpful because then you it's easier to analyze later but then you can see I'm just doing question mark a if you are not I am sorry now you can see it at the top
so the the nine question mark are just telling a brute force any character a nine length right and so you'll see that in that long amount of time that we did that then I discovered two whole passwords right so but by narrowing it to the pattern that I mentioned earlier with the with an uppercase a bunch of lowers and then a few numbers you can see that already I'm getting better results right I'm getting much more results it's got me two in the couple minutes while we were fumbling with that and then boom I've got a few so that's that's pretty good right that's that's better obviously but what if we do something a little bit
different so this is that hybrid attack so in this case I'm taking a word list of the I linked in the notes of three hundred four thousand probable passwords so very likely passwords that have either been released in breaches or have been generated because it's a pattern that people use and then I'm just tacking on four characters afterwards and you'll see that I actually get a lot more passwords very quickly and this is on a MacBook Air I kind of ran out of time but on the on the nine character brute-force who's going to take this two hundred nine years to go through that so you can see that this is working a little bit better
so back to [Music] okay so so that's how we do it and then and then I'd like to show you what we've seen out of this so one thing that we've seen is that you will find and this is very evident from the test that I just ran is that depending on the way you structure your tests you will you can you can get diminishing returns very quickly so it's very likely that if you put them in the right order you will discover the more than 50% of the passwords you're going to discover in about the first four hours or so of testing and then the rest of the week it kind of tapers off now that doesn't
apply to us because we're starting with that brute force method which is really a way to give us time to to prepare the remaining tests but that is how it ends up working is you'll get a lot of it very quickly and then start slowing off and then this is off of one test not not all of the two years worth of data but in one test you'll see that we still get a couple of those eight character and seven character passwords even though they violate the settings in Active Directory so that's why we test those and then yes the bulk is at nine because that's what's required but we even get some in the 12 and the 16 and 24
character range just based on those rules we're certainly not brute-forcing than 24 characters and we've also found that people tend to create the same password so some of these are going to be the same person creating multiple service accounts but in some cases it's it's that things like walking the keyboard going straight down the first two columns is very easy for people to do and this is this is data over the course of the two years aggregated and then figure it out and what you will also notice is that people really like to use corporate culture at least for us who we kind of bleed orange at our company with four of the top passwords
have the word pure in it which is pretty funny so then we started looking at our data a little bit further and this is something we've only started doing in the past year or so is we noticed that certain people were not only repeat offenders continually creating weak passwords but they were creating the same password or basically the same it won't let you create the same obviously so Rhoda scripts to to calculate the similarity between this discovery and last discovery so for people that fail two times in a row and we started out with a 180 - the first time we test I said that's a lot of people and then we sent them a notes
we sent them a separate email we told them hey your password this time is X percentage similar to your last one of X and we put their last password in the email and that gets a visceral reaction let me tell you people are like Oh aren't you the security guy like how can you be putting the password in the email that's totally insecure don't you know anything and I say yes well you're using the same password over and over again you are you have to change this whoa this is not your current password into your previous one and thirdly you've got less than two weeks to change it so I feel like the risk is minimized
especially if you do what you should do and create something very fairly different and to kind of demonstrate how would that look like give in to two tests in one quarter we discovered 805 passwords following quarters about 490 of those 334 people where the a failed both times and then in that group 138 the people were of that 70% or so threshold and let's be honest like 60 or 50 percent is still pretty similar but we're given people a break here while we're training them to do this and so the last thing that I kind of want to talk about is that passwords aren't the only thing right like I have all this stuff about
passwords we spend all this time but it's not it's certainly not the only thing protecting our network right we've got multi-factor authentication I hope you do too we've got a you know of great blue team who's looking at the data and identifying anomalies like logins from different locations and other things that indicate that an account might be compromised or things of that nature so we take all of those and then we face the toughest challenge because everything up to now is easy now we've got to convince our auditors that this approach works and that can be a little bit daunting and the biggest thing that I found is that they say we want to know
the policy and when they say that they mean group policy out of Active Directory and I say no no no no that's not the policy our policy is super simple it's published it's signed by corporate leadership and it says it's a little bit longer than us but more or less says your password must be strong it must not be weak and if it's weak you got to change it within two weeks so that's what we say and then it's got a little bit about the testing process and kind of stuff which I just went through and so we tell them that that's the policy they say what we're gonna screenshot the policy I'm like cool I gave you the PDF of the policy
you want screenshot of it too because I don't get it like this takes time and time again but eventually you kind of convince them we've convinced our auditors we've convinced our customers that this works and we've gotten past all of that so with that and a little bit of a hiccup that is the presentation I had for you special thanks to Russell in the audience who was my mentor for this and without him without him this would have been a jumble of misguided slides that were in no particular order so I hope that worked for you and I don't know if I've time but I'm certainly open for questions yeah I've got time saw you
first [Music] how'd you get management to sign off on this so two pieces so one big piece was what I talked about and so it's to me was actually easier to get management to sign off then internal and primarily external audit so that's that is your biggest roadblock it is very difficult to fight the kind of incumbent policy that's there inertia is a real thing and it's a let me tell you but I had a big leg up in that I came to this company to start the security program and they didn't have much in the way of incumbent policies or inertia that I had to fight I also had a extremely great boss who was was very bought into this
so I report to the CIO and he has been telling his peers about this approach and they're like they're they're like whoa how can we do this like they also asked the exact same question they're like how did you do that so I think it's it's with a lot of documentation so in fact a lot of the documentation I posted on github at least the technical details are things that we needed to produce to our to our auditors mostly the internal audit and once they buy in the management trust them usually and so that helps a lot and we also take all of our kind of evidence we treat it like a like an audit ourselves I call it the
password audit process and we we commit everything that we do all the the extracted passwords the rules that we use the word lists sometimes all the masks and we commit them to an internal git repository that only the security team has access to but we can provide that to the auditors if they if they really want to get into it nobody's so far nobody's taking me up on that they don't want to dig into that cuz I start telling a hash cat and they're like what but but that's that's how I did it how do people actually deal with being told that Possible's possible it's a crap I didn't actually you know react against it all they learn from it they react in
a number of ways I mean of course the feedback you get is gonna be mostly negative anyway most people don't just like hey this was great but so there's a number of ways so one big one especially when we started this program was know you didn't write you didn't crack my password I don't believe you right that is the biggest one and that's the that's the fun one let me tell you because because what they will often know I'm sorry we're a very open communication culture and we communicate in slack a lot and so they will ask that in a public forum so that's the fun once I don't paste our password but I give
them hints about why we like that I know it right so the example with the one Q a Z or Z XE vbn I just say well what happens is it's easy for us to find passwords where people walk the keyboard or give them a hint and then one in that case the guy was like oh how I get it changing my password so so so that works like I mean you gotta have a little bit of levity about it so that's kind of my approach the other thing is they think that they say their second reaction is you know how do they phrase this they say do you have all the passwords in plain text right they think that like
we've implemented a system because we built Active Directory or something we've implemented a system where we're just writing their password to a text file or something comparing that way so we just tell them no we've got real systems and they do this and here's the process so those are the primary reactions that that we've gotten other than and then the second one is the one I went through the visceral reaction when I send you your password in an email that that it's an interesting one but it's been showing pretty good results you mentioned the repeat offenders yes I have them all so how do you deal with those do you involve management that manager so can you give
examples on on the most the ones that are lost causes so we we might be implementing another thing but so there's two types of repeat offenders the ones that just keep making weak passwords but they're different right and I didn't address that one and primarily at the moment we're giving them or we're assigning them the web-based password training that nobody else has to take so we're trying we're trying to do a security awareness program where it's minimal and you only get kind of fed or provided the training that you need or seem to need right so so that it's not just like everybody saying the same thing so that's that's one of the approaches we probably have to think
about effort now that we've got about two years worth we need to start taking a longer view and seeing if there's anybody that's done it every time we had one that was that he was he was fairly high up in the organization and I don't know if we have the time to do this we are still kind of small company so maybe but one of our helpdesk professionals sat down with him I mean this guy's he's way up there sat down with them showed him how to create a good password to tricks the tips and tricks that we've also published because he doesn't have time to read it and he hasn't been caught again so so that has
worked as well but that obviously has a lot of time associated with it all right big hand for Kevin thank you [Applause]