Greg Foss - The Future of Destructive Malware
Show transcript [en]
hey y'all uh please join me in welcoming greg foss uh greg is a senior threat researcher at being aware of carbon black his talk the future of destructive malware will discuss the history trends and advancements of physically destructive malware thanks so yours great all right thanks so much for for having me everyone i'm excited to join you all here in this kind of dystopian reality that we find ourselves in presenting from our homes um but you know i'm really uh really glad to be here you know especially with the boulder community uh since this is my my home my backyard so uh super excited for this and just you know honored to be able to
to present today um so let me share my screen here and we will jump right in all right i think my my stuff's up so um so i i want to start things off by uh i really like uh you know what erica mentioned today talking about uh fear um and and the other f word that she didn't linger on a whole lot is failure is something that that i want to address before i jump into this talk because uh it's something that when i first submitted to besides boulder i had a completely different talk you know what i'm going to talk to you about today is a whole different ball game than what i was planning to talk about when i
initially submitted this talk we were initially looking at um you know what what we were seeing in terms of like apt attackers and more like advanced adversaries and government kind of nation state-sponsored side of things that was our real focus area at the time but uh you know into the post-covet era has really changed perspective for us a lot and it's caused me to look at a whole different uh side of things um in a different way because it's been evolving and what i want to talk to you about now is actually ransomware and ransomware i think is kind of one of the most critically destructive attacks uh that we're seeing now today uh across
our data set just from what we've been able to prevent on the end point uh in the beginning of uh 2020 to the current date we've seen a 900 increase in overall ransomware attacks um so it it's a massive problem and you know the reason i want to touch on this is more than likely everyone here that's attending this this conference is going to be affected by ransomware much more so than any type of advanced persistent threat sort of adversary um it's just very common and they're getting very good and they're changing their tactics with how they're targeting businesses and that's kind of what i want to dive into today it's kind of how they've evolved their
tactics now one interesting thing looking at just the distribution across industry vertical of ransomware itself just from our data sets and this is from 2019 we haven't run this in 2020 yet but essentially what we saw towards the end of 2019 was a big significant targeting towards energy and utilities and surely thereafter was a government and you know now coming into the election that i feel like this is going to be a significant target for a general e-crime and ransomware in general and state adversaries looking at you know swaying opinions swaying polls possibly uh who knows right i mean we're we're in literally twilight zone in a lot of ways uh as as a community and as a country and as a
world right now so it's real interesting times but uh the key here is these uh e-crime groups are taking significant advantage of a lot of these situations right now um you know the the old saying is never let a good crisis go to waste and that is no different when we look at these e-crime groups and uh what's interesting now is a lot of them have shifted to uh to actually moving operations online a lot of groups that were traditionally doing more in person sort of scams and things like that now have opened up a new avenue into doing online sort of attacks and e-crime related activity and i'll get into kind of why that's
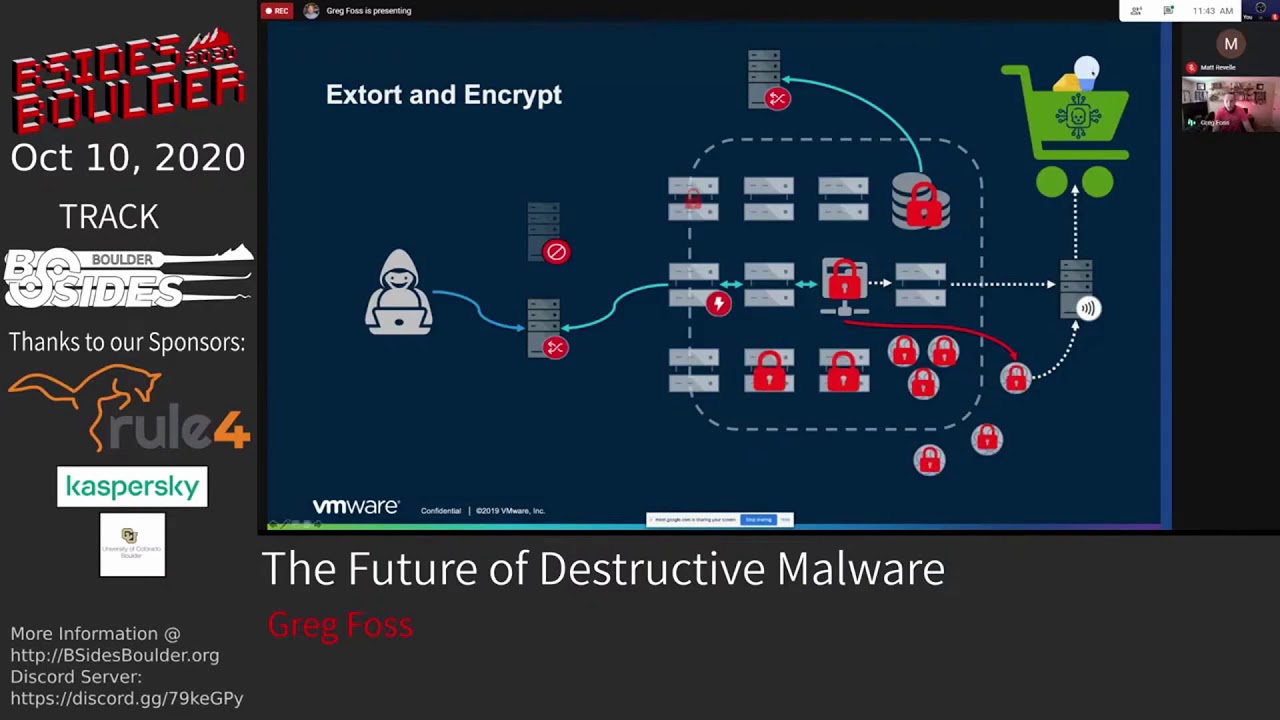
possible and and how that's being done so to to highlight this i want to take a step back and we're going to look at this actually from the attacker's point of view now this is a pretty interesting diagram that evan anderson ian lee from randori and myself put together for for a different talk but essentially it summarizes kind of what we're seeing in terms of ransomware and e-crime actors and evolving and how they're attacking organizations so what we're looking at here is our black box typically like a company that say this group wants to target and we have our happy little attacker over here the first thing they're going to do is some open source intelligence
gathering on the organization they're going to go find out your geo location your employee footprint you know your public ip address space social media all this other kind of good stuff that's out there about your company so you can figure out you know possibly high level how they're going to attack you then it's going to lead into a reconnaissance phase now a lot of traditional ransomware what we saw was much more just fire and forget sort of phishing emails and you know hoping about 10 of those stick and then unleash the ransomware what we're seeing now is a shift towards a lot more manual hands-on keyboard approach towards the initial access into these organizations so you know they're going to do some
scanning against your edge devices here so we'll pretend this is like an organization's dmz if you will and so now they kind of have an understanding of what your public footprint is and from that they can take an educated guess at what the rest of your organization may look like on the inside and now uh due to covet i put some outside you know home workers here because that's kind of a new avenue for them even though i would argue that it's existed for the past decade but now is only just really getting uh the visibility it deserves but so the next thing they're going to do is ongoing monitoring of specific assets and understanding you
know what is something that might actually have vulnerabilities in it can we watch this and wait for a new vulnerability to be released or be discovered and then exploit it at that time now most commonly what we're seeing is these guys going after vpn concentrators or publicly exposed windows and linux servers specifically looking at just people throwing windows servers out with remote desktop protocol open without multi-factor enabled i mean that is i would say like 90 of the incidents that we get roped into start with some sort of situation that way it's either going to be that or more likely a phishing email but it really depends on the group and what's going to be the path of least
resistance into this organization so of course you know they could go after this home user they could target a home router they could do it through phishing there's a lot of different ways they could target someone personally and then use their corporate access to ride back into the organization but what we're going to look at from this standpoint is kind of what i just talked about in terms of the most common way they're getting in and that's going to be taken over windows server that's in the dmz now first and foremost they're almost always going to have this callback to a second server from the one that they did the scanning from so they're not going to have this
go back to the server that you probably already have in your logs and already are at least tracking it to some extent because they've been scanning you so they don't want to continue using that box they're going to have this callback to a second server where they're going to conduct their primary operations from now once they gain access they're going to do this initial reconnaissance start understanding the internal mappings of the organization usually this is going to be done passively trying to not directly scan and stuff like that they're going to look to gather credentials and figure out how they can move from the dmz to the internal network uh assuming this isn't just a flat network like
a majority of companies on the planet um so you know there's a lot of different ways they could target a user and get a credential oftentimes these are just going to be in memory on this box already so as long as they can elevate their privileges they can dump those credentials from lsas or various other techniques to to pull those credentials needless to say once they have those they're going to begin probing from the dmz to the internal workings of the network now this is a key point here because this is going to be a way you can actually detect some of this activity like you know why would you see any authentication activity originating
from these internet-facing servers to your internal network one and also are there failed authentication temps and are there multiple failed authentication attempts this is going to be a good indicator to go off of to see if someone is trying to warm their way into your organization now eventually they are going to be able to find servers where these credentials work and they are going to be able to pivot and begin to move laterally and start to identify high value assets so over here i just made a mock little a backup server now nowadays there's a lot of better backup solutions that actually avert some of these problems but if you're still just you know uh you
know saving your your system images off and saving files off to just a random server that's going to be a prime location for them to target and not just target for access but they're often uh what we're seeing is setting up redundant access from these backup servers and now this redundant access is going to be something that isn't calling back at the same frequency of their primary server here it's going to be that foot in the door where they're basically leaving this access so that in case you find out about this they're going to be able to get back in through another way that you may not know about this is probably going to call back out
you know maybe once a week once a month or or something like that so it's going to be very low and slow something you're going to be much less likely to notice and catch on to and the reason for that is they need to maintain their access for as long as possible so they can identify high value assets and figure out the most optimal way to encrypt the environment now over here we have our file file share which i'm just making it easy for this example we'll assume this is where this company has all their all their important stuff right so often times this process here uh the internal mapping and identifying key assets some groups some ransomware groups will
actually take months of doing this mapping and understanding of the environment before they actually start figuring out how to exfiltrate this data now some of them will start doing this immediately they'll they'll use all sorts of different tricks to get this out of the environment one of the ones we've seen recently is leveraging own cloud using their own uh their own installation of own cloud installing this on a user's system and then just syncing files to it and then offloading this to another server which is usually going to be a compromised website like a wordpress site or iis or something like that and then they're going to offload these files through this user that's just one way
some of these groups are very verbose with it a lot of them will just use ftp so you can see a lot of this data traversing outside of your network which is another area where you want to have that visibility to understand you know is anyone syncing a ton of data out of our company is this crossing our boundary it's somewhere we were where we can actually inspect that traffic you know you want to make sure you have this layered visibility across your whole infrastructure and especially the ability to understand what's happening on these remote users systems now the second most common way we're seeing the sex filtration happen is uh over dns dns is something where
i'm still surprised so many organizations don't have dns logging essentially you know as a core tenant of their security program as a whole because it's so important um especially when you're looking at this type of activity here you know one way you can find this is often you'll see one system within your environment making thousands of requests to a single parent domain with multiple varying sub domains so that's one way you can detect this but either way you want to have that network visibility so you can catch this you know before they're actually able to get this out of your environment or the minimum halt them uh you know in this process because if they get your files and your
most sense of data out of the organization now it's fair game for them they're going to profit off of your environment no matter what you do oftentimes this data will be put in their marketplaces it will be hosted on their own servers which we'll be showing you in a little bit here but all these organizations now it's moved to double double ransom or double extortion where essentially you know they don't care even if you aren't going to pay for them actually encrypting the environment they're going to profit off of selling your data sharing your data using this data all sorts of different means to leverage this information that's been stolen from your environment two make money regardless of if you pay
them for decrypting your environment or even if you're able to restore from backups you know one trick with the backups we've seen is some of these groups will infect the system images directly so that you know when you're restoring data or when you're restoring from backups you're restoring their malware again so you know they'll still be in your environment even after you go through this restoration process but you know let's just play the victim here right so so we have our victim they've realized what's happened now that their whole environment is utterly destroyed and encrypted now they have to figure out how they can communicate with this threat actor which you know now thanks to new advancements
if you will i guess in our u.s department of justice this could actually be illegal for them to pay so you know there's a whole other layer of complexity added on to just this simple process right here um but you know we'll pretend it's it's olden days and and they can pay and actually get a key that works and they're able to use this to decrypt their environment so now you know they start recovering their data they're to a point where they're kind of you know feel better about things they've gone through this horrible situation and now they're you know they're not happy but they're somewhat relieved but the problem is a lot of these uh
things that are overlooked is going to be this residual access and this is just that initial back door that may have not even been discovered during this initial attack now also the malware itself especially if they've been able to deploy it in the backups and it's synced across systems is going to be able to call back as well so this attacker can still maintain access to the sys to the network and then they can launch the second and third stages of their tax which could be you know selling access into this organization uh it could be reselling data so other people can get into it there's a lot of things that can happen from this right here
so that uh persistence is just such a very uh significant component of this and um to highlight this we actually went through all of the ransomware that we saw over 2019 and this is actually a a chart that um andrew costas one of our threat researchers put together when he was basically mapping ransomware behaviors to the miter attack framework and um what was really cool about this and also kind of scary was he was just looking at the ransomware payloads themselves let alone the actors behind him which now we're seeing much more hands-on keyboard you know actual uh you know manual penetration and uh and monitoring of these environments once they're inside um but what you can see over here these are
all the different ransomware variants and then these are the different miter tids as they relate to persistence so you can see there's tons of overlap here and uh the commonality is that a majority of these uh ransomware payloads will leverage persistence mechanisms uh directly within the within the payload itself uh oftentimes leveraging root kit functionality such as modifying the master boot record they'll create scheduled tasks modify the registry modify startup items and almost all of them use hidden files and directories to some extent both in execution and in their persistence mechanisms so it's a very key component of ransomware that they want to make sure they're sticky and they stay in the environment and oftentimes these redundant
kind of accesses are not even going to leverage the the original binaries that you may know about they could be using powershell they could be using various scripts so you really have to do full instant investigation if you're hit by ransomware and treat it as an advanced adversary not just some commodity kind of script kitty or something like that that we might have viewed it as in the past additionally in terms of on top of persistence a majority of ransomware does credential access and this is oftentimes for them to elevate their privileges or they will also use this in larger operations such as credential stuffing so they will take credentials from browsers almost all variants we looked at have
done this where if you're saving any of your treads within your browser you need to stop immediately and wipe all of that content because it is trivial to pull that content out of your browser um use a password manager of some kind because that adds at least an additional layer for them to get through to do this because tons of tons of malware not even just ransomware does this sort of activity so something very important to pay attention to and and be aware of they will also target other applications that are going to be you know more esoteric across you know more of your general kind of user population but they can use these for various other
means as they relate to their overall attack um you know going after telegram looking for ftp credentials you know other credentials to your websites your online accounts your bank accounts all sorts of stuff like that is going to be a target for these groups because at the end of the day all they care about is making money from these intrusions uh so so you really have to keep that in mind when you're looking into these is you know what is the profit angle for this actor in obtaining this information and uh you know that will help you frame kind of how how the attack might flow from that point forward um you also have to assume that they're
monitoring your keystrokes they're modding your clipboard doing all these kind of traditional attacks to gather credentials and just simply monitor and you know also see if you if you were on to them as well but the final one i want to touch on there's a lot more we could get into but um but collection is something that is built into a lot of these ransomware families they will try and pull a lot of local data from the system they'll do this automatically oftentimes using powershell and what this data will be used for is often going to be leveraging their marketplaces for how they can resell data and oftentimes reselling direct access to systems as well
um so you know as you can see these are just some examples of some of the data that they collect but in general you know every single ransomware variant we looked at is doing some form of at least collecting data and leveraging this data to perform further actions from their malware payloads now taking a high level look at all of this we mapped out everything from 2019 across uh the miter attack framework so this is a big project that andrew costas put together and um you know what's really neat about this is just to see you know all of these techniques kind of stacked in how ransomware actually acts and all these unique components that are
associated with ransomware that people don't necessarily think of um you know so many folks focus on just this impact side of ransomware you know the encryption uh inhibiting system recovery destroying data all of that kind of stuff but really there's a ton more going on here uh with with ransomware in general that makes it a much more concerning sort of a piece of malware than you know what what it kind of is viewed as on the surface so you really have to look into all of these different kind of components and and that's what's great about miter because it gives us sort of a ruler for us to kind of measure against and understand you know what are the tactics
that that we need to be most concerned with as defenders something at carbon black that's immensely valuable to us because we can take this information and we can use it to build better telemetry better rules and overall uh help secure our customers much better from the my rate of these types of techniques that are leveraged across ransomware and various other types of attacks but without getting too much into the detail of ransomware itself i want to take a look at the other side of this the actual underground economy and what happens behind the scenes with your data and with your information once it's stolen by these adversaries you know uh the thing that's been eye-opening to me
we've been spending a lot of time looking at these marketplaces and looking at these uh the kind of a whole underground economy at scale of what's happening here and what's what's amazing to me is it's very much an industrialization that we're seeing with e-crime now where they're making it very easy for people to get in on the ground floor and perform some of these attacks without having necessarily the skills that you know you used to have to pull off some of these very large and prominent attacks it also makes attribution insanely difficult which is uh one of the reasons that we at carbon black don't focus a whole lot on attribution we focus more on the munitions
themselves and understanding you know how do we build the best detections possible for these techniques uh not so much caring about whether it's a fancy bear or pinchy spider or any of that kind of stuff although that does play into it but when you look at the e-crime groups and how they're sharing information and resources and infrastructure uh it changes our view significantly on you know just the overall uh kind of attribution as a whole um so the big uh change we've seen with ransomware this year has been this double extortion kind of component um you know as is popularized by the maze cartel in terms of uh you know trying to profit off of
the stolen data in addition to the uh encrypting the organization's environment it's really made ransomware a more significant threat because for a while you know all these companies would say hey i have better backups now i can restore i've tested i've done all this all this good stuff but really it's uh it's shifted to a point where cool you paid them for the encryption now what are you going to do about the stolen data because not only are they going to extort you for this data but they're going to share all this information within their inner circles this information is your entire active directory environments all users all encrypted credentials all that good stuff any browser credentials they've stolen
from your employees any customer lists any any information related to your customers especially looking at how these groups have targeted healthcare organizations lately is significantly concerning um because this is uh kind of escalating this threat to a point of you know how do you respond to this even if you pay them for both of the both of the problems here you're still at significant risk for years to come from all of the data that's been collected and what they're doing with with that data on the back end so maze maze cartel they're the only one there i'm actually gonna show uh their their url and i think they've actually moved this to uh just a tour now um but they were very
brazen like every single uh quote-unquote client you see over here was a different victim of them and you can go through their site basically every single day they're posting new uh information about new companies that have been breached by them and are now being actively extorted so basically like you know you'll have the company name article about the company they'll link to the news articles and they actually reference them as their clients um over here you can actually access the full dumps of their data so you can get gain access to a lot of very sensitive information very easily here now often they don't show all of this they will post it and then and then you have to pay for a key to
decrypt it or you have to know somebody to get the decryption keys some of them they'll just post it and share it openly because they want to embarrass the company but either way there's tons of information out here that significantly exacerbates the risk of what these actors are doing and how they're actually targeting organizations and kind of just highlights the punitive nature that these groups are taking now maze is a significant group and the reason i brought them up first is you know a they're the group that kind of coined this sort of trend they were the first group publicly or at least they're attributed with being the group that has leveraged double extortion and started
teaching other groups to do the same and now they're actually partnering up with other ransomware groups so ragnar locker was another significant group and now they have partnered up with maze and i believe uh last week we saw the first attack from their combined efforts where they actually used ragnar locker's virtual machine method of deploying a whole virtual machine to the host and then it deployed maze ransomware from within the virtual machine so as one of the you know defense evasion kind of mechanisms that they use and so now these groups are starting to partner up and share information share infrastructure share intelligence and techniques they're becoming extremely uh powerful and and all the more powerful in that
they actually are looking to partner with additional organizations now um and may as they you know the reason i call them a cartel is because they call themselves a cartel uh to believe they have well over a hundred members within the maze cartel so it is a significant group and you know very very dangerous group of people honestly but they're not the only ones nephron is another very popular ransomware group they run a website called corporate leaks you know same sort of thing as what we saw in maze they're they're dumping the data they're asking for you'd either pay to decrypt the content or eventually they release it for free either way it's a significant black eye
to these organizations that end up on on these sites are evil or soda no kibi is another very prominent ransomware double extortion group and one of the things i found interesting they run a website called the happy blog and uh over here i wanted to just highlight this one company because it gives you some insight into what they actually do when they're in these organizations um and this one's a good example because it's public and so it's easy easy to talk about but as you can see here they're saying for over a month the structure of the corporation's work user services and cloud data storages were examined and uh one terabyte of confidential data was copied as a result
and then they list some of the data that they've exfiltrated so as you can see this isn't just like a fire and forget they didn't send some phishing email and just you know wait and let it automatically go run and do its thing uh this was literally them in the organization mapping them out as an advanced adversary for a long period of time before unleashing their ransomware payload paisa or otherwise known as mespinosa um these guys they they actually have uh i gotta give them credit they have a pretty fancy site it looks like an old commodore 64 kind of uh terminal um and pisa stands for uh protect your system amigo and um these guys they do have a
pretty good sense of humor although they are they are definitely criminals they um they take the approach that their partners are making this data available to you and they actually give little advertisements for their partners and uh and the like so it's kind of an interesting uh site to go through but same sort of thing you know this is where they're posting all the stolen data and looking at the double extortion of their victims klopp is a kind of i guess lesser known one i would say the same sort of thing you know they run a blog they have news releases they have the leaks published they have all sorts of information here one thing i did highlight on this slide
is down at the bottom here there are one of the groups that has kind of banded together in this sort of consortium of ransomware actors that said they will not attack hospitals they won't attack orphanages nursing homes charitable foundations and the like so you know that that is good there is some honor among among thieves um but not all groups follow uh follow this right as we've seen uh recently with uh ryuk just recently attacking uhs um they were one of the groups that outwardly and publicly went against that said you know we don't give a we're attacking everybody with impunity and that means they're going to pay because they're much more significant targets and so you
know as we've seen they just orchestrated arguably the one of the largest ransomware attacks we've ever seen against the health care industry in the midst of a pandemic so they don't care at all but fortunately a lot of these groups actually are not following that that lead which is which is somewhat good i guess doppelpammer very similar very popular ransomware group they run another data leak site and as you can see here they're tracking the views um there's a lot of people that actually come across this content that is stolen from these organizations uh which is significant kind of highlights you know the brand reputation damage uh and related uh you know kind of blast
uh or damage from the blast radius from these attacks that you can have just by how many people will have access to this information once they decide to post it uh segment is another uh very similar group similar kind of uh kind of way and they actually run their site on the clear net as well so this is one where you can just go to their website and view the contents which is why i think they have arguably much higher number of views for a lot of their content you know as you can see this one there's 28 000 views of this stolen data from an insurance company um now a lot of this is going to be bots
and stuff like that scraping the data and and whatnot but still i mean this is a lot of information it's very sensitive these companies that is now out there and uh in the open now conti is a super interesting one this one um was actually initially discovered by brian baskin which is one of our threat threat researchers at carbon black and um what's interesting kind of come out of discussions around conti is they are saying this might actually be the next iteration of ryuk so we'll see you know what comes out in in terms of the uhs breach if any of their data actually ends up on here then we'll know it was actually conti but that is kind
of the big difference right uh ryuk does not participate in double extortion or at least not as far as we know but kante definitely does and they run a website called continues uh they have their press releases all all that good stuff and um you know this one is a little uh less lesser known i'd say but they definitely still post all the stolen data about about the organizations they've reached suncrypt is another one that is a rather new um you know newer to uh the double extortion game the same sort of thing you know uh encrypting organizations and uh posting their data uh online now there's various other groups that don't have their own websites but they
use various e-crime forums and hacker forums such as xss and exploits and the raid forums and essentially these are more going to be individual actors and this is getting more into the environment of like you know the individuals that are paying for access to ransomware as a service and leveraging credential stuffing tools or uh purchasing access from initial access brokers which which we'll get into in a couple slides but essentially you know kind of their their next stage of where this information goes is going to be leveraging credential stuffing and uh trying to pivot using this existing data that they have um so credential stuffing they're going to take all of this sense of data all these
credentials and everything and they're going to throw it into some actual commercial grade tools that allow them to test these credentials across a large number of websites and different services which is kind of how they often will hop to their next target is it's usually going to be an opportunistic sort of thing so any of these companies that are breached and they're related to or tied to any of these other companies become significant targets for them um and one of the things we've seen a way for them to actually do this more manually and actually pretty pretty uh creatively is by conversation hijacking and so what that is is they will get into your email and
they will go dig up old historical conversations and then uh you know with a outside company so say you're a law firm and you're doing work with some you know ex company or something like that they'll rekindle these old conversations that you've had in the past and they will start getting them talking to the point where they will actually share something with them usually a macro enabled document or something like that so they can leverage your partnership and your relationship with this other organization to gain access to that organization's infrastructure and now we're actually seeing them use slack internally especially for organizations that have a much more granular segmentation between hosts they can leverage slack as a form of
pivoting so they can start these conversations and send payloads and trick people essentially in order to gain access to other hosts within the network so they're really taking a lot more time and effort to figure out how to move around within these companies and leverage the companies that they've already compromised to gain access to additional organizations infrastructures now some of the tools that are leveraged for credential stuffing are actually pretty impressive we're looking into a bunch of these that are available on crimeware forums and this is from our report the digital shadows put together earlier this year where they were talking about credential stuffing at large scale and they mapped out the conversations revolving around the
top most popular credential stuffing tools and so over here number one is a tool called open bullet which is very easy to use you pretty much plug in your list of credentials and they'll go shoot it out at whatever sites you you aim to have it try them on now this one the number two centrumba is super interesting because it's one of the ones that actually uses image recognition within the tool itself to solve captchas for you um so it's a pretty unique approach and it works on the simpler captions not so much that click the fire hydrants and buses and all that kind of stuff um but this one is a super interesting one
uh in terms of just having you know this kind of technology like built into tools that are just leveraged for credential stuffing and not even made publicly available these are all commercial grade tools that are available on hacking forms now we won't get into these other ones but they're all kind of pretty similar just to show you what some of these look like over here we're looking at open bullet and down here is sniper but same sort of thing you just check all the boxes here for every site that you want to try these credentials for they also handle multi-factor in certain ways there's there's ways in these crimeware forms where they actually talk about how
you can how you can get people's tokens and stuff from sms push requests and the like um so so it gets pretty interesting the further you uh dig into this but one thing i did want to highlight on open bullet here is just built into the tool you can configure proxies so you can push all this through tor you can you know do it in more of an anonymous kind of fashion a lot of these will also help you solve captchas over here tracks if the site you're trying on has captchas enabled and if so they have various means to allow you to automatically solve those and then for some of the more intricate logins they
actually have selenium integration so you can use the automated browser kind of approach to to test these credentials across these various sites now solving captchas in and of itself is super interesting for the trickier ones like recaptcha and you know the the ones that actually take a little more uh effort to solve you can actually outsource these uh so there's various services such as two cache x evil 9 kw and image typers and what these do is actually offload the captcha to people you know in other countries for pennies on the dollar they will go and solve these captchas for you and then send the code back to you so you can submit the request
and there's various ways to tie these into scripts tie these into the tools that i that i just highlighted to allow you to automate even when these organizations are using captions across these various forms now on the open source side the more legit side there's a really uh neat tool called crit over by davinci that's pretty awesome it goes and actually you can plug in a list and they'll go check it against public breaches and this one's pretty quick and fast and it's one of the only ones i would actually use on an asset that's not a vm the other ones i would not really trust because of where they come from and the groups that are put them out
but this one is definitely a good one for you to just understand your organization's threat posture and know you know if they got access to x credential what else might they be able to get into with those credentials um this is just a quick and easy way to test that but you know realistically you have to take a significant look at the whole breach in and of itself uh when you're looking at the organizations um you know behind some of these some of these significant attacks and what they're actually going to do with this data on the back end which gets us into access mining or essentially uh the uh direct resale of access into
organizations um so this is a technique that's actually been around for quite some time i was very prevalent with just leveraging compromised assets for proxies you know dating back to about 2008 um you know mostly what we saw with these with this type of attacks uh and initial access brokers in general was selling access to single assets such as you know compromised home personal windows computers and things of that nature but we're seeing now is a significant trend shifting to compromising of an organization itself and then mapping out that organization understanding the potential value and then placing that dollar value on just direct access into this organization and then posting this information for sale online
and oftentimes the way they sell this is usually just going to be through direct rdp account that they've stolen or they've cracked or they've otherwise figured out sometimes they will have back doors deployed sometimes they'll have remote access trojans really depends on the target and the actor who's initially gained access to this company but most of these are going to be organizations that don't have multi-factor enabled and it's just going to be here's the rdp creds uh you have domain admin go nuts and so they'll sell these from anywhere from you know around a thousand dollars for some small companies uh to upwards of you know some of these organizations we've seen go for over five hundred thousand dollars most
notably one uh incident i'll talk about in a couple slides here but the thing that's concerning with this is it really lowers that bar to entry so you don't have to have this experience in gaining initial access to companies in order to gain access to some very high value assets in some very significant organizations now on just taking a look at exploit.in this is on their community kind of just main main forum website here but under buying and selling you can see that direct access is one of the top items on on their marketplace so it's one of the hottest commodities right now something that's going for a significantly high dollar value and uh is being sold regularly and
consistently uh in these in these markets um and so this is something that is significantly picking up steam every time we check on this we're seeing additional new vendors joining this marketplace and adding new and more high value assets to highlight what some of these look like uh this is from a russian crimewar forum but this one is someone selling access to quote unquote government center usa now if you start chatting with these people you'll find out more about you know where this is uh you know where they're located what type of government center this is and other kind of interesting things like that but as you can see you know they're selling this for around thirty thousand
dollars at the current price of bitcoin and um the way they do this actually to create sort of trust within these trustless markets is through escrow now i don't know if any of you have kind of messed around on some of these marketplaces but escrow is a means of the marketplace has essentially a wallet that you can put this money into to prove that you have the money to pay for this good or service the seller can go verify that and it creates this mutual trust and they can essentially provide this access and once you're both agreed uh that this is what you paid for the marketplace releases the funds to the the seller through escrow and everyone's
happy and now this person can go in and use their ransomware as a service that they just bought from the same marketplace to encrypt this environment without having any clue of what they're actually doing and it's very common this is another access to a government institution within the u.s and they got in through vpn and then they have rdp and they give you pretty good understanding of you know what the organization is what you'll be buying and um you know if you reach out to them you can find out all the details of what they're actually selling on this specific market so it it's very common this is something that uh you know all day all day every day they're posting
new uh direct access into organizations um over here some of them will do blanket posts like this you know domain admin into a saudi arabian hospital domain admin into a usa government network in connecticut so this person has multiple networks for sale at the same time and often you know if these organizations are implementing multi-factor they will give you instructions for how to get around the controls that they have implemented um so it's pretty much like uh leaving it there's no guessing it's uh it's very easy to use and very easy and into some significant organizations uh just by crawling these forums and being willing to put up money to to gain access now just how
successful are some of these groups um this is a guy who uh he actually just recently was arrested so so that's the only reason we're listing his name here but uh and andre turchin of kazakhstan he uh also goes by uh the name of the invisible god msp now if that sounds familiar you may have read the article about this guy attacking three prominent antivirus vendors within the u.s and uh selling access to their source code and he sold their source code directly and he sold direct access into these companies that was his that was his thing he was a initial access broker and just to give you an idea of the scope of this
he had victims and 135 different companies across 44 different countries and it's estimated that he's made at least 1.5 million dollars and uh just in july of this year he was arrested and charged with computer fraud wire fraud and related hacking crimes um and the only reason he got caught was because he went after the anti-virus vendors it was too big of a story too much publicity um so something where you know he he couldn't just uh you know pull off this attack and and keep hiding like he'd done with a lot of these other organizations that one was the one that did him in um you know he went after a group that actually had the means to track him
and uh was pissed enough to really want to follow this thing to a close uh to the initial person who'd uh breach their perimeter to to begin with so taking it to the next stage looking at these marketplaces you know that's essentially where a lot of this these transactions happen it's a central and quote-unquote kind of trusted location for these groups and individuals to share and trade and sell all of this stolen information and access and uh you know find new partners to work with um and figure out you know how how they can expand their overall operations um what's interesting to me about this is we've seen a significant shift from a lot of these
groups moving from the darknet to just clearnet websites a lot of these you don't need tor or itp to access anymore you can just access them directly um you know a lot of these actually have uh the escrow solutions built in i would actually say pretty much all of them that are successful due and then some of these actually include full chat and email support type solutions and uh some actually go through full third parties to do this it's run like a a legit full business essentially and the key to all of this is building up reputation across these platforms because all of these groups that are uh you know operating in these in these forums have
to have a level of reputation associated with their accounts in order for anyone to take them seriously and for them to do any sort of business with them and now you know we were we were just looking at you know exploit.n and xss and some of the more public ones but some of the interesting ones are sites like russian market which are essentially websites that specialize in just selling direct access to specific data and it's more like a traditional marketplace if you will so um once you log in here you're presented with all these various options for what you can buy here first up what we're looking at is just direct access to uh to single systems
and as you can see here they have the country listed where they're located the first couple octets of their ip address the isp that they're using you know what type of operating system and they also list if they have admin access to these hosts and they have the different vendors that post the data here but essentially these ones are going for pretty cheap if you just want to buy access to a single asset and use that for whatever you want really i mean it's only five dollars to purchase access to to a lot of these systems and so that was uh rdp they have ssh as well same sort of thing ssh is a lot cheaper
as you can see like a dollar 90 cents 80 cents for access to these various linux boxes now what's more interesting i think is uh these steeler logs so this is going to be a lot of people that have access to web logs and related logs within organizations where they actually have the visibility to view encrypted traffic or they view people accessing certain services and they actually sell the logs directly and what's funny is you can hover over these they'll tell you um you know do they have the logins they have passwords they have cookies uh all sorts of information that could be very useful for an attacker to gain access to bank accounts to
social media accounts and and various other websites and things like that um and these are going for around seven dollars or so a pop so so you know pretty good deal for what you're getting here you know of course they have the credit card dumps these are going to vary in price based on you know what you're actually gaining access to with these cards how much money is on it you know where they're located uh the type of card all that good stuff and additionally i don't think i included a screenshot but they sell paypal accounts as well same sort of thing and relatively cheap to gain access to to a lot of this information
now russian market is only one of these uh many many many uh markets of this type that are out there uh another one's uas or ultimate anonymity services uh they are selling you know the same sort of thing direct access to individual assets over here about ten dollars you know 18 and so forth so uh interesting thing with uas is they actually sell social security numbers as well um you usually have to get these in like bulk or you uh you know have to kind of guess and hunt around to find what you're looking for but pretty cheap right uh someone's identity and oftentimes this will include uh their email and sometimes passwords to their
email account for around two dollars so pretty cheap to gain access to a lot of interesting and sensitive information on on individuals now a lot of these are going to be private marketplaces that you have to you can't even buy access into you have to basically make friends somehow or you have to figure out bypasses in their website which i'm not going to tell you which ones we did for this but essentially over here you can see you can buy a remote desktop protocol in bulk uh you know pretty cheap again often organized by isp you can do bulk orders by country by isp um you know the the list goes on but really what i just wanted to highlight with all
of this is there's a lot of these vendors out there offering this data and additionally there's a lot of customers looking for this data so this guy amadeus mozart i guess is his name he buys rdp servers for encrypt so basically purchase access and then goes and encrypts these assets and looking at the various countries it's different dollar values depending on the countries where these assets are located uh usa going for the highest dollar value but essentially there's this whole ecosystem where you know criminals are providing this data and there's a market for it there's a significant market for it now the last piece of this is really going to be how they get their money out
and that comes down to money laundering essentially what we're looking at here is various usage of privacy coins traditionally what we saw was monero being used more heavily than uh you know anything else out there just because of its privacy privacy focus but now there are tools out there that actually say they can trace through these uh transactions and trace through um you know monero as well so they could actually come to find you know where where this money is going so uh these groups are now moving to haven protocol more and more because it's very similar to monero but has additional privacy uh mechanisms built into it to help kind of hide their money
now almost all of this money goes through cryptocurrency tumbling tumblers of some kind um so that's a big thing that's difficult for law enforcement it's how do they actually trace these transactions through tumblers through changing of privacy coins and all of these various components so really what they're looking at and the way a lot of these guys get caught is when they're taking this money out of actually converting to to cash that's usually where where the law enforcement will actually be able to step in and you know catch these guys so a lot of them are keeping their money tied up in these various uh privacy coins for quite some time so i mean at the end of the day these
econ groups are really going to leverage any and all means at their disposal to profit from any of these breaches in multiple different ways um you know ransomware as a service we didn't even really touch on that uh you know the marketplaces around that but that is a significantly growing market that makes it very easy for people to get in on this and profit from these from these breaches i would say the combination of these two things right here is really lowered the bar to entry and made it easy for people that don't have necessarily the the complex skills required to pull off some of these attacks to get in and execute some significantly uh
damaging attacks and this complicates attribution um you know there's all sorts of components tied in here with code reuse shared infrastructure pivoting between organizations selling access buying access all these kind of components that make it difficult to really put a name and put an actor behind these things of course we can say you know we know who created this we know who created this component but who executed the attack you know it's very difficult now just do you do how how much this you know is complicated by it by all of these different kind of components so really you know high level you want to deploy import protection segment as much as possible and ensure
that you have that layered visibility into what's happening within your organization and uh you know understand and be aware that these attackers will compromise third-party and adjacent targets in order to come after your organization uh directly and um even though you can negotiate with these people and you know oftentimes get the prices down on your ransoms and stuff like that you should never fully trust them and take the mindset of you know they probably still are in the environment and uh you know we need to we need to basically look through this in full detail to understand what they actually did from beginning to end and so that's why we always recommend people involve an incident
response firm when hit by ransomware because it's a much more complex attack i think than a lot of people give them credit for so it is something that's really changed uh significantly in terms of postcovid times as well and so with that i think we might have some time for questions but if not you can definitely reach reach me at my email or on twitter and i'll be in the discord for the rest of the day as well with that thank you all very much thanks greg we can try and do a question really quick um we just want to finish up at 12 30 for a lunch break um see there's a question from spike uh
we see a lot probably the majority of malware now profiles the system on which it's running um and most often will halt operation on vms with identifiable things like the vmware drivers or vmware tools installed on the system so is uh the question is is vmware going to address this problem by giving users the ability to randomize or modify the driver file slash registry associated with these drivers so that they can't as easily be profiled that is a great question that's something i i hope that we will do um you know coming from the carbon black side i'm gonna have purview into our vmware kind of ecosystem as much as i would like just yet
um but it is something you know we can always take this feedback back to them and say you know here's what we're seeing because you're right that is exactly what they're doing it's a great way for them to understand what systems they're on you know what are they in a sandbox are they in you know what type of environment and and figuring that out so so that is something i think would be very beneficial to to add um we'll see we'll see vmware is a big company and we carbon black is a small fish in this big pond so i don't know how much say we even have over these type of things cool yeah thank you for answering the
question um all right well i guess we're gonna break for lunch we'll be back at uh at 1 30 um with the next session and uh and brett discord will be going on so please uh feel free to hang out and uh and and talk see you all in about an hour thanks greg thank you see ya