CloudSec Rules Everything Around Me (C.R.E.A.M.)
Show original YouTube description
Show transcript [en]
so good evening everyone I want to just make sure cuz I was told from a very young age that I don't know how to control the volume of my voice could you all tell me in the back if you could hear me thumbs up thumbs down I'm used to pacing back and forth like I'm performing on stage like I'm gene Simmons so I'm painted in a corner here so this is unnatural for me so my name is Kyle Dickinson as you've guessed and welcome to my talk I appreciate you being here hopefully everyone socially lubricated from happy hour cloud SEC rules everything around me when I was coming up with the talk name I was listed in a wu-tang clan because
it's nothing to mess with however Who am I and what am I doing here well again my name is Kyle and yes I do drink monster I do not punch holes in to drywall though but monster yes should have had one today I'm a cloud security architect I also call myself a cloud security shaman because I'm convinced that anything to deal with the cloud is all just fairy tales pixie dust and unicorn farts so you got to have fun with there right I'm also a sans instructor I teach a five-day class and I'm gonna try to boil down some really good key points to just kind of bring in the basics and so the reason why I
created this talk was because there's a lot of cool talks out there they talk about hacking the cloud you know DLP in the cloud but I really looked and I was like what about just the basics like oMG we found at AWS or Azure subscription what do we need to do to make sure that we have security insight and how we do configuration management what about Incident Response Incident Response will change and we'll talk about that so one thing I want to start with though is who hears heard oh we have a server in the cloud so the service provider patches it for us who's heard of that before for anyone watching this there's about a trillion people in
here everyone's hands just went up so they have what they call shared responsibility model well Kyle what the heck is that well shared responsibility model is kind of like a diagram of course that tells you what you're responsible for and what the provider is responsible for this changes based on the type of service you're consuming infrastructure-as-a-service is going to be most common especially with lift and shift type efforts like we're gonna close our data center and we need to move to the cloud that's using Amazon ec2 as your virtual machines those are your actual servers right and then we move to platform as a service most people love this as your sequel it's a great platform you get to use
sequel and guess what you don't have to really manage the instance underlying on it who's met a happy sequel admin before I used to be one and I wasn't happy and then you have software as a service we'll talk about more on how they slide but software as a service the most common one I could think of is office 365 you don't have to administer exchange servers anymore hooray so how does that change based on the consumption that you're using well as you see on Prem everything's your responsibility the the hardware procurement the networking you know running the cables getting the intern to crawl underneath the datacenter to you know run a powerline infrastructure it
starts to slide and you'll see it just continues to get more and more into the service providers arms versus yours however there still is a responsibility that you have as a consumer an easy way to think about it is the service providers responsible for security of the cloud and you're responsible for security in it you don't want your service provider to be able to just patch your instances all willy-nilly that would be bad who here wants to have just a service provider have root level access to your ec2 instance or VM how many of you have actually patched a database server or exchange server restarted it and it came right back up unless of your Bill O'Reilly it and go
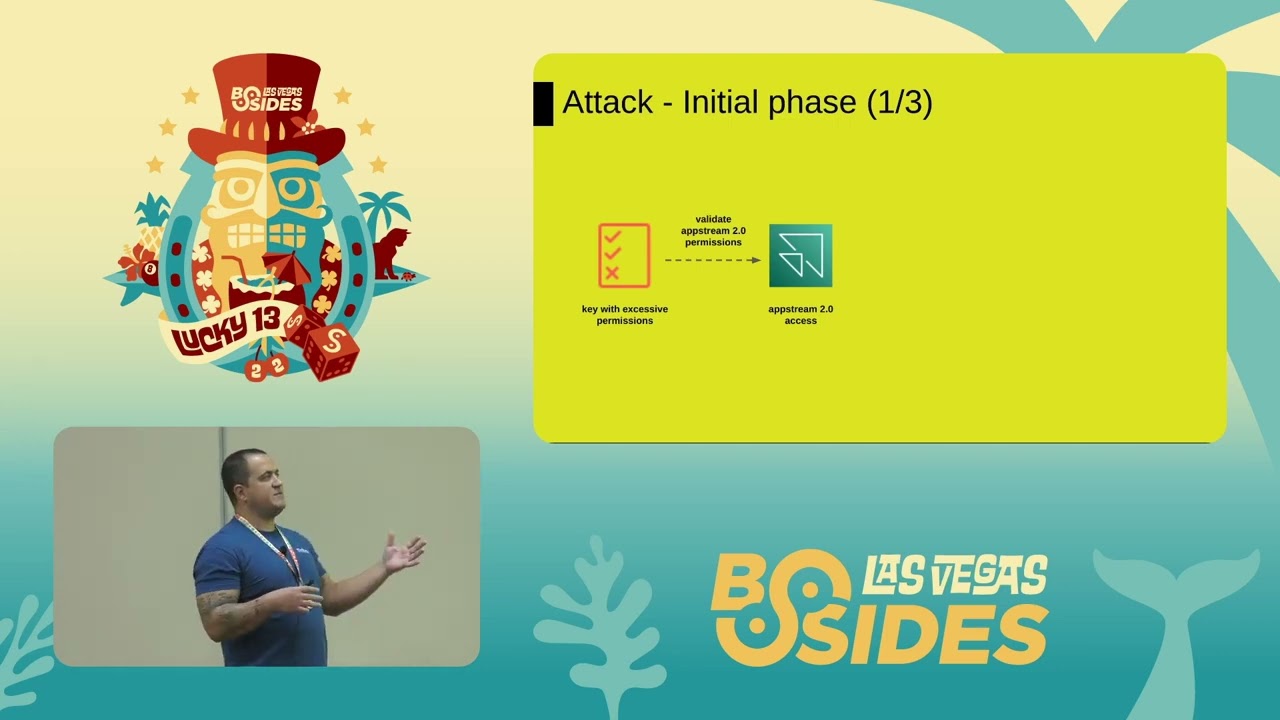
in Yolo you live your life first we're going to talk about logging now that we've kind of talked about the different types of services right so I want to tell you a tale I was in a room of about thirty very smart individuals and they said we're going to the cloud I'm like I think we're already there but how do we get all of our logging done to our scene or log analytics capability well I had the bright idea of well we're deploying this new tool let's set up every input we possibly can doing some bar napkin math for each input that you created you spawn a Python process for 200 plus accounts and configuring five inputs
each I'm no rocket doctor but that's a lot of math and guess what search heads don't like when you do that exactly what I did I crashed a crashed a search head I like to wear it as a badge of honor because now when you use this particular add-on there's a little warning that says do not configure on search heads I want I want to take pride in that and say that was me because Yolo so what kind of logging do we have when we use something like AWS and we'll talk about a sure don't don't worry we'll talk about them too when we talk about AWS we have cloud trail that's like the flight
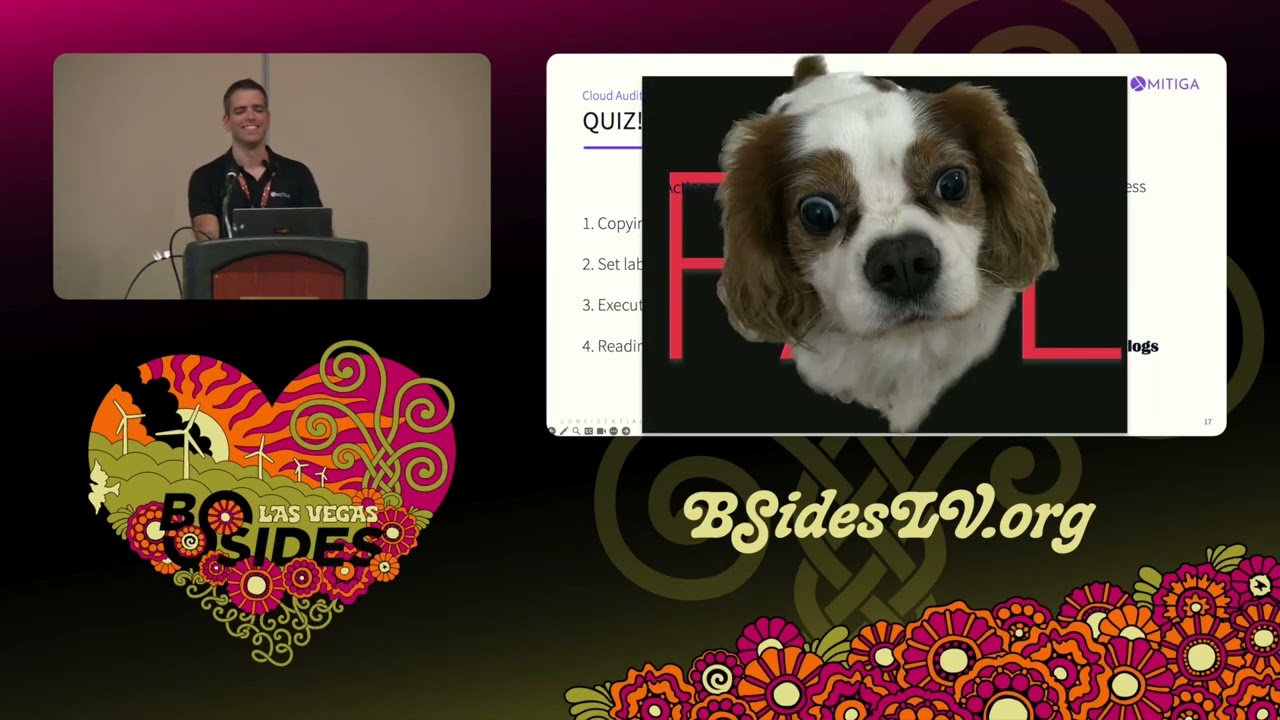
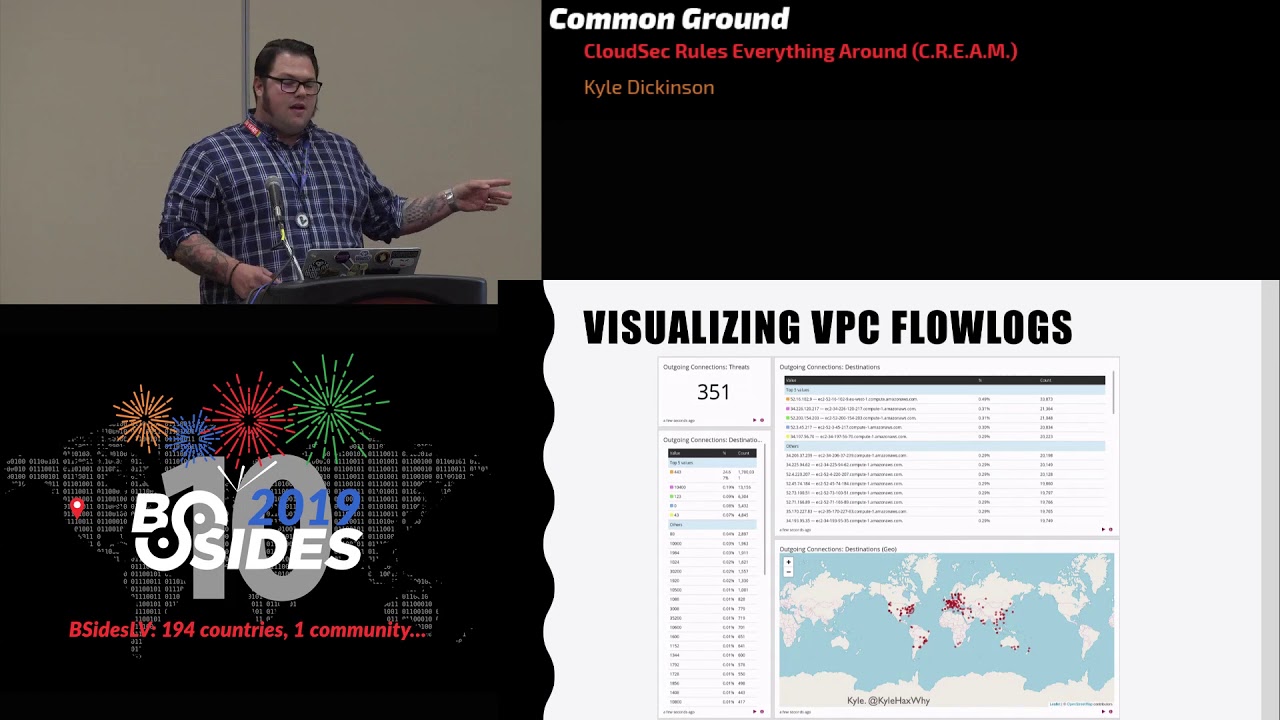
recorder of your accounts the who what where when and how if it could tell me the why that would be wonderful but it doesn't you have V PC flow logs now who here is like a you know IDs or IPS administrator and you're like I love that box that I have I get to monitor all the traffic your world is gonna change when you move to the cloud there is not really much east-west monitoring that we have available anymore unless if we architect it and thus add more technical debt and cost Noren overhead east-west kind of goes away however north-south is achievable what's really awesome is they just came out with VP see mirroring which is kind of like
copying and pasting all the traffic that went in and out of your V PC but that's only available in nitro instances at the moment so that's something to be cognizant of if you want to get flow logs it's gonna be you know something you strategize not just like yeah I turned it on now what with cloud watch logs this is a really cool capability because if you don't have a trillion dollar scene you can create alerts within those accounts based on this thing happened X amount of times send me an email give me a phone call send it to some sort of pipeline however would this really scale if you're setting up you know 200 accounts and you need to set up
you know five different cloud watch metrics and alarms how do you do that I would argue that you want to centralize it or use something like you know insert big seem name here or log capability here let's take a look at a cloud trail log ooh we're all amazed it's in JSON it's colorful yes imagine if it was exported in yeah more so cloud trail logs are nice because they tell us the who what where when and how and for the first part we'll break it down the who the whom so here we see an I am user and I blanked out the you know user name because I'm in a room full of hackers I also blanked
out my account ID because again hackers but we see that this is the account that it occurred on and this is the user that logged in now for this particular instance I was just logging into the console so nothing too crazy however if I was standing up like a ec2 instance or a virtual machine we would have more information returned in the request parameters so we could see Kyle stood up billion dollar per hour instance on this in time what's nice about cloud trail logs is they include the user agent so you can see how they authenticated where they using the AWS CLI where they using the SDK that's available were they using you know Chrome Safari who still uses
opera however what's tricky is and I looked at a very large environment there could be up to like 30 different user agents based on the version of the CLI based on the version of your browser based on the version of the SDK that you have so if you're gonna try to do some sort of longtail analysis there just be cognizant of we can't just say Oh Chrome Safari Mozilla you're gonna probably get back a lot of different user agents depending on how big your environment is so imagine we have a billion accounts well how do we set up the plumbing to bring all of those logs into our trillion-dollar log analytics tool I would argue that centralizing the cloud
trail logs is a very efficient method and you can actually do this with Azure event logs too what you're doing is you're exporting those to what they call an event hub and then you could have something just listening to that and then pull the logs but you have a single point to consume these logs what's nice about this is you're actually taking the evidence data in a sense out of the account that the actions are being performed in and then keeping them nice and safe in the security account that sounds great right yes kind of that sounds wonderful but the trick is you have a bucket policy that has a file size limit of 20 kilobytes
well Kyle that is a large text file yes it is I would agree however when you start working with hundreds and hundreds of accounts you can hit that hard limit so how do we do that and speaking of bucket policy how do we make sure that we give the appropriate permissions to all of our accounts to add logs into that bucket you know work with the developer like hey how do we automate this thing how do we you know determine it failed because I guarantee you you're not going to want to have to man do it I mean it's the funnest thing ever right so say we set up the plumbing for our cloud trail logs do we want to look
at flat files or JSON all day no we want to look at pretty dashboards what's great about visualizing this type of data especially if you have it all centralized is you could see where it's all happening if you know that most of your developers are in a particular region and then all of a sudden thousands of API calls are firing off outside of the country that might be an indicator of bad news something to look into right what's also nice about visualizing these flow these cloud trail logs is you could see who's trying to do something that they're denied if all of a sudden you know mark the intern is trying to stand up you know 20 ec2
instances and it's failing do you want to probably have a conversation with mark I would say hey yeah or do we need to get you the appropriate permissions always blame it on mark another nice thing about cloud trail logs and this is kind of a big topic at the moment s3 logging who's doing what to what files and what's nice about this is it full it's not nice that it's not enabled by default but if you enable it on the s3 bucket and then enable it in your cloud trail you then get these access logs then you could see what data is being written to what they is being deleted you know what is actually happening with those objects
that reside in that s3 bucket if you don't do a good job at data classification on premise guess what you could suck at it in the cloud too see I knew there was gonna be one heck ler and we talked about flow logs you know if you've ever looked at like tea shark that's really what the flow log looks like if anyone got tea shark/doo doo doo doo de doo stuck in your head I apologize but visualizing the traffic coming in and out again this is great for developers and also security use cases and you'll notice that a lot of these different types of log sources are dual purposed you could argue that cloud trail could be used for developers to
understand what is changing in their environment they could use that for configuration management you could also use it for security auditing in investigations with flow logs again not so much east-west information here but what is coming in and out of our B PC the V PC flow logs are really a you know - from and what's nice is it also includes the account ID however otherwise it's not too much information there is no real like click you get a P cap unless if you're using Azure which is pretty legit or routing the traffic through a P cap or in that instance right so when you're looking at cloud trail logs what are some bright ideas that you could come up with well
look for root user activity and best practices you should not be using the root account for anything and okay so funny story you had to use the root account to submit a vulnerability assessment request so that was kind of interesting yeah you also had to use the root for some billing stuff as well but I could argue that you don't need to use it to stand up ec2 instances so if you see root user activity occurring kind of check and understand why that's happening another reason why this is a bad idea is because there's no actual user attributed to that action all you see is the root user did a through Z it's not marked the intern
using the root user to perform these actions so put MFA on that thing and lock it in a vault things also look for is mf8 being disabled that's kind of an interesting event right work with maybe some data scientists and get an understanding of hey if this MFA device is disabled from this source IP from this user and then isre in a boleyn IP address that might be an issue there's a lot of different things you can do to fit your business use cases here cloud trail being disrupted when cloud trail was rolled out it wasn't really enabled by default but now if you log into your AWS console you see events there right but it's still not logging to what we
call a trail and that's how we get those logs out of your account and into your scene or lock at analytics tool but when you turn that trail off it sends one more API call saying hey I've been turned off kind of like the last shot in the sky so looking out for that because it could be disruption for evidence tracking is a good idea now you can argue yes you can prevent this from happening through organizations and service control policies but say you don't have that large of an organization that leverages those tools this is still a great idea to get alerted on if it happens lots of instances being turned on lots of instances being turned off
billing alarms OMG I can't tell you how many times I've been on Reddit and I've seen hey I think my account got hacked because now it says I'm gonna be spending ten thousand dollars you can set up billing alarms that'll tell you what your projected cost is for that month like I was literally sitting earlier today and I got an email saying your projected cost is $50 I know I'm breaking the bank here right but I want to spend only five so using billing alarms is a great way to determine compromised what do we get with Azure so with Azure you get a whole lot of different logging but we're gonna focus again on activity
logs and then network security group logs very similar to flow except through network manager you can now do a peek app which is cool with activity logs what I like about them a lot is there's this correlation ID so you could see when Marc the intern requested to turn on an instance and what the actual status of that action was did it get started and then completed and then is now running or did it get started and then it was denied because of some some policy that you might have in place on the role that he's using office 365 is its own little beast and we could spend a whole hour talking about it in fact
someone already did besides charm the tricky thing about office 365 logging though and the highlights that I take away from that talk and what I'll tell all my friends since we're BFFs now is mailbox logging was not enabled by default on your tenant there they now we're rolling it out to where it is now enabled by default but verify that because if you don't have mailbox logging enabled you're not going to know anything about those mailboxes especially if you have high-level executives that need to have you know sensitive actions performed another thing about it is is you use an office 365 management API sometimes you can get rate limited depending on the amount of events you receive and also to
make things tricky the office 365 management API has an Active Directory Integration so you can pull azure ad logs from this API but then as your ad has a whole different logging capability and believe it or not they don't have the same logs so you might be logging both of these things depending on what your requirements are isn't that fun and that's not a dig at all it's just the fact of the matter they're constantly improving this stuff but you know current state as of today using both AP is could be recommended this is my favorite topic where we talk about continuous compliance because I don't know it's just it makes me feel good to
know that I'm continuously compliant right gives me the warm and fuzzies and what we want to do here is we want to say bye-bye to shadow IT and we get to in a way who's ever seen that crusty old box that's kind of limping along and you hear the fan kind of like go away and you're like hey what's that thing doing it's like oh I don't know man don't touch it might break our whole enterprise and then you kick it and then the lights turn off for some reason shadow IT has been a big problem with on-premise deployments right who's had a big problem with shadow IT for those watching everyone's hands go up but
what's nice is with Azure Awl any service provider you get a you're really just using API is when you're using the user interface it's just visualizing the API for you you have the ability to query these API is to get an idea of your whole environment you can use that for asset inventory those sort of the C is critical controls yeah what's one of the top things up their inventory if you don't know what you got how can you protect your neck that's a shout-out to wave tank however now we have a new unique problem shadow accounts there's been times where you know I'll be talking to someone and yeah so I just stood up an account and I'm using my P
card for that well we can't protect that right now you may have to get clever with your management team on how you can detect shadow accounts but it's something to be concerned about because if someone is storing business day in their personal account it's gonna be hard to get it out right I would agree yeah so if you're having a developer do all their development in a personal account then they need to push it to prod you have business assets in an uncontrolled environment other continuous compliance tools allow us to check to see what has changed in our environment which is wonderful because who's ever had the problem of hey how come the network adapter is set to a
static IP instead of dynamically assigned now or hey who changed the DNS record on this mailbox server cuz now everything is always DNS right services like AWS config allow us to do this again if you don't have multi billion-dollar tools these are great services to leverage AWS config they had a quick start and it's now integrated with security hubs so if you wanted to stand up like the CIS benchmarks which is a wonderful way to kind of bring up a good baseline of security if you don't have to abide by something like HIPAA or PCI or Sauk - these are great ideas what you can do is you can have configuration checks to say hey this ec2 instance or
this RDS server or anything if it doesn't fall into these parameters show it as non-compliant and that's a wonderful thing it's a beautiful thing previously it was like two dollars a config rule to just have the rule existing in your account per month so we will talk about scaling again you have hundreds of accounts it's two dollars a config rule now keep in mind AWS config is a regional service so if you enable it you're not enabling it for your whole AWS account that could be problematic because if you want to leverage the Atlanta city that you get by using cloud services you're gonna have to monitor multiple regions but what's new as of recently is now it's
based on invocation for whenever the configural triggers so now if you just have a rule syn there it shouldn't cost you money always vary by that stuff though I'm no billing expert I use an app just account here's a fun story in the configural as I mentioned it can evaluate when you do a configuration change or you can have it set to periodically if you are in the process of moving at hundreds and hundreds and hundreds of servers over and you have a configurable that is gonna evaluate every time something changes with the ec2 API guess what that thing is going to evaluate a ton and then you're gonna get hey Kyle this thing cost us a lot of money or from AWS
saying hey this thing like reach the throttling and we need to kind of shut it off so understand how you do these evaluations is going to be based on your business requirements and also what's going on at that current time you know if you're moving hundreds of ec2 instances over our VMs over should you have that rule evaluated on every change or what it makes more sense to do it periodically I can't tell you that because I can't answer for your business but that's something to take into consideration it's also nice as it takes your resources and gives you an idea of all of your resources and what happens on the timeline this s3 bucket had a
bucket policy added by mark the intern and it allowed it to be accessible from the internet thanks mark there's other third-party tools that are a lot of really cool open source projects and I'll talk a couple about a couple of them one's called Prowler by a gentleman named Tony and Prowler is a really cool command line based capability that allows you to look at your account and parse it with CIS benchmarks because again those are just great ideas to look at it could perform gdpr it could also do HIPAA what's also very unique about it though is it could do a forensic readiness test so that'll tell you if you have all your ducks in a row
to do forensics on that account that's really cool how do we go about you know scaling this though another really cool tool is by Netflix you know small media company called security monkey easily one of my favorite names for a tool security monkey Sparra the simian army what's nice about this tool is it uses what we'll call cross account role authentication and we'll drill into that in a second but long story short a tldr on there is you don't have to have a local user for every single account you want to evaluate because then you you know start getting key rotation key management user lifecycle I don't want to spoil all the fun for Identity and
Access Management so I won't until we get there but that's just a nice feature what's also really cool is that if it sees you have a Genki configuration it's like hey the thing is not really a good idea you can actually accept that risk it's pretty darn cool so if you have businesses that have different risk appetizer and like yeah we know that thing is not really the best practice but it's imperative that we have it like this for it to run properly you could put okay this was approved risk evaluated etc etc etc and then you won't receive that information anymore which is also nice signal-to-noise ratios right and then with commercial tools there's a tool called red lock they
recently got bought by palo alto sass platform that monitors AWS google cloud measure does HIPAA GD P are again sock to CIS benchmarks and it does the same where you can accept the risk of something that alerts it also uses cross account role authentication what's also nice about this tool is it has a very well-documented API so if you don't even want to have to touch the user interface and you just want to integrate it to your CI CD pipeline oh man DevOps words now but if you want to present that information just via API you can do so I am up here no I'd anything in Access Management so Identity and Access Management is still a huge problem if
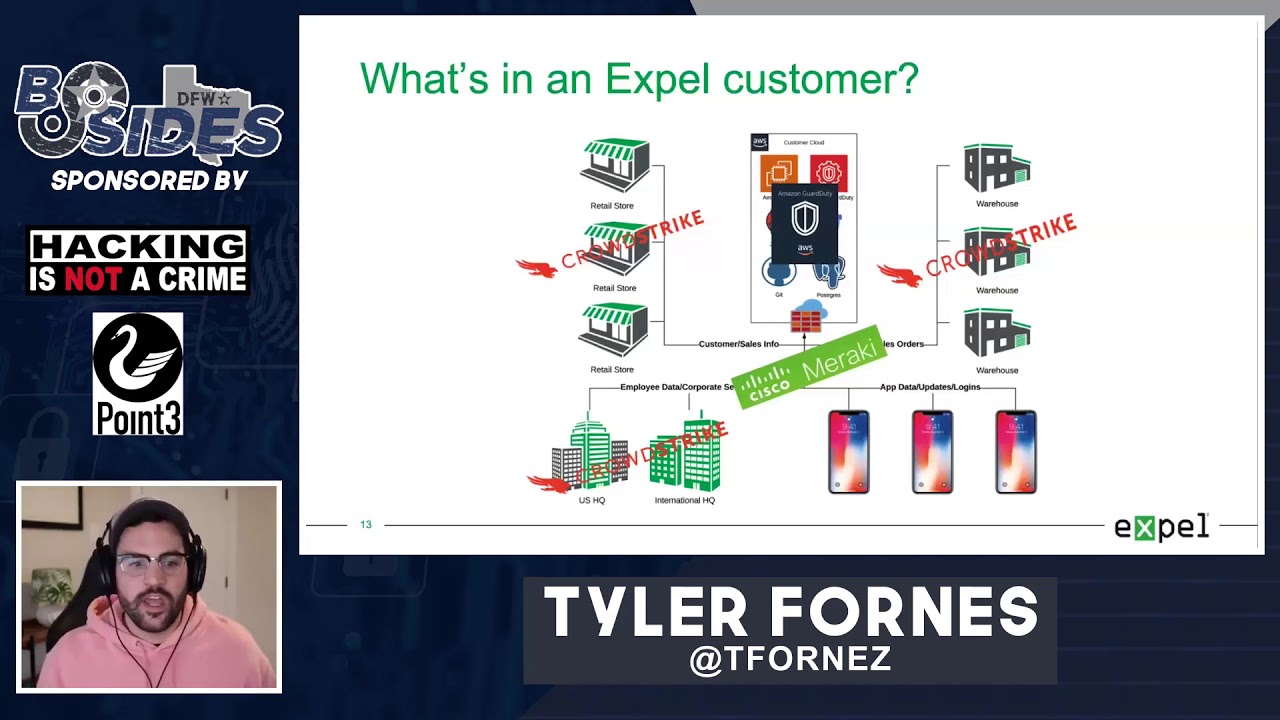
you don't do it well on Prem you could do it even worse in the cloud I mentioned process account role authentication and I'll beat that thing into the ground because I love it it helps you out so much so what does that actually mean well most of us probably use Active Directory and some sort of federated identity like ping or octa or one login what this allows us to do is manage access at a global group level and then use federated identity to do a sam'l assertion or we're doing a sam'l assertion and assuming a role into an account so say I am mark the intern and I need to access a security role in the
glue factories account what I could do here is I can log in to my security account and then from there all of the other accounts that we support have what they call a trust policy that allows mark the intern to assume the security role as long as it's from this account ID and from this specific role and here are all the permissions that apply to one this is very similar to how those other tools would work with cross account authentication what's nice here is that you're still using a single source of truth for user identity because user lifecycle is fun you get to enforce your local user passwords your MFA and then it just kind of blasts you
off into your accounts it's a beautiful thing with a juror you don't really have to do much of this because everything under your domain and azure is just in one single pane Darris a single pane of glass who has a bingo card right now so that's what's nice about using those types of authentication methods because imagine having hundreds of user accounts across hundreds of different AWS accounts or subscriptions and you need to enforce key rotation on that it's gonna be a fun task to figure out I guarantee it what are some of the best practices MFA MFA MFA you probably have MFA on your Facebook why wouldn't you have MFA on like the administrator console for your
cloud service footprint thank you using federated identities is also great because could you say with confidence that if Mark the intern was done with his internship he's going back to school we can guarantee without a doubt that he no longer has access to any of our accounts that's a scary thought then that's why we want to look into how do we do lifecycle management with local users as well you know if you fail to plan here you could really plan to fail it's really hard to hurt all the cat's back into the barn after they've been let out and running around who's ever tried to pick up a cat from a field and try to bring them back in the house I
know I haven't I see some hands and just like oh my god yes I did there's scars emotionally too so with user lifecycle policies using tags can help out a lot as well if you have a service account that is a local user tagged it with what is this thing or who owns it what's their email address what's their blood type no but what you want to do here is you want to enable your incident responders to quickly identify oh this thing just you know updates ntp but this is the owner of it so if you disable the key because you'd ever want to delete a key right off the bat because you'll never get it back ask me I'll tell you
you disable the key hit up the owner saying hey we think your keys been compromised okay I'll rotate it out of the you know application that's using it perfect or heaven forbid no no no don't delete it it's embedded into our application it'll break everything using automation can help out a lot too so say you do have suspected key compromised you can tag that particular user and say you know investigation then like your case ID or something like that and then automatically disable it there's actually a really cool tool called AWS IR and it allows you to automate disabling of the key we'll talk about Incident Response and what we can do there so again your incident response
plan is going to change because what do we not have when it comes to using a cloud service provider if I walked up to a data center knocked on the door and said hey I'm in the middle of investigation I need my hard drive they're gonna drag me off the property and probably have me arrested so how do we adapt our incident response plan to a service provider to our imaging standards change how do we do our incident response do we test our incident response have we verified that we can actually perform incident response there's nothing worse than letting your IR team just watch the world burn because they don't have the appropriate access to do their job well
how do you verify that do in game days testing it out testing your tools that's kind of like assuming your D our plan works until you need to actually Dr test your incident response plan you know are there any lessons learned on something that you can do to improve on
so with that being said we kind of shot through this does anyone have questions and not more or less the I have more of a comment than a question question question question question question question from a multi company standpoint if nobody has any key management already in place on Prem what would you say was your best recommendation for key management in the cloud so the question was for a multi company business that doesn't have on Prem key management what do you do when you move to the cloud well one if you can avoid using local users that's a thumbs up to what you can do is you could use something like a configuration management tool like you
know Prowler red lock or CIS bench or configural z' to show you when an access key starts to get towards say like X amount of days so say you have a policy in place that says every 90 days you have to rotate your key identifying the owners and putting ownership onto them there's gonna be a big part of it unless if you're gonna have a team that's dedicated to doing Identity and Access Management in your cloud footprint it could be a challenge and very big challenge to tackle some may say you know you can use the AWS CLI to just grab a token and assume a role instead of using a local user it'll vary there
is no silver bullet
yeah so I mean in terms of doing say detection response the automated response side seems like a WS SNS and and as your event hub have minute level granularity not sub second-level granularly do you have any solutions for sub second level or sub second level event generation not really because we're limited so the question was how can we get results or events faster than what the cloud service provider will give it to us we're really limited to that that's you know at our beck and call and that's just something that we have to learn to accept because we can't force those locks out of the service provider faster than what they're being generated at hey thanks for the talk by
the way um so what are your thoughts on automation around to incident response and detection like setting up lambdas and obviously you have to deploy cross region and a lot of things so kind of what is what do you use and what are you kind of seeing is the the future of that yeah so how do we automate Incident Response and make it multi region and just work very good err well using lambda functions is great or using CLI based tools yeah I highly recommend automating a playbook because if it's something that's repeatable why you do it yourself right that's the great thing about using cloud services just automate the toil I have seen where if an incident occurs
and an investigation needs to happen it automates standing up you know sift workstation takes a snapshot of the potentially compromised host shares that snapshot with the security account and then you can attach that snapshot once you create the volume as a read-only volume to that forensic workstation and then you can perform your analysis there are tools out there like margarita shotgun that allow you to take a memory image but the problem with that and I would argue that a problem with a lot of different types of Incident Response when using cloud services what if that server is not domain joined how do you authenticate to that server to perform acquisition so we are trying to move
right now from multiple individual user accounts in multiple AWS accounts into a single federated model do you have any recommendations on the best way to accomplish that sounds like a million dollar question so so it really depends on how you want to leverage accounts to you because I've seen businesses leveraged separate accounts to limit the blast radius so say you'll say you know HR IT they use this account for only their HR stuff and no one else has accessed except maybe the incident response team right how do you go about federating that access well do you want it to be like a hybrid model where you can access those resources very similar as you would as
it's an on-prem data center because then you're setting up like direct connects and or VPNs to access that or are you gonna do a pure public deployment where you're accessing everything using a public IP address it's it's a challenge in really something to strategize as you're moving the workloads because otherwise you may have all these workloads moved over then you're like well maybe this deployment model wasn't really the best thing so how do you want to access it how do you want to secure it or what kind of visibility do you need to create hey thanks to talk you mentioned AWS a new zoo do you have much GCP experience and if so what are the
parallels for each of the points you talked about so I myself haven't leveraged GCP as much from what I've just been at an enterprise standpoint a leveraging AWS and azure has been a big strategy that I've seen I've seen also a lot of developers leveraging Google cloud that's not necessarily a dig at all I just personally haven't used it that much
you notice that reinforce that Emma so now has the virtual network tap right I haven't played with it so I don't know what it connect you to do for you but it's there now so were you speaking of like the V PC traffic mirroring that AWS now offers okay yeah so yeah that that is that is available now however on nitro instances only so if your incident response or your plan is hey we need we want to do V PC marrying you will need to architect that on nitro instances which is like AWS is super custom created infrastructure that they made and it's been available now for I want to say a couple months I know they
announced the service publicly at reinforced in June but yeah that that's a cool capability that could have some cool functions hey hi so just curious have you ever had a situation where you've had to a grenade multiple sims into a singular sim for log aggregation due to license costs scope size scale that makes sense no so the question was have I had to ever take log data from multiple seams and then pop it into one single no thankfully you know it's been one tool to kind of rule them all but if you want to do something like a data Lake so then other you know various tools like you know naming just a few like Splunk
logarithm sumo logic and you want to just consume the data dependent doesn't matter on what tool you use that's an option
yeah okay so if a service provider has like a native scene capability in it no I haven't those tools do have a place you know I'm still playing with those as well but I don't know if they'll yeah not not at the moment I haven't so kind of a follow up um data transfer costs can be a big thing do you have any thoughts on reducing that data transfer cost there's actually a diagram and I'll actually tweet it out because it shows where you would get charged for where your data is going and how it's traversing really the answer is there's no simple way that I have found other than just you know monitoring what's going in and out and
your billing right but there's a diagram I could tweet out that shows where it is you're getting billed when you get transferred and all that so on the tweeters Kyle hacks why super clever when it comes to Twitter handles hey Kyle hello I was hoping you might have some some words of wisdom on closing the knowledge gap between like your your classic sim your classic IT security shop and where incidents are happening in the cloud and where where developers are living in a kind of a honestly more you know cloud centric war yeah so closing the knowledge gap that is a tough one because it could be based on you know who's actually you know do you
have your own cloud security team or cloud security develop or cloud developers but closing that gap is really just socializing and bringing in different exercises you know if we were to do this on Prem you know look at your playbooks on Prem how can we transform those into the cloud there's lots of different like basic trainings out there and a lot of different comparison charts so like if you do it in AWS this way this is how you could do it in Asscher or if you're looking for something like AWS config sure this is what you're looking for but I think it comes with communicating a lot they say when you move to the cloud
Security's ground zero it's you know everyone's responsibility at that point and I would agree we do have to make relationships with developers oh my geez yes we do have to create relationships and I have found that creating those relationships are very beneficial because when they come across something they're like oh I don't know if this is a good thing they come to you you know instead of you gotta kind of transform the mental model of how security is operated right you know if we keep saying no every time we're invited to the barbecue we're gonna be you know not invited to the barbecue anymore so how can we make that a mutually beneficial relationship so if you were to give your
Independence Day speech on moving to the cloud for the people who are still stuck in mainframe land and like I will lose my job if we move all these servers to the cloud what would you say to a security and a systems team to make them understand that this is not a bad thing you don't have to worry about the humidity in your data center dry heat thanks for talking to me bro
you don't have to worry about tape backups you know who's ever had to restore a tape backup but you know the storage facility is across the summit pass and that summit experienced eight feet of snow and then you know this company can't take their semis across the summit you're like oh man that sucks kind of triggered there right but yeah I would I would show the shared responsibility model and say look at all the things you don't need to do anymore you don't need to lift that pizza box into Iraq the money now when it comes to spending in the cloud that's also a tricky thing what's also nice is that you can scale your resources up and down
very very easily how many of you have ever had like to provision a VM and you're like I want 64 gigs of RAM and all the storage and all the CPUs and then you're actually only leveraging about 10% of that you know capability or the horsepower that you got well you can be more cost-effective and scale that down you don't really need 100 million gigs of RAM and 32 flops of CPU yeah
what is the best practice on protecting the root account passwords because if I put it in a safe or I put in an HSM then I then I'm don't have disaster recovery for that location and if I put it in one password I don't have audit so who accesses it and I don't I'm not compliant with BCI because now we have a shared admin account right so using something like a password ball that has the user attribution on who checked in and out the password is great if you still have like a security office that would do you know mark the intern check the USB key or the Heba key or the gemalto hard token or you know the phone
that has all of our MFA tokens on it out at this time then checked it back in at that time that's a good way really depends on where so working with a global company it could be tricky because you can have an office where the security team sits in building a in a different state than the development team now who is better posture to handle those keys we could all argue that security pros and lead hacks ORS that we should probably own those keys right but if they need to do administrative tasks and they're doing after-hours do you have someone on call to grab that key for you yeah you can't really duplicate those hard tokens right so that in
itself is a challenge fireproof safe in a security office
ever done girl simulations of the alternatives of sending your sim data on-prem versus keeping it in both a sim in the cloud and an s3 bucket respectively so that is a great question I'm glad you asked it where do you send your log data when you are consuming cloud services and you have like an on-prem deployment or is it appropriate to have something deployed to the cloud I call the time where I sent thousands and thousands and thousands of events to an on-prem collector and it saturated oh and linked and caused you know a little bit of disruption sorry so when you're starting to shift to the cloud do you start using like a cloud-based sim or
log analytics tool I would argue that it's appropriate you know keep the cloud in the cloud no sense and bringing it back on Prem because then if you have you know a cloud service based then it's coming back on Prem to just go back out I mean you're just getting costs everywhere you could store it in an s3 bucket absolutely yeah you know you could form a data Lake using s3 I've seen companies do that yeah I personally have not done the cost simulation though that would be tricky and I would it goes back to you know how tricky is data transfer rates right were you first can you get around to 20 kilobyte bucket policy limitation can
you get around it no it's a hard limit that's etched in stone for now I say that and then tomorrow it's gonna change
separate it might so the question was if you had a bucket policy that you need to manage and have thousands of accounts may be breaking up different buckets for different types of business units would be appropriate or by different businesses themselves or the use cases like you know these are all of our development accounts and so all the dev data is going to go into this bucket all of our production accounts will go into this bucket it's how you you know something to strategize so you wouldn't actually go and put it into several organizations similar to the a shared folder structure right you'd be actually creating different buckets themselves yep I think we got five more minutes
left unless if anyone has any other questions I'll be out in the hall or trying drinking water stay hydrated it's hot here a lot of the cloud security auditing tools are sort of reactive in the sense that they're dynamically querying the the Amazon API and getting the status back where have you seen anything for proactive assuming that like you're going completely through your CI CD pipeline and terraform and you want to check that something's compliant before you actually allocate the resources in Amazon yeah so again question is how do you be more proactive instead of reactive when a Genki configuration might get pushed through long story short yes you can do that in your CI CD pipeline there are a
lot of open source projects that do that right now and I do believe that Palo Alto just came out with one where it'll check cloud formation templates and your terraform template to look to see if anything is out of you know a compliance like CIS or HIPAA but yeah that is a great place to do it and using tools to integrate to that CI CD pipeline who's ever had to ask someone to fix something asked her they have done and they're like oh I've already been tasked to another project I could check that out in two weeks it happens a lot to all of us so having that immediate feedback loop for those development teams is a
really good idea yeah that's achievable though I think we're gonna get kicked out