Using Threat Modeling to Harden Your Identity Infrastructure

Show original YouTube description
Show transcript [en]
hi i'm jared brennan i'm an identity strategy and solutions advisor with sailpoint and i've worked in a number of roles throughout my career i've had enterprise roles i've had consulting roles now i'm on the vendor side and i put together this talk to tie a lot of that information together to help organizations understand how to harden their identity infrastructure by bringing the concept of threat modeling to bear specifically on identity a good starting point is to just chew on this question for a sec which parts of your business rely on your identity infrastructure if i'm talking pure place security i can look at some of the trends that we've seen around data breach activity over the years and i guarantee as you
dig deeper you'll find that compromised identities are at the core of virtually every single breach that's making the news and then abuse of of the privilege assigned to those identities and because identity as a concept is so pervasive throughout how our organizations operate there's tremendous value in figuring out how to harden that in a way that enables a business to do what they do without enabling attackers to get in when uh when they shouldn't um to just think about this at a high level uh provisioning of new entitlements to an identity um and let's let's take a new hire for example right if somebody gets hired at your organization they're going to get at a minimum a
domain account and an email address now realistically they're going to get a lot more than that but even if they're not on the domain they're going to get creds into the hr the payroll the benefit system so that they can check their taxes right they can uh update their their benefits once a year everybody in your company has an identity and and uh they're gonna have access to something now those domain accounts are gonna give them access to a lot of things um you know maybe their laptop internal file shares like sharepoint um eva or sharepoint right the wireless network databases on-prem apps there's a lot of stuff that you're going to link back to
traditionally active directory and if you're federating then you may be giving them access to some cloud apps as soon as they get access to that on-prem directory uh and even if it's just like sas apps or if it's infrastructure if it's aws if it's azure they're going to have a login and if that login isn't their domain account it's going to be a native account it might be where the user use their email address is the username although the password is going to vary from one platform to the next and this is what we're talking about when we talk about your identity infrastructure at a very high level and that's just flesh and blood that's not even like
service accounts or rpa right robotic process automation accounts or customer accounts right i'm just talking employees so understanding kind of that flow is step one and if you ask yourself well you know do we have any parts of our business that don't need identity that don't rely on the identity infrastructure you may have some components out that there that are maybe independent of this but i have a hunch that's going to be a much smaller subset than uh than what identity touches and so you've got some some choices to make right you've got to determine well where am i going to start what path am i going to follow to to clean all this up
um and i want to i want to give you some of that here today when i talk about identity i talk in terms of identity governance and administration so this this is more than just iam right your traditional identity and access management this is giving people access to the things they need in order to do their job making sure that access is appropriate at any given time and taking access away when they don't need it that the concept of governance really gets around making sure that all the things that you're doing are appropriate and as you're applying threat modeling to hardening your infrastructure you're going to be making changes you're going to be reducing what people have access to
right the number of entitlements they have number of systems where they even have accounts governance comes into play there because you want to make sure that you're not doing something that's going to keep somebody from doing their job i'm a big fan of the identity defined security alliance as a a vendor agnostic resource for figuring this identity stuff out if you're not familiar with the idsa they're they're kind of like a wasp if you're appsec right the open web application security project has been around for decades uh the idsa has only been around for a few years and they're a blend of there are a lot of vendor organizations that have contributed content based on what they're seeing in
the field and what their technology does uh and by a lot i mean over 20 different vendor organizations have said this is what identity looks like from our side and there's also a customer advisory board that includes uh practitioners and consultants to take all that information and say okay now that we've got all this this data what should people be doing regardless of the technology what should people be doing if they're they're covering all of their identity things and what the idsa has done is drafted a an identity defined security framework that includes just under 30 best practices that map to use cases and reference architectures to to help answer that question it's freely available to download from
this website and they have a blog that helps make the the connection between what we see in practice and how their framework applies and i wanted to share some things there before we get into the threat modeling piece so they've got three sections in that blog entry i just mentioned they talk about challenges with identities challenges with access and privilege and then challenges with third parties because all of that is in scope for this identity stuff um when they look at their their population and they tend to go out and survey the market right larger companies a thousand users at a minimum usually uh organizations with ten thousand or more and they ask the the leaders the people
actually doing this stuff day to day what's changed what does your environment look like and they look like at organizations over half the organizations they interviewed said that the number of identities that they're having to manage has increased uh more than five-fold over the past 10 years and i know from my own enterprise days i had to fight for every penny of budget and every head count on my team over and over and over and as more and more responsibility came our way that didn't automatically mean we got more budget or we got more people it just meant we had to get more creative about how we managed that environment and in the identity space i
have a hunch whether it's through organic growth whether it's merger acquisition uh you're seeing some of the same that you're managing more identities but at the same time all these additional identities result in stale accounts that nobody's using anymore but nobody knows to turn them off complexity is the enemy of security and as you're taking on more and more you're adding complexity to your environment that complexity if you look at the number of passwords we're asking users to remember some of these organizations had nearly 200 separate accounts that people were using to log in and do their jobs and when i look at password security and we we say why are people using stupid easier to remember passwords
it's because we're making it too complex for them to do their jobs it's because we're creating all these disconnected systems and they've got to have a way to get in the system and prove that they are who they say they are and the numbers are real i mean this isn't hyperbole this isn't made up this is what they're finding when they go out and talk to people and say hey what's it look like in your environment and when we look at it from a threat perspective they're finding that almost every single attack against these organizations every single threat requires some sort of human interaction which is why identities and the accounts associated with those identities are such high
value targets i've done a lot of pen testing over the years and privilege escalation and lateral movement are just beat into me that that's that's what you do when you you pop a box right you establish persistence give yourself the highest level privilege you can on that box and then try to grab another one so that even if they find you on the one you're still in you can still do what you're doing marriott unfortunately with their publicly disclosed data breach had an attacker on their network for four years before they caught them four years and i look at that and say god that's ridiculous how does that happen because the attacker knew how to get in
establish that persistence and then act like they belonged there that their account looked like it was doing what it should be doing um and we're seeing that you know the vast majority of these breaches and just attacks in general successful or not are going after privileged accounts and abuse of those privileged accounts whether it's by an attacker by an insider is one of the top three patterns that shows up in the the dbir from verizon and then of course like i said with lateral movement um once somebody's in they're gonna try to get around and that's just the the corporate accounts right now that we're extending our trust to these third parties we're crossing our fingers and hoping
they're doing the same and those third parties you can have nearly 200 uh third parties that you're sharing uh you're letting log into your your stuff every week with nearly three times that the number of third parties who somebody your organization is sharing data with is giving sensitive data to all of this comes back to your identity infrastructure if you don't have preventative controls in place and if you're not monitoring for uh aberrant behavior right potential misuse then you quickly become one of these statistics um the idsa in their most recent paper identity security work in progress hired a research firm to go out and talk to over 500 they're called qualified professionals so this is executives
uh individual contributors and managers who are actually doing identity on a day-to-day basis and again that that broad spectrum like a dozen different industries and and then some accounts ranging anywhere from 1 000 employees to uh they've got a whole category of 10 000 and up and these are the patterns that these people shared anonymously with the research firm to say yeah this is what we're seeing 94 virtually every single one of them who they talk to said yeah we had a breach and identity was part of the problem and of that 94 right well of the the entire population uh 79 percent and it happened said it happened within the last two years um so this isn't some trend that uh that
we're moving away from it's still very much a a an active real thing and the overwhelming majority 99 of these people said that we could have prevented it had we done something different on the front end this could have been stopped and i i don't know who that one percent is right i i got to think that you know in my experience everything's preventable from a security perspective except for that you know black swan scenario but uh i i'm not here to judge right i'll just leave that as is the the last stat i wanted to share from from that report um is that they they took a look at these organizations and asked them to
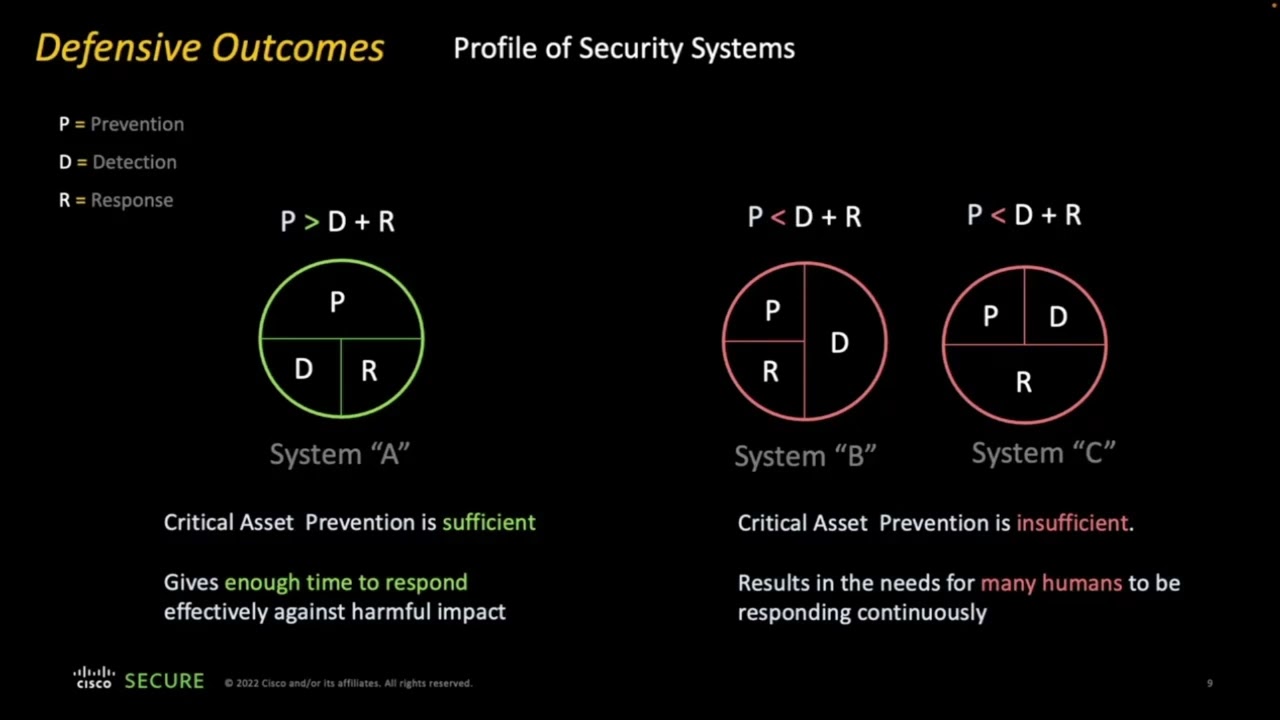
categorize themselves as either proactive forward-thinking or reactive and the proactive organizations saw an impact or even a breach to the tune of 25 less than the number of organizations uh who classified themselves as reactive and i mean that that concept comes at no surprise if you do security well on the front end the likelihood of bad things happening goes way down but to me the number of organizations right the disparity between we decided to do something on the front end versus yeah we just wait until we see something publicly disclosed and then go into scramble mode it was a pretty big gap highly recommend you check out this report and that you use it internally
as you're sharing this information because it can be overwhelming and i know it can be doom and gloom and oh those numbers are terrible how will we ever uh ever get ahead of it that's not the case no when you apply this concept of threat modeling to with a specific focus to your identity infrastructure you can have a measurable positive impact on whether or not you become one of those statistics and when i say this concept of threat modeling it's about applying a very deliberate systematic approach a repeatable process toward identifying threats and attackers and putting safeguards in place that you can come back to again and again and track improvement and show people that yeah we're
we're making changes for the better and this isn't compliance right because if you go out and look at publicly disclosed data breaches the number of compliant organizations that have ended up on these lists is way too high and the number of compliant organizations that don't even realize they've been compromised yet is the bigger concern compliance is binary right we're either doing it or we're not doing it but when you you bring threat modeling into play you're adding a lot of level of quality uh to your process right now it's not one one or zero right it's all or nothing no it's this is how deep we're going and how well we're doing at tracking all of this um carnegie
mellon's software engineering institute has a uh a write-up on a dozen different threat modeling methodologies that you can use i've got a link to it here at the end of the presentation i'm not covering all of these today but i do want to cover two of them to help you get started although you may want to check out that that article after you you get your feet under you the two most common threat modeling methodologies you're going to hear about in the space are stride and dread they both came out of the microsoft space they're both uh not being maintained as kind of an active discipline or practice but they're they're still both pretty relevant
they're they're pretty uh active in the the industry a lot of folks are using them today and they take slightly different approaches to threat modeling both of them use mnemonics so stride stands for spoofing tampering repudiation information disclosure denial service and elevation of privilege and when you're identifying a threat and running it through this process stride is saying i want you to answer these six questions about the threat where does it fall and um dread takes more of an impact-based approach to say you know with with these threats how bad are they damage reproducibility exploitability affected users discoverability um and so either methodologies is taking this idea of hey there's a bad thing that we have to
to do something about and putting some values to it putting some criteria that you can measure to say because this one is more significant than that one we're going to take action on this one first and so the the point of of the two methodologies is to help you do just that is is to help you put some prioritization around what you do so that you're not spinning your wheels and most importantly so you're not spending time on the minutia and spending time on things that can have the the most significant impact your organization when you apply the threat modeling process there's a simple four-step process that you'll go through regardless of which methodology you use
model the system find the threats address the threats and validate and this is what i want to go into at this point i want to talk about tools and techniques that you can use at each of these phases at each step along the way to help you build out that repeatable process so let's start with step one modeling your system here the system is your identity infrastructure so how do you do that how do you model your identity infrastructure well it it helps if you know where your identities can do things right we talked about identities have access to resources well the access is usually granted through an account and the level of access the specifics of
what they can do are all the entitlements associated with those accounts but from an identity governance perspective you got to step back and take a one one layer higher i'm not just looking at accounts i'm looking at flesh and blood people me jared right i at the company i work for have multiple accounts and i have different entitlements in all these systems where these accounts have access but i'm one person and all of those accounts have this there's a one-to-many relationship between jared the identity and the accounts that jared has so in order to kind of reverse engineer that mapping of identity to accounts you've got to figure out where all of your authentication stores are
and start creating this like an identity warehouse right you need some mapping to say this person has access to all these things and i say that that's at a corporate level right that might be an employee that might be a contractor but now with the rise of especially robotic process automation becoming so ridiculously popular um there are all these non-human accounts that don't map back to a flesh and blood person although you might say that jared is the one responsible for an rpa account so there may be an association between a human and a non-human account that's a good first step is identifying all those directories also looking at your third parties your customers right
don't exclude those apps or systems because they're not employees again if it's an identity if it's a person needing access to a thing you you want to capture that information somewhere so there's a little bit of legwork a little bit of investigation here when you're looking for authentication stores um you might look at larger systems or platforms anything as a service would be your your cloud authentication stores you're going to have authentication stores on-prem that more often than not are going to be an ldap directory or a database ideally you're going to be moving a lot of things toward a single ldap store again complexity versus simplicity here but start by trying to just put that
list together and in order to to help you put that list together go into the process with the concept of the joyner mover lever life cycle in the identity space this is a pretty common uh model you'll come across it at some point if you haven't already uh and these are the events that result in state changes with your identity right if i don't have a relationship with an organization today and then i sign up somewhere and they say okay jared you as a person have this relationship now we need to start giving you accounts and giving those accounts entitlements that initial sign up is a joiner event and it's from a business process standpoint it's
going to trigger all the technical changes that happen to enable me to have access to things now over time those relationships inevitably change in the employee space this is you know commonplace people get promoted people move to a different department people go on long-term maternity paternity disability leave people retire but still need access to certain things in order to do their jobs those mover events still need to be identified and tracked but they're they're much more complex to automate you can automate a joiner event to some extent but the mover events require a little more delicacy a little more intricacy and then at some point there's a lever event when someone is no longer engaged with the
organization if i'm not there anymore and you need to take my access away well you need to know where i have access you need to have that one-to-many mapping defined because when that lever event happens if i'm leaving on unfriendly terms the reality of human nature is sometimes people are hot-headed sometimes people make decisions that they'll regret later on but those decisions can have damage decisions like deleting an entire organization's cloud storage account look that story up that's a fairly recent story that is very concerning so look at your authentication stores within that identity governance life cycle because you want an idea of when things change and how do you collect this information if your organization has a cmdb
start there it's going to have most of what you need if you've got a team doing more like service management and asset management now they may have collected the vast majority of this information already you'll want to spend some time looking at excuse me third-party relationships which include not just vendors you're working with but even like software as a service app so people are using you can find a lot of this with your procurement your accounts payable teams if you sit down with them and say who are we paying monthly bills to right who are we paying bills and how do i know whether or not that relationship comes with access with login to a website somewhere or if
we're granting those people the ability to log into our stuff they'll know so build that relationship with your procurement team your ap team uh you can also use technology like a cast be a cloud access security broker um you can look at heck even if you've got a layer 7 firewall and you're looking at application traffic for login activity right you've got technology deployed today that will help you round out the data you get from your ap and procurement team that will help you uh identify that shadow i.t especially if you're not paying for it it's one thing to go say who are we paying each month but it's another thing to say uh where
are people uploading data uh but we don't have a business relationship we don't have a contract they're just doing it um and what i found and and this is crazy simple but it works uh reach out to people non-technical end users and ask them a very specific question here what websites do you log into in order to do your job i guarantee every single person at your organization can answer that question because it's not technical it's not overly complex and they all know what their job is right you don't that's not your job your job is to help them secure it but if you reach out to these line of business end users that will help fill the gaps in where
these other two tools may be lacking and especially now that we've had such a monumental shift to remote work you may find that some of that collaboration is happening more quickly as people are just signing up and using things without going through ap without going through procurement uh with um stuff that they're all connecting to over the internet that doesn't necessarily have uh uh you don't have visibility into the network traffic so uh use that uh non-technical approach and on your network right do an nmap scan look for your directories ldap listens on 389 and 636 uh if it's ldap s right secure and then http and https your web apps you know are going to have a
login page so traditionally you're going to find them at 80 and 443 but all the admin consoles all the non-standard ports that the development teams and the the infrastructure teams have enabled uh for administration or for testing uh 8080 8443 are common but they're not exclusive um so and and this is above and beyond like your uh if you've got bnc if you've got secure shell right what all the other protocols but you're looking for where can people log in and you can get that within map and nmap remains one of the most uh useful free tools in the infospec infosec space today um so once you you do that step one right you're modeling your identity
infrastructure you're looking at your your joint or move reliever workflows you're looking at all the places that people have accounts and entitlements mapping that back to identities then you're ready to shift your attention to the threats and when it comes to identifying threats that you should consider right threats that you should evaluate as part of your process privacyrights.org has maintained a chronology of publicly disclosed data breaches for years they have breaches dating from 2005. to 2019 who was compromised what do we know about how many records um and they stopped maintaining the database in october of 2019 with a promise that they'll get back to it but you can take all of that years and years of data that
they've collected and look at the aggregate that comes out each year from the verizon data breach investigations report where they identify trends and patterns based on data breaches some of which may not have been publicly disclosed also take a look at how i've been pwned from troy hunt to to date have i been pwned has nearly 10 billion accounts in their database so going out there and looking at what resources has troy incorporated into that tool is going to give you an idea to kind of follow the the trail follow the breadcrumbs back to that data breach and if it ended up and haven't been blown can we get back to root cause what's been publicly disclosed about it
and then i'd also look at google news i've got some alerts set up they're just daily emails of keywords a quick search on the keyword data breach or even just go at their point in time and look you've got a lot of information you can tap into about publicly disclosed data breaches go back and look at what were the root causes of these breaches what do we know about how the attackers got in and build that into your throat modeling exercises you should also download nist special publication 830 rev one their guide for conducting risk assessments even if it's only for appendices d and e um appendix d uh outlines the number of threat sources
and appendix e outlines a number of threat events it's i mean it's almost like a checklist right copy paste over into your um your your threat modeling documents right and uh you've got a huge head start you're not having to sit in a room and just come up with stuff out of thin air no these people have done a lot of research over the years and they're giving you a lot of information to help you get started and what i really like about the nisstock is from a technical standpoint uh a technologist tends to go right down into the weeds right i want to look at the the vulnerabilities on the system give me the
the bone scan reports let me look at the the criticals that have publicly disclosed uh exploit code right um but nist breaks down this uh these threats into three different categories right there there's the information system level but then there's also like the business process level right are your users doing anything in their day-to-day job that if that process is disrupted or just by the nature of that process or is there a body or population of threats that are relevant to what they're doing and how they're doing it and then at the organization level there are another family of threats like take mergers and acquisitions if you've ever been involved in m a whether you've been in a company
that's been acquired you've been the company doing the acquisition you've done consulting around that if you have two companies that have grown up independently of one another and suddenly all of their identities need to be able to work together that all these systems and apps need to talk to each other you might find it becomes least common denominator until we can figure it out i did consulting once for a company that had their stuff together right their active directory uh security posture was actually pretty tight um and they were bringing in a very immature company from a technology standpoint and in order for this company to continue operating the team that was doing it well had to
loosen and lighten their controls right they had to let up on what they were doing otherwise the company could make money and that money pays for the tools it pays for the budget it pays salaries so um that's there's a different kind of threat than a very specific like a single injection attack right it's it's very different but um that's the value that when you look at the nist stock that the value of looking at holistically at this stock can give you it also points out a distinction between adversarial threats and non-adversarial threats because sometimes uh stuff is just accidental right if somebody's using an account that's over entitled they're a privileged account that has way too many
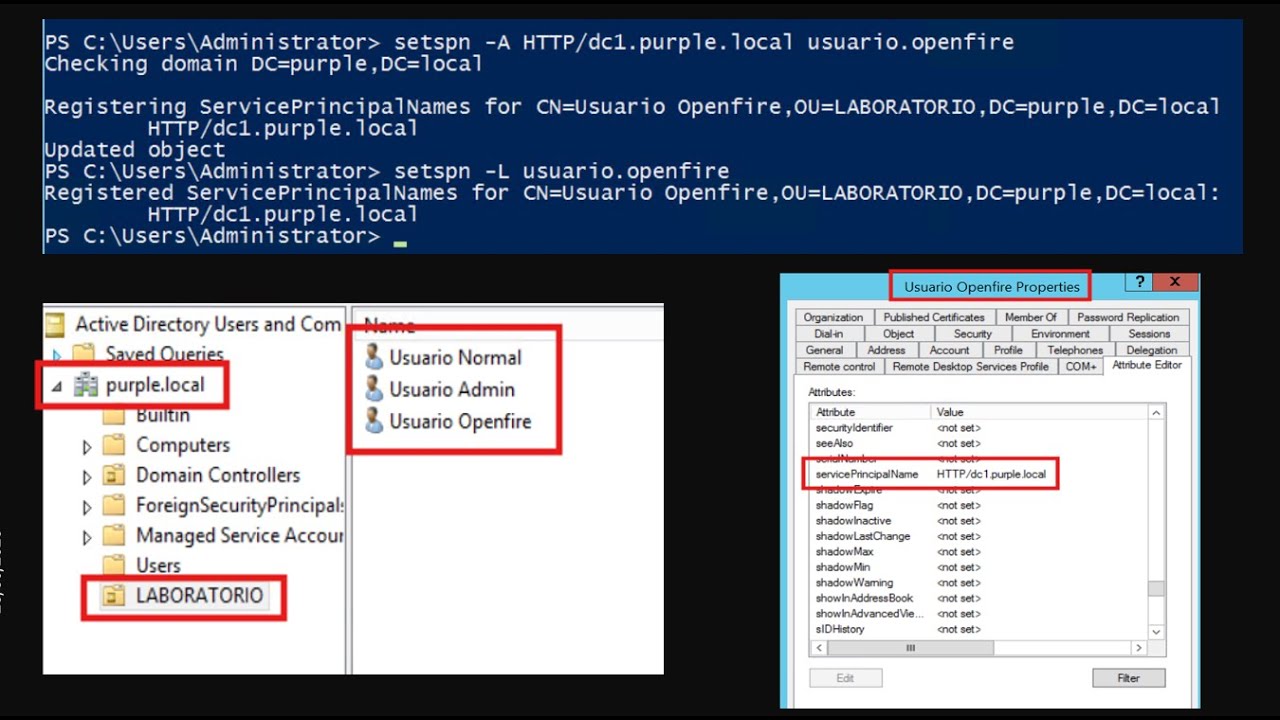
privileges that's not necessarily intentional but the damage is still going to be just as bad if an attacker gets our hands on that account so look at this this document and i've got a presentation i've done a number of times called hacking identity where i go into a lot more detail about pen testing and tools and techniques that i would use as an attacker and people a lot smarter than me would use to get in uh within 15 minutes on day one and it's always always going after credits i mean it's not overly complicated exploits it's a lot of it's password spraying i do a lot of ocean gathering and try to gather information that might
help me later on but i've got a link to this talk later on if you want some very specific kind of red team attacker details i've got a lot in uh in that resource as well so once you've you've done that you understand your environment you're looking at the threats that are relevant now you need to say well what are we going to do about them right um what steps are we going to take to address these threats and one of the biggest challenges is getting this stuff out of your head and onto paper so that it makes sense right because it's even if you just go through those two nist dependencies it can be
overwhelming so how do you break that that complexity down into simple like data sets or collections of elements that that you can step back and say yeah we need to act here and we're okay over there i use xmind i know free mind is a good tool in the space as well but like if i identify password spraying as a threat which here's a little secret it absolutely is to your organization um then i i might say well what are we doing to prevent that are we training people to use strong passwords are we blacklisting certain passwords that we know an attacker is likely to try like summer 2020 exclamation point um are we using multi-factor to make it
harder to launch that type of attack uh or have we been able to enable passwordless authentication so it's not even there's nothing to to target right there's a lot of things on the preventative side that you want to draw out but on the detective side what are we doing to detect it well maybe you've got a security information management tool in place that's looking for that type of attack right one password launched against all the uh the user accounts in your environment but what are your third parties doing maybe that's a blind spot so see now you can start to say we've got this in hand we're doing this control but wait over here we've got a
gap uh and then what are we going to do when we detect it if you don't know what null routing is don't jump right in you might say if i see somebody doing it they're definitely bad i don't want to accept any traffic from their ip tread lightly because you can inadvertently do some damage but use a mind mapping tool to uh to just start putting order around these these threats that you've identified and then you want to analyze your attack surface right you want to get more detail about what's out there above and beyond that kind of attacker's perspective i do a lot of ocean gathering um between showdown and census you're going to have a pretty good idea
of what attackers know you have on the internet uh dns dumpster and fine sub domains are a good complement to that uh between those or among those four tools you get a lot of these are the systems and ports that are exposed externally in other words these are places you can log in if you want to attack us uh and then because you work for your organization you're not limited to passivo do some active nmap scans right do a full poor scan of uh your internet facing systems right don't break anything but see what ports you can identify that have been exposed externally see what systems like non-prod especially have been exposed externally that you
can maybe take offline and then do just that right but before you get too deep into this exercise right even as you go through that first pass of all the threats and you're you're doing maybe say you settle on stride so you're going through and doing stride for each one and helping to kind of score how bad they look at your environment in your environment how worried you are about them um you can do some cleanup concurrently right you don't have to wait until the whole threat modeling exercise is done if you know you have network ports exposed externally that an attacker could use to try to log into internal systems but there's no legitimate business purpose you you're
allowed to submit a ticket to say can we close that that network port right you don't have to wait until you get through your threat modeling exercise if you know that you can again reduce your uh your exposure you can do the same with apps that can either be taken offline if they're exposed externally or maybe moved uh internal hiding behind vpn or come up with some other way to to access it may put about one of your cloud environments uh disabling inactive accounts is a gimme right if you have accounts that belong to people who don't work at your company anymore and you don't have any any reason they got to be careful if they've got
business processes that someone hard coded their account into be delicate with that cleanup but you can kick that initiative off as soon as you start your threat modeling process you you don't need to wait there and then reducing privilege right taking away privileges folks don't need if you find that they're over entitled or uh if their account has too much access right part of your your remediation stage your stage uh three of addressing your your threats is closing things down and just as a matter of good hygiene you know you can do this stuff right away one of the more challenging things that infosec pros have to consider though is there is cost and benefit
in play here right if if you look at um all the threats you've identified and and you come up with safeguards or controls that you think are going to be useful uh if you're going into that with no consideration the cost then you're going to be sorely disappointed when management or leadership says yeah we just we can't afford that or we can't uh justify spending that much money to protect that resource now if it's a matter of physical safety or loss of life whole different conversation but there is a cost benefit analysis to be done so that you can determine whether or not you're overspending or underspending on the the solutions you're proposing so bring that to bear when you get to this
stage of the process and then the validation right sooner or later you've you've got to go back and um i know some of you may know this proverb uh it was actually made popular by reagan in the 80s right trust by verify that's right uh the the u.s president in the 80s was using a russian uh proverb uh reasons for that but i got separate conversation uh don't just assume that when you tell people hey we've gone through the threat modeling exercise here are the things that we should do uh don't assume that they're just automatically going to get done you've got to go back and take a look the those technical scans are going to
help some of that if you've taken stuff offline um i would go even deeper instead of just like poor scans with that map deep authenticated scans this can actually arguably be pulled forward into the the analysis it's tricky because threat modeling is more of a a conceptual exercise than the amount of the the technical uh resources you bring to bear it can make the process too cumbersome on the front end but at some point you do want that technical data because it's real it's an actual representation of what your environment looks like and when it comes to scans you should absolutely be doing authenticated scans of your hosts and you should be doing unauthenticated scans of production
facing web apps and authenticated scans of non-production instances of those same web apps without an authenticated scan of a web app you're uh you're missing a huge portion of your attack surface um but you you can take this data in uh and use it to verify whether or not certain things have been done and you can also feed it into the next iteration of your threat modeling exercise um you can test whether certain actions have been taken through user awareness training right we talked about uh user interaction being so common with actual attacks against organizations so uh through a lunch and learn whether it's physical whether it's virtual through online training social engineering simulations with
tools like covants or know before social engineers toolkit still free out on github right just test and see whether or not users are falling for some of those identity based attacks right when you come up with the threats and say yeah we think this is really bad here um you can emulate some of those uh attacks exploiting or using those threats as your the basis for the attack and determine how resilient your organization and your users really are part of that testing goes above and beyond just basic simulations though deep dive pen test absolutely whether it's an internal red team whether it's a third party that has a specialty deep experience in pen testing you want
to bring that to bear i'll be a fan of the pen test execution standard till the day i die it is so good this little grassroots thing it just gives you guidance around how to run a pen test and you can see threat modeling has been considered a part of the pen test standard for gosh since day one so if you're engaging a third party to do a pen test feed them your your threat modeling uh results right when you go through that exercise and you've captured all that information just hand it over and say this is the stuff we really care about hammer away i mean it may be a more embarrassing report if you look at pentest report
that way but really that's not what pen testing is it's an education tool and that's just giving you a significant advantage right you're getting so much more value out of the time and money you invest if you're sharing that throughout modeling information and having a pen test that actually adheres to to that standard and then a few tools that uh i'd recommend you actually try on your own to give you some insight into uh into your environment and into an attacker's mindset discover is a great ocean gathering tool i used to use ntl on bother but i know if you pop a set of domain creds and get in and can hit the the domain
controller crack map exec lets you launch a password spraying attack directly against a dc um against web interfaces you can use something like burp right the paid edition of burp uh to do a password spraying attack um and responder is a great uh little tool that if you're on the internal network takes advantage of the the chattiness of um ethernet to try to get creds um but just a few tools to check out again i've got a lot more in my hacking identity presentation but when it comes to validation don't just hand things over right get engaged roll your sleeves up give it a try so so what should you do next right now i'm giving you kind of
here's some some methodologies and some resources around methodologies here's the process explore those various threat models and pick one that you want to try right don't try to do too much don't try to do everything just pick one and say hey we're going to go through a throughout modeling exercise where we pull some resources out of that nest stock and then we sit down with a group of people and try to figure this out so pick a methodology and draft an identity data flow diagram not a technical architecture diagram just a joint remove reliever uh workflow how do identities come into that business relationship with your organization where do they propagate accounts and entitlements uh and
how do you manage changes and what do you do when somebody leaves right just a high level i've done this in maturity model assessments i do a lot of assessments of identity programs where i apply the capability maturity model and the identity defined security alliance framework to help organizations understand what they're doing and how well they're doing identity and we always front end that conversation with the data flow diagram just a real simple white board 20 30 minutes it's been eye opening every single time for the people in the room to say i did not realize that that's how that works i thought it was different um so do that at the beginning of your
threat modeling exercise right just put that diagram together vet it with a couple of folks and then you know you've got to put a team together because you don't want to do this in isolation you don't want to do it in a vacuum you want to uh bring people in from the app side infrastructure your devops team um maybe uh you know legal right maybe uh um audit maybe human resources line of business right it's going to vary depending on your organization but it's also a chance to build relationships and help people understand why you're improving your identity infrastructure why you're making changes to the way they always did things because you're helping to provide
resiliency you want to make sure they can do their jobs but you need to understand organizational level business process level and information systems level threats so that you can take action to address those threats and then prototype this threat modeling process by doing it just once if if you pick stride or you pick dread as the methodology you want to follow for your first threat modeling exercise you're not married to it for the next 10 20 years right you can do it once and say yeah not for us and then go out to that carnegie mellon blog pick another one and you know just bounce back and forth until you find one that resonates with
your team one that makes sense to your organization um so just do those four steps you know take a take this slide deck i've got some other resources i recommend if you don't know adam showstack hit this guy up on linkedin look him up on youtube he's got a number of classes on threat modeling on linkedin learning to go into detail he's even got a book designing for security that gets into threat modeling it's going to go into a lot more detail than i can go into in an hour but uh adam's the guy when it comes to threat modeling and you can learn a lot from what he has to offer i've got that link here out to the
carnegie mellon blog a link to the nist document and then you know publicly available information is great if you can get involved in an isac uh specific to your industry you can get some insider knowledge around threats that people are running into right now so if your organization doesn't allow you to engage in an isac tell them i said they should because that's uh it's a gimme right it's just you're giving the attackers the advantage if you're not actively engaging in conversation with other professionals in your industry and if you're a leader uh put one of your people on this right you're the one who needs to fight for them to to get the budget in time to let
them do it the value is absolutely there but get them engaged and then uh the last resource um lenny zeltzer's critical log review checklist for security incidents it's an oldie but a goodie uh it's it gives you some very specific things to look for on the response side that will help you kind of again reverse engineer well if i'm if i'm seeing this in the uh sim in the the event logs then what triggered that right what led to that it's a great resource to help round that out a couple of other resources here including the book identity attack vectors from a press it was written by darren rolls who was a former cecil at sale point and maury haber
over at beyond trust mori's also got another book uh privileged attack vectors that uh get into this topic in a lot more detail and i mentioned i've got my hacking identity talk out on the youtubes right there's the link you go pull the one you want out of the uh the list they all cover the same material you just get different stories each time last but not least hit me up if you have any questions about this identity stuff about pen testing about building a program about building a strategy it's all i talk about anymore and i've got kind of that broad knowledge but i'm going deep into certain subject areas i'm an easy guy to find on linkedin it's
a social media platform to spend more time on so reach out to me there i'll get you a copy of the slides i'll send any other resources i have i want to help you be successful i i think you know mindset of abundance right we can all get better by sharing and learning and teaching so i want to do my part thank you very much for spending time with me on this talk i hope to hear from you soon take care