Threat Modeling for Security Professionals

Show original YouTube description
Show transcript [en]
so happy to introduce our next speaker in the black track Matt Trevor's he'll be presenting on threat modeling for security professionals a little bit about Matt Matt Trevor's is a technical manager for Carnegie Mellon's software engineering institute matt has more than 15 years of experience in information technology information security and secure software development strategies matt obtained his master's in computer information systems from Boston University and his bachelor's in computer science from the University of New Brunswick Matt also holds the CISM cissp and C CSP professional credentials with that like to welcome at Trevor's Thank You Ryan all right so he stole one of my slides which is good because I have too many for 30 minutes the obligatory SDI
disclaimer so we'll go through that so what we're gonna talk about today a little bit about me I'll go over some terms so when I say things you'll know what I what I mean may be different than what you interpret we'll go over when we should do this exercise what the exercise is and why we're doing it I'll review the OWASP top 10 pretty quickly then the meet the stride threat modeling then I'll throw in some octave Allegro some mitigation strategies you can use alternate sources of threats and then obviously a summary so Matt Trevor's this is always the most complicated slide in my deck because our company has an identity crisis so depending on where
you are some people know search division some people know the sei and some people know Carnegie Mellon so I work for the search division at the software engineering Institute which is attached to Carnegie Mellon we are an FFRDC which is a federally funded research and development center we do lost lots of awesome stuff we are hiring this gentleman in the front right here is looking for a pen tester so one quick reminder that we have lightning talk tracks going over during lunch so if you'd like to go to either the gold or black track we do have some 30 minute talks lined up otherwise feel free to continue of your lunch we do have beverages that are
being served including of the adult variety so if you would like to join those talks though please start making your way there we'll give you about five minutes or we'll just continue along so some terms and these look pretty obvious but I just want to make sure that we're all on the same page when I say things so a threat when I say threat I think of anything that negatively impacts your business right it can be an advanced persistent threat such as a nation state it could be a script kitty who just found this super new tool and starts banging on your website can also be an insider right an insider threat or a disgruntled employee it could also be
the backhoe operator about to put their bucket through your internet line right that's also a threat to your business a vulnerability unknown or unknown weakness so the most popular would be zero days right that's what we all hear about in the news is zero day this zero day that vulnerabilities can also be propping your door open so if you have access control at your organization and somebody's moving stuff and they put a a door blocker in there that's also a vulnerability asset assets so there are four types of assets when I talk about them so information so any information created by your system so if you have a customer relation management system the data created by
the CRM would be an information asset log files can also vote also be information assets then we have technology which are just the hardware and software that drive your business people we also consider people assets the people that operate your critical service and then facilities the facilities would be the the brick-and-mortar buildings where any of the other asset types reside risk so if you've taken your cissp you're probably thinking threat times that's the the base one right if you come from different lines of business you may be thinking probability and severity or impact and likelihood when I talk about risk I talk about the the likelihood of a threat exploiting a vulnerability and the severity of that
exploitation that is how I typically define risk we have qualitative and quantitative which which are both two different types of risks for us non experts in risk qualitative is usually where we start that'll be where you see a matrix where you'll have low moderate and high and then maybe different different items so two popular qualitative risk analysis are Dredd which is made by Microsoft and then octave which is Carnegie Mellon product quantitative is for professionals this is where youyou speak in terms of finances or percentages a really good example is fare factor analysis or information risk they fancy themselves a quantitative risk analysis also if you read the book how to measure anything in cybersecurity risk they will talk about
using confidence intervals in Monte Carlo simulations to be able to make a statement such as I can state with 90 percent confidence that if you don't install this control you will have a twenty to twenty-five percent of data breach in the next six months that's very complicated and not the subject of today's talk but that is where people want to go they want to be able to quantify their risks and then two of the topics we'll talk about today stride and octave stride is a threat modeling framework created by Microsoft in their late 90s that stands for spoofing tampering repudiation information disclosure denial of service and elevation of privilege we'll get into that and what it actually means and then
octave is a risk analysis framework operationally critical threat asset and vulnerability evaluation so we'll talk a little bit about that and you'll see why in a moment okay so what exactly is this and when what and why should we do this so you want to do the threat modeling as early in your development lifecycle as possible so if you think of discover design develop debug deploy maintain dispose as as the system development or software development lifecycle you want to move this as far left because this is going to help you with your testing and I think we've all seen that when you do testing or have your requirements defined you are going to save your
company money because you're gonna find vulnerabilities or issues with your product much quicker so if you don't find it until it's published to the field you have to get your helpdesk involved and then somebody has to triage it and it goes to level two and then developers have to be assigned to it and management has to get involved so it gets very costly very quickly the further down the pipeline you find a bug functional versus security testing so I'm going to just use login a login page as an example so functional testing on a login page would basically be putting the right username with the right password in and it logs you into the system right so that would be a check
also you would check for a login with a bad password and it would say invalid username or password that was would be typical tests that you would run against a login page security testing or negative testing is where you hit it with special characters so first thing I would try on a login page is maybe some sequel injection right so I'm going to throw some single quotes or some other characters that may cause the system to deviate from its normal process flow or I'm going to fuzz the field and try to put 10,000 characters in it anything I can do to deviate so that's great for technical folks but business folks are gonna say why the hell am i spending
money on this right it's it's added cost so what your business speak you're gonna increase the return on investment because you're going to move the the finding of the vulnerabilities of the bugs to the left of your process which is going to decrease your total cost of ownership it's also going to save you a little bit of embarrassment because if you don't find something until it gets in the news or it gets in the public it will make its way to the news and then you will have on your face so increase ROI decreased TCO okay so one of the I'm assuming everybody in here is familiar with our wasp right right great great yeah great
company international right security professionals all over the world participate they have many top-10 lists including the one we'll talk about today in addition to mobile and proactive controls is that a jet attack proxy is a really good open source tool you can use to test your application and then Sam for those that would like to institutionalize the practices that help build better software Sam so as you'll see there are two lists up here I have the 2013 in the 2017 there was some movement but not a great deal they changed some top and some titles injection is still at the top I would have thought we would have fixed that since 2003 but apparently we have not
cross site scripting sensitive data exposure two of the big ones that don't get a lot of love are Security misconfigurations and using components with known vulnerabilities software supply chain is becoming one of the biggest problems we have because as people just adopts code off github and don't really run it through code analyzer you're introducing vulnerabilities your your solution and you may not even realize all right so a threat modeling with stride it's actually pretty easy so we have our spoofing tampering repudiation so on and so forth they are each associated with a security principle that you should be familiar with so the reason why they called it stride is because they couldn't come up with a good acronym using CI a and the
other term so that was why they came up with stride because it sounded cool anyways what they've decided is you have the vi threat categories and you have four different depictions that are part of your data flow diagram so you're going to talk about external entities which would be web browsers or third-party integrations so if you're using Open ID Connect or an OAuth and you're sending it off to have somebody else authenticate your users that would be considered an external entity and if you look in the top left corner you'll see that you don't execute every element of Stride against every type of entity right so they've gone through and and made it this is where
you should start now if you feel that something else needs to be evaluated feel free this was just their starting point any questions so far nope yep right all right so what you do is you draw a data flow diagram in a large system this can get pretty unwieldly so if you're doing a brownfield so an existing situation maybe break it up into blocks if this is greenfield maybe do the same thing as you can see I have all four asset types but then I also have dashed lines the dashed lines to me just represent network enclaves so we may have DMZ s you may have extra secure storage in the in the back because you have your
databases and just want to talk a little bit about the various data stores I have so if you look over here I have customer data but I also have the database backup right a lot of people will backup the database with sensitive data and then forget they did it and now you have access to your system so it doesn't do a lot of good to have sensitive information backed up to a login and not pay attention to the database backup you'll also see that I have a process here for our DBMS right that's your relational database management system so when you when you evaluate a database you have to evaluate the data store and the process by which you're evaluating
again for reference we have in the bottom left corner the stride matrix and then this is a term a sentence that I I created to help make sure that you you classify it is threat of a threat actor using one of the stride executing against one a year your your data flow diagrams by exploiting a no hospital 10 so is there a threat of a threat act a threat actor spoofing an external entity by exploiting sequel objection right and then you can make a quick snap decision yes that sounds like something I should pursue and now I'm not going to worry about it because it doesn't seem likely okay so that can get really complicated
to to go through all 10 for all the time so what I would encourage you to do and this slide deck will be available for download after the conference go through and just Mark X's in a bigger matrix so I pick spoofing external entity injection broken authentication sensitive data exposure and you go down and this is again just but something to start with so it may be different for your system but this is these are the different lost popped ends that you would evaluate her combination if you'll notice as I mentioned earlier a 6 and a 9 are completely checked right because you should be checking for known components known vulnerable components and miss configurations at every step of
the way so imagine you do this against your system you're going to have a large number of things that you're going to want to check right and if this is the first time you're doing a threat model you're gonna be overwhelmed because there's going to be 400 things for you to check on right and you're gonna panic and throw in the garbage and say just stick your head in the sand so what you can do is use a risk analysis such as octave Allegro to help you order the important risks near the top so it's a qualitative risk analysis framework and it's going to help you prioritize the work and it does it in 8 steps
the first step is defining your risk measurement criteria and don't do this by yourself go find your business folks right you are in business you're doing security to help the business move at the speed as fast as it can okay so don't try to make the risk measurement criteria by yourself go find some some business focus um risk risk folks so I come from health care so obviously my example is going to be healthcare base so the most important thing in medical device manufacturing is do no harm to the patient so that is the number one priority we have when we did risk analysis so near the top I have patient safety and then I have low
moderate and high so low no are negligible delay in treatment a couple hours maybe for moderate and then much longer delayed or even death would be considered high right that's and then even if you don't hurt the patient you can't run afoul of the regulator's right you can't run afoul of Health and Human Services or any other entity that is paying attention so that would be the second highest risk for the organization then we have brand damage loss of productivity and customer confidence right so you define your risk matrix I pick five as a good starting place you can do for you can do twenty obviously if you do 20 it's going to take you a
much greater amount of time to do the risk analysis so we've defined the the risk measurement criteria we kind of got these next to the information asset profile in the containers for free with our data flow diagram because we've defined where the data resides and we define what our network looks like or what our components look like together our areas of concern and threat scenario scenarios we already did using our stride analysis is there a threat of a threat actor kind of activity all right so all we have left now is to identify and mitigate risks so here's an example right we're gonna talk about spoofing and external entity so remember when I said Patient Safety
is the highest it gets weighted as a five right so let's say I'm spoofing an external entity and I'm evaluating sequel injection right well typically when people do sequel injection they're not going in to change data they're just going in to exfiltrate the data from the network right so patient safety not really there it's not going to delay diagnosis it's just the data is going to go away right so it gets a low but since it's already waited as their highest it gets a five so we get five points for patient safety it may not negatively impact the safety of the patient but you're gonna hear from your regulator right if you have if you disclose more than 500 records in a
geographical area you have to report it to Health and Human Services so that would mean that would be a high and since it was rated second highest priority it gets four so four times three is 12 so regulatory legal gets a score of 12 and then we have brand damage productivity and confidence they have their own scores we get a risk score of 28 we move on to the next one right so you can do this in Excel in an Excel spreadsheet with dropdowns it's pretty easy but you're gonna do it for all of the various threats that you went through so every time you did is there a threat of a threat actor doing this side
or the other thing each one of those would get a line and you're in your Excel spreadsheet now something you'll come to realize for those that participate in agile software development is this isn't going to fit neatly into a sprint right so you may have some risks that are off the charts high but are gonna take six eight ten twelve sprints so you're going to take those epics and break them down into smaller components of work but at least when you go to do that your product owner is going to be able to look at this justification as to why it's important that it's scheduled in your release so we've identified all these issues we
have a couple hundred to fix where do we go to look for help so the Cloud Security Alliance cloud control matrix has a lot of really good ways to secure your cloud installation Internet engineering engineering task force standards o auth to transport layers acute security password-based key derivation functions all of that stuff is already done for you there's no sense rolling your own many of the frameworks such as the dinette framework has PD KDF built right in so you don't even have to to write those Center for Internet Security critical security controls they've just released version 7 one another great resource for determining how to mitigate risks 853 if your FISMA governed by government physical
requirements you can use 853 or 171 controlled unclassified information largely in line with 853 and then obviously international standards ISO 27000 you're going to say wait Matt where's 27001 27001 is like a three-page document with just titles the the meet is all in twenty seven thousand two twenty seven thousand eighteen is privacy in the cloud if you come out of this with anything do not make your own you are not smarter than the entirety of the the international security community you are you will you just don't do it there's a lot of good stuff Oh wasp is also another really good place so I can't believe I took that bullet out but OS would be a good place to go because
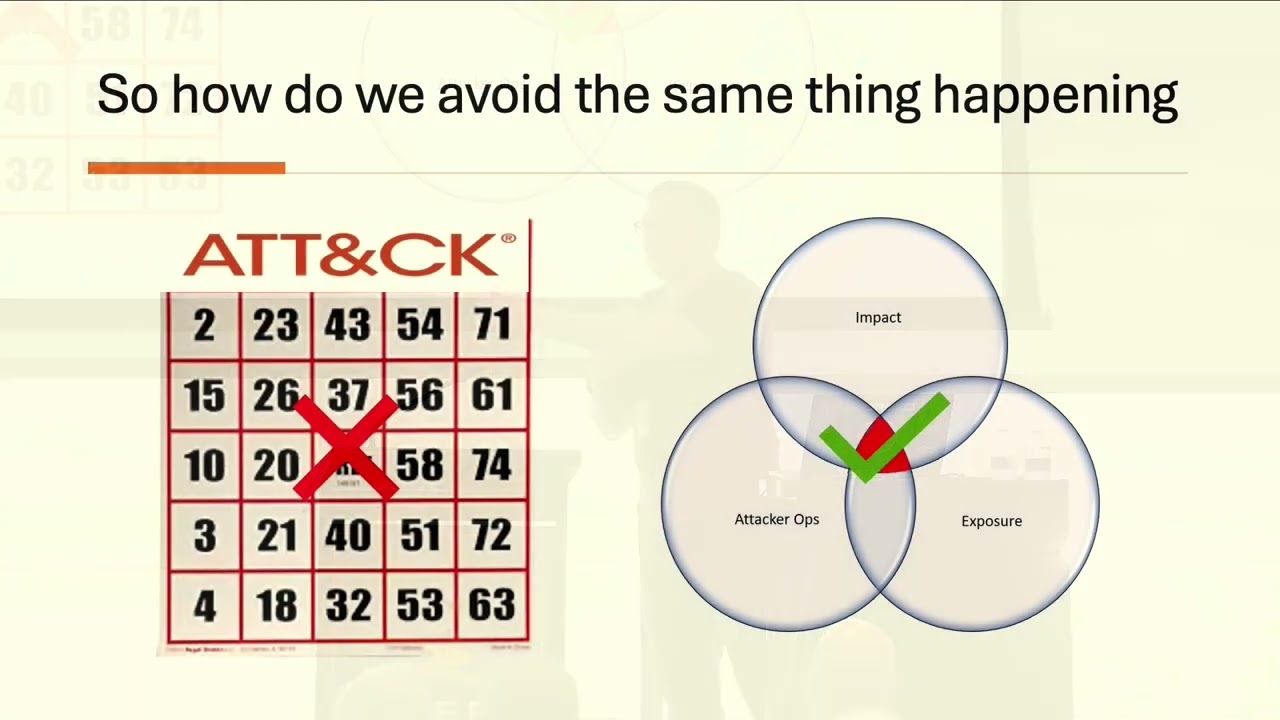
they have their proactive controls so when I gave this talk before people would say well I don't have a web app so what where do I go to find my threats well there's a really really really good document that is published I will have the resources and the in the last slide it's called Dodd car which is the DoD cybersecurity architecture review and they've worked with the mitre attack framework and basically given you a the landscape of what they consider the most prolific threat sources available today for your advanced persistent threats so it's broken down into stages objectives and actions and as you can see there quite a number of threats or ways folks can can external trade data or do other
demand damage so in that document you'll see they'll have what they have a heat map and a coverage map so the the heat map is actually based on observed activities by it the NSA so the darker the color the more prevalent they've seen it in the wild so if you look up here for engage phase two spear phishing emails those never work right so that obviously they do work because they see them all the time I also see web sites vulnerabilities and your web sites right so these are the the things that if maybe you're not developing software but rather you're a systems engineer or an architect you could use this as your source of threat for what things you
need to mitigate so and then we have the coverage map so that was observed this is based on a bunch of smees in a room evaluating against protect detect respond from the cyber security framework so they'll go through the exact same boxes as you saw on the other page but they will bunch of smart people got in a room and threw numbers out basically what happened right and now the the higher the numbers so obviously right is something you should consider and green may be something you can push off to later so in summary familiarize yourself threat sources you can either use the OAuth top 10 you can use Dodd car you can use a combination
of both create your data flow diagram using the four shapes of stride define your risk measurement criteria from from octave Allegro so that you can prioritize them properly complete your worksheets again I just used Excel calculate your scores sort rank identify industry standard mitigations do not roll your own and then practice it's going to take you a while to get good at this I mean it is difficult when you just first come in and look at a data flow diagram and try to make sense of all the threats that is partially why I have that statement is there a threat of a threat actor because that will help you scope your work and with that I
think that is it so there here are the resources so obviously OWASP Dodd Khan and NSA threat framework v2 or at the bottom there they're pretty good reads especially for technical folks you may consider things that you hadn't considered before when you're writing software or building out your cloud is or what have you and with that any questions no I'll be walking around around so if you have any questions you want to do one on one that's fine again I encourage you at 4 o'clock to go to Justin Forbes talk on how to frustrate a pen tester he's pretty good at it so I think you'll enjoy that as well so thank you very much
[Applause]