The Security Practitioner's Guide to Going from "No" to "Whoa"

Show original YouTube description
Show transcript [en]
all right i think we should get started what do you think josh let's do it i'm excited hopefully everyone's energized it's day two and it's the afternoon and if i'm not mistaken we're all kind of coming off lunch but uh let's let's let's hope the audience is energized so uh we're glad to have you here and uh we're we're doing our first kind of team presentation josh and i but i'm going to turn it over and let josh kick it off i believe right i i mean i'm happy to kick it off hey everybody i'm jeff stokel i am here to talk to you guys today along with my buddy john about the security practitioner's guide to going from no to
whoa and the whole idea of this presentation was we're going from no because you're not on the same page to whoa where we're starting to talk with management and they're actually understanding what we're saying um you know leadership is constantly telling us now as security practitioners uh but it's because you aren't communicating in their language which is the language of business and security issues are often seen by practitioners as binary uh you know is it an emergency will it happen won't happen that kind of thing and so the idea behind this presentation uh what john and i are going to talk to you guys today is how do we go from that state where hey we're being told no all the
time to a state where management actually looks at what we're doing as a value add to the business uh and you know we're in a much better position as security practitioners because they're actually listening to what we have to say that's right and to get started i'll introduce myself briefly my name is john overbaugh i'm the chief information security officer for alpine software group we're sort of a private equity company that purchases and runs a number of companies in different verticals i've been in information security since 2012 most of that time in healthcare and really have had a lot of opportunity to learn how to social engineer leadership and that essentially is what we're going
to talk about today awesome and i'm josh sokol i'm i used to run the information security program for a big 1.6 billion a year publicly trade organization called national instruments i did that for about a decade uh and then eventually i moved into a role as ceo and cesa simporis and uh simpers is a free open source uh enterprise risk management tool i actually when i was working at ni my bb came to me one day and she said josh i heard about this risk management thing can you figure it out for me i said yeah i can do that i did a lot of research i came across the nist 800-30 framework for risk management i said this is what i
want my program to look like but the piece i struggled with was the tool set i started off using excel spreadsheets quickly realized that they wouldn't scale i used a homegrown lowest notes database for a little bit and wasn't dynamic enough and then i started looking at the big grc suites that are out there um eventually i got to the point where i couldn't afford the big grc suites the excel stuff wasn't going to scale for me and so i ended up writing something i ended up releasing that thing that i wrote free and open source for the security community uh and that is simple as so today we're going to talk to you guys a little bit more
about kind of what goes on behind the scenes there we'll talk about the management stuff and whatnot but before we get into that let's talk about the atlas cinder uh the atlas syndrome is the no it's the the idea that we are putting all this weight on our shoulders so take a moment think about all the security tools that are currently seeing in your arsenal all the different things that are out there how many are there five ten is there more than that once you have that number in your head i want you guys to think about uh the the alerts the things like that they're coming from your nga v the evr the firewalls the scene right
now in terms of those alerts uh sc media did a survey back in 2018 and they said that 55 of enterprises see more than 10 000 alerts per day and 27 saw more than a million alerts per day that's a crazy number when you start to think of it and maybe you guys are seeing that same kind of thing and de misto in 2018 did a state of sword report where they said security teams were were bombarded with a hundred and seven right there we go sorry i i was getting a different presentation coming in over me i was like this is super weird and i just closed the process um so uh that soar report basically said
that the security teams were bombarded with 174 000 alerts per week um and averaged about 25 000 per day so regardless of the source we know that our security teams are up against a constant barrage of alerts now since we know about all these different alerts uh when i was at ni we had about a hundred thousand vulnerabilities that were found by our skin and all those different vulnerabilities that were found were waiting to be triaged so if you think about it this was me every platform that i learned every vulnerability that was found these were my burdens to bear and in short this was me i i'd have panic attacks thinking about all the what-if scenarios
i sometimes had trouble sleeping at night thinking about which would be the nail in my coffin can any of you guys relate to this john do you relate to this absolutely i mean josh having been in information security for over over 10 years now this is what we deal with day in and day out is that heavy weight on our shoulders of knowing everything that's going wrong knowing where all the skeletons are knowing what's going bump in the night and it is it literally can be physically taxing like no joke but also it's something that hampers us in our performance in our professional advancement and and the success that we have in work if we don't figure out how to manage it
and get through it absolutely no i'm guessing the rest of you guys feel that same way as well and what we're going to talk about today is kind of what we do about that john's going to cover that a little bit more the other issue that we run into the thing that we see very frequently is what we call the chicken little effect and we see practitioners going this route all the time the idea here is that with every new issue discovered the sky is falling right every issue that we find is the worst issue possible there's no prioritization there's no way to discern which thing is the most important thing to work on and ends up
becoming a constant distraction from work which pays the bills right and that's a big issue there so what happens all right well what if i told you that eventually management is going to start to ignore you you're going to get used to hearing the word no right over and over again because you're now seeing you're being seen as an inhibitor to the business so this is your last chance after this there's no turning back you can take this blue pill and the story ends you guys can go back to work you can continue to feel like atlas you can bemoan your fellow security practitioners about how you're constantly be being told no or you can take the red pill you can stay
in wonderland john and i are going to show you how deep this rabbit hole goes and remember what we're offering here is the truth and nothing more right very matrixy but you get the idea you can pick that red pill you're going to go back to the same old way the same binary approach the same atlas syndrome or you can listen to us and find a new way to approach it which is the non-binary way and so i'm going to let john kind take it from here sure thing say thanks josh so we're we're presenting an alternative approach instead of the chicken little atlas syndrome approach we're pretty presenting a new approach to information security management the foundation of
that is an entirely new perspective that security leadership's responsibility really is to define assess and contextualize while reporting so the key here is that we have to understand our role as security practitioners and most important in understanding that role is that we are not the risk owners we are risk discoverers and we help teams to understand and respond to or treat that risk so let's jump ahead one more slide here and we want to talk about how we do that well look our companies trust us to conduct risk assessments or maybe the better word is they interest us to conduct risk assessments we start by proposing and working for agreement on a list of controls or on a
control framework and then we analyze against those frameworks when we're there to serve the business and to support them in improving security by helping them ensure they're adhering in our compliance to those frameworks to accomplish all of this our program has to be written down and approved by senior management now there's an interesting kind of side conversation that you and i had here john which is this idea of auditors right that now that we've got our framework the auditors are going to come in they're going to say hey you know these are the things that you should do and i i had this happen to me when i was at ni where they said hey um
here's the checklist do you do this and i'd say yes check that off and then they'd say do you do this and they i'd be like no and they'd check that off right yeah and i ended up writing a blog post about this that called auditors don't understand security the whole idea is that this checklist approach to risk management just doesn't work right the idea of risk assessment via checklist what are your thoughts on that well that's that's a good question i want to actually drill down a little further into this risk management framework and talk more about it and by the way this risk management framework should not be new to anyone this is what we do all day
long and it's a more visual way of looking at what we do as leaders we run parts of the company through a traditional risk management framework or a process what's important in all of this is that the new phase i've added on there the document phase right it's important to provide a clear definition of done for a given control otherwise the business runs out of patience with us or because the definition of done is not clear they always say yeah yeah we've got that we've got that so our program can either be unclear and frustrating to our business customers or our program can be ineffective a paper tiger at best so by having this solid framework where
we document our controls and then we assess prioritize plan and tractor remediation vulnerabilities this is a better approach to um to to completing that cycle now josh i want you to tell me a little story about about the last time you did a road mapping exercise yeah absolutely so you know back when i worked at national instruments uh my management kept coming to me and they said josh when is this going to be done when are you done when does security stop and you know the the funny thing about this is we all know security practitioners it never stops right there's always the goal posts are constantly moving uh because our threats our adversaries are constantly changing
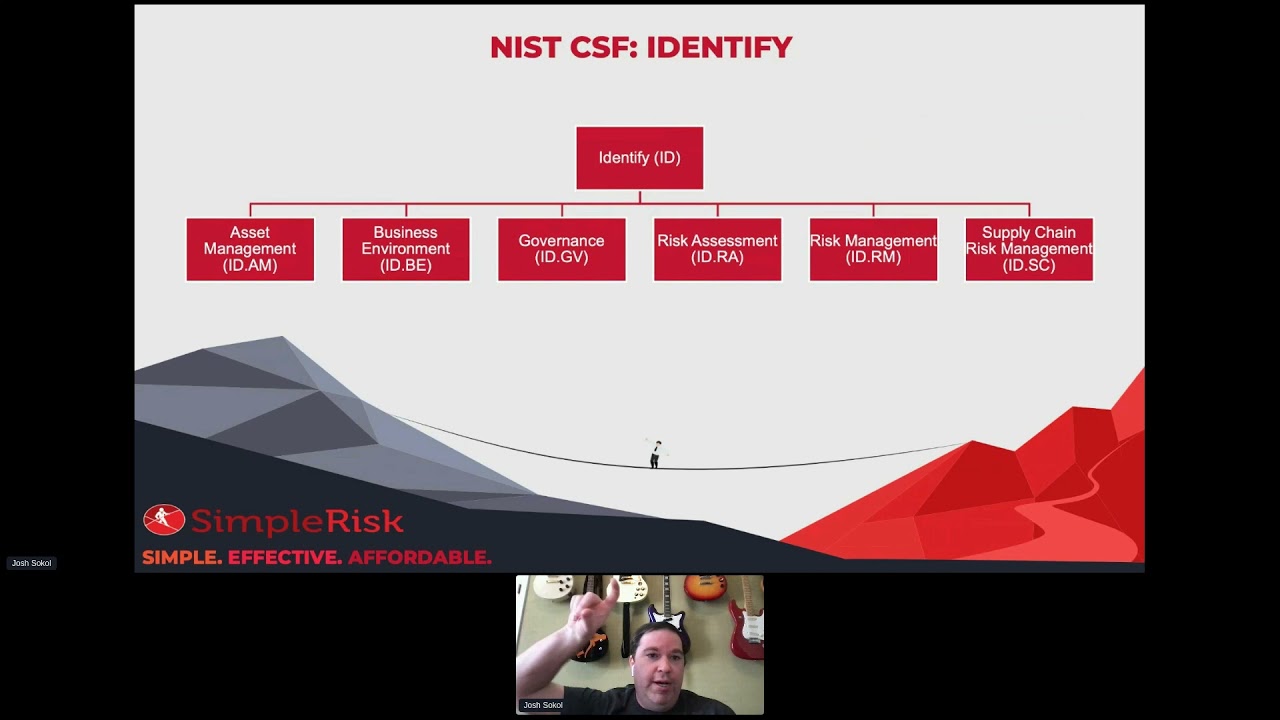
their approach um so i did this exercise i took the nist cyber security framework and went through it and for each individual item in there i said this is where we're at today and this is where i want to get to basically you know a an assessment of our state and what we looked at for that was the difference between that um you know if there was a big gap that's a big risk if it's a small gap it's a small risk but at the end of the day we were able to basically take this uh exercise that we did and turn it into a road map for our organization we could say that hey if i
bridge this gap now we're in the place that we need to be in order to to move our organization forward and the key is to get to that bar josh like you said right so there's there's an assessment of where we are today versus where we want to be and what's important is making sure that senior management is on board with where we want to be once we have agreement there then we can define those gaps we're not the owners of those gaps we're not the bad guys that are bringing bad news our job is to observe and we can now answer that question when does this stop well it stops when we meet the bar that was
set by leadership which leadership approved then we we go to work on it now the key is that we work with leadership we start because we're security experts we're the ones that really know what what the right controls are so we'll sit down come up with those controls propose them to senior leadership help them understand the pros and cons of either meeting or deviating from that particular control and eventually we reach that conclusion so part of our job here is to build consensus now go ahead josh do you have something you want to say i was just going to say you know one thing that i wanted to key in on there is what you said this is a proposal
we're telling management right this is what we'd like to see but we're not deciding as security practitioners we're not the decision makers because we all know the people the budget things like that yeah that's right yeah as i mean as a ciso for instance my job is very different from what it was you know 10 10 years ago as a director of security today my job is to sit with senior leaders in the company and talk from a strategic perspective about risk talk about what the appropriate control frameworks might look like and talk about the business problems that we're facing that might prevent us from implementing those so it is very much a conversation that we have to have at the
leadership level now josh you know i get asked a lot um either within my organizations but often uh uh outside of organizations by by the way i'm really active on linkedin um you can follow me there or uh you know connect with me i'm also pretty active on reddit um a little more anonymously but still same idea i talk a lot about leadership and about security and one of the controversial things i always tell people is i don't care if you have policies or procedures in place i want to see an incident response plan first and there are a lot of people who say no no you can't do that you have to have a
policy to dictate your procedure or you can't move forward right so some people really assert that we have to have policy and procedure first others say we have to have controls and it's an age-old argument but what's interesting about this argument is it's actually a trick question right um we need policy and procedure we need controls pretty much at the same time if you want to pop to the next slide josh pretty much at the same time and as we develop one it will feed off the other and we'll be going back and forth oh sorry i skipped a head one didn't i um we'll be uh we'll be we'll be flipping back and forth so
just in this approach where we're talking about you know we want to go to senior leadership with a control set well we have to have a policy first they're going to inform one another you're going to write these together if they don't exist today you're going to modify them together if they are in place today that's the important thing so both of them come first and so the real question here is what is our responsibility so really to summarize what we're talking about senior leadership's responsibility rests in identifying and communicating where the risk is that is what a strong risk management program does and then we define the associated processes to correct that program how do we track what decisions are being
made and who's making these decisions is another thing we need to tackle when we have that tackle what we're doing now is we are we're setting a bar we're identifying gaps between where we are today and where that bar is then we're we're sharing those gaps with the actual owners of them and then we're also collecting from them their plan to remediate that all along senior management is informed they understand from a metrics perspective as well as an anecdotal perspective where we stand the business may start fighting us on this because what we're doing is we're we're ridding ourselves of the atlas syndrome we're taking that big ball of responsibility for the security work picking it up
dividing it and placing it on the shoulders of the business owners who have agreed to the agreed to the controls but have the control gaps and are responsible for the remediation by the way the business might really fight you the first time you try to document their decision not not to fix something but that's okay those conversations are what we need to have and i actually want to talk briefly about that what if they say no so i want to put in your mind this idea that we don't have all of the context of what's going on in the business we don't understand everything around what our executives are making and the issues that they're facing and honestly
sometimes it's probably better not to know it's not that leaders don't value security although i will admit there are some who do not but rather that in the context of everything else that information security vulnerability we're talking about that may not be the priority right so for instance as a startup company we may be so so small and have such small revenue that the decision is either we add new features gain new revenue or we go out of business and we don't really have the luxury of addressing some of that security stuff we have to take a risk because otherwise we're threatening the very existence of the company this is where you as the security leader
really define yourself you can complain or whine and say my you know my cso is an idiot my ceo is a jerk whatever you want to say or you can accept the answer and come up with an alternative that might help compensate or mitigate the risk and it may not be a full mitigation but it might help to reduce the risk to an acceptable level the key takeaway i want you to have here is that no is not a terminus it's a junction the successful leaders in business today in information security are those who look at noah as an opportunity to get to yes that is the most important characteristic we can have now we want to be able to take all of this
information and bring it together and get to yes on the right things we want to be able to filter our highest risks to the top so we can have good effective conversations about those and and deal with those sooner the challenge is how do we do that how do we bring all of our risks together how do we understand what appropriate mitigations are for those risks how do we document the decisions that we have made and how do we ensure that senior management is buying off on those decisions and we can literally prove that they made that decision well now we need tools and as josh pointed out earlier probably the tools we have today aren't enough so josh i want you
to take a few minutes and talk more about that yeah absolutely um so when it comes to tools for uh risk management um you know we need good tools uh that enable information security leadership by creating a strong governance foundation we need those frameworks that john talked about we need to develop a strong risk management process something that's easy to understand something that's easy to follow identifying and communicating this risk is where the strong risk management program the associated processes come into play and so this is how we end up getting rid of that atlas syndrome um additionally enforcing separate roles for risk assessment conveyancing acceptance and then you know lastly enabling the business to
make informed risk-based decisions and that really is going to be the key thing here our business is the ones making the the decisions and that's going to be a theme kind throughout this presentation now have you guys ever seen a spreadsheet like this these are my favorites oh yeah i mean i i lived these when i was at ni i've seen dozens of templates like this online you know if you search risk management template this is what you come back with and so you know i've lived this the issue with templates though or spreadsheets um is this you know you you can try doing risk management excel it's generally available to you there's no additional
cost but it comes with a lot of challenges the first one here is spreadsheets don't scale you know you have a spreadsheet with a dozen risks for a single team it might be manageable but one with hundreds or thousands of risks across multiple teams it just becomes unwieldy um having multiple people editing the same spreadsheet uh at the same time that's a recipe for disaster and worse how do you maintain an enterprise approach to risk management while ensuring that one team doesn't see another team's risk the second one here is a spreadsheet just isn't a database right you can do pivot tables in excel you can use fancy formulas but joining data from distinct tables is difficult if not impossible to
do in an excel spreadsheet uh in something like sim course database queries can sometimes span a dozen or more tables which takes a fraction fraction of a second uh when it comes to a database uh there's simply no substitute for the efficiency and scale of a database when you're joining multiple distinct sets of data um and then the last one here spreadsheets require maintenance um anybody who tells you otherwise is just you know flat out wrong or they haven't used a spreadsheet um those who fall into the spreadsheet-based first approach to risk management they'll typically spend just as much time tweaking their spreadsheet and messing around with their formulas as they do actually managing risk and remember
again i started out doing risk management with spreadsheets right i've been there um each new report is going to require a substantial investment of time to create and it really just ends up being a waste of resources that are far better utilized elsewhere in your organization now once i realized that my spreadsheets wouldn't work i used a homegrown lowest notes database to do risk management you can do this you can do a diy approach try and write yourself um you end up spending countless wasted hours on development instead of doing risk management which is what we're trying to do and you know when the reality is is that most of us risk management is this
much of our overall responsibility and we've got so much else i would play if you're spending that time trying to write a tool maybe it's not spent in the best place um especially if you're not a developer man you got problems there um so yeah john tell us about the ideal solution well you know so what's interesting is the first half of my career i spent in product groups building software at microsoft and uh was very familiar with the tools that we used internally to identify track and remediate bugs defects in our software then you know fast forward i'm in information security and um both as a practitioner as a director um in over multiple groups and then also as a
consultant with numerous customers all i had in my hands was was an excel spreadsheet and you know i just didn't have the tool set that i needed to get the job done i needed to be just as effective at managing thousands of risks across multiple teams as i would be with 10 risks i also needed to allow multiple people to work in in my solution and in fact my first role as a v as a vice president as a vp i had i had seven members on my team and they were all responsible for identifying risks and the spreadsheets that we had just weren't keeping up with it finally i needed to be able to report
easily across multiple data sets for different customers and i needed to be able to spend my time um working on risk not on the tool i like to tell my teams all the time that look the tool is there for us we're not there for the tool uh and so you know um and we don't want this to sound like it's a sales pitch but i was thrilled to come across simple risks so as josh mentioned i started looking for risk management grc tools grc solutions they're very high priced they take a long time to stand up and they they require a pretty heavy uh commitment we on on one of my teams stumbled across
simple risk and i thought it might have be too good to be true so first of all it was free and open source if i wanted um there was also a paid commercial version of it and so you know what really helped me was finding this solution playing with a little bit uh just doing some scenarios and realizing holy cow i can bring all my risks in one place i can start to propose solutions to those risks i can track agreement on whether or not the solutions will be accepted and i can track that risk to completion so today what we're going to do is we're going to walk through the risk management process we're actually going to do it real time
we're going to use simple risk not because we're trying to sell it to you it's free but because it does a great job of demonstrating all of the phases of risk management and again in the end what we're trying to do here is take responsibility for fixing vulnerabilities off of our shoulders and placing it upon the shoulders of the business owners the people who actually can fix the risk so let's let's dive in here josh and let's walk through it yeah absolutely so the first piece that we talked about was creating this strong governance foundation through the control frameworks and even in simplest core there's kind of two different ways to go about doing this you can manually add
your own frameworks manually add your controls into there um but my personal preference is leveraging what's called the compliance forge secure controls framework uh this is a free thing you can download from securecontrolsframework.com uh they'll give it to you as an excel spreadsheet but what they've done is they've taken about a thousand uh security and privacy related controls and they've mapped them across 185 different frameworks so things like nist oh so pci dss hipaa gdpr you name it all these different frameworks are all mapped in here and what you end up getting with this is kind of this uh if you're a fan of lord of the rings like the one ring to rule them all approach you you basically have
like this one control set but it applies across the board and the huge advantage to this is when it comes to your compliance when it comes to actually testing these controls you test the control once and it applies in all those different locations so that mapping is huge um yep this is this is what i love if i can interrupt briefly this is what i love about having a control set and the ability to map controls to various frameworks it allows me to customize my controls for my organizations uh the company i work for we own 45 different companies we have very different security needs at each company some of them are in behavioral health which
means they're under the united states hipaa laws some of them are um under pci and other data data protection laws but what's what's important here is i have a common set of controls mapped to different frameworks what also helps me is i can map controls to my customer contractual commitments so josh like you said i may have i may be in a hipaa regulated environment i might have 15 customers that give me a very definitive list of security controls that i have to have in place what i can do is map all of those to my existing control framework then i audit once and i can report multiple times that's right yeah um the other interesting thing here
and this kind of drives back to what we were talking about with the um the csf exercise that i did where i said here's where i'm at today here's where i want to get to is we can use any control framework really to do the same kind of exercise so we can say you know with this example this is gogo one and compliance forge you know my current level of maturity is performed my desired state is managed and so now we have that gap and within simphours we can go uh there's a cool report called the control gap analysis report um that i built based on the what i presented to my management um and it's gonna show me
it's gonna show me here's where i'm at today here's where i wanna get to with each of those different control families so i can see i'm doing well at asset management i'm not doing very well at uh secure engineering and architecture and you know josh there's one thing i really like about this graph and first of all we're all going to have a little laugh about this right because we all know that executives want pictures and you know i used to joke about it but actually honestly there's no better way to communicate the status of 250 control sets than a graph like this so the key on this graph is that the black line is the predefined agreed upon maturity
level that we want to reach as a company we've selected these controls in each of these areas and said senior leadership says this is where we need to be the blue line shows where we actually are today i can put this control down in front of a ceo and within about 10 seconds that ceo understands i need to make investments here and i'm cruising well here yeah and to put in the language that you used earlier it's the bar right the black line the desired state is the bar that we've agreed upon to me and so in any of these areas where i'm not meeting that bar that means that we have something explained to do this is what
we're going to do to guess that point and when we're not meeting that bar that's what we call risks and we want to go through a common risk management framework and the one that you've developed in simple risk is based on the nist 830 framework so josh why don't you walk us through that a little bit yeah that's absolutely right so you know the second item that we talked about was developing that strong risk management process but i think the more important thing here is that it needs to be easy to understand and follow um the reality is is that you know a lot of the people who are going to be entering risks in your organization
they're not risk practitioners they're not risk experts they're the use guy who discovered a unencrypted ssh key while messing around on a system right those are the people who are going to be interacting with this so you know the process that miss gives us is pretty simple it says hey you need to be able to spit your risk keep a registry of all the risks in the organization talks about plan mitigations what are we going to do to address these risks john you and i had a conversation earlier that maybe we should change that to treatment because we're not necessarily going to mitigate everything right we might transfer the race we might decide to research or to
watch uh the next step is the accepting the mitigation so this is where we start to look at hey this person said we should do this yeah that sounds good let's go ahead and do that and then in my opinion the most important piece here is going to be the management review this is the piece that gets the weight of the world off of your shoulders as the security guy this is where we say hey management here's the risk these are all the risks in our registry here's what we think that we should do about it do you agree is this the bar that we want to hold ourselves to and when management says yes we should cool they
are now empowering us to make these make these changes right it might not be us making those changes it's the business that's doing this uh if they say no if they say no we're not willing to do this then like john talked about earlier we might lack the context we don't know that the business has you know a thousand dollars left in the bank and can't make payroll this month right there may be some very valid reasons why they're making this decision not to it's not our place to question that but it is our place to make sure that decision is documented uh because that's what gets that monkey off of our back and then the last piece here is the
review regularly so risk management is a cyclical process we don't just do it once and forget about it uh we need to make sure that we're re-reviewing our regular basis because frankly risk changes you know you have a cve that's introduced uh well let's start off with an oday that was introduced a week ago right that oday is huge it's uh somebody's automated it's compromising systems uh all of a sudden we have a cve we have a patch in place the risk goes down right so risk is constantly changing and we need to reevaluate those risks in order to do that yep yep now one of the things i love about using a tool like simple risk
is uh well let's step back if you consider tracking risks in excel how do you do it you have a you have an excel uh ply a worksheet in a workbook and you have columns for title and for owner and so on and so forth and really not a lot of context to help you fill it out you could pre-populate some of the columns by using you know a pick list and so forth but that's just work to build the worksheet so so what really has helped kind of move the lever for me and my experience using uh simple risk is that now i can track risks just like i use jira to track my defects and that
metaphor really um it it gels well with our development team so a very simple risk management workflow is something we have to have it this system has to present it to users in a simple and intuitive way to allow users to submit the risks themselves and you can see here this tab that we're showing is how i collect data about the risks across my 45 companies um and you know i allow those individuals and those companies to create those risks what's really nice about this is that there's there's a framework in here for rating your risk and you can use any framework you're comfortable with if it's dread if it's stride if it's the common um you know impact times
likelihood if it's the owasp risk score if it's a cvss you can pick whatever you want to do put it in here and as josh is going to demonstrate in just a second that risk score is normalized across all risks no matter how the score has been entered it's the same score across all risk which allow you to compare risks with one another so josh why don't you take that that tab and talk a little bit more about that yeah absolutely so you know the idea is that we're able to go and we're able to say hey if this is the likelihood of an issue and this is the impact here's the risk score so we can use that kind of
classic risk methodology that you learned on your cissp um but as john said you know you've got things like oauth first-rate methodology so if you find a sql injection vulnerability you might want to capture it that way uh if you find the latest log for shell vulnerability you might go through a cvss corn because that's a cve that you can capture so really this is just a matter of documenting the decisions that we're making and the process that we use to get to that point no okay but josh i'm gonna interrupt all right all right this is not a 10. all right fair enough john this is how many times do i have to tell you not every risk is attended
well you you've told me enough times for me to know better for sure um you know you're absolutely right so this risk right here it says that it's a 10. um but the interesting thing is that a 10 uh is um it's subjective right if i am the information security person and this is a risk the system is going to get compromised in my world within my purview that's a 10. right but as soon as we go outside of my purview now we're talking i t is that still 10 that one system getting compromised is that still 10 probably not when we're talking the it realm of things it's probably my data center is offline that's probably a 10 in the it
world okay but let's take a step back and let's say all right for the enterprise is the data center going offline is that the 10 or is it the fact that we we've lost all of our customers you know is that the real town or the fact that employee died right is that the town so when we're looking at these risks you're absolutely right john we have to keep the context uh in mind and we have to kind of baseline this and say is this a 10 for me or is this the 10 for the enterprise and that's what's nice about the way we can enter risks and modify them in simple risk or any other good jrc tool
for that matter they can be entered by someone and we can triage them and sort of override that and record our decision so every time i tweak a risk i will document it in the notes field so what's interesting here is let's assume we've generated the risk we've created it somehow we agree it really is a 10. we have the opportunity now to talk about treatment how are we going to deal with this risk and we all know that there's a standard formula right there's like five things we do we can accept it we can transfer it with with insurance we can fix it we can uh what else can we do we can reject it by just turning that
system off lots of different options we can capture those as a proposal here in simple risk yeah and so this is this is the mitigation page right this is where we are deciding here's what we're going to do next what's that strategy look like do i accept transfer whatever but probably more importantly is we're deciding what we're going to do here so you look at the current solution this is where we're at today this is what we're doing there may be some controls in place right now we start to look at the requirements these are the things we have to do and then the recommendations these are probably the things that we should do and then you'll notice
just really quick josh this is the definition of done so i won't let a a risk owner um review a risk or i want to let a risk get to a risk owner without defining the definition of done for them so it's very very clear what they have to do to fix this risk yeah it's the bar it's when we meet this bar we can say that we're good who are here we've achieved that level and kind to that point you have that may gain controls along the bottom there where i can say hey these are the controls we need to have in place in order to fully mitigate this risk [Music] now next do you want me to take this sorry yeah
go forward okay i'll take this one so next step that happens we've we've found a risk we've come up with a proposed mitigation or a proposed treatment for the risk now what we do is we take this to senior management and we perform a review senior management sits down generally um you know maybe not at a at the risk committee level but at the risk you know whoever on the senior leadership team owns risks in some cases that might be the cso if the cso's dialed in enough to business challenges and solutions they may be the one making those decisions but regardless we sit down with them and we go through these risks and that
senior leader has the opportunity to say yes or no this is what i want to do this i don't want to do this and so forth and we capture it on record and what's neat is a good flexible risk system is flexible enough to allow different individuals to capture and go on record for how they're going to handle different risks based primarily on the risk and the impact to the to the company so josh you want to show us that yeah so when i was at national instruments one of the things that i started looking at was the rest of my organization i started to get this kind of registry of all the different risks
out there and it looked kind of like this it was a pyramid and i had a lot of stuff on the bottom and i had not so much stuff on the top right and most of your risks are going to look something like this for most of our organizations well i started thinking about this and the other thing that looked like a pyramid was my management i i had you know my ceo and then my presence and my vps and whatnot and so when i started looking at how to to kind of put my program together well what i said was all right why don't i say that my managers they have the ability to review
the insignificant low level risk these are things that they have the money the people to be able to address within their purview and then i started looking at the section managers and i said hey you guys you'll do medium level risk because you have a little bit bigger budget and more personnel and then the uh vps you know or the directors they would do the high level risk might be she would do the hot the very high level risk and so what i found was i could build the visibility and the accountability into the chain of management i could basically assign the review of the different risk levels based on where you were in the
management chain i ended up being hugely effective now there's going to be permissions for other things in here too we can decide who can create risks who can modify risk things like that uh we can determine who can plan mitigations who can accept them uh and things like that so lots of permissions need to be built in the system and this is where we start moving light years away from our spreadsheets because we couldn't do this at all when it came to the spreadsheet yep i mean it mirrors another business process which is the uh the budget approval process right low level managers can approve so much spend medium level managers so much spend so
on and so forth same thing around risk lower level managers are allowed to take a certain amount of risk on and as you move up the uh the seniority chain you are allowed to or welcome to or invited to or responsible to take on more risk yeah so let's take a second and let's move on and let's talk about the informed decision making how do we actually decide which risk we're going to fix which risk we're going to ignore for the time being and the answer is reporting and this again is getting away from those spreadsheets we need to enable the business to make those informed risk-based decisions and there's a few different ways that we can kind of do
that um traditionally we look at the the highest level risk in the organization we point to that thing that's the very worst thing in our organization and we say that's the thing i should fix perks and without any other contacts that may very well be the case but when you start to pull in the context piece you may realize that that might not be the most important thing or it might be not be the one to fix first maybe the level of effort uh is you know it's gonna cost us a million dollars to fix a risk that might cost us half a million dollars should we fix that risk probably not right but it all we need
that context now the other thing that we can do is we can look at uh the the level of appetite so every organization your level of appetite is going to be completely different uh and you'll say hey uh usually when you start you're gonna be like well we got a lot of tanks right so my level of appetite is gonna be really really high because i just don't have the time to deal with anything that's underneath that okay josh let me let me just interject really quickly here level of appetite or risk appetite here is the level of risk you're comfortable operating in so you risk tolerance if there's a one most of us don't care about the ones
right they're just sort of annoying gnats uh tens like those are the rhinoceroses that are trumping through our camp so companies generally are somewhere in between a one and a ten in their risk appetite and as josh is indicating you know that will change over time as well but i just wanted to call that out yeah that's that's a great point now um you know when we're making our decisions we're probably if we're using this kind of higher level risk we're going to start off looking at those really big ones and then we'll work our way down so your appetite will actually change over time it's going to start off being super high but as you
start to eliminate a lot of the the high level stuff your appetizer can get smaller and smaller and smaller because you've actually fixed a lot of these issues now the other thing that we can do here is we can look at that level of effort now this is when we start to look at contacts and so we can look at the mitigation if we said the mitigation for this is trivial uh but it's a 10 risk score that's my low-hanging fruit that's the thing that i should attack first because that's where i'm gonna get the most bang for my buck whereas you know if i have something that's gonna be a significant amount of effort but is you
know one level risk i probably should save that one towards the end now the other thing that we can do here is we can look at the controls we talked about the controls um and so when we're making decisions we can look at this control and we can say all right look at all of the risks that are tied to this particular control there's a lot of risks here if this control fails for any reason what does my organization look like now and now we can start to talk about defense and death should i add an additional control in place because you know if this control fails i don't have anything to compensate for that um and
so this can help us to identify where those gaps may be or where we're relying too heavily on a single point of value the key here is that there is flexibility in how we present and analyze our risk uh through different um different pivots right pivoting off controls pivoting off cost pivoting off overall risk and appetite and so forth so that flexibility allows us to do a couple of things number one we can examine things in different ways and derive kind of a consensus opinion based on those multiple approaches number two we may have a leader who has a specific agenda or specific responsibilities and we want to pivot and show them risks related to their
responsibility so that flexibility is key and critical for us in that risk management discussion so look i want to step back here and just kind of wrap up where we've been and what we've been done so we started out talking about the atlas syndrome right carrying the weight on our shoulders because we have these lists on our desktop full of risks we know so much about this organization it's overwhelming and we've talked about now how to how to move that conversation from oh my gosh this patch isn't in place we've got to stop everything and do it we want to move our conversation from that to a conversation about risk and talk about risk in terms of relative
risk business risk and risk ownership when we make this adjustment right so again we've we've uh eschewed the blue pill and we've taken the red pill we're changing the way we talk no longer we speaking binary we're speaking on a scale of one to ten and we're speaking about the actual owners of the risk now we give management the context that needs to make informed decisions about treating risk and we have a platform to communicate it across the business this is revolutionary because um you know for me i started my career with fear uncertainty and doubt and it got me so far not very far but it got me so far i had a few things fixed but what was
interesting is i kept uncovering more stuff and eventually i asked myself what's the definition of done here and realized the approach i was taking i was burning you know i only had a few tickets here to share and i was burning them pretty quickly and so i knew i had to change what i was doing and that's where i stopped dropped back and started to look at more of a risk-based formula and more of an indexed approach by tackling this approach the other thing i was able to do was finally put responsibility for risk where it belongs if i don't own the tool if i can't deploy the patch myself i don't own the risk and i need to find
a way to communicate that as a cso but also i needed that as a director as a vp and as a consultant ownership of risk is what we're really talking about here ownership and relative measuring and a good solid grc solution helps us get there now we've talked a lot about simple risk today not because it's a sales pitch but because it's a great tool that really helps us get our job done i highly recommend you take a look at it josh josh's team has a bunch of videos out there how to use it but for me it really was revolutionary it allowed me to put all my data in one place pivot on it and really communicate
and assign ownership so i appreciate josh and the work that he's done to produce simple risk but i also appreciate the the progress that i've made because of my risk-based communication awesome uh well very cool so uh that kind of wraps our presentation for today um we'll go into the chat and see uh what questions there i see one uh right now from ricky uh so ricky asked us in performing remediation and mitigation why not revisiting the impact and likelihood instead of the percentage uh so you absolutely can uh when it comes to inherent risk score you can certainly reevaluate the impact and the likelihood and we didn't show it in this presentation but there is a risk scoring
history and the system will trap that so if you actually change the likelihood or the impact of the risk itself um you're going to be able to reflect that now the reason why i went with the mitigation it's simple i my whole goal when i was designing simple risk was simplicity i wanted to keep in mind that there's a lot of people in my organization that did not understand uh they had a mandate to do risk management but that wasn't their job right and so when it came to that i could be like hey when you applied this particular control how effective was it and it could go um i feel like it was twenty percent
effective then go boom 20 right that was the kind of approach that i was taking when when i went for the mitigation percent now we do have an item on the roadmap to be able to apply uh likely an impact to the residual risk as well um but honestly i feel like the fact that you can do that to the internet risk or that you can do a mitigation percent um it kind of gives you the same value i in much simpler format so you know just to kind of to dog pile on that i actually do both so i'll all i'll create a risk sometimes one of the nice things about simple risk is i can actually generate a
questionnaire and when i'm creating the questionnaire i can tell simple risk if the answer to this question is no open a risk automatically so i don't have to sit there and hand type all my risks in but but what happens sometimes is you know you don't have context so i just pick okay in general this controls probably a four or a seven or whatever once that risk is auto generated i will sit down with a risk owner and we'll talk about it and we'll discuss what's really going on in the risk assessment and notes fields i'll capture that information and then i'll probably tweet the risk score in fact i spent an hour with a ceo this morning going over that
very same exercise where we tweaked risk scores and then as josh said when i throw a control in place if i haven't completely mitigated the risk i want to know that if i've only brought my risk score down by 20 then my risk may have gone from a 10 to an eight um that's good there's control in place but i haven't dealt with it all so both both approaches are necessary and josh my screen's a long ways away from me because the way i set things up so i'm going to have you read the questions and we can go back and forth answering them yeah i i don't see any other questions right now um i think
ricky's was the last one that was up there so all right i know we're we're sitting about 10 seconds behind uh them so maybe somebody's thinking of some amazing question to ask or maybe john you and i were just so good at answering all the questions anticipating uh what they would come up with uh that we don't need to answer anything else yeah um usually silence worries me all right if you want to reach out you're welcome to reach out like john said he's big on linkedin i'm on linkedin as well feel free to connect with us we always like having more friends on there um and then if you want to tweet at me i'm at josh
sokol uh john you want to give a twitter shout out as well you know i just i can never say anything in 100 characters what is it now 300 characters so find me on linkedin john overbought see it's easy to find me if you want to chat um i i like to connect with people so go ahead and do that let's see thanks so much oh i wanted a question someone asked a question all this time left all right guys thank you so much for uh for coming to visit us we appreciate it take care yep thank you
you