COM Hijacking Voodoo
Show transcript [en]
hello athens welcome to come hijacking vudu presentation my name is nicos vortas i'm glad to be here thank you for the invitation i hope to don't disappoint you for the next 20 minutes i will talk about common hijacking persistence who am i my community name is nick wood or ncv my friends call me nick wood it's a counter-strike name i'm cyber security consultant and there's the young greece i have ocp oswp and crto the last one is my favorite i was speaker at devsecond chapter greece besides tirana and cyprus i'm community supporter of cloudbridge.io furthermore i'm author of com hunter root and tools uh i am member of big warriors ctf team shout out to my guys
and this is my twitter if you want any collab uh please send me dm probably i will answer you i'm not a diva today we will speak about what is calm and we'll explain come more deeply and we'll show a live we'll show an action about the com hunter tool com what is calm okay the full name of com is a component object model it is a windows built-in software interface com is useful for the communication for any applications mc1 application functional to another and supports a large variety of different programming languages in order to avoid any conflict or troubleshooting of communication different applications in different written in different languages here is an simple example of using com
we have a word document and we want to end a worksheet from excel file for this action com works for you behind the scenes and here we have the worksheet in the document okay let's move on com relationship okay we have an application name and and application b application name may be is the word document the application b maybe is the excel document for the previous example the application is the com client the application b is the com server application a request for an referring object from application b and application b returns its functionality any component of application b has a unique identifier named class id okay each comcom component is the is the defined via
class id which is observed randomly globally unique identifier each component exposes functionality via one or more interfaces identified the interface ids a com class is an implementation of one or more interfaces represented by their class ids or programmatic the identifiers blog id this is an example of class id in probably in your system
the machines the local machines come objects are in high high key local machine reads the software classes path and user's com objects located in hiveki current user registry software classes path probably you know that okay the hive key class route is the merge of a high key local machine and have key current user registry
but we have something very interesting here it will have the same entry in the local machine registry and the high uh in the and in the current user registry the entry of uh current user registry um comes first of a local machine register more specifically if an attacker has an entry in current user registry with a malicious dll this entry will run first of local machine registry entry okay last but not least about com relationships the local server key represent the full path to an executable implementation the in proc server 32 key represent the full path to a dynamic link library implementation okay this is an example of class class id probably in your system again
this is from microsoft teams as you can see in proc server 32 key and this is uh the dll file as we sent as we said in proc server 32 supports only dll files com hunter okay com header is a 40.8.net framework application ssr tool about com hijacking persistence uh author okay it's me and the code review by dimitri chicopulos i will say special i want to say special thanks to the mr copulos my exco working from 12 sec you are a teacher for me thanks for any advice tips about the code the format the optimization and i want to announce that me and dimitris the meters and me we will release more tools in the future
the current version of com100 is 1.1 0.5 and this is uh the ascii art of compander probably you will see that this is a wrong version because we took the picture from the first version
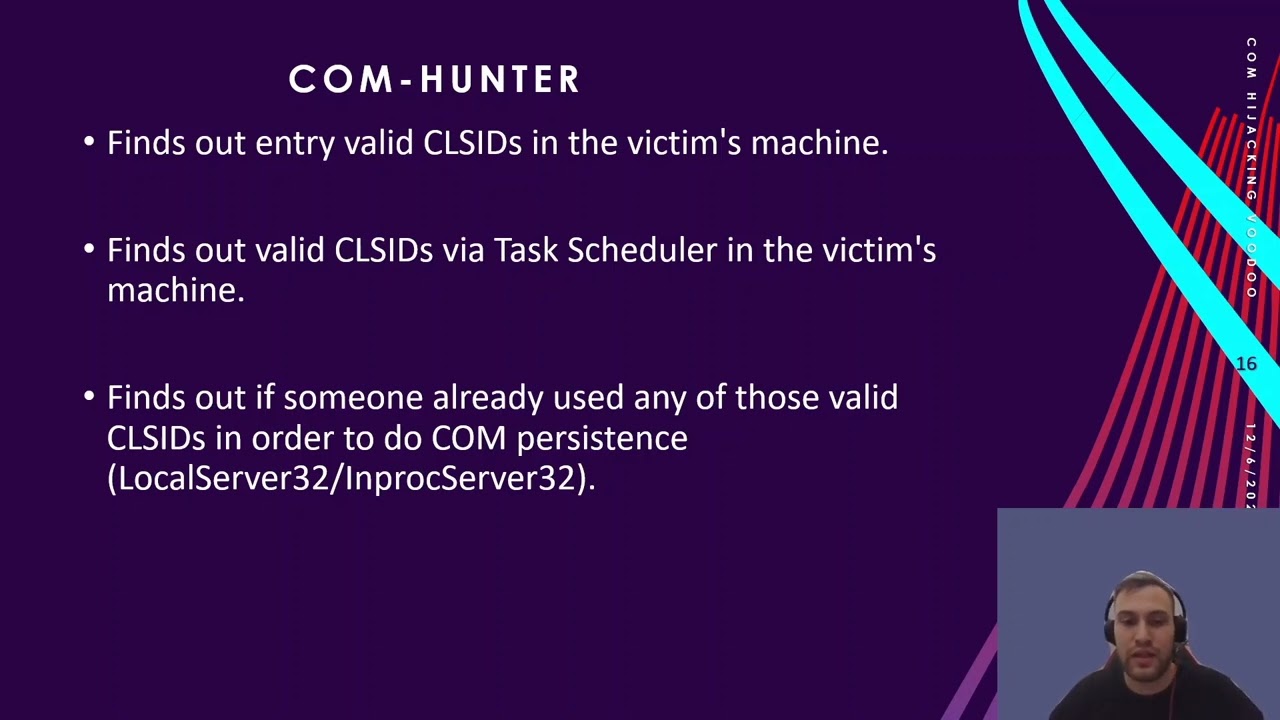
some useful uh some useful things about uh com hunter finds out the entry vault class id in the victim's machine finds out valid classic this via task via task scheduler finds out if someone already used any of those valid class ids in order to do com com persistent this is a defense feature it supports local server server 32 in proc server 32 as we said before about the exact dll finds out if someone already used any valve class id via scheduler in order to do a comp resistance tries to do automatically com hijacking persistence with general valve class id tries to automatically come hijacking persistent via task scheduler and tries to use trade task key in order
to refer to a different component okay let's see how com counter works in action here is rc2 i use a cobalt strike okay we have access on victi's machine we don't care how we gain the this axis okay
okay
let's try to upgrade interactive cell okay uh here we are first of all we need to upload evil dll invictus machine
okay we will use it soon let's execute com hunt com hunter on memory
okay let's do this for the full screen here is uh the full menu of com hunter as we said before we have two modes search and persist the search mode has two method four methods the persist mode has three methods okay let's use com hunter to find a useful class id without using any tool from cc tunnel suite like procmon okay as you can see com hunter found those class ids furthermore it's very interesting if you have if you use compounder in a system which has pre-installed some other application like a chrome or firefox browser com handler will find them and will try to find any useful class id as you can see okay back to our example
okay we'll use this class id because it's very promising
persist mode general method here is our class id and this is
the arrival dll okay com hunter says that we have persistence in the victim machines let's restart the machine okay we don't need this
okay
when a machine will power on
the user will be will sign in
will gain a new beacon as you can see we have con persistence under dll host process okay let's go from for from the defense side suppose you are a com a threat hunter okay and you want to use com hunter you can see that the com hunter found that someone used this have have used this class id and someone has persistence on your system okay let's go here
okay
and now we'll use it again nothing but suspect from found here your system appeared to become comparison free okay back to cobalt [Music] we can see that we remove the evil deal from registry but the beacon still works let's use it again to do another transistor persistent page distance
okay full screen okay let's use the search mode get task
okay com100 found like valid classic dv stack scheduler is very promising let's use this for persist
for task edger we don't don't don't need to add the class id it do it automatically
okay commander says that conversion in this system okay let's restart the system again but no need to restart the system go back and try to sign out okay and sign in again
they'll become stopped but now we had a persistent under the process dll host now we have persistent under the task scheduler
okay let's suppose that the user want to sign out again
bacon stopped as you can see
doesn't work
the user will sign in again a new beacon appeared every time that the user will sign out and will sign in we'll take a new beacon and they all done we will stop okay let's go from the defense side okay find task scheduler okay sorry
someone used the scheduler and this class id to do comp resistance so back again [Music]
to registry in order to remove it
okay as you can see this is our level dll let's remove it but the beacon works
okay this is the comb hunter thank you for your attention i hope you like it and last but not least it is what it is boys





