BSides Glasgow 2018 - Ken Munro & Andrew Tierney - Code readout Protection Bypass... For Dildos
Show transcript [en]
should we do this then yeah let's go hey let's do it shall we fantastic I am I'm shocked there are so many people in the front row because what you don't know about this talk is it comes with audience participation yeah you weren't expecting that way now before we start very clear this is a this talk contains a lot of adult humor and a lot of adults Eames probably not suitable for children there's a really good talk about mainframe password cracking in the next one by the fact you're here I assume you're all just a bunch of pervs so that's just fine now this is an update of a talk that we gave this time last
year we've done a load more research on smart things over the last year and I'd like to share some of the ridiculous stuff that we found but this talk does come with a serious message as you know we're Hardware reverse engineers we've spent a lot of time working in IOT automotive reversing maritime reversing that sort of thing one of the problems we often come up with up against is when we're trying to extract firmware we find often that the vendor has set code read out protection which means we can't get the firmware off it Andrews part of the talk is going to be about how we get around that how we bypass CRP and how we
get access to the firmware and by some amazing fluke one of the sex toys we looked at had the chip that we knew the right CRP bypass port which is why we've managed to glue a dildo talk into a hardware hacking tool it's completely tenuous I promise you anyway I want to make very clear this bit of the talk is very very not suitable for work so I'm not taking any responsibility for a fence in this talk and I want to start with explaining that I brought my my lovely friend Kayla along who you all know extremely well and one of the issues with them doing talks about adult toys is your Amazon recommendations get
really [ __ ] up okay you do this which causes all sorts of problems the other main issue is major she's Taylor doesn't actually fit in my bag properly so I had a debate on Twitter a couple of days ago about where the Kahler goes head up out of the bag or feet up anyway we'll come back to that so another major issue you need to be aware of if you're going to look at researching sex toys is amazingly the blogs we wrote about this have been incredibly popular I strongly recommend if you want to blog about vanilla research in smart sex toys you need to use a content delivery network to deal with the load our website was dosed by
the number of security researchers reading our work our website went down when we published our our last dildo blog the other thing you need to be aware of is you're probably aware when you tweet a link Twitter will try and pick up the first image from the book and one of the journalists at some motherboard vice tweeted a link about an ask we'd written and Twitter kind of misread and inherited the wrong image and the very well-known journalist accidentally tweeted a picture of a woman's cervix so it kind of needs to be really careful there I want to start though with the concept of teledildonics everyone heard of the idea tally building it's great so this was coined
by a really well-known guy Ted Nelson who's rather more famous for coining the word hypertext now as I did explain this talk comes with you audience participation so I want to explain how teledildonics works so we need some volunteers here you can have that the idea is you're one side of the world right you're the other side of the world there you go fantastic and the other is you have your mobile apps all right so you got your phone connect back to your phone connect that to your phone and then you can have virtual cybersex and you can control each other's stuff and it's fantastic but the bit I find really freaky is actually you can also I done
with it what have you lost the butt plug I have lost the butt plug who's got the bat buggy anyway so the problem is is that what am i done there's this that you can't give this one out that hard wide one you mean I've lost the butt plug this one this one's wired into the mains but the scary thing about this is I thought this is a really good idea because you know this in for example you know the military where couples are split up for many months at a time I kind of get this I can see where there'll be actually a useful way of keeping your sex life alive whilst you're away for months at a time but
then we're discovered actually they have multi-user sessions so you can actually have online parties so there'll be someone in here with a butt plug would be someone with less like a couple of other people someone with a dildo and it gets really really screwed up as well I'll take those back now you you look really credible with that actually one careful owner I promise you that hasn't hasn't been anyone yet so this is a whole area that we were discovered a little while back it all gets really really weird now the first thing we looked at was actually the owner then it was this little puppy this is the love ence just call that a puppy yeah it's a
bit broken there actually anyway I mentioned this last year now the first problem is is most these devices come with static bluetooth pins if they have a pin at all pin on this one is four zeros which means that if anyone's in range you can pair to it and take control of someone's sex toy which is just sounds a bit weird but there were other problems too when you're using the mobile app and recording the video of your session you can record stills and those are rendered in the Android package file from bitmap JPEG when they're done there's a temporary image file stored on slash SD card so that's the physical or emulated SD card
available to lapse that's never deleted properly so that's kind of a bit a bit horrible a bit a bit grim really isn't it but then things started getting really weird another research a guy called that Alberto Segura started looking at a chrome plug-in looking at how you could exercise the API how you could play around with this toy and do weird stuff and he found a slightly different version the cam girl version the idea you can cam model so people pay money you can they tip you and take control and other unpleasant things that don't do it for me but you found all sorts of XSS issues but the ones that were really interesting is he discovered you could
actually remotely hijacked the toy but you needed to know their email address and that's where things get a little bit difficult how are you gonna find that email address and that's where their API was really [ __ ] up because you it offered a query you could actually query and enumerate the API by email address and secondly even better you could in it will disclose whether they were a model or not so it made this hijack really really easy I'm just bonkers and then things went a bit further we then discovered a rather amazing feature of the cam girl version or cam model version of this toy that pings your employer and you know when
you're sitting there going I don't believe it's just can't possibly be written like this and then okay I'll explain so the mobile app that controls the device that allows you to connect their API and for people to take remote control of your thing where you can modeling job every minute it pings outbound from the mobile app looking for apps Levent comm which is the server that the api needs to communicate with it pings outbound all the time even if the apps in the background or as long as it hasn't been closed and we were eyes there's actually really quite a nasty issue here I don't know how cam modeling works but I imagine that it must be a
part-time job for some perhaps a part-time job for some have also got full-time jobs so what would happen if you did you cam modeling thing at night and the next day you went into the office with the same phone and connected to the corporate or guest wireless network your phone is continuing making pings for a cam modeling server now I'm pretty sure that gonna be picked up by content filters so by - using this app the IT staff and your office can I'm asked the fact you're a cam model now the next bit of this attack I call mum's a cam model because there's another major problem as well when the mobile app is provisioned on your network when
you start it up it creates the server publishes reports three four five six eight and anyone on authenticators on that same network can interact with that service you can do some really cool stuff you can hijack the dildo you can disclose the factory on it I'm thinking you're in a house a shared house you see that port open you know that someone else in your house on that same wireless network is a cam model school network teachers a cam model oh this gets a bit grim doesn't it but even worse if you can also hijack we have to do is request get toys of the API and you can get a list of the toys
that are in use and there's also rather a cool common origin problem within the mobile app that has been fixed now if you can convince anyone on that same network to go to a watering hole site you can remotely hijack their sex toy that's only in the Android version of the app not the iPhone version but that's crazy I mean this people are doing very private things and the apps and the making them I mean they can be unmasked next crazy one this is this is my really [ __ ] up Mary Poppins suitcase as an eight foot dildo and everything this is the kuru flashlight yeah unused untold although we took it to Vegas and for some reason you put the
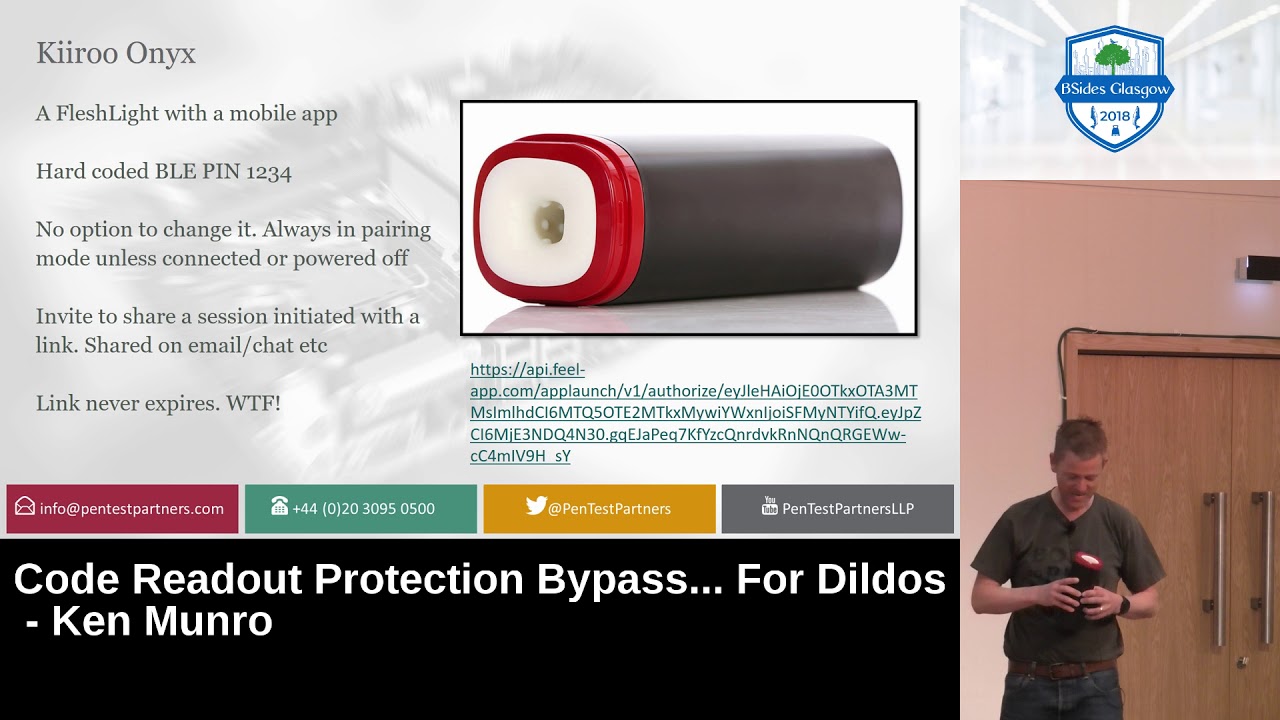
sleeve on your head yeah it kind of fit nicely yeah I live like the weirdest Smurf I think I've ever sleep it's the nicest thing you've ever said it's properly odd another great example though this has got a hard-coded pin you can't change it's one two three four but the really weird bit is if you want to join someone else's session the way it works is you're given a link a static link that never expires now whilst it does use SSL which is progress and it is nice and long and strong a random it never expires so that link is the link to this flashlight so please don't try using it crazy crazy stuff um this was
another one so we're working on this clitoral stimulator which is a bit odd trying to find security flaws in it and we discovered it actually used quite an unusual JTAG protocol so we ordered the programmer finally arrived so went yesterday to our sex toy cupboard open it up and discover that someone's taken the clitoral stimulator I mean it was you was it yeah somewhere desk I just assumed it was one of the other staff in the office I don't know wondering notably the sex toys in our place which is a bit random but I also want to tell you a story about working at PTP so as you probably know we're a little unconventional and when one of my
colleagues joined about four years ago on this first day we lucky everyone to have a little pet research project and we gave him a choice you had a choice between the Wi-Fi kettle which you'll know is now legendary and dildo you chose the cattle come on now anyway so now that guy joins a little more recently about about 18 months ago and we're sitting there and Dave and I are working on one of the sex toys which is having a bit of fun actually we were working on on this one for some reason this one's covered in glitter I don't if something's been shown over jaslyne I'm not quite sure but um in order to get the hardware
which is actually inside the base you actually have to pull the rubbery bit out and the instruction men who say put a couple of fingers in and pull hard however it's got no bluetooth security so again while Dave was trying to finger it to get the contents out to do some more research and now the one of my colleagues Joe jumped on it and drove the inflator so he's now stuck two fingers dip in a thing and actually couldn't get out until Joe deflated it a little bit later on that was quite your fun he was really cross with Joe that day that's another story anyway what we were doing there Alex had just joined on the monday this is first every
week he looks overseas us working on a sex toy in quite loudly in a quiet office goes oh I've got a smart butt plug at which point there is stony silence in the office 20 heads terminal start looking at his new starter who's going increasingly red no no no no I bought it for research I haven't used it no it's fine it's it's there for demo purposes anyway you know who you are Alex yes which is great fun now that that led us down a whole new path of weird stuff and I'd like to introduce you to the love ends hush now the weird really weird bits when you start looking at the the box I'm just gonna show you this because
it just blew my mind it's some of the stuff Wow oh that's pretty crazy all because my back and some of the stuff that's going on in the back there it is crazy strong rumbly vibrations discreetly quiet what was the other one you noticed Andrew oh yeah and from its range as well it even defines a sitting range as well Wow that she's just my bloke so anyway so we absolutely had we wanted to see how far you could actually interact with these so we bought some high-powered Bluetooth equipment but we needed to simulate it being inside someone because it's going to reduce the Bluetooth range no one in the office would volunteer and we
actually sat down and have a discussion about buying a pig a dead pig to see how far we could but we fund about if we could expense a dead pig in the name of our R&D I don't know we were hit and then cook it as well because we didn't wanted to get away she had a butt plug in who though anyway yeah but what's interesting about the butt plug particular is here is most of the toys that I've showed you that they're kind of things you deal with in privacy of your own home what's unusual about the butt plug is it's actually intended that you wear it when you're out and about which got me
really thinking cuz I switch bad boys thinking thinking yeah really thinking so we started having a look to see what we could do with it all on country right well I I love PowerPoint it [ __ ] there we go so first of all had the same problem as all of the other dildos it had no no pin on it for pairing and Alex was looking through the FAQ and said no sensitive data goes through our servers and everything you send to us is encrypted and that's great that's fantastic until he discovered actually the jabber client so the chat messages that people were having whilst controlling each other's butt plugs were completely plaintext now in fairness actually the manufacturer
was fairly good about disclosing we just closed it to them and they actually replied I was blown away this just never happens they replied left it took a little while but that's when a whole new feature of sex toys started to get really interesting to us now Alex was out in Berlin and he was out there with his bluetooth sniffer I don't about you I always go around with at least at least knitter on and what he discovered is mostly devices it's very difficult to suppress the advertising ID so if you know the advertising ID and you know it's static you can actually start to geolocate sex toys and that's where things get a bit weird
so the blame ID of the Lovings hash is LVS underscore zero zero one and that meant when you're walking around with your Bluetooth sniffer you could see people and blowme actually Berlin and spotted at LVS zero zero one hush butt plug whilst he was on the streets and of course what you do next your high jacket and this is where it's really interesting the difference most other sex toys are used in private this one people will wear it when they're out and about now typically I imagine you'd have it turned off but you can just connect to it using the app I'm you can use the API if you want you can use it ever
believe it actually just download the app and drive it to max while someone's walking around and you're not really in the position whilst you're walking down the street to pull the butt plug out your pants are you so you're sat there going oh my god what's going on kind of absolutely stuff so it's absolutely trivial to hack these devices and find them which is why things get really weird now we decided to coin a term and alex is just so good with words now you all know that when you go hunting for wireless devices you go out on a wor drive and he decided that when you go hunting for Bluetooth adult toys that's called screw driving
what's it I dunno I struggled to contain myself and he said that now I've been out screw driving for lots in lots of different places but one the most fun I wanted to look at and I did this a little while back is that went to the houses of parliament just as all the stuff was going on and I'm so sad to say that I didn't find a single sex toy advertising whose Bluetooth IDs on I was in the houses of parliament but can you imagine yeah you're there and the MPs are in the chamber doing PN Q's that have found one fantastic someone is wearing it what they do turn it up to max live TV brilliant now you need to
know the IDS to look for I've got a list up here for you and the one that leaks out you is the virtua stroker there's no hiding not that does is there but those are the IDS this is actually on github already it's not our work whilst we did the original work around Pleiades a guy called using their Enderman or the Internet of dong has actually been out included over a hundred of these already and is now cutting them coded up a script that does it all for you so having mist around with dildos for a bit of fun I think now's a good time to go and look at code readout protection yep so we like reverse engineering stuff
as well as doing this ridiculous thing so what we want to do is we want to pull the firmware from the Bartok it's got a micro processor it's got code running it and we want to get hold of that and you may have heard this saying physical access means game over you hear this time and time again with laptops phones servers it means once you've got access to a device you can do what you want to it you've got complete control the promise of IOT is that once you've got physical access it's game over and so the device is already in the hands of the attacker pretty much you've given that device away they can do what
they want to it and I don't know if you know about this but the FCC if you produce a device that emits radio and you want to sell it in the u.s. you need to submit to the FCC the Federal Communication Commission thank you and and you need to submit you know what modulation it uses what frequency it uses and you need to put internal pictures there as well so without buying devices we can actually look inside them so these are pictures from the inside of the butt plug and to be fair it's quite hard to take apart and we were tweeting it an Iran we needed a scalpel screwdriver it's not the easiest thing to take upon it's
never going to go back together again in the same way and what you can see inside it you can see it's got this little chip here which is a Bluetooth low-energy chip and we found that it had something called code readout protection enabled which means we can't read out the firmware from it so it's already in the hands of the attacker but in this case it's actually in the butt of the attacker so we decided to look more in more detail could we get the code of this now I don't know how much you know about embedded systems there's kind of three major components that make them up you've got the CPU the processor that's
probably not into everybody here you've got the RAM where things are still temporarily but you've also got the flash and the flash is where the firmware is the operating system the code it's where we find the vulnerabilities in the device so we want to access this flash to see how the device works and find issues this is a camera it's a samsung techwin camera that we've done a lot of work on in the past and what you can see on it this big silver chip is the CPU or system on chip got the processor in it it's got all of the the kind of main components of it but it doesn't have the flash or the RAM down the bottom there
we've got two chips that are both RAM and you can see these squiggly traces going up to it they're called match length traces and there's lots of them each Ram chip has got like 20 odd lines going to it so it's really hard to intercept but there we've got the flash chip that little chip there and what that means is we can be solder it we can use a hot air gun we can take the flash chip off and then we can read it so we use a thing called a universal programmer which is that white box there put the chip that we've disordered we can read the flash and we've got access to the firmware this is actually a
fridge we poured a lot of time and effort into this Samsung fridge to read the firmware off of it to get the firmware and examine it and we haven't actually found any really significant vulnerabilities in it so this is a microprocessor the security boundaries around the CPU we can always remove the flash this however is the chip that we've got in the box lock so it's that little black box there now that contains the CPU the RAM and the flash all in that little black box so what that means is the security boundary is around all of those so what manufacturers do is they enable something called code readout protection and that stops us access in the flash
but there's ways around this and we're going to go through a couple of them there one of them specifically to do with the the butt plug why do we want to do that well if we look at it as a black box we've got the toy it might have USB Bluetooth Low Energy GSM Wi-Fi but we can't really work out how it works we can fuzz it we can throw information at it but it's not going to give us many results so if we can open that box up if we can access the flash we can see the firmware if there's any shared secrets or keys or passwords we can access them it might have a serial port which allows us to
access the operating system directly the RAM might contain decrypted data you know something's decrypting data from SSL it's got to be decrypted at some point we might be able to read it now a lot of you may have heard of something called JTAG JTAG is an electrical interface that allows you to access things on the inside of computer chips it stands for joint test action group it's got five wires just electrical signals that all connect to a thing called a JTAG controller and they can interact with the flash the CPU the RAM and do a thing called boundary scan where you can change the value of the pins on the outside there's also variant of it called swd
serial yd debug and that just compresses those five wires down to two just so you've got less wires it's quite a complex protocol you can see this is a sniff we've taken of reading some data from a device you don't really have to understand JTAG at this level this is standard this is what JTAG does now the thing that isn't standard in JTAG the things that aren't mandatory are you don't have to be able to access the flash you don't have to be able to access the RAM and the security that JTAG offers isn't mandatory so you can prevent people reading your code using code read out protection but the way you do that is up to you you can do it in
your own way and manufacturers do do it in their own way and that's what we try to exploit now the vulnerabilities I'm going to tell you about here then not my work we have developed our own but these are other people's work I don't take credit for them so this is this is the chip from the butt plug this is this is the butt plug that we've got oh you found it where was it can so we we tore one of these down earlier on today and unfortunately it doesn't actually have the same chip as the older one we looked at so the screenshot you saw earlier of that chip it's not in this one so we
only had to do it against the actual device but what we do have we've got little development boards that contain the same chips this is just a three-pound development board of ebay we're gonna it's locked so you can't read the firm off of it and we're gonna get the firmware off of it it's a diagram of what this this looks like you've got the JTAG controller and it can access the flash it can access the RAM and it can access the CPU but when we lock it it stops us accessing the flash and the RAM directly the Unitas we can still access the CPU and the CPU can still access the RAM in the flash so
there might be a way around that and it's going to go to live demo this could go right it could go wrong what we're going to do is just leave the presenter over here there's far too many sex toys on this table so what we've got is a thing called an ST link this little red box here it's a JTAG adapter it's again they cost less than ten pounds and we've got another one of those little development boards there so you can see it with the NRF chip and we plugged four wires onto it's just power and two wise for swd
that's lucky isn't it hunter - Wow let's just close the presents because I think this is using a lot of CPE
yep of course like that I always go wrong to anything just give me a second
no that's not working okay we'll go back to the slide I've done it so we can fudge this so what we can do is we can connect to it using swd and when we connect it via swd we can then tell me into this thing called open OCD the open on chip debug and what we can do is we can issue commands and the first thing we do is reset halt and that just resets the chip so it takes it back to the initial state at that point it tells us some information so you can see there we've got PC the program counter that's the instruction the chip is about to execute you can see there it's set to
twelve B nine eight you've also got the stack pointer that's the start of the stack which they're ending one C four eight that's an address in RAM where the stack starts so reset ship and it's in this initial condition but where has it got those values from where did it get the program counter from where did it get the stack pointer from well on arm it's really simple at the beginning of flash address 0 you have the initial stack pointer value that's always the case and the address of for the next one along you've got the reset vector so we know two of the addresses in the flash memory we know the first two addresses
you know what the value they are we always know that and when we interact with this device we can talk MDW 0 by 4 that means show me the word at memory address for memory display word 4 and you can see there we've got 12 b99 now that's 12 B 9 8 there the reset vector this is operating something called thumb mode which means the last bits always set to 1 just to mean it's work in a different mode so we know that memory address 4 is the reset vector we can display all of them registers so there I've just type reg and you see it's gone are 0 through to r12 so these are the arm registers when you reset one
of the devices the registers default to s so you can see all of them defaulted there apart from the stack pointer and the program counter what we can do with open a CD is we can then type step and what step does it says move the program counter forward 1 carry out the next instruction so we don't we don't have to know what the code is to do that we can just move forwards it's just going to carry out the next action and then stop so you can see how the program counter has gone from 98 there to 980 so it's step four forwards because that's how arm works and we can from beforehand register r3 was all left
but afterwards register r3 was shown this value here 1 0 0 1 0 1 4 so we know that instruction that's operated has modified r3 that's a given we've stepped forwards it's modified r3 what we can do on an unlock device is we can look at what those instructions are so you can see 12 b9 8 that reset vector there is load into r3 program counter plus 84 so what it's done is it's gone to the address program counter plus 84 gdb calculates it for you so 12 BF 0 and load whatever that value is and that happens to be if we display it but value we saw an r3 now we can't take control of the program
counter there we can't execute that instruction with a different program counter because that's the address it runs err so instruction although it's changed r3 we can't control it we can turn on write protection and and read out protection on these devices so when that's enabled you can no longer write to the device you can no longer read from the device you can still have raised it but if you raise it you can't read anything cuz there's nothing there to read when we do that you saw earlier we typed in MDW 0 by 4 and we got a value of the initial the reset vector when code read out protections enabled we just get all zeros so we can't read
anymore we've confirmed you can't read it but what we can do is we go back and look at those instructions the instruction at 12 b 9a there it loads into r3 whatever are 3 points to so if you set r3 to point 2 0 and execute that instruction it will load whatsoever is in flash at 0 and load it into r3 so now what we have is a way of actually bypassing the code read a protection so if we set our 3 to 4 that second instruction there will read the flash memory from 4 into r3 so what we do we set the program counter to 12 b9 a so that's that second instruction there we
set our 3 to b4 because we've got controller the program counter we step forward which gdb SSI and then we read r3 and in r3 there you see we've got 12 b9 9 which is the reset vector of the device so we've read flash on a lot device but only one single word of it it's pretty easy to work around that actually we write script just loops through byte by byte recovering the memory now I would demo but for some reason it's decided it doesn't want to work that will dump the memory it's slow it reads about a byte every second so for the full device you know it takes an hour but that's an hour
and you've got the firmware off the device and this is this kind of idea of break once exploit everywhere you only have to break the device once and then if you find a vulnerability in it you can use it wherever you want so we can do this on the bottle now in all honesty it didn't really healed that much we already knew what the pin was on the butt plug there wasn't any hidden functionality there wasn't anything that really was of interest but the code read out the process of getting there was interesting now there's a more interesting demo here and it's moving more towards bigger more powerful chips now the SDM 32 is a series of ARM
processors their arm cortex processors they're quite low-power but they're found in everything there's probably in excess of a hundred arm cortex processors in this room there's probably one in everybody's phone the B ones in watches the B ones in laptops they're just absolutely everywhere now this behaves differently to the other one so we've got a similar situation to start with we've got the JTAG controller at the top and normally it can access flash and RAM now if we lock that and we connect via swd jate I can access the CPU but it's also cut off the CPU access to the flash it's also cut off the CPU access to the RAM so if we've locked a
device and we connect via swd we can't read the flash so it's quite a strong protection compared to other than that other technique won't work but what's important is we don't know how this JTAG controller works there's no details out there it's a black box you know there's no source code and that can be bugs in hardware and some of these bugs can be really really quite significant so this is what normally happens when you start using the device we've got the device trying to read its own flash memory that kind of makes sense we've got swd trying to read the flash memory the first thing when we connect via JTAG swd is we read the ID
code that's like the identifier of the processor we do some messing around do a bit more messing around some more messing around but by this point the device starts reading the flash memory when the device starts reading the flash memory because we've got swd connected it locks the flash it stops us reading the flash memory we try reading the flash and it won't work so the first time that someone tries reading the flash it locks the flash but what we found out was that you can actually read the flash anyway you can just read one byte of it so here this actually manages to successfully read the flash even though SWT is connected and what we also
found out was that those messing round steps are indeed messing about you don't have to carry them out so what we can do is we can move the Breede flash step much higher so we can skip all of these steps they're mandatory according to the datasheet but in reality they're not so the flash locks at that point but we've already managed to read one byte and memory from the device so we can only read one byte at a time so it's pretty simple this we reduce the swd down to a bare minimum of that messing about we initialize and then we set the read address read one byte of flash and then we reset the device we literally pull
the power turn the power back on and we've managed to access the flash now that requires very very tight timing we need to have control over resetting the device so powering it on and off and we need to very very quickly send swd commands and normally we'd use that little red debug adapter but it's over USB and USB is horrific Lee Layton it's really really slow like put a laptop out of the question we can't use a laptop to send these signals too much latency so instead what we do is you take another embedded device that's just running bare metal so we're running swd directly on that device and we connect through to it we've got tight control of the timings
and we can control the power this is taken straight from the original research that some other people did showing this is the board under attack here and this is the attacking board so this one here is locked we can't we shouldn't be able to access the firmer on this we've got an swd connection between the two of them we've got power connected between the turn so this board can turn the power on and off to here and then we just got a serial interface going through to the laptop and the laptop takes control of the process but it's actually the attacking board carrying it out now we've got the same thing here this could go right it could
go wrong we'll see how it goes so let me just start the presenter software again so what we've got is this board here connected to power with all the lights on it this is the attacking board so this is one connected via serial through to my PC the big red board at the top is just that Dean's a serial adapter the one on the left-hand side here is the board under attack so this one's got JTAG locked we shouldn't be able to read anything it seems like the presenters drop the resolution right down
of course this worked every single time that's closed the presenter so it seems to be causing things to go painfully there we go it's better now this is going to interact with the device and it all it's going to do is going to cycle through it's going to read one byte reset it read one byte reset it and hopefully it should work nope let's give it another go let's just reset that there we go so now you can see it's chugging through reading it out byte by byte if you can look at the board here I'm not going to switch back to the presenter you can see the power lights flickering so it's actually cycling the power you can see there it's
got a string that says if you can read this correctly you've managed to read out the firmware so it's gone through resetting it reading by resetting it reading by it's a race condition in the way that it deals with security and this is this is really common these code read out protection bypasses there's hundreds of them available it's more about the general techniques than it is the actual the actual specific process the one that I mentioned for the NRF v 182 works on officer arm cortex-m zeroes for example let's just scroll through so the question is why why do you need the firmware to be secret well there's a thing called Kirchhoff's principle not kirchoff's principle because they're
different but sound almost the same and the saying is a crypto system should be secure even if everything about the system except the key is public knowledge I'm sure a few of you've heard this or most of you've heard this and but vendors don't really subscribe to this they they want to keep everything private because they've either made mistakes in the implementation or they think that that privacy will improve security there's intellectual property now I realized that maybe a butt plug probably doesn't have that much intellectual property in it but when you're looking at things like self-driving cars they can't make decisions connecting over the Internet all the processing is got to happen in that car so I'm
what they need to do is they you know they need to put their processing their vision systems everything within the car we've recently been reverse engineering a Tesla which has been quite an interesting process I mean the cars worth is probably it's a most expensive thing we've looked at yeah I you've got 80 grand and currently it won't move so if you have you've been in a Tesla there's no you've been in service there's not many people have been in Tesla they're a bit rubbish inside aren't they they're not the nicest cars but the thing is it's got this massive central information display that a big console without that in the car you can't unlock the doors you can't
open the windows you can open the glovebox and you can turn the hazard lights on and currently it's sat in about 800 pieces on the workbench in the lab isn't it yeah what do you reckon the chance of it going back together is not good not good it's only 80 grand can the other thing is device device keys quite often people put IES keys in devices and then the same for all of the devices so it might be encrypting communications with the same key or the bootloader the firmware might be encrypted using the same key we can get it off one device we can apply the attack to other devices so that's another way we can use code reader
protection these are two examples that we've actually done jobs for now how many of you have got a VoIP phone on your desk lots of you how many of you if you came in to work and found your VoIP phone was missing would care not many of you so a big utility company came to us and said if you steal a VoIP phone what can you get out of it because no one's gonna care and I was going to call the police when you steal a VoIP phone all day and what we found was it was really easy to get the 802 on X F in an Access certificate from the device with that certificate we could put that onto a
laptop go into their premises connect to their network and then access things we shouldn't be able to not major problem but it was a failure of a step in their defence the other one are these these little Cisco routers these are designed to be put in remote workers houses so you know you've got a guy working remotely you put that in his house he's got two different ApS that you can connect to one for work and one for personal stuff it's got VPN keys in it they're not very well protected so we can steal that device we can get the VPN keys and we can use them now I liken this to armadillos so armadillos they're crunchy
on the outside but soft on the inside this is what CRP is people perform this like hard shell around their firmware but when you break into that show you're getting into the soft insides and you can do whatever you want as a contrast you've got what I think we should be doing which is the dine bar soft on the outside and crunchy on the inside so I think there's kind of soft on the outside crunchy on the inside aspects better be open about the security make it so that your device doesn't have secrets that matter I kind of had to Google for this armadillo image and when I talk to armadillo into Google you know
it's just that people also ask it so can you eat an armadillo the armadillos make good pets but then the best find this is the bottom can you get leprosy by touching an armadillo Google really does give you an insight into people that just quite special now kind of coming back to the vendors the people who actually make these things and the the chips those microchip produce pic chips they also now iron at mill who make AVR processes they make ARM processors they make a huge huge number of processes again there's probably tens of them in this room and they've got little kind of security disclaimer down the bottom of their data sheets talking about this
code reader protection and it's got some interesting insight into there they're thinking about this the first one is microchip believes that it's family of products is one of the most secure families of its kind on the market today when used in the intended manner and under normal conditions so what they're saying though is if I connect using a normal debug adapter to their normal product and don't do anything untoward I'm not going to get their code out now that's not what we do we break things we're designed to use them outside of the intended manner there are dishonest and possibly illegal methods used to breach the code protection feature no [ __ ] just dishonestly I mean what what is
this proving these methods require using the microchip products in a manner outside the operating specifications it's just like it's just saying it's not gonna work you're gonna get the code out anyway they kind of bring it back though you know they say neither microchip not any other semiconductor manufacturer can guarantee the security of their code that's important that's what we need to realize this is saying and this predates computers by along Church regard our toothbrushes and diamonds of equal zeal will lose fewer toothbrushes and more diamonds I mean it's kind of an important thing this is a butt plug you could spend you could buy a processor that's really really expensive you could put tamper detection on it you
could spend hours and hours writing firmware you can add per device keys but fundamentally it's a butt plug and there are bigger problems and we just need to keep things in perspective so what can we learn from this if you're a collaborative research it so that's someone working with a customer you need to make your customers aware that you can get the code out of these devices you can't rely on code readout protection time and time again people come to us and they say well you didn't actually get the code out of it you didn't find any vulnerabilities and we say well if we look good look at the code or there was a bypass what would we
find and quite often when you do break through that [ __ ] in the armor you get somewhere um offensive security research isn't by that I don't mean like him as in offensive and swearing all the time I mean people who are doing it without cooperation learn these techniques learn how to bypass code read out protection you can reapply them everywhere be prepared for failure is time and time again you can spend six weeks trying to bypass code read application you just can't do anything and by development boards instead of real devices now how much there's a bot type cost can about 80 quid 80 quid or three quid for for a little Bluetooth development board and
it's the same thing you can learn the same techniques on that versus that so by the development boards and learn how to do these things I think semiconductor vendors they don't realize that there's bugs in their chips neither st he make that second vulnerability or nordic he make the chip with the first vulnerability have actually openly admitted that these are problems that's kind of unheard of if you find a problem in security of software security it gets published people find out about it do should we talk about other things so yeah that's a roundup of the code so we just will do the butt plug Oh do the Box on 10 sounds like it yeah
okay so um we we wanted to do a hijack of the butt plug but the internet connection here is really awful and we can't get some software that we needed so what we decided to do there's just hardwired it to a power supply just to see what it did and it's get the presenter up so it's kind of it's wired into the mains pretty much and I'm just gonna see what happens just for a bit of a laugh given that I set fire to a kettle doing a talk at blackhat let's see if we can set fire so plug it's quite powerful actually it's like it's mate is your hand okay now by the way he
was holding on to it earlier should we up the voltage and so then after giving it now and it's currently draw it so it's that's about a watts of power can well say well whoa jack see likey that's you play tunes on it it's quite hard and maybe right so that's seven volts eight volts so it's destroying one in a hot 12 watts of power sure sure okay shorted a butt plug all right let's hope they're holdin apart would be fine so it's nine volts 20 watts of power 13 14 do a common hold on to Andy oh I can smell this in all this smoke yet that's it it's gone this smoke coming from the
backside [Laughter] fantastic has anyone ever done that on stage I don't think there's anyone ever done that full start no oh it's like the hamster story isn't it right so anyway um guys couple of other bits and pieces come on that's right we were going there's not time to talk about some of the other stuff we did last year so you know about Andrew tonsils from what we did last year in Edinburgh I just want to kind of wrap up with a couple of bits and point pieces guys is CR P is really important a lot of manufacturers will set it thinking they're um systems are secure and the firmware can't be expect it extracted but just to remind
we talked about this last year as being serious a little bit porn is a big business can't get away from it it's huge and I think we all laugh at some of the security Phil as we find in dildos because maybe we're just a little bit uncomfortable and perhaps also a bit shocked that these things are used by people and also shot at the poor security of you know stuff that we all saw in mainstream IT being fixed 10 to 15 years ago but I've seen this quote please stop laughing which I actually think is really interesting it's not my quote it's from Internet dongs guy cool uses a nickname render man and he's actually been doing some really good
stuff to try and get secretory vendors to up their game to deal with researchers and actually the last cam model exploit problem we had he helped us disclose it to the vendor and they fixed it within about 30 days it was just really good but the problem is right now there can't working from such a low base of security they've got huge amounts assuming that they're not doing the basics not doing SSL they're not pinning they're not doing even simple key storage so there's a long way to go however it's been one of the most fun and interesting crazy projects we've done there's an organization we'll love and laugh about the sex toys but actually it's really good fun to play
with so if you fancy having a go go buy some I mean go [ __ ] up your Amazon recommendations like I have I'll get some really weird stuff I'm gonna leave you with us cyber giving us Andrew that's me this blog is full of stuff by and large the blog is suitable for work it hasn't been blocked by too many content filters yet but there's loads of how to's how to deal with hardware how to learn the basics of hardware hacking how to teach yourself code read out by possible hope you enjoyed it thank you [Applause] nearly ready for Jess to go propagate time for a couple of questions if anyone's got one anybody for questions they were brave
enough to put their hand up and tell us they've got a sex story yes that's a really really good question as as a privacy campaigner called Amy Stepanovich who is really active in trying to get the concept of digital rape which is fundamentally what it is already we've seen people held to ransom through theft of very personal photographs that they're convinced into sharing on skype by scammers what's to stop the next step forward in that being actual compromise a very personal data from your sex toy I genuinely think this is going to happen I do not know of a single legal environment legal framework in any country around the world which deals with the concept of digital rape I
know that lots of lobbyists are working I do hope it comes to loss soon because I think it's really important we are going to see cases of digital rape I'm sad to say I think we'll probably see cases of people driven to suicide through people holding and embarrassing and extracting money from people through their sex toys which i think is a really bad state of affairs any more questions no one else is brave enough to put their hand up and say they've got a sex toy right thank you [Applause]