Lies, More Lies, and Ransomware Statistics

Show original YouTube description
Show transcript [en]
all right without further ado lies more lies and ransomware statistics okay i turned the mic on oh i can hear myself great okay so let's uh let's uh so you can do so my name is dennis i'm an engineer uh so um uh yeah so what i'm gonna do is i'm gonna walk you guys through some of uh the business decisions uh that we make internally for our own company for our products and what to do and what the charge things like that and also some of the number crunching that we try to give our clients from an advisory sense because actually this is one of the most difficult challenges i've had uh so far
in my career is to provide some kind of quantification that i can defend on who's gonna hit with randomware what's the probability and what's the impact right the numbers are all over the place just to warn you we're not going to boil the ocean here but i'm going to walk you through some stuff that we're doing internally and some of the challenges that i had and when at one point i had to walk away because i got too angry so we'll definitely cover that one so first of all um i noticed a large technical crowd here right so some of you of course know exactly what this slide is all about some of you uh maybe
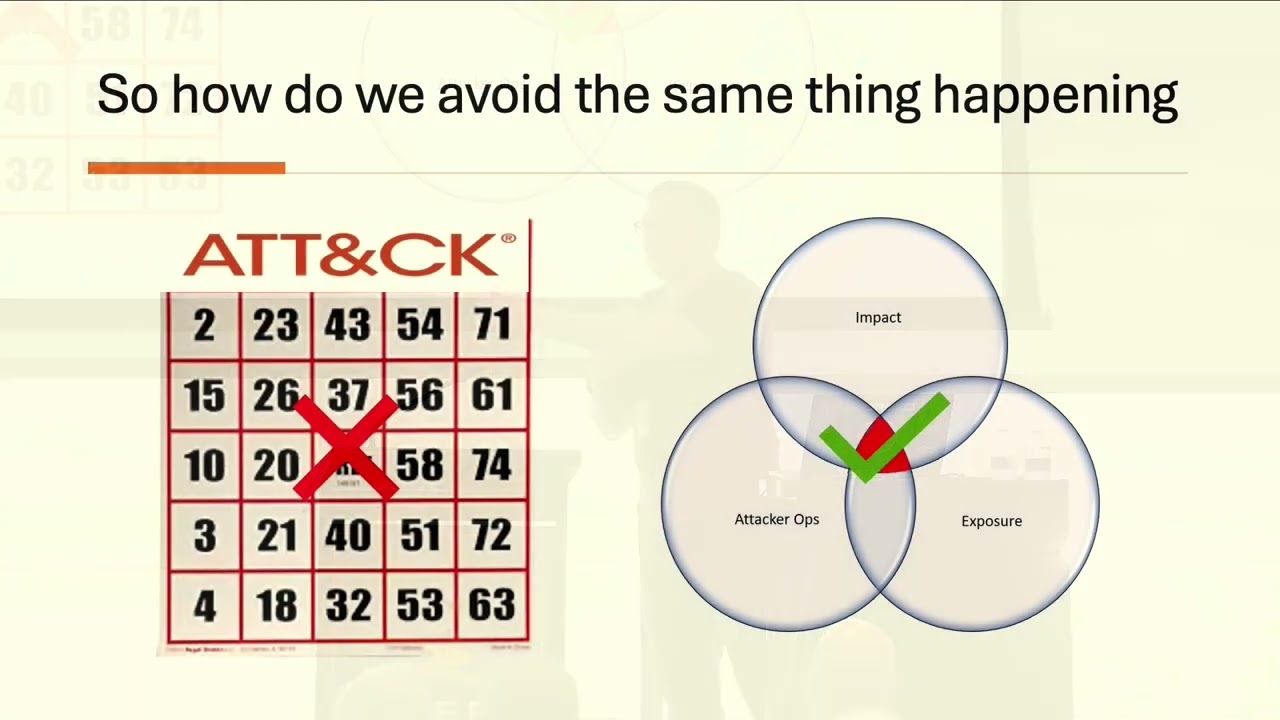
you've never seen it before and that's cool either way right so um we're talking about the probability the impact of risk and it's a good diagram to show so what we're going to say is you know what is the probability and what is the impact the death to the business right for a ransomware attack it sounds super easy right to maybe pick one and go with it the challenge is that you know when you're looking okay what do i want to do what can i do to actually maybe uh figure out what needs to be done for ransomware right one of the biggest things that i see and of course what's that saying you know if
you buy ibm those are getting fired like just buy what the neighbors are buying kind of thing well what's happening with ransomware is really really interesting to me there's enough data out there i call it enough fail on the defender side that we actually have some really good metrics right and one of them is that oh it's like i have to face forward like a proper speaker so one of the challenges is that people are buying like next gen endpoint security products right as part of the suite of things that they're buying to try to keep up and combat ransomware because when the boss is asking what are you doing about ransomware you better have an answer hopefully it's a good
answer but you have to have an answer right around 61 of people are out there actually buying endpoint uh security products right edrs well if you notice here the if you take some market survey results edr's like next gen endpoint products really only have around 36 percent of market penetration right so there's not a ton of people out there buying the stuff that probably a lot of the people here have in their businesses right of that group if you look at the numbers over three-fourths of the victims of ransomware have those tools so what's going on is that the ransomware people perversely are attacking the folks who have security budgets right who have the money to go after you right they're not
going after the uh you know the penniless non-profit that has no security product and has uh i don't want to name any names they don't feel bad but like free antivirus you know they're not going after those folks they're going after the folks who are spending money on backups and point security and it's not because folks like you aren't trying to do something right and they did a survey i think it was so folks did it it was 91 companies said they want to do something or they already had something right to try to combat ransomware so it's definitely something that we're all concerned about um unfortunately the attackers uh are going after the ones that are concerned
right so let's first start with the risk management exercise let's say okay we need to prepare to ask for budget like you want to go buy a tool right so what's step one for any project find a scapegoat right for when it fails but really you need you to find some kind of third party data source to say look this is the probability and this is the impact for the ransomware attack right this is the risk management exercise we've got to do when preparing for budgets make sure you defend your math right if there's the board members who love numbers maybe it's a cfo on the board there should be one probably right um then you need to make sure that they
don't have numbers that are wildly different than yours so you're not stuck with this battle of the facts you know trying to figure out what the right facts are we'll get into that i've actually never seen an environment like this before where the numbers for risk management are so wildly off uh that it actually causes some major problems in deciding risk spend of course i know everyone is the organization everyone all the attendees your you know your board meetings are very nice you all decide numbers logically and you move forward right maybe no one laughs so that was my one joke yeah okay so let's get back to uh back to business okay so if you get it wrong
we have enough fail again or enough win on the good guys side that we actually get to see the effects of getting it wrong right you just um we'll say that like someone just says i'm going to go buy an edr and we're going to call quits right that's been my solution and just like you know data breaches there can be stolen data right um the business still is able to earn revenue right it's not a business continuity issue in many cases right with ransomware you have this whole extra element where it's not like you know um you know you lost data and then everyone argues about reputational costs and you know uh regulatory costs and things like
that and it's all cost doing business in this case you have major impact like the cfo has line items for the kind of impact here for ransomware right whenever the business stops operating with revenue at that point honestly if you look at the numbers and then pull up fema reports it's very similar to a major fire in like a restaurant it's a very very similar track and to how long your business has before it's gone forever which is a very scary place to be right um so one thing that i really want to point out here is that even when you pay the ransom and survive 61 of the time your organization has lost the data
forever now a little war story here i get a phone call last week from someone there you know who uh they got hit with ransomware was the manufacturing uh plant and um they gave us a call back and said they're taking care of the problem themselves they don't need our decrypters or anything um i asked oh do tell do you need help whatever you know well it turns out they said no we're deleting all the hacker files they were going through all their servers and deleting all the encrypted files their files right and they said they were almost done and i don't know if they're ever going to call again because at that point their business is
gone right so like um but regardless so 64 loose data 82 percent lose business critical data and what that means is the old game of backups right where the hackers maybe got the most recent backups but the ones in the tape drives back inside the mountain are you know pretty safe right and so you now have 23 copies of 2011 tax returns to your business but you don't have the rfps that were due next week right and so what's happening is that 82 percent actually of that 61 is kind of weird but they've lost business critical data it's not just like hey i lost my photos that weren't really important it's i lost the stuff that i need to service my
customers contractually i have obligations i have sales things going on that data's gone forever even undoing decryption it didn't quite work right it's just it's known um are there any msps or i.t providers in the audience it's always like no no whatever he reads there oh there's someone actually raised their hand oh my goodness i'm sorry for you on the spot you know so like um so what happens is when uh if you're like uh msp your messed source writer it provider gets hit with ransomware or has a customer that gets it with ransomware if the other customers find out in 15 of the time half the customers walk within three days once they find out um
normally within 75 percent of the time at least one customer beyond the one that got ransomware walks right so these are very very serious issues even for the i.t providers right because knowing it's almost like this uh social stigma we're going to get this a little bit more where no one wants to talk about getting with ransomware but it's happening enough that when it does happen even though we're spending money to try to stop it what happens is is that you know people are losing business they're losing their livelihoods things like that normally i stop here and ask questions but does not seem like people aren't like in the mosh pit here like ready to ask
questions so um so one another another technique you can use i've seen this actually at play before um this was uh if you guys ever heard of martha's vineyard it's actually part of a larger corporation it's it's a government body so their their operating revenues and their their balance sheets are all kind of out there for the public to read if you really really really want to do it and what happened was was that they had spent a ton of money on backups and other things to try to uh you know stay in business to react and respond very quickly to ransomware right there was an old game i saw it being played i'm at
one point i was over at nsa you know national security agency and there was a game they played with government contracts where if they knew they weren't going to succeed or couldn't succeed then they would redefine the success metrics right they would kind of scale back what success was so they could all come back and be like we won and it was like yeah but you only did like half what you said you were going to do in the beginning right so in this case what i'm seeing is in some cases um to to manage the risk and manage reputational damage to the i.t team to leadership these quotes are actually from the security leadership right i'm sure he's
a great guy i'm sure they tried really hard right ransomware happened they finally got minimal services up after a week for it's called the steamship authority or something uh jim one of my guys was from boston so he's all about it like but um up in that area and what happened was what they were up and running right within a week well i pulled down the balance sheets and i said what are we talking about here in terms of the revenue loss of the company for that one week after they spent all that money on backups they can come back within a week right turns out they lost 3.6 million dollars in sales lane revenue based on
projections you know for that period um that put them in the red for the next 18 months there's no coming back they're in the red if they do everything right right and so that's the table stakes here really is that you know even when you say oh we did it we're back within the norm is actually like 12 days or or 15 days something like that to get minimal services back um they did within a week they still are in the red like the business is no longer profitable uh just on that one event so let's let's focus on ransoms that's like if you're going to define the risk and the cost of the business
there's a whole bunch of variables and uh there's some really really smart people that do all that discreet math that we kind of slept through in college right that have you know a thousand variables to figure out the risk exposure how much it's gonna cost to business things like that let's start with ransom i redacted the names of the data sources on purpose because um you know i you know i i didn't want to name anyone i don't want that to be a focus and maybe it's because the source right these are three leading industry standard sources that people like previous presentations actually use in their analysis on you know in their advisory things like that the first one
showed um three years of ransoms right and we have forty three hundred dollars fifty nine hundred dollars and eighty one hundred dollars that is not a typo right what is a typo exact in that faith like that's the face i made it was like this can't be real you know what happened was was you dig into their math this was a major publication by international company what happened was was that they forgot to put in a zero in one of their calculations and that it went straight through to publishing people layered on their analysis and their math and then you can actually google around it's still out there being repeated what happened was was that those numbers
were then used by other publications because it's now like trusted source and three or four layers down you actually i found an article where someone was advising on how much insurance to buy for their company based on the 8 100 ransom right which everyone in this room should say that sounds kind of low right um but these are you know uh desktop publishing people they don't know the numbers like we do right um we have data source two right which had eighty four thousand dollars which is probably more reasonable maybe it's not newsworthy right i mean that's sad to say but you know with the losses it's not the the five million dollar ransoms right um
it's a respectable number we have data source three again a very very reputable source they have some inside knowledge into some of the insurance payouts actually so from cyber insurance and they're coming with numbers for average and median now um i know we uh kyle previously get a whole bunch of like mathy things with bits and bytes and everything right we're not going to go that deep but if you look up the difference in average and median so what happens is is that basically there's a whole bunch of lower cost ransoms that are being accounted for and we're going to talk about that in a second so what that means is that there may be larger ransom
sums but what's happening is it's called a um hey it's not showing i'd like to throw a graph there to show it but like basically there's if you look at the graph right then i'm really bad about standing in my spot so if there's a graph right here it would show there's a whole bunch near the vertical axis right and it kind of tails off and when that happens that's the number you get on data source three right so that means they're they're having access to a whole bunch of data that show low like it's like a volume game low number or low money value high volume a whole bunch of transactions at lower numbers right
i'm gonna call that a lie in a second right so look at the raw data this is from where the good guys beat the hackers they only got 1.8 billion dollars and they gave up we got them right so they retired because they got out they're probably back in our group now right but we got some awesome awesome raw data off of their winnings basically right rather fitting word a casino right so um there were about 3 000 victims that they released keys for um i'm not going to ask any feds in here this isn't this isn't uh you know defcon but like um there were 88 victims that law enforcement was tracking at the moment
right that they knew about that were reported right if you do the math that means that of all of our risk analysis we're all doing for our boards and our companies and our managers we have three percent visibility into what's really going on that means that companies are getting hit and they're not reporting the average ransom in the data from avadon from those folks is a really cool z net report there's other ones out there was that the ransom was actually 600 000 so we go back is is that anywhere close we're seeing here not at all right so companies are getting bled right they're trying to fix the problem it's almost like a social stigma like i
don't know like vd or something like you can't talk about it ever you know like in normal society right and so that's what we're seeing here right this is not a good situation for us as the i.t security and the business leaders to try to mitigate risk imagine if the fire departments had that kind of like shortage of data right there would be major major problems with the city blocks burning down so possible biases we have here um i'm probably dating myself a little bit with that screenshot so so we have um an issue where we do have missing data sometimes it's not always that egregious but i do find that there are mistakes in the math i'm
assuming it's because um there's just so much strange data out there that people are trying to put together myself included where i'm like it towards the end i'm going to say this is my gut says because we have to do at some point you know because there's just not enough good data out there on this so um the the crime with the missing zero really was that there there's only so much data that is out there right and we have to trust it because we don't know what to trust right and so the real crime here is that that data is fueling the exact same people that are doing analysis at your insurance company right at law
enforcement at other places to fuel pricing for products like what we're doing right to fuel okay what's really the cost to the business what is the business impact right um the probability we know we already know now we only have three percent visibility right but in terms of the uh the cost right um we really need to watch um what we feel might be wrong i mean i don't have a better answer for you than that right um but i'm trying to figure out when we go through the analysis is kind of like what feels right which doesn't feel right what can i latch on to that's good there's actually a government report that came out i'll get
to in a second that helps out a lot with that we'll go into that i'm very happy about it the uh the second possible bias is the victim profile so first of all the ransoms for like small indian companies um are much much lower like three to five thousand dollars really right um and what's interesting is that different verticals have different uh ransoms of which the market can bear right so med tech can afford to pay a lot more ransom and to keep it quiet before the fda testing right than say a mom and pop butcher right it's just the way it works right for every industry ever um so what's happening is that depending on who is willing to speak up
we'll get to this in a second um uh depends on it it heavily skews the ransom now if uh if 10 000 small companies in india in pakistan all report that they go with ransomware right but then the uh the companies in the united states that have reached council on the phone and some strange security company person asked them hey have you gotten ransomware can you tell us to ransom how much it cost your company that week please don't tell shareholders right um you're not gonna answer right and so that is actually one of the biases i'm seeing is that folks that don't have the lawyer a culture the mature kind of like breach response culture like we have
here in america tend to answer up more um and that i want to say pollutes the metrics but it definitely has a very meaningful effect that we already saw with the the graph that i had to pantomime you know um so uh the second thing we see is that i call it the goldilocks for ransomware like so what i see is that we saw some african clinics got hit right and they had computers of course this isn't like you know they run the dark ages but they also still had a ton of paper because they didn't quite trust the computer stuff for power reasons or whatever i mean this is like u.n right so it's not like
they're living in the dark ages right um but they had all the paper records so they went down from ransomware it it stunk for them you know they weren't super super happy they had to have it fixed but they went right back to the paper records right and then so it didn't really have the impact for them like it would if it like upmc or whatever and you're all digital now right so um the second point for the goldilocks you know method is that um the the super super big and um you know very technical people at these very large fortune 50 companies um they require a different style of attack to actually have meaningful impact right a
small attack on a branch in a big bank uh you know big international conglomerate isn't going to have the same impact right you have a different style of laying low spreading out going through it could be six months or a year before you actually hit them with the ransomware right and take out enough data to really put the pain on them right that's not going to be like a a ransomware as a service kind of like a script kitty just running through right um what i find is the are the most vulnerable actually are folks that have some good tech in place they have like maybe office his 65 set up and they have sharepoint they have all these cool
things going on and backups right they are dependent on the technology but they're not so mature and big that they don't have like seven hot sites set across the united states right like that's that's not what we're talking about here so um we find is that the folks who are have to have successful businesses um have good technology have edrs and antivirus and all the cool things right and firewalls are the ones that actually hurt the most for ransomware attacks because i mean we already saw a little chart right they're going after folks who have budget for security right they're bypassing in various ways which that's not this presentation right but um we're seeing that that that really helps um
define kind of like your risk we don't have good numbers right but we can say look we're not i mean bank of america i don't know yeah but but we are we are a company that is technology driven independent and email driven right then we know that okay the ransomware probably hit us hard you know um and the ransomware vector uh so i love using this example because uh there was a data source that uh had a whole lot of reporting on the stopped ransomware variant the family right and um unfortunately stockbrain somewhere their big claim to fame was actually file share like pirated software and pirated movies and stuff that was their major major uh vector for spreading
right well the bias there was that um stop ransomware the individuals who are downloading pirated copies of office are not the big game hunters right they're not the people who can afford to pay big ransoms and so this one reporting that came out um once they realized it was all stop ransomware i was like no wonder the numbers are so low it's all like college kids you know and people who are like pirating sex the city episodes you know they're not gonna like pay a lot of money in ransoms right and so the data sources of where the security companies are getting their uh their metrics heavily heavily effect is affected by the ransomware that they're exposed to
does that all make sense like no one's like walking out in droves i guess it's all good paid by they are okay so um so also who is the one to talk right i kind of went back to this a little bit so the large ransomware data sets for reporting um it seems to be very survey driven it's down to who does not have a lawyer who says shut your mouth right rightfully so probably right um you know it's smaller organizations it's i've noticed also it can be cultures that are more open um and more collaborative uh than ones who are less collaborative right that seems to also follow a trend from like a society standpoint right or
organizations that are more collaborative or industries right um so what happens is that that shapes it's a big enough problem three percent we only know about three percent of it right um it's a big enough problem that that dramatically influences um you know the data you have in front of you uh for smaller ransomware data sets what i'm seeing is there um there's companies that specialize in uh incident response right dfir right and um they normally have a limited set of customers right that have ransomware there's like what 3 500 security companies all servicing folks in the united states alone right so um they have a very limited view of maybe a few hundred people you know that we're
victims right and they're basing all their metrics off of that which is a dangerous place to be any medical study that has 300 people only you know that's not a that's not a good medical study to rely you know put your life on the line for right you want thousands and thousands of people right so we also see that you know sometimes there's man data disclosures now that could be because of like government regulation that could be contractually right that could be where you're an i.t provider and your customers talk to each other or they're down the street from each other and all of a sudden the restaurant's closed right so there are living disclosures that you know can
happen um sometimes you you really don't trust your nda because the employees figure out what's going on right and next thing you know they're on facebook and they're talking right and that can cause serious serious money but it does give some good insight into what's going on right there are certain ransomware incidents we would never have known about hadn't it been for people kind of leaked it out right because of a actually a mandated disclosure to a supplier i am seeing where um public relations attack mitigation strategies uh minimization uh call your pr firm have them kind of manage the communications just like a breach right they got to be fast right this is ransomware right your
business is going down possibly so i do see that that also seems to affect where there could have been some good data there's a very large consulting firm that came back and they said okay we went down from ransomware there was no impact but we're back in business now a week later you know and i was like okay at least have some sense to it don't say there was no impact when you're down right um so we do see though where it kind of hides the data from us as security folks because we could have gotten good data there right in terms of like okay what did they do that worked what did they do that didn't work
what was the probability they felt like would they do right and wrong and that's kind of would be good for us to have right and unfortunately again we why there's very good reasons why but they uh we don't have access to that data um and of course small companies normally are much more open about these ransomware attacks and things like that they're by their nature more community oriented normally and you know they will disclose more again it goes back to that that that graph that you know i wish i'll find it um the um where low ransoms for mom and pop shop a gas station is not going to pay the same amount as upmc right just common sense
right they don't have the budget to so those were the problems right i'm an engineer right so who decided it was a good idea to start a company right so i'm sure my employees hate you saying that but like um so uh what happened was i said okay you know what i'm a data scientist i'm an engineer i can figure this out give me all the raw data right so i poured through stuff and i figured out where the best sources of raw data were and i had this masterful beautiful excel spreadsheet with like 80 variables in it and i said i'm going to figure this out because i need to know if i'm overcharging or under charging
for my ransomware prevention products i'm really selfish right you know to figure out and i can convince people that here's the probability here's the impact i finally have the numbers the juice is cooked right well so i started doing that and i realized the third world country issue was becoming a problem right where the low paying ransoms weren't as much and it was polluting the data unless i'm talking to them right like don't don't go to a north american country i'm sorry company and throw out a whole bunch of numbers from third world right that's not going to be a good lineup for anyone right so what happened was was that um as i was
going through i got the data right it was great it was in a an excel spreadsheet um and then i realized that like the numbers kept coming out no matter how i divided and added between the cells and the columns and the rows it was always 5.69 was the ratio for everything and i was like let me put in more companies or i'm sorry more countries i put in canada i put in switzerland i put in you know sweden and great britain it was always 5.69 so that's where i kind of like freaked out a little bit not in a good way either because i did all that work and i had all the available data out there i think
i talked about it here more yeah and i was like well it's all made up then because there is no way the economies of like every single first world country have the same currency ratios and the same market verticals and everything right it had to have been all made up at some point where i feel like some intern was like i give up and they started slapping in numbers and was like no whatever guess this because i didn't see it until the very end and it wasn't even like a clean number it was like five point six eight seven four nine six four something like that right and i was like no way that that number that specific
cost end up conditions right but would ever have survived has all 80 variables right for all the different countries which means i went right back to square one where i was like great now i've got gut feelings and i got butterflies in the air right but i do have three percent exposure for what's that worse you know so does that all make sense to you guys why like the numbers shouldn't be lining up that cleanly across the global economies okay cool and now you see why i took the names of the reports off of here because i don't want to like i don't want that to focus i want the the problem with the numbers to
be the focus right so we're right back to here right i mean right back to where i was right where i was just like now what do i do right because you're like well what's the probability what's the impact all i can tell you is that i'm right back to gut feelings right and that every survey out there is now suspect right i'm looking over my shoulder no matter what number i give so here comes the federal crimes enforcement network fsan right um you say you said fedsen maybe uh new report came out i recommend you go find it and you read it one of the first things that they did it was great um is they said
again i'm not part of the organization right but i read that quote and i read through it and i said the first thing they they saw was we need more visibility right we need something that we can hang our hat on i mean it's a it's a federal like crimes unfortunate network they're very financially driven right so of course the quants the accountants the cfos the risk managers they want to have numbers they can rely on right just like we do right i got to know how much to ask the boss for and i got to go defend it right so great they said hey in the fall 2020 just that was just a little bit ago right they said we
want to have more visibility into what's going on so they started asking ir companies to put stuff in now it was kind of like a ask told right um without a whole lot of teeth at this point quite honestly um and what happens is you see here 2020 they started to get a lot more data in right now we're not we're not you know beating that three percent yet but we're doing a good job now right we have better visibility in the numbers we can rely on right from us-based ir firms it's not global right it's u.s so it's our market right and it's folks who have gone ahead and gone to ir firms so
you're not going to get grandma trying to get the grandkids photos back as much right you're going to get companies like ours that actually have needs to stay in business right and what's great is that you see here on the 2021 we're starting to get velocity now right because now we're starting to see what's going on uh in a better way with the disclosures we have a higher number now in 2021 and they only measure till june so now we know okay we knew it was kind of bad we didn't know how bad but now we see that the velocity is well it was bad sort of it's much worse now right we got that
right so if nothing else you could point to the velocity um data driven right from the u.s government showing you that ransomware is more of a problem now for organizations than it was before not not blocked attacks or whatever these are victims this is all ir this is all ransoms being paid out from ir firms that have agreed to collaborate with the us government how am i in time anyway am i oh wow okay so strategy two and by the way i am super super excited about this report i recommend you go download it i had no play at all in it right um you can find them on linkedin with that weird qr code
and you know if you trusted it and uh go ahead and ask for it and i'll send you the link you know so strategy two was follow the money now there's the visibility problem here let's talk about that for a second but following the money has been a great way uh to follow people whether it's like the mob whether it's like terrorists you know uh or political campaigns that maybe gone awry all kind of things right so following the money what they did was they found 177 bitcoin addresses that were known to be used by the bad guys for ransomware right bitcoin if you didn't know it um allows you to look at the transactions and see where the money
is going and coming from right it's not as anonymous as you really think it is the weakness is getting the money out of bitcoin really that's the hard part when you have 5.2 billion dollars right just go to the bank and cash that out right so um so they realized that with the limited number of visit amount of visibility they had despite us saying you know hey we don't know what the ransoms are but we know they're making a ton of money right these guys have a system down right and that's only limited visibility the uh they kept with an estimated ransom value from those ir firms of a hundred forty eight thousand dollars for an attack um
on average that wasn't the uh you know it's higher this year than last year but they have more visibility and we can't trust numbers right um which as a math person freaks me out right but um so we see that the so you can estimate you can come back with defensible numbers and say that hey for probably small to medium enterprise right i'm at a hundred fifty thousand dollars of ransom on average right um and uh the total value was a 400 million so visibility right we still only have partial visibility 400 million versus 5 billion right so we don't quite know what's going on yet with everything but we can at least have some numbers they
can trust right which is the name of the game and risk management right you have to have something you can defend and go back to the bosses and try to manage the risk the illicit finance disruption efforts if we see so there's two things going to happen if we see ransom stop like as in ones that we know how to look for stop right they're going to continue sorry they're going to continue but what happens is we lose that visibility it's the whole like hey why didn't they knock out the informant you know kind of thing where it's like oh they left them there so you keep on forming right we have a way to see right now right um
i i will bet anyone one of the delicious burgers downstairs like on any day of the week that if you make ransoms illegal and some business has their pers some small business will say a restaurant has an sba inspired loan tied at their personal credit and their house is collateral they will pay that ransom to save their family right it's going to happen that it's not even an ethics or morality question right and so um with this we actually get some visibility right now what's happening is that um there are other bitcoin uh technologies i'm sorry cryptocurrency technologies that's how pervasive bitcoin is right um that are out there that yeah okay cool that have um
a lot of money going around not all of them allow for visibility we have into the money flowing around right in fact there are some that actually um are not uh they're designed so you can't they're designed to be dis decentralized without that level of tracking just so that the government can't come by and say hey uh knock down that exchange you know this is totally decentralized peer-to-peer very secure and it's in its implementation from the ground up right so we're already starting to see where some ransomware operators are moving to those cryptocurrencies my first question right on the business side was okay well do those other cryptocurrencies have the capacity in their financial networks to actually go
ahead and execute five billion dollars in transactions right um and the answer is yes they do we see we have 1.1 trillion for bitcoin ethereum is 482 billion we go down number six here 56 billion there's still plenty of room there right for ransomware to run all their known operations five billion dollars worth uh through there right um without really having a hitch and uh bitcoin we have visibility otherwise we don't so we may be losing that in the future right but we have it now so we should use it now is the point we should all download that report again i have nothing associated with the report but i read it and like i loved it you know
because it actually gave us numbers we can rely on so on the insurance side we actually have some cool business continuity numbers now remember what i said about um sometimes you can have a survey or you have you have a report come out but the number of cases you're looking at is very low and that can poison your results unfortunately the number of claims here they only knew the ransom in the third of them so that's not good that's you're already at like what six claims and you only knew four or the six or uh but um well or you didn't know for the six but you see where you have all the numbers here for business continuity
we can roughly get a ratio of about 1.6 right so if you can figure out the ransom roughly something then you can start to multiply and get the business continuity pieces now you have something to work with to try to get that business continuity piece down right in addition to the ransom of course right you have numbers to work with to be able to convince your cfo to convince the ceo to go ahead and spend money on this right without them coming out with that eight thousand dollar ransom which has actually happened where i've had reports come back and they're just like oh no look it's gonna be a problem i got petty cash you know and i'm just like do not
trust that data you know so um so really you know we're we're still not quite having things settled here on like i don't i don't have a nice story to give you to say it is definitely i'm a vendor and it is definitely this one because that makes me the most money you know that's just that's not what we're at right we're just kind of like we got a big problem folks we don't even know how big the problem is that's what i'm trying to say if if you're confused too yeah of why this guy's up here doing this yeah i get it right because like i lost it at one point when i saw like that ratio i like
how to put down everything for like a week but it's like i was like i'm just do coding or something to relax me you know so um so what we do see though is that the more evidence we're getting the velocity showing it's not getting better right we are seeing that there is an 80 chance that once you're a victim once you will be a victim again we have had some of our clients for our prevention product who while deciding whether to install it got hit again even before it got installed right that's happened a couple times now actually so um 46 from the time they think the same attackers you know what this reminds me of with ransomware's a
service coming where you have more and more salesmen out there right trying you know how many of you have sales guys call all day right you know call you and leave voicemails and text you and everything else right well france tells me the same thing right so what i'm thinking we're starting to see now is the mafia protection money model right where the ransom's only 150k we can pretty much afford that a lot of businesses can afford that it's gonna hurt it's gonna hurt like heck but you can afford that take out a loan whatever well it's not enough to kill you it's enough to make the payment keep on going so that they can keep going back to you
over and over again i think we're kind of heading towards there i it's just it's my gut feeling um i'm going to stick with it and i hope i'm wrong but i think we're going to start seeing a show up as a line item on our budgets right we're going to say okay this will take this much hit again it's been nine months it's about time for the mafia to come back and demand protection money again with a ransom i i just it just feels like it but again i just told you not to trust anything i ever said right all these security people say and here i am saying well trust my gut but
that's kind of where the evidence is going and i would love for someone to have at b-sides next year where they say this wacky guy dennis gave these numbers and i proved him wrong look at my math behold you know gloria's purpose you know so um so that that's kind of where where i'm at right now and i know you have time so i did it right do you guys have any questions while i'm here that bad huh no it wasn't that bad it was great you guys like it you good
but tell us tell us a fun fact about you oh jeez um so um so when i was in the army um i was artillery and then i became an mp person so i did like missions and compliments hillary they shot you out of a cannon well it gets better so they took away that and i had like a jeep right but i had all of my sam's books with me because i wanted to be able to get back into i.t and security when i got back right well you know how the qurans are all like very fancy with like the threadbound and everything it's not just for looks so my sans books my security
books gcse and everything else right um they were melting during missions like i pulled out and it'll be like next to like boiling hot like grenades and like you know ammo cans and everything and like chapters would fly out it looks super technical right you've ever had like one of the sans books so they're always like a rocky kids around that would like grab our papers and of course it looks really important right seeing like how to configure cisco router securely kind of stuff right and they always thought it was like mission stuff because they didn't read english and i'm sl i'm i was fast i was 25 or whatever but like slow compared to a
rocky kid you know and i would chase them like quarter mile in the desert until like for way too many times before i realized and that's never gonna win you know and when i got back i started an i.t business and i can actually tell the chapters it was so sad that i was missing because i would get to a certain point and be like how do i do that you know and then like i could get my book and there'd be like a gap you know where that chapter was just gone forever and had to buy a new sam's book that's how it happened now that is a great fun fact come on give him a hand
thanks everyone