To the docs and beyond!
Show transcript [en]
okay so hello everyone and welcome to my talk titled do the dogs i'm gone this talk is about exploring usually unexplored act of faith vectors little bit about me uh who am i i'm a hacker a country hunter documentation reader i am also a two-time vp and one of the top 50 hackers on background okay so let's go over the summary of this talk this talk comprises of four issues first is a cross right crypting issue that was a story of fat prevention filters and blacklist second is a story of black security misconfigurations for pii and more absurd is about burning or hacking amps with use with the help of query builder and final one is a classic low profile
inclusion with a footprint so what is documentation you may ask um documentation um going by the dictionary of definition of documentation documentation is any communicable material that is either used to describe plain or instruct regarding some other object system or procedure such as parts assembly installation maintenance solution okay so with that with that out of the way um let's take a look at who uses talks any okay so there are a few big names to it first there is adobe or em and there's uber google cloud shopify canva etc so we should reframe that question and it should be more like who doesn't simple search of the term developer talk on google brings up about 444 million
results okay so why documentation or what's the need well talks coming out shifting tight but the core concept of it remains the same first off it helps the readers behave developers or the end user to understand how a piece of code actually works second say plate of solid reference to look back up later third is it provides constant updates on new features and pieces and final one on the most important one is community discussion proposed that provide new insight into a pre-existing picture or maybe some updates about coming on okay so let's go over the first bug of the stock um here we go so it's hacking on this product based company or software as a
service company um so had a really standard documentation as most of sas companies would have so going over why uh this documentation what did i find with the feature to build terrible paint that's what you see is what you're getting now this is somewhat uh that what you once you see is what you get look it looks like you can format the in that conformat like italicize it you can get fold or you can even add an image to it and most interestingly you can also view the source code for the html source for it okay now let's see let's see what the documentation happens to say about you it says standard html tags are generally
supported but for security reasons following html tags and javascript events not permit well this seems like a black list okay so what next it is about concerning development practice really questionable now what our blacklist you may have we are actually entity list or list of items that that are to be prevented accessed now what's the problem with blacklist you may ask there is that at least one other entity be left out and in our case they were quite dirty okay so going over to the documentation again we have restricted html tags uh to be scripted of input button and sdg but what about anchor or what about i frame tag and other tags okay and they have also restricted new
javascript and most of all javascript have been reported that begin with an on that is on click on load on chat etc cool but maybe they forgot about using javascript adding javascript uris to the blacklist cool so now that we are armed with this information let's get hacking time to build a payload okay so we start out with uh the most basic of test that is a blank anchor tag this is the test and then we proceed to you know add again we should have attribute then contact this extravagance.com
uri that is invalid okay so it passes the test and next we try actually and cute from javascript that is bloodball obviously the web for the filter locks it cool so after a bit of a passing i come across that is the same kind of the same but just a little different it is ah equals to javascript documented domain um just uh sp in place of the letter c we have 99 so what is this you may have um enter html entity uh so what are html it is a method to display reserved html guide greater than or less than but you can also convert the normal letters like a b c d f to h terminal so the corresponding
html entity for hashtag 99 uh that we call
that is 1099 simple then the app are then passed into the word javascript that's bypassing the filters and triggering a classic alert here we have stored active interaction so that is done we will move on to our second part of this talk um it was yet another product based company or software at the telephone company you can say that um they had a kind of webinar to interact with potential customers and introduce them to their products or their stuff uh okay so once you sign up for that webinar you would get an automated slack input so what could possibly go wrong yes with configuration so what are these configurations you may have they are incorrect configuration of
system that lead to security issues or security war rebellions so if i were to define euphoria or a moment of stream or sheer joy and happiness as a hacker this would be my hands acted at food.io had invited you to join their workspace crew as a kid sadly i had guest access to one channel only that was returned for the demo but who cares okay moving on contrary to what one might think slack isn't secure by default once it's misconfigured allowing any or all members of the channel to restrict or allow posting in the channel here is a snippet of slack official documentation explaining a bit about it that all members by default can use this feature but workspace
admins or owners can set different permission what do i mean by that it is that any uh any band of person in this invited channel could restrict posting for all of uh the rest there is people that are present in the channel and maybe not even allow threads okay so this clearly highlights the necessity of focusing on granular access controls in an organization but wait there's more by simply querying plaque rest api one could easily dump names emails phone numbers and some people addresses to bi to be such so steps to reproducing this for as far as folks firstly you need to make a post request to slash uh select the default rest api that is slash api
users.list and then you would get a json response that contains the results something like this now it was required to quite a big json file around 7.7 megabytes and it contained 10 of pii so how do we make 10th of this a huge chunk of data thankfully thank you comes just their cup to the same let's say to linux page 2 and big thanks to my friend and dominator nike for helping out with the regions so we do this that we save the even uh json data in a data file and click it out and then pass it to take you with a pipe and use the custom that are flag to occupy custom detects that
beautifies the list of email names and phone numbers that we have so with this speed command we were able to filter more than 3.5 000 unique countries that were of the members that represented the slack channel it's a bit of a proper concept for those who are impressed they also at this picks to that uh also from slack official documentation said by default must uh email addresses are displayed in slack profile but who knows that admins access
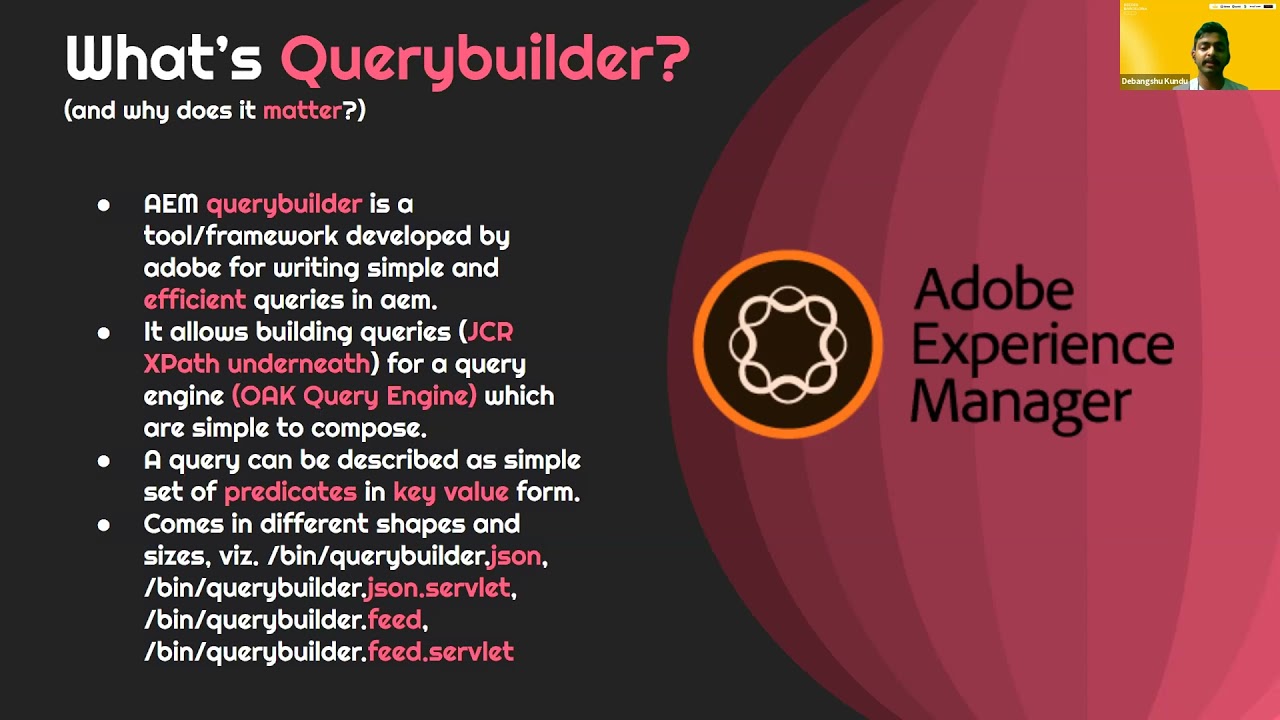
of this stock it is about uh aes or adobe experience management so aerobic manager is a legacy cmf that is getting used by various companies across the world so what is query builder why does this matter so aem perimeter is a tool of framework developed by adobe for writing simple and efficient very easy aem it allows building gtx path queries for both very simple so a query can be defined as a simple set of predicates evaluated and fairly builder does copy different types of slider like when slash query builder.json slash elevator tortoise dot servlet feed and feed dot served okay what now let's start by debugging normal query builder first up is the domain that is psi.com
followed by the path to variable the api that is open squarebill.json and followed by the queries or the stuff that you want to fill but um real world stencil looks somewhat like this there is a domain followed by the password variable api and the stuff for next film and uh multiple splash sheets have white listed extension in order to bypass satisfactory configurations after this one we have appended a uh widely possibly widely detention like css and multiple flashes okay so let's take a bit of a detour what is dispatcher well dispatcher is am or adop experience managers caching on or load balancing tool that can be used in conjunction with a enterprise cloud web server this is how
in the vm environment looks like there's a author intent with replicate to public constant there which is then passed on to the dispatcher and then finally to the general well am prior to murray lee lies on dispatches or dispatchers dispatched on any quality to function as an allow or denied it if certain paths are to be allowed tensions are to be allowed or this uh things are going out that these are denied so an allow rules look somewhat like this like the given allow rule um allows access to any or all folders that are under the folders and files underneath or directly and this is the denial um this would deny any get request to
the given point that is selected here i guess now it's clear that what role the multiple slideshares had allowed extensions that did not chip dot png dot css that are added somewhere on here planes okay so back to query builder time to talk about the actual stuff that would help you in uh coverability and think of a content so here's the positive variable the kpi and followed by the stuff that you want to implement okay so it's time to talk about the query parameters so that you can build queries normally and no longer rely on tool output yes well first up is type equals to entities profile this display list of files that are contained with
application next is type equals these two folder which displays folders that are the application and typically page with free capital that is used for pages next is full texting string this would scrape the entire application for any or occurrences of the given input string well next is node name equals to star dot extension you can specify the delta to be anything like whatsapp whatsapp.txt and jar and store next is path hook this query from the given operation within a specified part like slash home slash okay next is p dot limit equals to minus 10. suppose you want to specify a limit to the number of results you want to keep like 10 or 20. so notice that p
naught limit goes to 10 or 20 something like that or maybe you want to dump all the resultant uh you know files or folders you will go simply p dot limit equals to minus one to extract all that okay so maybe you want to find recently modified items you would go order by equals to add the rate tpr to content flat who is the large class modified this would uh bring about the recently modified uh items or the items that have maybe dev has touched up on recent okay let's talk about property and property dot value so i'm going to give two examples of it in this stock first is property consultation created by and property dot value equals to
admin this would bring about all the files or folders that have been created by the admin user you can specify this to be uh some uh like author or any of the user that you may find cool so next is property goes to create rightlook operator values posts so this would bring about all the files or folders that have secret their title name you can specify this to be anything else like password or something like that okay so maybe you want to turn on multiple parts for group or dot one the score parameter that's path uh so you go group dot one and let's go party first
so this given very would uh confine your opposition area of operator into two folders that is slash app that's like one so time to see some stuff in action okay it's the full text query that i talked about it is for full text equals to admin yeah um as you can see each one of the listed items have am somewhere in their body or title or something they to have a message next is a full textbook called secret and full text equal to all the listed items have password somewhere title or name or
next is the this way this apparently all the active files in the given application so let's break it down first is type equals to at least two pi for fetching files under the path that is called sd and roll depth equals to start.txt okay and p dot limit equals to minus one to fetch all the resulted apps phase results next is the for similar just we have changed the extension to be dot html here the list of html uh compared to txt files here very useful uh okay so um combining queries for better results please take it to the grain of salt and it won't always work depending upon the dispatch configurations that you encounter in the file
so um this is two queries first one and second uh first one searches for all the txt files that are that is directory and the second one searches for um all the html files under the suppose you're gonna combine that into a single query but we do we go simply that's because that is two five we don't need to change that but so we don't need to get that and we group this together group dot one the query that is node name because star dot x
that's it well everything that i talked about talked about is well documented in adobe's official documentation at experiencelink.org.com okay so the one of the final ones of this stock factory school apparently it is this is a classic local file heat or right vulnerability with some other good stuff okay so let's go over the workflow of this talk because uh hacking on a widespread program a white spoke program means that any of all the domains that you control are in scope so i went over to strodan what you showed that it's the search engine that many of us have to choose to find a specific technology or find uh spread into the hosts that are confined to a
given certificate or a domain so i use the talk of filter that is simply to target this searches for or that is called ssl uh certificates for the given tag specified to be google for facebook uh this would search up all the certificates belong to please get google and list all that so assuming the target to be targets um uh inputting this uh i found an id point into top. um upon visiting i find a developer admin panel which was known for uh many of its functions well so instinctively i went over to the application.js file that was in the source code and upon scraping that file i found it relative path that is tms the api plus
scripts pipe and particles hubba well uh upon seeing a path parameter what a hacker would try doing instinctively is a part reversal and ultimately a local five pollutant he did the same that is simple local file inclusion fail dot path type the file that i want to build the password command use for moving look finders
[Music] on this note i would like to put a reservoir who said live love and logo by inclusion [Music] okay i didn't stop on it then the theme is directly here this uh steamed a little bit uh you know out of the box so i went over to my directory booklet for simple that is responses so i wanted only 200 responses and i did get a single uh 200 open spot was it ui page or swaggy by dot
that are available on your website in the ui or graphical user interface format it renders all the api calls generated from your generated from your open api spec with visual lock update so which makes it easy for a that is back and implementation and we get use the wrong question this is what you will mostly encounter in the world but please do take note that and suppose swagger ui security one okay so every function uh swagger ui and api calls that are assigned to different http methods that are used to perform different they get required with some who detected slash directed by the some data and also requests for the same data and delete request to delete the
uploaded data well it also shows the name description parameters required in the api call additionally it also holds the resulting responses after the api call has happened whether it was a 200 okay or 401 403 for the phone that okay so let's talk numbers a bit here um there are about twenty eight thousand two hundred and six public swagger by intensity as well as at the moment of uh preparing system so let's get back to power talk topic um this was the swagger ui that i encountered in a while the first five operations being uh and the sixth operation was the most useful let's take a crusher this is what i would call perfect definition of credo get it up
until it first one the the obvious
okay and this is why you shouldn't leave such api an awesome page simple post request to flash tiabath slash api script slash file um but enough to create any file in any desired folder with any content type tension i have for the demo i have i included a pc.html file and in any desired folder like flash test i didn't hamper with flash any other important folders because that might be catastrophic production and as a result the file gets created in the desired folder that that's next uh is the delete treatment we specify uh the paths to be practice slash dot html uh pass to the uploaded file okay and this deletes the desired file from
one location file gets it awesome well uh final one say bonus fight so about what
by supplying the arbitrary audition i specified my pub collaboratory base of the origin header and it reflected back in the acio or to control origin uh with credentials okay so this is a very simple exploit but uh called composition
successful exploited vulnerability would lead to disclosure of the uh authenticated information pertaining to the reduce good so a few takeaways from this stock first in blacklist aren't always good pro second is focus on granular access control centrifugation soil issues since the human element is very error-prone third is by testing any cms in all public documentation to better understand how it actually works and the fourth one and the final one never leave a sensitive apis unauthentic to complete staging depth of production thank you everyone for taking tuning in and big thanks to besides barcelona for allowing me this opportunity to present my talk and you can talk to me at this historical time on twitter and um for
questions so let's let's give a couple of minutes just if people want to write some questions in the meanwhile uh again as i said you can write questions here in zoom or uh you can write them in slack and we take care of them uh we wait a couple of minutes just one question i'm very curious i never heard about the uh what's called the business adult business experience um yeah exactly how common is it how many instances it's very common uh like uh tesla uses it volkswagen uses it many other company twitter users oh okay okay again for me was like quite it's quite interesting right and i was googling at the beginning very
interesting yeah and i was like oh wow um and i was like okay it's quite interesting let me google and see how common is it because again usually you can find tons of posts at the moment in the wild okay okay i got a big companies second a lot of big companies do not know okay okay i was thinking they were more like sharepoint and all this type of stuff so uh not really sure about that so no i mean we don't have any question uh so far we have uh well just someone who wants to thank you uh nihal was just thanking you and it was cool and it's like learn something about where you build it again i think
everyone just knew something about fairy view there it was uh yes it's a quite famous but like people actually tend to stick to the tool output and usually they don't put much to pertain you know building the queries manually or just trying out stuff that is present in the documentation so that was that's what this talk was about that makes sense makes sense um yeah okay we don't have any questions so far so i would hold on a second okay so hold on there is a question okay there we go uh see for me now uh is there a score is there a course misconfiguration uh often exists in swagger ui i mean president very common uh
it depends but it it you can find it is kind of common but it depends on the you know the people that are building it in the back they do specify the text that say what exists but if they leave it as if it would okay great yeah thank you thank you again so anything that's uh well thank you this was my and all of besides partner uh what was my question so thank you for that absolutely thanks to you uh and again if you have any more questions or you want to reach out to the bank show he's in slack so we can reach out to him





