Unified Protection with The Elastic Stack

Show transcript [en]
hi everyone my name is James I'm here to talk to you today about the elastic security very excited to show you all the latest and greatest that the stack has to offer and when it comes to security analytics stress hunting incident investigation you know so on and so forth just very briefly about myself so I'm a security specialist at elastic typically working in the AMIA region and I've been using elastic for a very long time quite a few years now during the company just under two years ago and what I do is essentially help our users community or our customers it's how they can deploy and use our technology for security analytics obviously over the past couple of years
we've been really focused on making that experience easier so you know even though we've been used for security analytics for a very long time and initially it was for the mainly for the threat hunting use case just because of how much data elasticsearch can store and search to very quickly it became very popular as a way to start you know offloading massive data sets for threat hunting teams as time passed by though a lot of our users started to go beyond that they really wanted the traditional security analytics and seam capability that most of their existing tools provided because they already had all this data inside of elasticsearch so literally just under a year ago now June
2019 we launched the first version of our sin and our goal was really to try and simplify that experience so we didn't want users to have to spend you know months of building their own rules or creating their own dashboards things like that we really wanted someone to just start deploy and start running things immediately that's where this security portion really comes from there's now a lot of content that you just get simply by downloading the free version of elastic and and running it there's literally very little for you to do however if we did want to you still have all the existing functionality so if people did want to create their own custom visualizations if they didn't
want to create and editing when it comes to customized content or data sources or feeds that is still all possible so we didn't take any of that away we just added a tremendous amount of goodness for anyone to get started using security on elastic very quickly obviously as being an open-source company we have the leverage and power of the entire security community so even events like this one you know it really shines and shows hey here's everyone trying to collaborate to take away this or try and reduce the security problem and you know elastic is used very heavily in that space a ton of community projects elastic so you know things like the helices ooh rockin a same security onion
there's so many dimension and that's really really refreshing to see everyone coming together and trying to solve this problem and the last thing is at the heart of many of those projects I'm not going to mention on one slides I'm going to dive into a demo for the most parts of this presentation but I didn't want to highlight for those of you who might not be too familiar what the technology stack looks like so it's let you just kind of stay on the slide and just talking with about how elasticsearch is where we're gonna be storing our data so think of elasticsearch as the as a datastore in fact that's what it is elastic search is designed to be very
scalable so you basically add more nodes as we say as your data grows or as your search needs grow it's horizontally scalable fully open source you download it you run it wherever you like and it just grows as you need to grow we of course have several different ways of getting security related data or any data into the stack so today we'll be talking mainly about beats so beats are very lightweight the shippers that you can just install on a host anything with an operating system really pick what data you'd like to send to the elastic stack and you're after and you're good to go most of the what we're going to see today is our own beats and we do also
have an endpoint solution now and we're not gonna talk too much about that today just because this is a community event and you know we're going to talk about what anyone can just go and download that run so we'll be talking mainly about beats today but we also have lock stash as well so block stash is the traditional way let's say the traditional way of getting data in so box is more server-side components you said unlocks that server we start streaming data into log stash over syslog TCP may be read from revelation database query and API whatever you want looks such is also a full transformation tool so if you needed to change your data you know
rename fields send it to multiple different outputs you can do all of that at works - in fact if you've heard don't you know the extact that's where this is coming from a search box - gabbana after the introduction of beats a few years ago we decided to you know start branding it as the elastic stack because BL core bellick or lb doesn't sits very well on the tongue so whatever you want but this is why I would want to be masked exact as opposed to the exact these days but again you're free to call it whatever you prefer so okay I'm not a big slide guy so I prepared a demo for you today and just
to give yourself context into what we're gonna see as part of the demo so I have a Windows Server machine and which is just your typical deployment of Windows servers running out of Amazon ec2 there's a couple of our beats on there so I have packet between lock beads and so packet with is looking at packet data on the wire so it's literally a packet data flows over this interface or something interface on this machine where we're picking it up and we're looking at things like DNS traffic TLS handshakes flow data so a tremendous amount of stuff we're looking at will not be it is there to look at Windows events so your traditional security
event log application anything you want you can literally specify any Windows eventually as we need to collect so grab it parse it and send it to the elastic stack in our case we're also gonna be using system to enrich what we're able to do and detect on on Windows so obviously I'm sure most of you are familiar with system on fantastic tool by sysinternals literally if you really want to do security analytics and you know collect forensic information for Windows this one is the way to go and to help and really highlight how much community has helped here I'm using a consistent configuration by the community by all of Hartung some shout out to him he does a
fantastic job with this configuration he actually built a modular way of adding in different system own rules and which is fantastic and it's also enriched with the mitre attack framework so I'm sure most of you have heard of this country to walk outside today without hearing my framework so we're gonna be using that and diverging the mitre attack framework and it's taxonomy to help when we're doing our investigations and analytics and very simply so all this data from the from these two beats is being sent in this case straight to elastic cloud it doesn't really make a difference where in terms of where your deployment of elastic is I just use an elastic cloud for simplicity but you can have
this and on-prem you can host it in your own private clouds wherever you want there's literally not going to be any difference where you deploy this so that being said let's dive right in and let's start off here so for those of you who have never seen it this is elastic synth so this is cabana more generally but we're in the sim section of Cabana over here and really again what we're doing here is we're just trying to ease people who want to do security analytics without having to build too much content themselves this has grown tremendously over the past couple of months you're going to see a few features here which potentially haven't seen before and
we're running the latest version as of today which is version 707 and we're going to be talking about other parts of Cabana just before I start talking about the same so I will give you some examples there I do want to highlight that all the data that you're sending to elastic can be used throughout any components there you don't have a restriction of just using it in the sim you can literally use this data wherever you like or you need or whatever your team's prefer we give you the content out of the box if you want to use it if you decide I'd rather build my own that is always going to be a possibility so I
just wanted to highlight that alright so in the sim I mean we start off with an overview quite typical so we have a breakdown of rules that are being detected so we shipped with quite a few rules out of the box I think about 130 as of this version they're looking for a wide variety of different adversarial behaviour so we're kind of looking at some of those today you can see within this view they're already mapped to the mitre attack framework so you can see there's a you can split by a list of tactics and change the rule name whatever you want and whatever you prefer as an analyst however you know it's elastic we will take any data you'd
like so we don't you don't have to use our signals again if you have something on your network maybe an existing sim or maybe anything that has its own rule set or alert set you can bring that in and visualize it and what we're calling external alerts so in my case for example I have certain kata and I am running our endpoint solution so those do show up as external routes as well but any device or bit of software that you have which is generating its own alerts they're gonna show up here and you can view them as external nodes so any device or tool that you'd like you can breathe them in here and to just
work well for breaking a lot of events that we're receiving so there's quite a bit going on here so we're going to be talking about that one machine which mainly has one long piece of packet bead but as part of the rest of my sim solution I do have five beads which is looking at things like SSH dogs and then if all the beads which is the cat the or the daemon framework for integrity monitoring so on and so forth so the machine we're going to be working on as part of the the example will not become packet read but there is other data flowing inside of this particular sim instance we also have a bit of a breakdown of you know
what's going on how are people using the sim right now so we recently introduced the concept of cases so as you're going through an incident and you'd like to start collaborating with other people a team or other teams potentially we now have the option of case the train 10 and any recent cases that either have been opened by other members of the team or you can switch to cases reported by yourself and they will show up over here we'll talk about about that in as part of the demo we also have the concept of a timeline of time right it really is an investigation so we're gonna be using the timeline today but any recent investigations that are
happening you'll be able to see them right over here as well as a newsfeed so you know at elastic we do have our own protections research team you know people looking at malware samples writing rulers and we really wanted a nice way for anyone using the sim to get any updates from them as quickly as possible so instead of us sending out like a marketing email or sales email because most analysts don't see those things we publish them straight to the eyes of the analysts which is pretty cool so you basically as as we're working on new stuff we can publish them send them here and you'll be able to see them as someone using the sim pretty
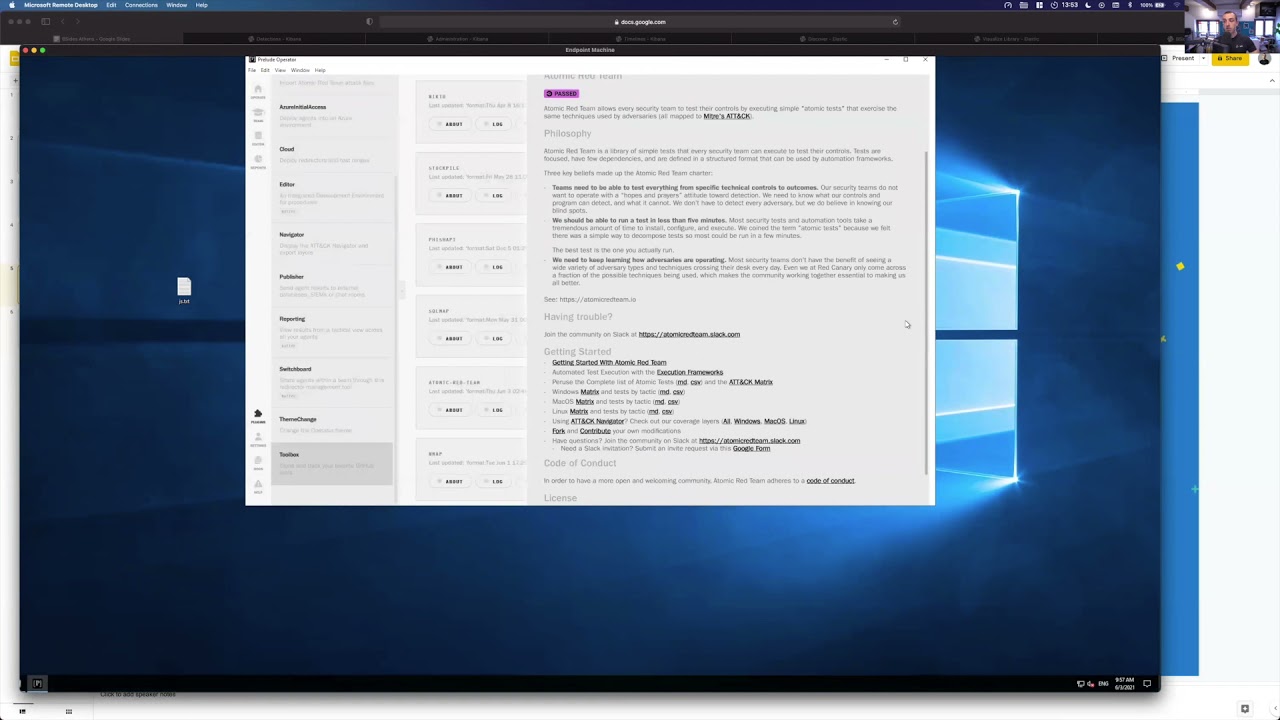
much hands-on and this is configurable so you can turn it off if you're not interested in this in the future we're probably allowing you to configure your own newsfeed but right now it's either elastics or you can turn it off let's go ahead and for the sake of this let's dive into our detections page so again as of this version we're shipping with quite a few detections out of the box and just to give you a bit of context into what we're going to see here so that machine the thing has let me bring it up here second so I made a mistake I said it was Amazon in the slides actually at Google I did I
remember I did change it so I apologize for that minor detail but on this machine I have those beats running and I definitely this malware sample so and I'm sure some of you are familiar with this was from the helix or apt 34 group and it was a phishing campaign sent this email at the word document with a couple of macros in it and as soon as you click on it and enable execution starts running a bunch of stuff so there's actually still going on so it's it's it was still running up until a few hours ago and so I want to show based on this real sample what you're able to detect and investigate pretty much with the
out-of-the-box configuration of the elastic stack so again I haven't done too much custom work here at all in terms of the sim it's definitely what you'd get if you went and downloaded it and ran it today and the same from the data collection perspective so the beats are the out-of-the-box configurations and plus the the systemö configuration which is on all of github page so um this is all literally like downloaded and started running I haven't spent hours or months or weeks preparing stuff in terms of contents I have to detect so that's running there so I just want to give you a bit of background on that and let's see what we were able to detect so
um I said this last night just to prepare for the the presentation but it was still going up until this morning and I do want to show what was initially detected when I ran the sample so you can see here immediately after Fritz the scroll let's order these sort by timestamp within the same in the detection is view your you're gonna be able to see everything that's being triggered for your environment you can see here after I ran that sample immediately had some events from system on start to trigger so it seems like windows script executing PowerShell and we did have some alerts from our endpoint so this would be true for your own endpoint
solutions or whatever used to be used and it's one of the reasons why I mix that in just to see hey whatever data set you're using it's going to show up there and keep scrolling down we see again local things like local talk show it has been created and like a persistent pattern of that windows script executing PowerShell and I believe there's a few more as well things like DNS tunneling and we're gonna talk about this in a second so on and so forth so you can see at the time that something was ran a lot of stuff was affected just by the out-of-the-box routes which is pretty good to see so he was an analyst you're already able to
tell hey you know this was a real word sample and I'm able to detect a lot already without having to do too much work myself now on that note like how would an analyst starting esta gating written so yes there's a nice breakdown signals and we got a list of what's being triggered how do I start investigating so there's a couple of options here and again we're gonna be using the the concept of the timeline that we have so let's say and if probably if I was an analyst first of all I'd probably sort by severity score especially if I'm saying that I had a lot of rules and trigger for the same host so you can see
in this case they're actually all for the same also if I wanted to one of the ways I can do it is that sort by the risk score for example and then we can start from the the more important one so this is one way of doing it but and my case that the way my brain works is I might want to dive natively into this host view just because I can see there's so much going on for that same host so why don't we do that if I click on this host it'll actually take me to the host view in this case just a few things I want to highlight here in terms of what
you get as part of the data collection process so the beats themselves they're not just collecting the events but you can also see here there's collected a tremendous amount of metadata about the host so again this was Windows Server 2019 and it is running in GCP so this is metadata collected automatically and so like there's whatever cloud provider it is it's automatically gonna try and query for the the different providers pick up the instance IDs and things like the interfaces so on so forth and you notice here there's an anomaly score and this is actually based off of that DNS tunneling event that we saw so I'll talk about this in a second but essentially
one of the things that matter where the sample did was and it did really an estimate so we were able to detect it with the machine learning job in this case which is fantastic so like even for you as an analyst to get peace of mind that you have you know the concept of defense-in-depth we had and you know alerts trigger from the same perspective so you know the static rule it's a traditional way which is which is great and everything should have that but beyond that we're able to sort of model this behavior and spot something else based on something which is a bit trickier to do statically so we're modeling all these DNS requests
and spotting potentially unusual ones based on things like hey how long is the DNS subdomain as an example so that also was triggered here and we did get an alert for it - then I have some views that I can start using to really help the investigation or even before the routes triggered you know the concept of hunting proactively we give you a few views to start off there so for example we list out things like the successful and failed authentications things like on common processes so here we can see everything every process that's running but also its arguments so for example right now I'm saying immediately there was instance of cobalt chrome which had
12 arguments things like shall do tasks created but something will probably want to investigate shall do tasks itself on store by command prompt and those arguments there things like word running so and so forth PowerShell W script so I have a few options like I can start to terrorize here what I want to potentially use to kick off my investigation either after something triggered or even as I'm hunting remember if we decide to do proactive hunting this stuff is still gonna be available and you so you have multiple ways where you can start theorizing what to look for let's work on this partial activity here so there are 56 instances of Parrish and in fact
these pretty much relates to those detection that were seen and if we look at their arguments there's a bypass argument which is already strange in itself why are people or things why people try to bypass the execution policy there's also this Apple ps1 script like for me in my eyes I don't really know what that is yet it might be did you submit it might not be so why don't you start investigating and here's what we're gonna use the timeline so I'm gonna open up this timeline that we have on the side here and what the timeline allows you to do is really start off an investigation without having to write a massive query so I can literally just
grab PowerShell put it into the timeline and this is gonna search for across all my data sets across all my hosts where I have processed named PowerShell this is using in the background what we call the elastic comment schema which is essentially a fief naming convention which is really handy if you want to search for the same thing across multiple different data sets across your entire environment if you're using the beats again this is something we do for you automatically if you bring in your own data sets there's much more ways you can adapt to the common schema it's actually totally open so you can actually commit to the git repo if you want and submit a pull request for
adding multiple data sets so it is a totally open schema as well as soon as I drag that in there you notice we're seeing quite a few events again I'm gonna go sort by timestamp here just so I get a more chronological view and immediately the first event we see is a creation event happening from the endpoint you see process create from system on and for most of the event types not all of them yet but we get there we do this work to call event rendering so we try and make it really easy for anyone who's doing an investigation to just read what's happening without having to necessarily open up and collapse the full events
because some of these events you know they're very long they're gonna have a tremendous amount of data so wherever we can we play it out like this so basically this is saying James in this domain this house started PowerShell and these were the arguments via this parent process so I can already see that the parent process of this partial script was W script why is W script calling PowerShell as an example we can see a lot of different stuff already so there's quite a few DNS events going on and we can see that it's really a bit unusual the subdomains are quite long and strange and they're all happening for this with your face that com domain
again you can see it's very easy to read something a DNS request so it's pretty cool to have that the event will be rendered differently depending on the data type and depending the the data set so I don't know if I have an examples here but if you had things like flow events that show up and this will show you like the bite size and things like that so it's pretty cool it makes it much easier as an analyst Ajay to digest and read and remember if we said this is enriched with the mitre attack framework ten resolves both to the rules that being triggered that's something we do for you on the suicide but this data is
coming in if you wanted to use that to aid your investigation of course you can do it so what I'm going to do is I'm going to enable those columns just to help us and see if there were any um you know mitre tactics that were hit as part of this dataset and let's go ahead and filter these down so it makes it a bit easier and you can see these are all categorized by the type so I have a tread type here and in my case I'm gonna enable tread technique name and so technique ID all right so now I can be able to see them here and if I have any events roulette hits like I'm saying here
PowerShell I'm seeing the ID I can use that to my advantage so if I wanted to I can just continue to narrow down my query by dragging one of these elements into the timeline so why don't we narrow this down a bit you know I was interested in the like the bypass argument specifically like that's probably gonna narrow down like the events I might be interested in most but I can also do like hey let's just dragging the parent process I can also instead of dragging and dropping if I'm not too much of a fan of that I can search into the dictionary way as well so why don't we do like process orbs and
you can see how we're suggesting here that quote fields are available and we can do something by class go ahead and do by bus fields args our mistake and now we get all the events from all our data sources where we had process arguments that contain bypass script so we narrow that down quite a bit again we can see quite a few PowerShell techniques we expect and yeah so we're starting to narrow down our query doing our hunt maybe I wanted to only include where I had this argument as well so I can just add that to my query see what's happened there as I'm dragging again I can also decide between an and or an or
so if I drag the time there needed to be an orrery so depending on what I'm looking for and so on and so forth so I can keep doing that I can keep narrowing down my query before we saw that with your face that come domain so maybe I can do something like this right so I can even actually from here drag into the timeline so I can just add it doesn't as an or query and I'll also get those events as well as they come up so it's pretty cool I can build sort of any sort of search that I'd like either based on a theory based on a hunt hypothesis or even based on the routes
that's where children so just to recap we started this off just because there were so many rules it's triggering for the same host and then also machine learning told me that there's an anomaly around the same time as well so it just starts to put two and two together and as I'm building these hunts or these investigations I and save my queries if I can use it either in any other parts of Cabana or any other part of the sim as well so literally there's a Save button here you can see I give this demo a lot but I'm gonna name it the same besides I save it and this will allow me to do whatever I like with it laughter
so I don't have to start from scratch we can create our own detection rule based off of this so if I always want to support this activity we can and and even within the timeline itself what we've tried to do is to keep it more interactive we allow it to leave notes so even if you save this right and someone wants to come and we reference it again so let's do demo here so even if you don't give the name it will persist but let's say someone wants to reference hey what was James investigating during this besides demo and I can leave notes for them I can leave notes for any other member of my
team or perhaps an auditor or something like that we support markdown syntax here as well so if you want to leave screenshots images you can do whatever you like so we do support that at the timeline level but also at an individual event level so as I'm going through these events I can do something like you know hey this is spacious I've so-and-so to investigate for example and I can leave all my step screenshots again what I'd like at the note and it will keep track of who left it and that's what time so keeping all track of all of that as well the next step from here would be you know I'd start collaborating with multiple people
like formally like let's create the proper incident to start responding to it so you know this is happening on an endpoint maybe to start cleaning up let's get rid of the PowerShell script let's make sure the DNS tunneling isn't effective and blocking out the natural connectivity for example so we write from it in the same timeline I can go in and start a new case so I can say attach timeline to a new case and what this is going to do is it starts a case creation menu so you can see here again resize case I can add tags I can do whatever I like here and you notice in the markdown syntax for the case we've automatically
the link to that time right but if I have done any prior investigations or any other investigations and other timelines I can also include those just by clicking this button so you can see how several timelines being worked on I can just go and add them here and again the full syntax of markdown is available can create the case and it will automatically create that case for me it's a automatically I did click on the button and and you can see it's currently open for two seconds here the reporter here is the reporter here are the participants so as other people starts chiming in here and maybe leaving their own comments and things like that
and it will they'll appear in the participants you can also link back and quote any particular comment block so it's very interactive and you can see here I have a similar case which I pre pre-loaded doing the same investigation I did links to a threat report I found online where I was focused on that with your face dot-com domain and Michael Scott chimed in here you know to clean sucking up the end points but he did another investigation and found powershot stuff so and it can be really collaborative if you need this also feature here if you have a commercial subscription to push to service now so that's also an option there if you have service now in your
environments and you send it there that is available and we'll be adding more systems and the comic releases but it's pretty cool to have that capability you just push it as a last thing I'm going to highlight as part of the detection so so far we've seen just refresh this page we've seen what detections were triggered for that rule but what does it look like if I wanted to dive into a specific detection so for example we saw the DNS tunneling 1 what if I needed more information about what that is what's doing what it's querying so I can actually instead of you know going in here and going to the timeline I can just click on one of these I don't give
me all the details I need about that specific rule or the detection so all the information and remember all the ones we give out to the books contain a lot of the stuff including you know micro attack tactics and techniques but also an investigation guide so maybe you're not too familiar with what you should do for the specific technique or tactic and and maybe you've never even use Cabana for analytics right this is gonna allow you to have a really interactive way of showing them what to do and how to investigate so having that markdown syntax in there the super powerful for adding gifts and images and things like that last thing I'll talk about is of course as an analyst you
might not want to you know have to be or you don't have the capability of being eyes on screen all the time so we do have the concept of having external actions so for example here I have a slack words which I built for that same alert so this is the literally the same alert that was sending me slack messages as it was triggering as an example so you have a full customization here and as you like last thing I'll show is what does it look like to create your own rules so you know so far we focused on the 1 so you've had out-of-the-box and there's a very long list of these but what does it affect to create your own
so you can see here this is the list of the ones we provide if I wanted to create my own there's a nice button create in route and then I can create my query and either based off of a query I write here and now or maybe the saved query so that besides query I wanted to use it again you can see it adds the timeline filters and the arguments are within the search bar and maybe I want to focus on machine learning this is a paid feature though so just I like that but everything else is included just by downloading the basic distribution I can add a timeline for investigation I can give a description whatever I like add
in things like the mitre attack tactics and techniques said in my investigation guy pick my schedule and then pick my actions as well so this is what it looks like to create so we tremendously simplify this process for everyone who's tried to do this on elastic in the past just to highlight that now this is available as an option of course and I did say I'll show something's outside of the same and so just to give people an idea like you can use the exact same data to build something like this which we call a campus work pad which is a totally free form drag-and-drop way of looking at your data and I've drill down so for
example these would actually make me back to the sim and this is based on that mitered from that system on config so you can utilize any sort of tool within the rest of Cabana that you want we have things like our maps where you can have different layers and join different data sets and we have things like graph exploration so there's a bunch of different tools that you can use so you don't have to stick to the sim you can use any other part of Cabana to your advantage well thank you all very much I hope you've got a better understanding of what we've been working on at the last from security perspective and there
is a Q&A after this so please feel free to ask any questions if you need thank you very much enjoy the rest of the conference