Treat the Problems, Not the Symptoms

Show transcript [en]
up next up we have Eagle Goffman with treat the problems not the symptoms baby steps to a more secure Active Directory environment alright thank you so welcome everybody and good afternoon my name is Eagle Goffman I've been doing security more than 10 years now and right now I'm working in small start-up called xn cyber we do automated security testing focusing on running blue team simulation and prior to examine our work at Microsoft Research in different Active Directory techniques and how adversaries can exploit Active Directory working on some different solutions so we are here to talk a little bit about Active Directory security and we're gonna discuss some fundamental security issues exist in most active directory
environments and how attackers can explode those and also review some security controls and defensive solution that try to solve the symptoms instead of focusing on solving the real problems so if there is one thing I would like you to remember from this talk is that if you don't fix those fundamental security issues you leave your network vulnerable to different type of adversaries and it doesn't matter how many security controls or defensive solutions you will put in place into Active Directory infrastructure you still leave your network vulnerable to different types of attacks so let's review some use cases of real attacks that happened this year so the Singapore healthcare data breach that happen last year basically more than one and a half
million of medical records were compromised and even the Prime Minister medical records were compromised and this attack is the classic attack of Active Directory a attack that happened on a customer environment and a large number of vulnerabilities weaknesses and this configuration could have been prevented before the debrief started so basically those guys released a very long report describing how the attack took place and the key parts I learned from that report is that basically those guys perform a penetration test a few months before the breach started and discovered a large amount of different vulnerabilities and misconfigurations on their Active Directory infrastructure but they didn't invest enough time to fix dog so they didn't want to invest enough time for fixing
those so you know all what happened afterwards so there are three fundamental things I would like you to think about throughout this presentation 1 do I follow the least privileged model - what do attackers really need in order to move laterally on an enterprise network and 3 how can I make it more expensive for the ad reserves and those are three fundamental questions that should change your security mindset so every time you're adding new security controls or every time you're evaluating your Active Directory infrastructure you should think about those questions and those will help you think more like a hacker all right so before we go and speak about Active Directory attacks and the trends that we have today we first
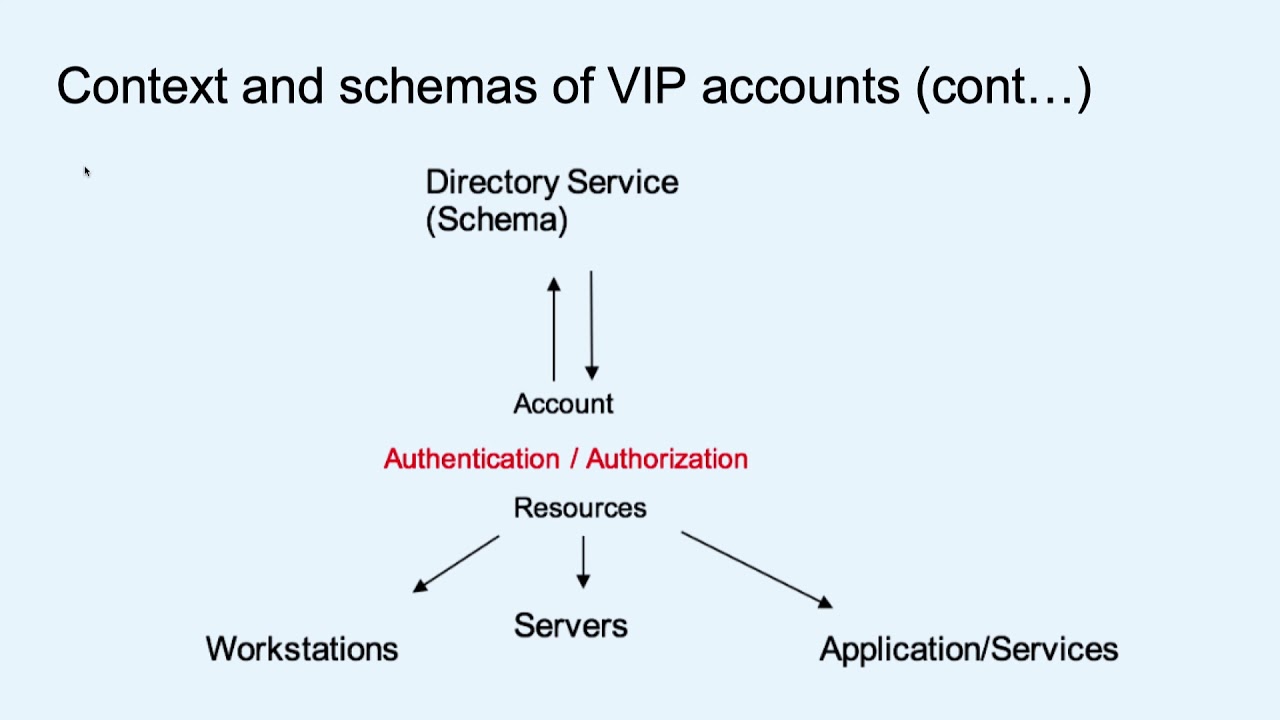
need to discuss several basic concepts that used in Active Directory and use on Windows system so the authorization of implication model of Active Directory so local security Authority is responsible for all authorization and authentication on Windows system there is a local process called the elseís process and this process is responsible for all those implications and authorization mechanism on windows access tokens are the result of successful authentication against those endpoints so if you are using Kerberos or ntlm to authenticate to endpoint machines what happened after a successful authentication is that the elseis process will create an access token and that access token include all the permission and all the necessary user rights for accessing local resources access right and privilege are
also important to Active Directory security so an access rights are enforced on securable object and privileges are also very important and enforced locally on my machine so you can deny all the specific user account if you're using privileged you can allow or deny specific user account connecting to endpoint machine and by doing so you can reduce the attacks of Active Directory logon types are also very important to security and there are a bunch of different logon types but the Windows system uses some of those can live credentials on the target system so if your administer to use the wrong gun types to access and manage your workstation in service they can leave those credentials on the target systems
and if one of those system is compromised it is very easy to use those credentials later in moving people the network of course trust relationship also very important to security and there are a bunch of different relationship between different domain forces on Windows so we have external trust to a trust one on trust etc and if you don't understand how those translation works on your infrastructure again you leave it much more vulnerable because sometimes if one domain is compromised advisors can exploit very simple miss configure domains to later remove and people to different domains or different forest alright so also delegation of security rights is also a very important concept of security so let's say your help the
state need to reset passwords for internal users instead of granting them high privilege account what you can do is grant them a specific access a specific security right to just reset password instead of instead of granting them high privilege account and again by doing so if you are using delegation of security rights in the right way you can minimize dramatically the attack surface you have in your ad infrastructure and of course delegation and credential delegation is the hot topic right now there are bunch of different attacks that adversaries used to exploit a delegation and some of those delegation setting on Windows are considered to be legacy settings and should be never used on modern Active Directory
infrastructure alright so Active Directory attacks office so credential tab is the most famous attack techniques in Active Directory I think it's one of the holes the most hot topics in the recent years and there are many security controls in many products that say that they protect you against credential theft but actually most of those endpoint solutions work mostly on Windows systems and still your Linux servers in your Mac OS rotation are much more vulnerable to type of credential type attacks so you should pay close attention to those links and networks OSS if you have some kind of hybrid environments in addition to that Active Directory attacks also have the huge attack surface including different tactic in different techniques RPC
protocol for example use RPC protocol access control is abuse of Active Directory object cable hosting which basically means brute-forcing encrypted part of the Kerberos mechanism so attackers can just request many different service ticket and try brute force loss offline the ligation of which we will speak about it in a minute and group policy view so if you have a count that is compromised and that account had ownership rights or it's some kind of write permission on a group policy that means that all machines that managed by those group ology policies or all users that managed by those couples are compromised and different general windows attacks such as faction infection session hijacking which speak about a hijacking LDP or SSH
session and of course those can also easily be exploited Service ejecting speaking about getting a compromising account that has high privilege running under high privilege such as domain admins and of course token manipulation impersonation which speak about how attacker can abuse active session and active token on Windows local machines instead of stealing credentials so credential stamping is the most famous technique used by attackers on readiness in the last couple of years unfortunately despite its popularity there is no simple way to protect yourself again this type of vulnerabilities and Microsoft invested a lot of time trying to defense again credential type so they introduced into use they added multiple different security controls that try to protect
against credential dungeons such as LS a protected processes protected user groups Alice a credential isolation in virtualization on the other end Linux and Mac OS are still far behind Windows so attacker can choose a different paths to attack your environment itself focusing on your Windows machine they can steal those Kerberos ticket from Linux or Mac OS and in that way they can compromise the whole domain alright so let's review some a simple example that was recently published so this one ability was published by Lee Christensen from Spectre ops basically if we have a compromised server a windows compromised server that running on an uncontained delegation the adversary can send a simple out PC packet to the domain controller and
basically we have two businesses here in this vulnerability the first one is that an unconcerned delegation that should never be used is compromised and the second ones that the domain controller running ESPO service and spooler service on windows system is responsible from print for print jobs and there is no reason that those Pula service will run on domain controllers but for some reason Microsoft decided to leave those on all domain controllers by default so we send a simple RPC pocket to the spooler service and then the spooler service will authenticate it back to the compromised machine and by doing so he will leave this ticket granting ticket of the domain controller on the attacker machine so now that Acker possess
ethical grunting ticket and this ticket granting ticket belongs to the domain controller machine accounts and we can simply DC sync all passwords from that domain even more than that sometimes if you have two-way trust relationship between different domains first you can use this a simple attack to jump to different forests or different domain so again a very simple technique mostly using misconfigured Active Directory settings and that's a very high topic and very high attack that was published on Twitter by diligent speak about how you can exploit exchange servers to letter remove and to sync all domain password so again if you have unconstrained delegation that is compromised we can just send this section server a simple packet
requesting push notification on some email communication so after sending this packet exchange server will connect back to the compromised machine and again by doing so he will expose this ticket granting ticket and now the attacker can use this ticket granting ticket ticket to change some permission on Active Directory so what they discover basically is that this machine accounts it belongs to the exchange server participating on some high privilege member groups that belongs to change and one of those groups have the modified permission on very important Active Directory objects and basically Edward cells can use that settings in order to add themselves the necessary permissions to this is single password so again a very simple attack and a
mostly using miss configure Active Directory settings and I access list right so there are no magic bullet for good security so today's security controls and defensive solution range there are a bunch of different solutions ranging from the most simple values such as a restriction to the most sophisticated ones such as IPS protection intrusion prevention system endpoint protection and India and although solution mostly tried to fix symptoms and not solving your real Active Directory problems so if you deploy only its security controls if you add additional security controls you don't fix your fundamental issue you still leave your network vulnerable so as a set of switching credentials are basically try to protect your bed against credential theft multi-factor
authentication used by most loyal to the organization can introduce additional point of failure and admins can use those pointer fellow in in order to bypass the second application there so on Windows there are many a protocols that don't support multi-factor authentication so if users are able to compromise strong accounts they can easily bypass multi-factor authentication so you should check your multi-factor authentication solution and understand how those work and whether a point of federal remote access encryption basically doesn't add any security at all so encrypting data doesn't end security and deception was is a hot topic recently there are many different deception solution that try to add some horny traps on your infrastructure on your endpoints for
example sometimes they try to inject fake credentials into the else's process hoping that adversaries will dump those credentials and use those and in the end then we can identify those adversaries but in fact advanced adversary's or sophisticated vs. can easily detect those injected credentials there are bunch of different registry settings that you can look at or Active Directory attributes so we can very easily identify that those credentials are not used as commercial dormant and and just bypass those and of course intrusion prevention endpoint protection and ETL solution are becoming much more sophisticated but if you look at real use cases and there are bunch of different real attacks ranging from ransomware to advanced a PT's all of
those loss Prudential's all of those use some kind of version of mimic cuts but those idiot solutions still have a hard time identifying those on many cases so adding security control is a good step but only after you fix your fundamental issues if you don't fix your fundamental security issues if you don't you stick your high privileged account if you perform some operational active drugs and just add additional security controls you just make it much more complex it you don't add any security all right so LS s protection was added or to Windows 8.1 our LSA processes can be SSI protocol process can be easily bypassed by using kernel driver so if adversary you scan a driver they
can easily bypass LSA protected processes so Microsoft decided to introduce credentials well on the Windows 10 system and a credential guide considered by many as a very sophisticated mechanism and a manual security hitman but it has one huge limitation it prevent attackers from stealing secrets from a compromised system however it does not prevent them using those secrets on the Cobra my host so let's say a more specific example on the left we have a machine running Windows 10 and running credential yard so VTL 0 represents a virtual machine running the normal operating system VTL 1 will present a second virtual machine that is running an isolated kernel in this scanner running a special process that's supposed to store those secret so
if those this VTL zero machine is compromised and attack you run mimikatz then they can't steal secrets they will just get any cryptid below but Edwards's can use different techniques to bypass those so a simple token impersonation can be used in order to laterally move your network and access other workstation and all servers even mode simpler than that dead muscles can just hijack your RDP session and again move laterally and PBOT your network and even mode is simpler than that horses can run key loggers on your local machine and might book so they can steal secrets so all of those techniques are very simple there are a bunch of open source tools that can be used in order in order to perform
those attacks and they can be performed but not so sophisticated vs. but what happened if an advanced adversary are taking your environment well they love to go a bit deeper lower layer than the hypervisor so if they came from compromised the Intel a me or the M PSP that basically means that they controlled your entire machine so they have full access to your own memory and full access to all devices and then easily dump those credential instill those credentials from VTL one virtual machine so again adding additional security controls is a good step but only after you streak and handle your basic fundamental security issues on your Active Directory all right so baby steps to a more secure
domain so before we continue and speak about this les les section I want you to remember that regardless of the tactic used by adversaries the target remains the same finding credentials with broad permission the adversary only need one valid high privilege account to compromise your entire domain and therefore our goal is to reduce risk so you should follow many different small steps in order to reduce risk on your Active Directory infrastructure and there are a bunch of things you can do you can deny Network logon to all local administrative account you can mark a high privilege account and sensitive and by doing so you disable delegation and if you disable delegation you can't use a delegation attacks right so simple
steps and if you do those steps you minimize your attack surface you can use edit delegation instead of using built-in admin groups you can force SMB signing all your critical servers on your crown jewels a bunch of steps you can simple steps you can follow to reduce risk right unfortunately we don't have enough time to go over all those steps so we have I built a simple a mitigation model based on configuration complexity and this model will guide you in the right direction focusing force on more simpler steps right so you should start at the bottom so at the bottom you can see different levels of complexity so first it should review local workstation servers and that mini counts
you have on those servers you should make sure those admin accounts don't use the same password and you should restrict access for local administrative accounts then you should review privileged account and groups in Active Directory there are a bunch of built-in groups such as domain administrator enterprise administrators a group operators all of those all those groups have this equal powerful if you compromise one account in one of those groups you can easily add yourself to the second group of the throat to the third group so even if addresses are able to compromise one account basically that's it's a game over for your domain so it should review and reduce risk you should remove many of those users that
are participating in those high privileged group to the bare minimum right Microsoft recommend using only one domain admin user for pair pair domain all right and sometimes you can use G technology and not use domain that means at all after following that step you can identify service accounts with high privilege and again if when we have evaluate a different customers we find excessive number of services running under domain admin privileges and it's a very bad practice there is no reason services to run under domain admin account you can use a super mission you can you shouldn't use never it should never use active Active Directory domain administrator will never for services use previous options workstation again
the use of practice boxes in speak about separating administrative tasks from normal operation so if your administrator need to browse the internet on it to read emails he can use the virtual machine in order to do that and if you need to manage Active Directory he can he can use the privileged access workstation to manage Active Directory and this machine is usually hardened with very high restrictions and of course identifying your aliens identifying your critical asset is one of the most important things you can do for your environment if you don't know where are your crown jewels you don't know how attackers can attack you you don't understand where all the choke points how ad verses can
get to your crown jewels so you need to identify those you need to harden those you need to enforce different settings for those using group policies you need to force SMB signing you need to seek administrative access to those a critical asset and of course you need to log in and monitor those critical access constantly and the last step that microsoft recommends doing is implementing the administrative tier model and it will take you time to implement that minutes of the tier model something from four to six months approximately depends on your organization size but if you implement this model even if you implement part of this model you can you do you do significally Active
Directory attack surface so let's review here we see a bunch of different workstations servers Active Directory in different database when users come to the office in the morning this login to the local workstation and perform a bunch of different operation those machines communicate with each other in different ways and you see those two red lines that means that administrative account connected to those servers or nas in this workstation to manage those machines once they do that they expose the credentials of those machines so if one of those servers or workstation is compromised users can take those credentials and basically the whole domain is compromised so what you can do you can enforce that mini set of terminal and
that means F of T model basically means that you separate different workstation you identifying a service user service accounts and those need to be classified to belong to only one tier so each tier has its own t administrator and each team has its own active Active Directory and you can see that from tier 0 you can't jump to tier 1 from t1 you can jump to tier 2 also if you don't have the time implementing that model what you can do you can use different logon times to administrate your workstation so instead of implementing this still you can use non interactive logon types in order to administrative administer your workstation under the second or the the first tier so if
you're using Network logon you don't expose your credentials on the target system so attackers if those machines are compromised attackers are not able to steal credentials because there is nothing to steal ok so what one times is one of the most important security features that has on Windows and you should use those wisely and here's a big list from the best practices of Microsoft and bunch of different community tools and built in tools into Windows that you can see some of those use interactive logins in live credentials on the target system and some are not using those so for example if you use PowerShell win RM you don't expose your credentials so if you use MMC you don't expose your
potential but if you use PS exact you expose your credential on the target system right thank you very much if you have any questions if you have any questions you can post them to the to slide Oh or we can just pass the mic around no it does looks like we're good um so on behalf of Eastside San Francisco I would like to thank you for your presentation today Thanks