Burping for Joy and Financial Gain

Show transcript [en]
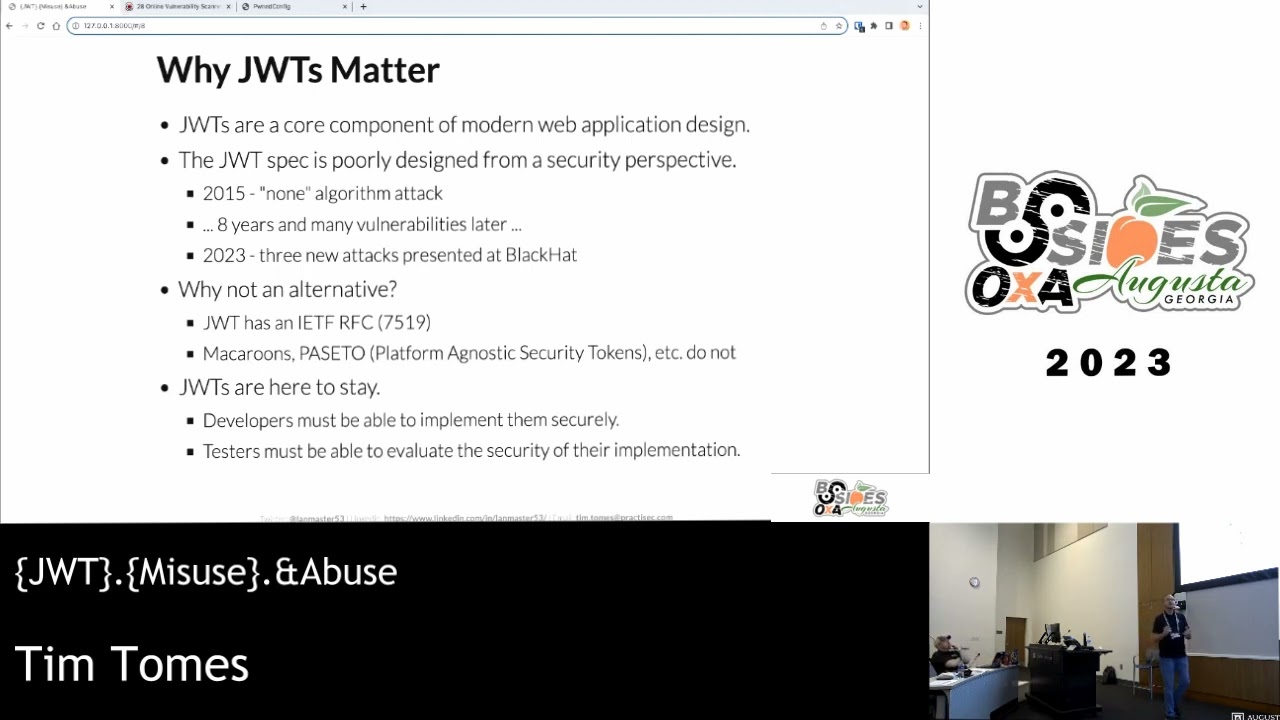
I'm pretty loud as it is expect to be too many problems with that all right so this is burping for joy and financial gain as you can imagine we're going to be talking about burp suite by the tool by port swagger I'm as far as kind of the title where it came from I've always told myself that I would never go to or give a talk the head for fun and profit in it and service is my way of using that without actually using it it's a little against myself so Who am I Landmaster 53 for those of you that are into the Twitter thing and social media you can usually find me by that
handle a husband father and veteran those are my priorities in life a coder so I do some do some coding I wrote a tool called recon ng and a couple things honey badger framework I just I really enjoy writing code been doing it for most of my life it's kind of where my passion lies in software which is kind of how I got into application security in the first place it really was a natural transition for me I also consider myself a breaker as of next Tuesday I will be a freelance consultant working under my own company called practical security services currently I work for a company called envision which is a software security firm I'm a
teacher independent instructor I used to teach for sans used to teach at blackhat so on and so forth but lately I've kind of taken training over on my own under my company's LLC and I teach a course called practical web application penetration testing a wapt you may have seen it or heard of it around so I did the teaching thing it is a it is a port swagger burp suite or port speaker preferred training class for Bart so it's on their web site and stuff if you're interested in that you learn a lot about burp in that class a whole lot some of the stuff we're going to talk about here are things that I expand on a
little bit more in the class I'm also a share a blog and post things and my projects and everything at WWE three calm and I do all of this stuff because it's what I believe I was created to do and I find great joy and serving out my god-given purpose so that's why I'm here today alright so my outline you can see where you are some sort of joy or the ability to make more money so probably we'll see maybe maybe not so our disclaimer here [Music]
[Music]
[Music] I'm just going to teach you based on my experience and that's kind of what I'm here to do so naturally take that with a grain of salt so the first thing I want to talk about with embark like I said simple stuff [Music]
[Music]
different endpoints with intruder right you might want to be able to name this thing so later on in the week or later on the assessment and you go back and you want to reflux or relook at some of those results quickly and see where you're at so let's bounce over here to - burp and pone tub real quick and I'll kind of show you how and why I use it that way so phone hub is an application that I wrote it's the source is available I don't necessarily consider it open source in a sense that I don't care if you use it for personal practice and demonstrations and stuff like this but I would prefer folks not take it and
then use it in a class or something to make money with it that's kind of my intent for it so I'm sharing the source code it's a flask app so it's written in Python and it uses some react on the front end and some other stuff as well but this will be kind of the app that we used to demonstrate everything that we're doing today all right so basically I've got a soap web service built into this thing and here it is and of course we want to pull down the wisdom file for it you have the wisdom file here and if you use burp then you may or may not have played with this extension called
wisdom which is a really nice extension that will parse wisdom files and give you the ability to it'll create a sample request for the soap web service and then it'll give you the ability to interact with it floods different parameters and stuff like that so what I'm gonna do here is I'm gonna go and find this in my history where I loaded that wisdom file right click on it parse it and if we click over here and whizzed alure you'll see that now we have we haven't one operation in this service called tools okay that's here is a very claim very plain to seeing we can see this it's obvious now here if we click
on that we have our sample recruit pressed we can right click it send it over to repeater and then here in repeater we have our sample request and now we can see here we can replay this we can manipulate parameters so on and so forth and then we may have 35 other operations that we want to do that with well if you look here within repeater it's just got this one there and if you look down within the service there's nothing real obvious with just say okay I'm dealing with tools info here you just double click the tab tools info and now you've got a reference that you can go back to it I have no idea what I'm going back to
you I kept having to reparse wisdoms and re-export operations into repeater and so on and so forth and the ability to rename these tabs was just something that I was like you know what I don't know if anybody's like me and doesn't know about this but they need to so I'm gonna share it and we've done that now and I'm gonna prepare for a future demo here just by showing you or repeating this once and just kind of showing you the operation there so that's renaming cabs up so this next feature that's already built in a Berber [Music]
[Music]
[Music] within intruder okay so let's go ahead and look at this real quick if we go into our pone tub application the place I want to focus here is in our forgot password field so real quick to try to determine whether we have user enumeration here or not we can put in an obviously fake user like this it says user not recognized okay I already kind of know where this is going right and if I enter my actual user name what I get
this is an actual attack that's got me to self a fortune five
and all it took was being able to harvest that information for large numbers of potential user names so let's go in here and let's see what this looks like an intruder because we want to attack this all right so all right we have our base request our post let's right-click it we'll send it over to intruder positions the only position he wants the username here we're just replicating the behavior that we just did in the application itself and for our payloads I'm just gonna use a simple list here will type in some of the ones we already knew we tried to fake user will do Tim will do an admin will do hacker princess so you got some user
names in there and we go ahead and actually I think we need to set this to follow redirects as well just because of the way the application behaves and then we'll start the attack and very quickly we can actually come up here and sort by length and see that we have this two four seven two four four seven two four four seven two four four seven and then a difference in size and very quickly based on the behavior we've already go in we can analyze that but the idea here is to talk about these rules and what that'll help us kind of even further determine this so once we have this information we're like okay we can
determine which ones are valid invalid users but I still want that security question if we go into options and we scroll down here there's this section called grep extract and if we add a rule here what it does is his Berk will go ahead and make a base request the resulting HTML and then we can come down in here and find the information we're interested in in this particular case it's going to be the security question favorite food and if you notice here and this is kind of a cool feature in verb as you highlight this watch what happens up above as you highlight that it begins to build either deposits tracking that information out of the
payload so once I do that I usually use regex just because I'm more comfortable with regex than I am string parsing you just select that I've got the regex hit okay and if I come back to my results what do I see I've now extracted that information to some of those and come back to this process and try to reset somebody's password so those grep rules are really awesome for a lot of different things and I encourage you to find interesting or to use them if you're trying to get data out of your fuzzing requests they're perfect that's what they're intended for right and we'll come back and I'll show you in here in towards the end of the
talk we'll talk about some of the limitations of this and how we solve that problem as well but grep rules are certainly certainly worth taking a look at all right so let's talk about some of the stuff that perhaps isn't totally obvious within Bert oh the first one being
[Music]
[Music]
it's not [Music]
[Music]
[Music]
save us the couple of minutes that it would take to do that so super simple we're going to conduct a quick attack against the profile page so I'm gonna log in as me Tim's even a user he is okay good or the profile page and I had the ability to change my profile this is one of those things where if I can conduct a cross-site request board free attack against this that's pretty awesome so let's click Submit account information successfully changed great basically what I was just doing was this priming burp I want to get this request inside verb so that we can test for this method interchange so what kind of request is this here suppose right post request and
obviously it'd be a little bit more difficult manually change it like we talked about or if you right click there's an option here change request method it's that simple click it and it does all the work for you so the way that you would do that is you would run you at first in fact I'm going to need I'm gonna change the request method back you just hit go as a post and analyze the response and you can see here it redirects back to profile 302 found you could follow the redirect if you wanted to it's just sending you right back and there's no error in this HTML anywhere then you would switch it over actually
I'm using again oh that's because it was the redirect my bad alright so the initial post we check the response can we go back we changed the request method we do the same process again and if it's exactly the same then we know we've got the vulnerability right at the server still most important easy way to test for that all right so this next one it was a game changer for me this completely changed [Music]
[Music]
[Music]
[Music]
[Music]
[Music]
[Music]
[Music]
[Music] and there's a way to do that okay so what I want to do is I want to go back here and go back to repair to our our web service request that we made earlier because a really good let's go ahead and send this over to intruder so this is what you would do obviously this one right here is a place that we may want to foes that's the input parameter for this soap request is where that one is and we're going to want to fuzz that all right so we can right click on it and send it over to intruder okay and let's look at the positions so one of the things I
want to point out here all these things pre highlighted and we just want to get rid of the ones that we're not interested in fuzzing right now so just clear them all out and we have the one left our injectable parameter now if you right-click anywhere within this request you see the option and all of its glory
is very in a very very precise way only scans and things that we want to it reduces the amount of noise we make if we're trying to be stealth it reduces the dangers that we create it gives us a lot more control all right so let's actively scan this define insertion point we go up to the scanner we look at the queue and it's already finished because everything is local and super fast so we can see immediately we didn't have to wait for the wizard we didn't see I spent a lot of time manual testing and I will identify different parts throughout the application where I'm like I've been around long enough I know that parameter
probably one herbal I'm gonna hit it with a scanner and I can use this tool to just hit that one without having to loop in the entire up at the entirety of the application so scanning defined injection points big time win okay alright so now let's get into some unintended functionality [Music]
[Music]
[Music]
[Music]
[Music]
so going over here in the burp row actually let's go to the browser first I don't have TLS encryption on PO hub so I'm going to use my website so let's get rid of a GPS and just to Landmaster 53 because remember we're taking advantage of default behavior and I should have Internet okay so going here into burp let's look at our history and what we should see is exactly what we do see which is Landmaster 53 comm says hey I only do under w w so it remakes the connection redirects over to 2w w and then what
the HTTP so that's that opportunity to get in the middle how do we test for that well we can go over to our proxy settings options if you go into your proxy and you click Edit there's this ability to force the use of SSL all right so that's the first step in this once we do that we've got Bert behaving the way we wanted to but we're gonna get all these responses with references to HTTPS with secure cookies search secure flags on cookies and so on and so forth so if we scroll down we have this ability to convert HTTP to HTTP and remove secure flag from cookies now if we go back and we do this same exercise
let me clear the history to get out any 301 redirects we hit enter did I get a pop-up at all that said at this point no so the only visual cue is this the connection is not secure this traffic even though it was supposed to be over TLS okay and if we go back to h2 our history we can see what happened here actually I don't see the clear text maybe that's it right there well regardless you see it in the browser right it's unencrypted so there was a protocol designed to to protect against
control and the way that we do that is using this TLS stripping approach right here okay so another another fun way to use burp in an unattended fashion I'm gonna go in here I'm gonna reset this to that I don't goof up future demos let's turn that off and uncheck these boxes okay so the next unintended use
[Music]
[Music]
[Music]
right so let's run through this real quick I'll show you what it looks like and it ends up being something I now use on every single assessment this is a fantastic idea so the first thing we want to do is is hide I only want to show show only where's the thing I'm looking for only requested items that's the stuff that I've actually requested all right so within my within my particular target here if I look at contents you could see everything that I've requested at this point and I'll add a few more of those I'll go up here and we'll login we already are logged in we'll click on a few of these either
login we'll click on a few of these things artifacts tools games so we got we've maxed some of the application right so we go back here and we look and we can see that okay we've got a decent amount here what I want to do is I want to highlight all of these I'll go in and I'll highlight it and then now if I go up to my spider tab I can see that there are 39
so we'll just let the spider do its thing and then of course you look at the forms you've already logged in so we don't need to spider that one again a registration normally we would have mapped this already so I'm just gonna ignore it login again registration again and so on and so forth so I got through spider has ran if I go back to my target now anything that's not highlighted his new as new [Music]
[Music]
[Music] with these now on highlighted parts I'm so super simple but something that's missing that we can now go back and add because of some other unattended features here so really like that capability that's something that's been super helpful to me okay so Burke does a lot of things right and I guess
[Music]
[Music]
[Music]
[Music]
and it starts right here okay so this is ideal I do have interest so this is very very
starting point so I wrote this script to kind of just give you that information so you can get a head start and this is where I'm going to develop a lot of the documentation for this for this extension out but really simple is just copying the code right and then you take it over and if you didn't notice it before you'll notice it now the script tab and I already the script in there so let me delete that so you have the script tag so I'm gonna paste my script in there and it does a couple of different things this one's pretty basic it just looks for a request it just says hey if I see a requests
coming through the proxy then I'm going to do these things some information about what's exposed in the context of the script of the script er so I'm just going to go in repeater and I'm just gonna launch this thing and then under extender tab Python script or output you see this is kind of the standard out for our script you see all the information in there those of you that don't do Python this probably looks like a foreign language to you but those
you can extend it you can play with it a little bit more and all your right back here inside of the extender tab and this in this UI output this UI output text block okay so that's kind of nice right now you have some place where you can actually begin to dig in to this what Python script er does and utilize some of its functionality but let's look at how we can actually a practically apply this stuff all right so custom passive scanning checks
[Music]
[Music]
[Music]
so let's actually take this one and see what that looks like copy it over write this in here and then we'll go in the application and actually those let's look at our vulnerabilities first I will go to target we'll look at issues and you can see this one past password filled with autocomplete enabled but you don't see anything else there do you don't see anything else about autocomplete but go here to the application and I go over here to messages this is obviously a forum correct what do I have there text field will autocomplete enabled right and if I go down I can look it's I've created the the issue to tell me to show me the
exact on that kind of sensitive information right so that's just an example of how I use I keep that in there all the time and then you can extend this right you see I have a line break right here check for all the complete on form fields just add another regex [Music]
but Burke would do all that for you and treat your issues for you so if you have some passive things you want to look for that burp isn't looking for by itself BAM there's a capability okay another way I use this is regex extraction now remember I was talking about the [Music]
and I'll miss out on the rest of it and I'll show you an example of where I've actually ran into this where I needed this particular capability so let's go over here to in fact messages is the right place so say I wanted to harvest username Python script or we can say hey every time you see a request or a response that's coming back to a truth okay so let's do that real quick I'm going to use this particular and I think I've already got yeah I've already got this in verb so let's go to the proxy that's fine where that's at right here right click it send it over to intruder and so what we want to do
here with intruder is we just want to cycle through all the pages right what we're trying to do should cycle through the pages here there's only two pages 0 and 1 but there may be 35 pages then you never know but here we're trying to cycle through the pages so we'll do that we'll go over to payloads and since I already know there's only two pages will do a 0 a 1 and make sure I got all the configuration stuff here okay yeah so now I can go ahead and I can run that and I can go in here and of course I've got all the messages there now I'm going to not want to go do that
my previous grep rule approach and kind of show you what that would look like so I'm going to my options I can do grep extract add and let's go down and create a regex for the username which would be inside parentheses right there these regex hit OK and my results show me one username but I want all five okay I want all five of them every time every time I cycle through a page and that's where the script comes in so what it says is is okay if it's a request and if it's coming back from it or yeah if it's not is request so if it's a response and it's coming back to the intruder tool
then I want to run this regex and I want to print out the matches so let's go and let's grab we can actually grab our regex straight from our rule that we just created which is kind of handy I'm just gonna copy and paste this whole thing actually I probably should've did this bar first so let's get this first take our script put it in our scripture tab then that's good now let's go for fetch er regex and replace this right here because that's the regex we're looking for now our script setup let's go run the attack again find where I'm at attack repeat the attack repeated once again you see only see one there right but I
outputted the information to here and what do I see
kind of go through and pull it all back how am i doing on time getting there okay so last thing I wanted to cover I think it's the last one yep bypassing client-side animation okay so let's go in here and actually try to break into this particular application let's log out log in and if I do a username we know exists but I'd say I don't know the password and I hit enter it says invalid username and password I could try something else Tim try again Val username and password I could do that a whole bunch of times manually and it would work in the browser but doing that it's slow right we want to automate that particular
attack so it's going to burp I'm going to close out these windows because they're annoying so we're going to burp our history will find that request there's our login request right there we can right-click or zoom in on a little bit and you can see the issue here right you see user name
probably somehow involved in this anti automation scheme okay I could look at the the response to the login page scroll down to the bottom look at the JavaScript and determined very quickly what that logic is it's taken the nots and it's taken the provided password but if you're just doing but if you just make this request it's going to be detected as a balk so I'm gonna go and I'll show you this will right click it the request send to intruder the position we're interested in is the password let's actually clear them all
passwords the right password by the way so we start the attack and we notice real quickly that even the right path none of them authenticated correctly all of them are exists the responses are exactly the same and the reason being is because we have bot detected right it didn't do the proper calculations and so this is a perfect opportunity for us to use this Python script earthing again so let's take our script copy it put it here in the scripture tab and then replicate this behavior again but this time we're going to intercept it so we do Tim I'm gonna make it a bad password and login so we have this here which gives me the proper nonce for this
particular request on a right click it send it to intruder positions once again we're only interested in the password here because it returned the cracks of nice password payloads with the correct password another fake another fake and start the attack and here we can obviously see that when it landed on password it properly authenticated
simple Python logic in the Python script these are these last four examples are common things that I come across actually quite a bit where TLS and threading and all this other stuff that's already built into Burke for you take advantage of Burke's capability use the Python script or stuff and make it easy on yourself 10 20 lines of code and you'll probably have what you need to have okay alright so that pretty much covers when I want to talk about I'm going to try to demystify that and create some documentation so that you don't have to dig through the source code yourself you can just come to my website over there and kind of see how
to how to how to actually write those ok so that pretty much wraps things up if you [Music]
[Music]
[Music]
we got time for questions and think we've got stuff to give away
[Music]
[Music]
[Music]
[Music]
[Music]
[Music]