Ducky-in-the-Middle: Injecting Keystrokes into Plaintext Protocols

Show original YouTube description
Show transcript [en]
all right my name is Esteban title of my talk is called ducky in the middle injecting keystrokes into plain text protocols so I work as a penetration tester for a company called coal fire we do all sorts of security stuff I blog and do some security research on my own so basically what this talk is about so the title itself is a reference to the USB rubber ducky which is a pen test tool that I'll show in a video and the whole focus is on exploiting applications that can do two things so they can send keystrokes to a machine as part of the protocol and also that they aren't protected with any sort of encryption and this research began for
me just with curiosity of how some of these applications worked so I wanted to dig into them a little bit so if you've never seen a USB rubber ducky this is it right here so you have I see use video playing nope here we go so it's a little USB thing you plug it in it emulates a keyboard and then you can just open the command prompt this right here is a Metasploit web delivery payload but you could basically do anything you can but you could do with keyboard so when it comes to analyzing protocols you don't really need a lot of tools to do this you can pretty much use Wireshark most of the time and for my analysis I use
mostly Wireshark if you haven't used Wireshark before it's a protocol analyzer and you can do deep inspection of a bunch of different protocols it has parsers for all sorts of things you can capture and analyze live or you can do it from a pcap or a packet capture that's already saved a disk it runs on Linux Windows Mac you can do lots of filtering and it's totally free so if you haven't seen Wireshark here it is top you have the it's middle you have the breakdown of the different headers and then you have the raw bytes at the bottom so the first concept that we need to understand is TCP session hijacking which is basically
taking over an existing TCP session and in order to do that to take over a TCP session you need to know what the sequence number is and most of the time nowadays this is completely random but a long time ago it wasn't and if you've ever read about the mid Nick attack where he used TCP hijacking to compromise the system of one of the people investigating him it's a really good read and I would recommend checking that out but if it's not possible to just guess the number you can still sniff it if you have a man in the middle position so there's a lot of different ways that you can get man in the middle
but ARP spoofing is probably the most simple and common one I think I lost video okay so TCP hijacking has been around for a while it's been around basically as long as TCP has there's some older tools that can facilitate this like Shai Jack and hunt or some of the ones I found and TCP hijacking can't really be prevented if the attacker has made in the middle but you can stop the impact from it by encrypting the data that's being communicated or just you know using a message digest or hashing for integrity checks so right here here's a demo it's kind of busy but this is a TCP hijacking attack on the right I have a tow net client on the Left I have
a tonot server in the middle I have Kali Linux which is the man in the middle enter cap running it on the top for the ARP spoofing and at the bottom is hunt for the TCP hijacking so all the actions so to speak happens down at the bottom so I have man in the middle and I'm kind of messing around here for a second but you can't read the text but it will say you've taken over the connection and once I take over that connection I'll be able to start typing into the callee system and those commands will then be sent to the telnet server so I basically jump in the middle of this existing connection and then I
can start modifying files on the telnet server so if you look all the way to the left in the temp directory and the file explorer I just created a temporary file so and I did that just by jumping in the middle of an existing connection without breaking it so TCP hijacking is pretty cool but when you're attacking something most of the time you don't really need to use this technique because there's easier techniques available for example like telnet it's much easier just to sniff out the telnet credentials but it is to actually perform a TCP hijack and then also you can get the real client server out of sync and they will break their connection so all the protocols
I'm going to talk about from here on they can be TCP hijacked but I'm going to attack them in other ways other than TCP hijacking so the first one is VNC you've probably heard of it probably used it and you use it to remotely control another computer uses this protocol called rfb which is pretty old and doesn't have any encryption built in the author authentication scheme uses DES which is a very old and deprecated cipher and also the passwords are typically truncated to eight characters and what that means for us is that if you're brute-forcing this you will pretty much find any key regardless of what it is just because the key space and cipher are very small so VNC that
when the server is running it has a password file to connect to it this password is also encrypted with DES but it doesn't even matter that's encrypted at all because all of these VNC passwords are encrypted with the same static key so if you just look in the source code and many of these VNC clients you can get that static key and you can decrypt the password if you can access it either in the registry or on the file system so this is what a VNC stream looks like on the wire so this is Wireshark at the you can see the protocol negotiation the server will send a challenge the client will send a response which is both based
off of the password and then once the connection starts you can start sending keystrokes or mouse movements or screen updates so here I have some keystrokes and you can very easily see it it says test and if you look at the bytes they're actually just regular old ASCII so it's just from Wireshark you don't have to do anything fancy - sniff out the keystrokes so there's a couple other tools if you don't want to use Wireshark there's this one called B and C key logger you can just run it against the peach cap and it will just extract all the keystrokes there's another tool called Foss for V&C cracking like I said before des an egg character so you can
pretty much always crack it there's a tool called VNC crack that's pretty fast cain and abel can sniff and crack these handshakes as well which is another really old tool that you can run on Windows so once you are able to crack this handshake you'll get the plaintext password and then you can just connect to VNC and just control the screen remotely but if you don't want to go and start moving the mouse around and clicking on stuff you can use Metasploit to perform a tap and attack very similar to what a USB rubber ducky does it'll open the command prompt and start entering keystrokes so right here I have on the left a Windows 7 box and on the
right Kali Linux running Metasploit and when I run this module you'll see I think it's going there we go so we run it it opens the command prompt starts putting in text superfast and then you'll see a meterpreter shell pop back on the kali linux box so probably about 2 seconds you can use that to pop a shell the next application i want to talk about is called hippo remote so this is something that i came across as a Mac user and it was a tool but you could use your iPhone and basically turn it into a trackpad or you could use it as like an external keyboard as well it also boasted features like being a
password manager it was really popular right now it looks like it's no longer maintained but there was like quite a few downloads when I downloaded it so here's a little video of how it works I'm just gonna skip it for time but so when it comes to the implementation on Windows you're basically just using a VNC client that's forked off of Ultra B and C and if you're using it on Linux it's you just use whatever VNC version you have on Linux but if you're using it on Mac it has its own app that they developed called hippo connect and that's what I'm going to focus on so with hippo connect it has some problems so for the password
storage it stores it with inside a P list within the launch naman or launch agent so on Mac launch Damons and launch agents are what are used to persistently like run applications when you boot up or log in and inside that P list the password is there for the server but it's not encrypted at all and what's worse about it is those plist files are completely world readable so even if you were to log in to a Mac with a guest account which should really have no permissions you could go read this plist file get the password and then when someone else logged in you can start using you could start injecting keystrokes and the program also runs as
root which I didn't find any like but buffer overflow or anything but that's like a good candidate for some privilege escalation as well so here's the P list in red here there's the relevant portion where it shows the password so it's super easy but if you can gain access this file you can find that password to connect so just like the protocol itself is pretty much like VNC uses the same VNC authentication scheme you can you can send keystrokes and mouse movements so here's the Wireshark TCP stream you can see JSON here this server identifying itself handshake response and then the keystroke or mouse movements so right here I created a tool to exploit this protocol and the first
part I made was to just monitor the keystrokes so if you have man in the middle between the iPhone and the system you can start sniffing out the keystrokes as they get sent so right here this tool is called angry hippo and we can see the handshake come across the screen and then we'll start seeing the keystrokes being sent once they start typing on the iPhone keyboard so the good part is cracking handshakes because once you get that password then you can start doing whatever you want not just sniffing out what the person is doing so we sniff and we can get the challenge and response and then once you feed both of those two
angry hippo with the crack option and supply a word list it can figure out the plaintext password I ran this against the rocky word list that comes built into Kali and it took me about five minutes to get through the entire word list and this is just a single threaded Python script so if you use something like VNC crack and just fed these handshakes in you could probably crack much faster with it so pretty much always crackable so the fun part is once you crack that handshake and then you get the password and at this point you don't know you no longer need to have that man in the middle position so I'll use angry hippo to start sending
keystrokes to my Mac so on the right we have Kali on the left the Mac and we're gonna start sending keystrokes to the system so we'll start up a netcat listener we run angry hippo and then real quick you see a flash what just happened there was I opened up spotlight typed in the terminal brought up the terminal put a one-liner for a reverse shell then closed out of the terminal so it happens very fast so if someone were to fall victim of this attack it's likely that they wouldn't even notice what happened so here's a slowed down version of it and you can see once the attack runs you'll see spotlight open terminal being typed out and then you'll
see a just a regular one-liner for a reverse shell typed in it will back around the process and then it closes out the terminal window so like most things on Mac they use Bonjour which is Apple's implementation of the zero config protocol and it's super useful for all sorts of things but especially for attackers because it will broadcast out whatever services are running on that system so right here I'm using an application called bonjour browser and I can see that hippo remote is running and I can see the hostname the IP and the port so if you're worried about this happening to you if you use hippo remote you know you probably don't want to use the the
VNC option or the hippo remote app just because they're all vulnerable to this the screen sharing functionality in Mac OS is a little bit better because everything is encrypted but you usually don't have to worry about this now because that hippo app isn't really maintained anymore so it's probably just time to stop using it if you did so the last application I want to talk about with synergy so synergy is a bit more popular and the way it works is it's a mouse and keyboard sharing software so if you had say a Linux box a Windows box and a Mac system you could use the same mouse and keyboard to kind of pan across all of your different screens seamlessly
so it's actually really good software when I got it there was two versions there was a basic edition in a Pro Edition and what you got when you upgraded to pro was you got SSL encryption but the basic didn't have any encryption at all so that's what I focused on since I've done my research on this and released the tool synergy now a synergy two with two versions that are both encrypted so I don't know if they knew about my exploit but now if you download the latest version of synergy it'll be encrypted either way that's just kind of a breakdown of some of the changes between the two versions I'll skip that video so monitoring
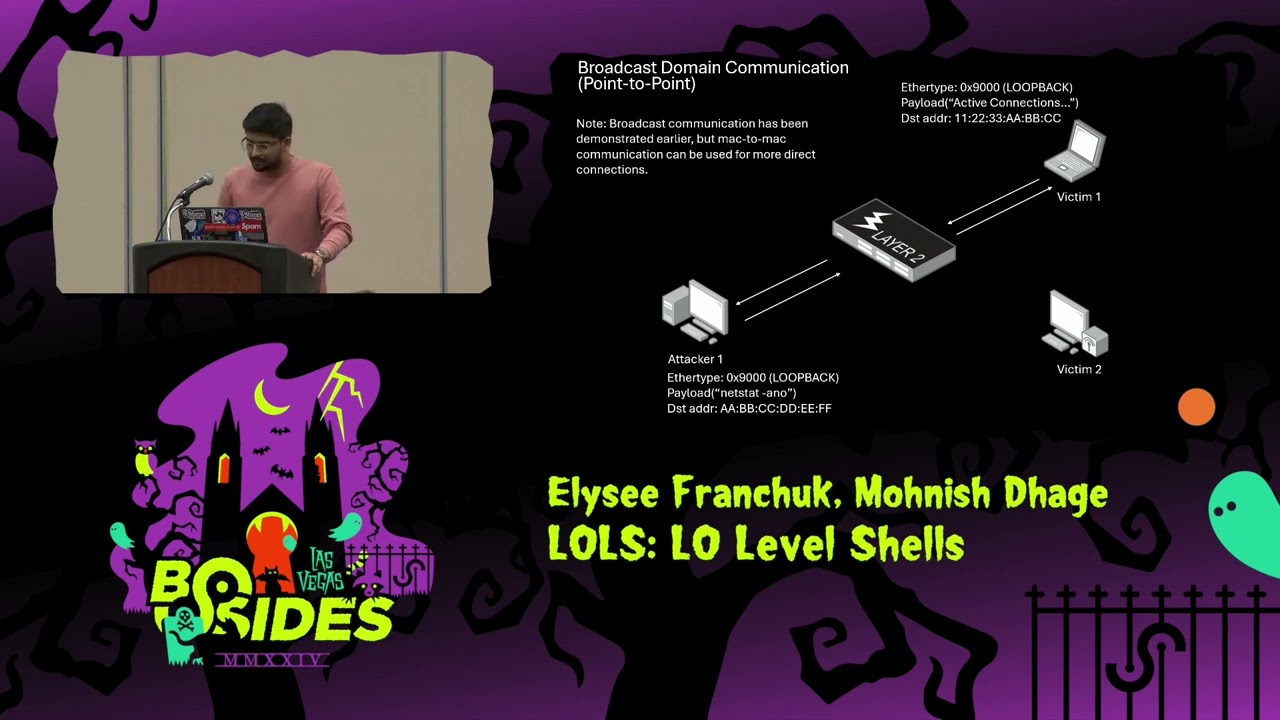
keystrokes very similar to the others if you've ever used scape II within Python it's super easy for packet monitoring manipulation so here with just nine lines if I'm man-in-the-middle I can sniff out all the keystrokes that are sent with synergy so with hijacking it's a little bit different than the other ones the other ones I used a man I'm in the middle attack to capture the handshake and then crack it but synergy doesn't use passwords it what it does is the client will actually configure what server they want to talk to and that's the only real form of authentication and the client will initiate the communication first with the server but the server will be
the one sending the commands so they have this functionality built in call it Auto config which uses Bonjour to basically go out and find a synergy server so if you're on the network and you have a malicious server running it'll just identify that as a synergy server and automatically connect to it so here we're gonna do is we have the client on the left the malicious server in the middle and then PowerShell Empire running on the right to catch the shell that we're gonna pop so right here we got Empire running we run the tool it's called dissonance it starts up the rogue synergy server the client clicks Auto config it'll quickly find the server I
have running and then it would just start accepting keystroke commands so right here command prompt I start typing characters this is a one-liner to pop reverse shell in PowerShell so we'll see the agent callback on the right there so there's another way to do it too so more likely than not if you actually encounter synergy on a network it'll already be associated a client will already be associated with the server so for attacking we want to basically jump in the middle of that connection so what we can do is we can assume the IP of the real server we can ARP spoof the client into banking the bad IRP now goes to us and then whenever a connection and
synergy breaks it'll automatically try to re-establish that connection so once the connection breaks it'll connect back to my malicious server because that's how it's designed to work so right here we have the client again we have the real server that has an active connection and on the right we have the rogue server and the command/ctrl server which is PowerShell Empire again so you can't really read the messages but you'll see all first all sniff Bonjour traffic to find out where the server is what its IP is and it also sniff out where the client is so I'll have the IP address of both of those so I know who to spoof so on the right I'm
just selecting the IP addresses that I found by using Bonjour this is if config I assume the IP of the real synergy server then I run an ARP spoof against the client to convince it that I'm the server and then I will run the dissonance tool with the payload of my choosing so right now the connection is broken between the two but as soon as I start this server up it'll automatically connect and start accepting keystrokes and again command prompt just start spraying keystrokes and then it pops a reverse shell with PowerShell Empire so if you like synergy because I do like it I would recommend if you're using synergy one basic you should upgrade to
pro or use synergy 2 or if you're going you know across you know networks and you want to use you know the basic one you can just tunnel these over SSH as well yeah but when you use the the pro version everything is as so encrypted and if for some reason some one man in the middle is you and puts up a rogue server you know notify you that the fingerprint of the server has changed and you have to accept that so if you did go and like click yes to this warning you could still get owned but if if you know what you're doing for the most part this should give you you know some notice
that you're being attacked so in conclusion just unencrypted protocol is just aren't good don't use them at all and don't be afraid to do your own research either so this was just kind of a side project I had in my free time I didn't take too long do so if you're interested in just like picking things apart I would say go for it all the tools that I mentioned the rogue synergy server is there on my github as well as angry hippo both of these are written in Python not a developer not really much of a programmer but Python super easy to use so if you hadn't gotten into any programming yet I would say jump into that and have some fun
with it down on the right is my blog I talk about a lot of topics related to pen testing and just kind of security research that I do and that's it so does anybody have any questions you know yeah someone brought that up to me the other day they're like and I hadn't heard of Mouse Without Borders I wanted to analyze it and maybe sneak into this talk but I didn't have time but yeah that's something I wanted to look into yeah very similar type of software I know I went through a lot of stuff kind of fast so if yeah if you have any questions let me know or talk to me after if you don't want to ask it
publicly or just want to you know talk about anything cool I guess that's it Thanks [Applause]