Minions vs. GRU

Show transcript [en]
[Music] attention [Music]
[Music] thank you foreign
Okay cool so the talk I'm going to be giving is uh it's titled minions versus Gru or the Gru and I want to be discussing sort of uh what the role is of Civilian Volunteers in cyber War and uh sort of probably the image they have of themselves is something like this but the reality is it's it's not even this which would be at least benign um it's a it's a bit more uh complex and nuanced and um actually a bit dangerous but of course uh the problem is that the the people who are suffering are actually not the opposition in this case um the role of civilians has basically been to cause problems for the people
who are actually trying to do something so why am I going to tell you this well I'm a grug and what I've been doing for the last decade I've been doing cyber for 20 something years now but for the last decade or so a lot of what I focused on has been research where I do a lot of um reading and mostly talking to people and listening and discussing and finding out how they work uh what they do what's useful um sort of learning and understanding from people who are engaged in operations at multiple different levels on the defensive side on the offensive side um in you know companies versus in small groups versus when they're operating
individually or whatever so a sort of um I'm speaking here from a position of having discussed with a large number of people who have uh first hand insight into what's going on and I've synthesized that sort of trying to bring that out now in a cohesive narrative and we will see if I succeed and the approach that we're going to go through is basically a brief introduction to um not you I don't know if you guys are familiar with this but uh there's actually a war going on in Ukraine um and there's been a cyber component so we're going to be talking about uh sort of why this war is unique uh why there is cyber and War and what cyber
and War does uh we're going to be talking about the sort of the players the hacks that they've done the lessons that can be learned uh you know bearing in mind of course that in the middle of awards are not the ideal time to draw conclusions based on public and uh you know hearsay information you know we're going to we're going to look at what we can um and then sort of close it out and I should also point out that this overview I think is out of order but anyway we're going to be hitting these topics if not necessarily in this order and uh this image is here to let you know that there are things that seem
one way but they're not now it's about uh deceptional stuff okay so if you take nothing else away right this is what you should remember do not allow civilian volunteers to hack inside your area of operations right it is not what you want they are the opposite of what is useful if you are trying to run a war um I will get into more details on how and why and let's go so very quickly we need to sort of um just go over like there's multiple layers of War uh this is not necessarily relevant but it's important to know uh when we're doing analysis so you've got the Strategic layer which is sort of um
the broader understanding of like what you're trying to do and uh where you need to be in order to do it or sort of the objectives you need to have to achieve those ultimate goals then you've got sort of operational which is the how do you take your things to the places they need to be to do the stuff that you want or how do you uh like how do you achieve the objectives that you want to achieve with the resources that you have and then we sort of have the Tactical which is the like what do you do once you get there like what what do you do to actually achieve those objectives and
um as you can see like with these three layers basically uh the higher up the more influence the state needs to have and what's happening and as it goes lower down um it sort of it becomes a smaller scale thing and people can get involved and so sort of the takeaway from this is that where the civilian volunteers get involved is at the Tactical layer which is sort of not really the most useful layer to have people just show up in particularly if they're not integrated into the previous layers um so about the war this is a valuable uh cauldron of um basically like an experiment to see what happens in a real peer competition
with cyber where there's a significant part of uh the war is actually taking place in cyber a large part of that is actually information operations and the ukrainians have been absolutely smashing it on that one the ukrainians are just dominating and um it'll be interesting to look at why I think there are a number of cool reasons one of them is that the ukrainians are led by a sort of like a young comedian who has a smartphone and is clued in and comedians are useful because the instrument that the comedian plays is the audience you know they they learn to connect with people and uh sort of interact and get reactions out of them that's incredibly
useful if you are trying to do information operations um anyway I actually do not have time to go into this so the um the majority of the Cyber effects that we saw were actually during that initial Invasion phase particularly during the first day um this was done by Russia where they were able to successfully uh isolate and they were able to isolate the commanders and they were able to disrupt the command and control channels uh this was very effective in disrupting control and um also immobilization but the Russians were unable to exploit this for a number of reasons um but you know that's the important thing to remember is it was successful but then um that wasn't sufficient in itself
um since then cyber has not been particularly tightly integrated into operations and part of that is an inflexible Force structure that the Russians have where the operational control um at the like the actual thin edge of the wedge does not have control over cyber operations that's done from back in headquarters so there's this disconnect and stuff but there's sort of a lot of different reasons right like maybe there's nothing useful to hack like what exactly are you supposed to do with the DDOS that's going to fill um you know a tanks diesel like that's not going to help uh there's not a lot of cyber that you can do that's going to help in artillery barrages
um you know it could be that there's no strategic direction or there's no resources so no one cares you know like there's any number of reasons and we don't know and uh the reason this is important is it's important not to draw lessons just because something hasn't happened doesn't mean it's um you know it shouldn't happen during this phase it's not an indictment of cyber that it hasn't been used it simply says in these contacts with these circumstances it hasn't been used so it's important to sort of not try and draw too many lessons um what we've seen in terms of actual use has been very tactical right it was the use of you know deny degrade disrupt
uh targeting of government systems critical National infrastructure was targeted once and it failed but generally speaking it was this initial short sharp strike and then pretty much nothing there's been a lot of Espionage there's been um some other attacks that have happened the the major cyber attacks that have happened have been outside of Ukraine as more of a signaling effort which we will get to in many minutes but with that sort of said you know like that's the Cyber that we have had in the war so far uh let's talk about cyber war and before we go on I just want to interject for a minute because what you're referring to as cyber war is in
fact cyber War as I've recently taken to calling it cyber plus War so cyber is not a war fighting domain unto itself um the problem with the term cyber war is it sort of creates the idea of a conflict domain that exists in isolation of everything else right like if you talk about air War you don't assume that there's like no infantry involved or that the the Navy doesn't matter anymore you know it's it's part of an integrated operation there's an entire thing going on including the state behind it itself being actively involved in many ways to prosecute that war it's not done in isolation and similarly cyber war will not be done in isolation
it's not a thing that can just happen that doesn't exist as a platonic ideal it is something that has to be part of you know a complete balanced War um and what that means of course is that Wars will now have cyber elements and we're starting to see that we've seen um it hasn't really been talked about but in uh no go on karabakh that was quite a lot of cyber stuff that went on it was very interesting we're going to be seeing a lot more in the future so it's valuable to know about that so let's start talking about you know where cyber fits in war and that's easy so when we think about
creating a warfighting capability inside cyberspace for part of our strategic intent and we're looking at doing a global effects integration and like I mean what the [ __ ] if it's called like The Art of War why are there no drawings right like this is rubbish um instead I think uh probably the most important thing to remember is that cyber attacks are not attacks all right like no one dies nothing gets blown up like it's not actually that big a deal in like the middle of a war it is something that could be used to uh augment or supplement or assist with another attack but in and of itself it's not an attack um you know and and similarly you can't
really say like uh this addressed a bit of the the legal thing but you know if people are participating in a DDOS against Russia does that mean that they've become combatants on the one hand yes they're now participating in the war but on the other hand it's not really an attack so no they're participating in a crime um it's not part of a war Okay so let's talk about what actual cyber warfare is and a big caveat up front is this is wrong like the taxonomy I'm about to give you is not uh a it's not used anywhere um I don't think it's absolutely correct but I do think it's useful I think it is
uh valuable to use these uh these stages to sort of understand how civilians can participate in what's actually happening and these are the three things so we have Espionage information and effects um Espionage is basically collecting information or perhaps subtle sorts of influence um that can be done sort of stealthily and whatever but it's it's not visible you know it's something that happens uh covertly and in the shadows it's heavy on stealth it's just not an exciting thing that's going to get reported on uh information operations on the other hand tend not to be treated as cyber because they're basically what PR companies do or marketing or whatever they do not have um the sort of like offensive cyber
operations uh bling going on but they are very very useful um particularly strategically in terms of making sure that your allies remain on board so you know an information operation will help you sort of shape the information environment which will then hopefully lead to influencing the behavior of the target audience and the big one of course is the effect operations which um like even this terminology is a little bit out of favor now but again the idea here is just to be able to understand that you've got like um stealthy stuff that no one knows about talking about stuff which no one cares about and then actually doing things which look cool and um those are sort of like the three
groups and the effects are the stuff that like looks really cool and the idea is that somehow it will help you in some way that's the overall goal um but Espionage is actually useful like out of all of this stuff it's the most boring but it's also the most valuable like you can actually do things with it um it actually directly helps you prosecute a war um information operations again really really important being able to shape the behavior of your opposition and your allies absolutely vital to being able to win a war like you want it so that um your allies stay on your side and that your enemy sort of lose uh lose heart
and don't want to keep fighting anymore like that's what you're going for and then you've got effects which um I mean they're a lot more exciting than just grapping through someone's emails to see like if there's anything interesting uh these sort of things like they seem really cool you've got your DDOS you've got your defacements you've got like putting stuff on someone else's TV or playing things from hacked radios or you know whatever like all of this stuff is just it's flashy and it's cool and you know it's not that useful uh unless it's part of an actual operation so where does that leave us well we've got cyber we've got war and who do we have playing in uh the Cyber
War that's actually going on right now so if we look at the Players um they sort of fall into two groups you've got your state actors on the one hand and you also have non-state actors so the state actors are by and large not that interesting um sort of to look at like if they do good stuff but most of the time what they're doing is espionage there's very few who are involved in actual effects operations um and of course the reason for that is as we've talked about like it's because Espionage is actually very useful so uh when we're talking about State actors we're talking typically about State security forces and I'm going to hit
next and hope that I have a slide but yeah look at that okay so um basically on the Ukrainian side we've got the sbu which is sort of like uh the KGB but not uh the gur which is like the gru but not basically so you've got your uh State intelligence service you've got your military intelligence service there's also the police who have some degree of uh cyber capability particularly because uh a not insignificant not insignificant number of them used to be cyber criminals who have been sort of coerced into working so they do have some capability and they have um historically at least they've wanted to participate as far as I know they are
not doing that they are not um conducting their own cyber operations but you know don't quote me on that one as far as I know the Cyber operations are being done only by uh sbu gur and any contractors or whatever that they might have working for them just like NSA has got Raytheon and so on the other hand um you know in in the Red Corner we have Russia who has um the primary uh sort of operator in this uh this war so far has been the gru they've done all the effects they do a lot of the Espionage um I guess as FSB is trying to wash their hands of it because they don't
want to be tainted um with you know the catastrophe but um yeah FSB sort of has control of Espionage over the near abroad I'm not sure if you guys are familiar with the way that you know Russia considers its uh former satellite States this might be a bit foreign to you I know that the baltics is very far away from um you know Ukraine and stuff so anyway I'll skip over that but yeah like basically you don't get svr operating in Ukraine very much because it's not part of their agreement um the one interesting thing is that Russia also has cyber criminals in particular Conti who have uh begun working for the state and uh what's
become I think quite interesting is that the way that their operations have evolved show increased integration with State operations particularly the the state command structure um and I really hope I've got slides on that okay non-state actors on the other hand is where we've got this huge mess [Music] um so we've got like the Ukrainian aligned non-state actress starting with the I.T cyber Army and so briefly about the I.T cyber Army um when Ukraine was initially invaded they panicked as one does being invaded and everyone who had a half reasonably sounding idea and pitched it to the government basically got greenlighted so this guy came up with the idea of starting a sort of like volunteer force
of cyber hacker operator types who would come and help Ukraine cyber hacker operate and like that was okay so they basically put out this call and said hey you know everyone please come and help us and um that attracted quite a lot of people they did show up to help and there was a lot of DDOS there were a lot of defacement um there were a bunch of cyber criminals who got involved and sort of what what this reflected was um there's this dichotomy between uh so you basically have two types of followers that you get on these things as uh the sympathizers and supporters so sympathizers show up and they're like I feel strongly about this this is really
important to me but um you know it's getting on past eight o'clock and I've got a thing so you know I'm here to show my support but I won't be here and then you know like not showing up the next week and so on where supporters are sort of more consistent and uh we saw that with basically the the sort of level of activity and the number of people involved the early phases of the war particularly in the first two weeks uh two or three weeks so a lot of activity and then it sort of died off fairly rapidly um basically the the criminals got bored and stopped doing defacements all the people doing DDOS sort of had other
better things to do at their time um there's still a lot of people involved but it is uh a lot smaller than it was before they are not necessarily more skilled now than they used to be but I'm not going to go deeply into the organization of uh the it Army because one of the most important things about the it Army is the media coverage that they have gotten because the media coverage does not accurately reflect the reality of what they're doing it has had the effect of attracting more volunteers and since the it Army has been causing problems the um like their operations and the coverage that they've received has caused issues for actual
legitimate real operations that are being done by you know Ukraine and their allies so more volunteers has actually just made things worse so the coverage you know it represented what was happening uh it showed that it made more people show up brought in more sympathizers uh and it ended up alerting the Russians and it caused a huge shift in the security posture of Russian um systems so for you know the the first month or so while all of this coverage is going on Russians started getting a lot more secure like they worked hard they you know um like we can go into basically like when there was a DDOS going on it meant that there was no traffic that
could be sent from you know a legitimate cyber operators who are trying to hack something if there was low hanging fruit and it got uh grabbed by some random person in the U.S who then did a defacement it meant that that access was not available to legitimate operators who might have been able to do something much more useful with it um it meant that people who had low hanging fruit were motivated to go and secure things because they saw all the media coverage of what was going on and they didn't want to get hacked so certain things that could have been hit they were shut off um again things like the you know um there's a friend of mine and we were in
a discussion and someone said basically like um but you know all of those attacks is useful like it's noise you can hide in the noise you know they won't be able to see you and the my friend was like yeah it's noise for me too like I can't see anyway like it it it covers everyone like noise is noise it's not useful it's just a problem and that sort of the thing that I think has not been understood uh particularly uh outside of the media and also in um don't leave I can see you on the camera okay so it hasn't been understood by analysts and I'm not gonna name where this is from but
this is a very very relevant quote because it cracked me up when I read it basically um he says like the it Army make like it makes no sense that the defense and intelligence Services basically just did nothing and allowed the I.T Army to conduct operations freely and independently because that would highly likely also lead to strategic confusion and tactical interference with the defense and intelligence Services own operations in cyberspace you think like what did you think happened so you know like the obvious problems are obvious but people have assumed that basically given how um like important it is to not have these problems obviously no one would actually do something this dumb like that makes no
sense it's got to be a lot smarter than that and it's not like it's really not any smarter than it seems it is actually that dumb and um that's sort of one of the problems here and why it's sort of unfortunate is that you've got these uh guys trying to do a job and you've got people trying to play a game and the game players really shouldn't be [ __ ] around here uh one of the things that gets set a lot um if you see interviews with people who have volunteered to go and fight um they always say like it's not Call of Duty you know if you don't have military experience if you don't have
um you know the background you shouldn't be here and I think um that sentiment needs to be understood for cyber as well like it's not a game when you know uh someone does something in Russia that causes that asset to no longer be available to a legitimate operator it's not a cool thing it wasn't like clever it's a problem um it outside of the Strategic control and strategic hierarchy without being integrated into how the whole war is being fought anything that is done by these independent groups is wasted at like the best case scenario is it's completely wasted but realistically it is negative in some aspect like it's either raising the security awareness of the other side it's cutting off access
it's obscuring something it's interrupting and interfering with acting like ongoing operations um like stop it don't do it um all right so that's the I.T cyber Army there's also been uh Anonymous who sort of like they rocked up early on they did some DDOS some defacements you know and then they kind of they got bored um the the major use of anonymous as far as I'm aware now is it's just used as an umbrella organization for um much more interesting groups which I'm calling tiger teams um basically these are groups of um experience cyber security professionals who have strong motivations and are turning their skills towards acting to assist in a way that they can and these people have been
um doing a lot of stuff and I think the the thing to understand is the difference between them and the I.T cyber Army is the operations that these guys are doing are much more focused they're still not integrated in the same way that they should be in order to be truly useful but they are not as problematic they don't cause the same level of issues and so um just sort of like the the connection that these guys have to Anonymous is like they're not actually part of the anonymous group like they don't join the channels they don't discuss anything they don't do any of that stuff but a lot of their operations get attributed to Anonymous and that's fine by everyone
like Anonymous is not going to say we didn't do that and these guys are not going to come out and be like no no that was me um they want it this way so basically if you see a really impressive cool hack almost every time it's going to be the work of a tiger team or similar like the state does not have capacity to just [ __ ] around they don't run non-essential non-essential operations they don't um they don't have the time to put into you know putting something on TV just for the hell of it when they could use that to try and gain access to like the logistics back end and learn what the um
like the depth of the reinforcement situation is you know like they have important things to do and it does not include playing around so almost any time you see like a clever Fun hack it was done by someone who's not the state and it was not directed by the state um Okay so that's kind of like the Ukrainian line side on the Russian side things are a bit different we have um mostly sort of um Russian uh State linked and controlled groups so we've sort of got like the the killnet hacknet stuff going on um these guys they are very very closely coordinated with the military um they have done a lot of high visibility effects operations
they clearly take Direction on what they're supposed to do and that direction make sure that their operations are strategically aligned with the interests of the Russian state um
so they they play this big game about how you know like they're independent and patriotic and whatever and they're clearly not um I don't think anyone buys that uh then we have conti and Conti has done um an interesting thing like clearly they've got some connection with fsp as we saw from the leaks and it seems that some portion of Conti has uh Gone on to doing exclusively uh Ukraine targeted hacks to assist the Russian state in some way um and what we've seen over time is that those hacks have gone from being um sort of a little bit more obvious easy to catch and less focused to being more stealthy and more clearly focused
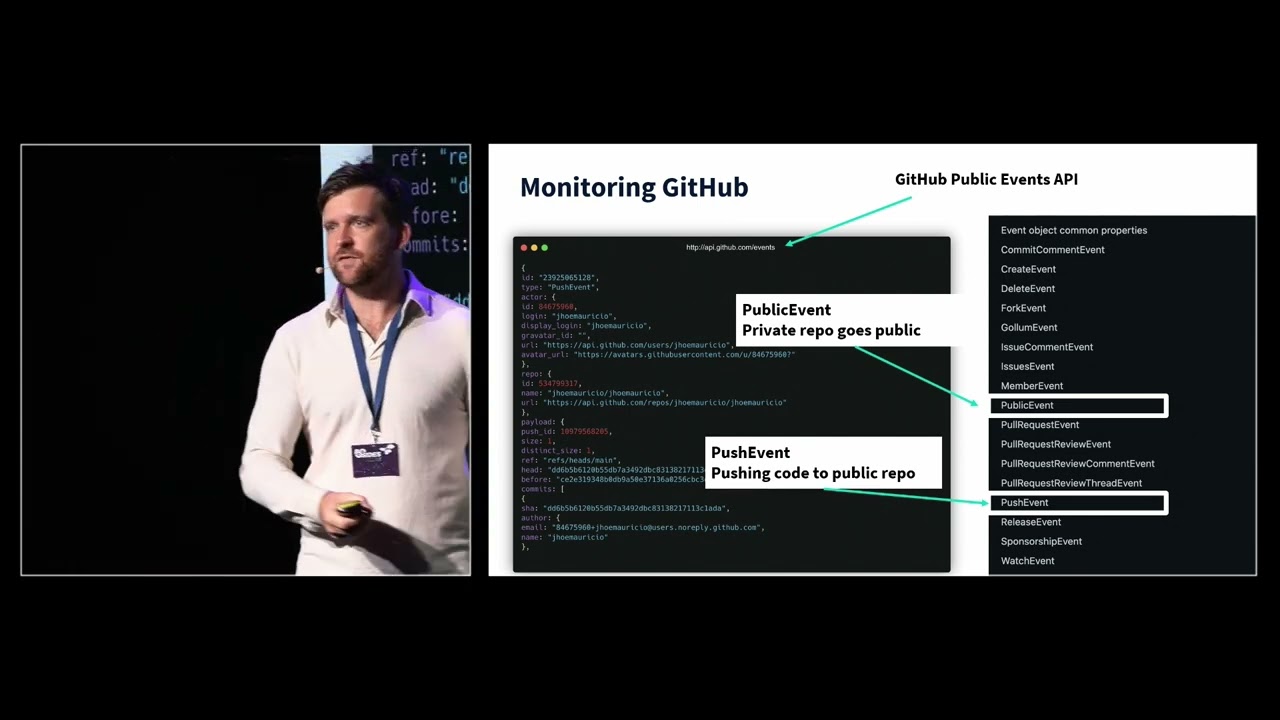
which I think shows a tighter operational control in targeting and in being able to sort of realize the value from this group like there's more interest from the command structure um this is ironically from imotet who is in Ukraine but basically like this is the like this is a realistic state of you know the professional cyber Criminal um okay so that was abrupt um let's look at some of the things that have happened in the cybers um stuff that Anonymous has been associated with so there's been a lot of data leaks via DDOS Secrets um why this is good is that it's provided a lot of data leaks the downside of course is that there is so
much that has been leaked that it is not possible to analyze it there's just too much information it's not um it's not accessible in a way that can be looked at so who really knows what's in there uh it's interesting and maybe someone will find something valuable but it's just been a flood of um data that no one can do anything with really um they've done a bunch of like amusing things uh of of little to no consequence um more towards no consequence uh so like you know the TV stations have been hacked they play like Ukrainian patriotic music um on Independence Day a bunch of IP cameras were hacked and they played the Ukrainian national anthem all across
Russia there's a video put out it's kind of amusing but you know it didn't exactly stop the war it didn't cause protests you know it's just uh it's amusing um the one exception to an effects operation that was visible that I I believe is actually was not done by um independent civilian operators that was actually done by a state-controlled security force is when um the Crimean TV was hacked and it played an address from zelenski and I believe that this was coordinated with the states because it happened during an offensive um I believe it was the start of the cares on offensive so this was due to the timing this was I believe obviously linked to State
security services and the difference is sort of Fairly clear on the one hand you've got you know something being hacked randomly and like playing music whenever and then you've got something that is playing an address to the people of an occupied region which is being assaulted by the Ukrainian military you know it's very clearly linked to actual military operations um on the Russian side we've got like the various Russia Nets and they've done things which are very clearly signaling for the state so um there was a DDOS against Lithuania uh for you know reasons
um then there was this very interesting attack which didn't get a lot of press um it was in June I believe or perhaps very early July and about an hour before a missile attack on Odessa there was a call for um basically DDOS and other attacks against the Odessa air raid systems and that is very interesting because it demonstrates an operational link between the military and this group but it also suggests that part of what they are looking at is ways to make um attacks against civilians have higher casualty rates right like I think that that's very interesting um this sort of thing of going against air raid systems the Palestinians have done in Israel as
well so like this is a tried and true known uh way of going against a state so it's interesting to see it showing up here as well um so having looked at like some of the players and some of the hacks I want to talk about like the reason that you have cyber like if you're fighting a war the reason you have cyber is you want to be able to exploit it right it's got to do something for you like the entire value like the entire point of having the Cyber is that it gains you some advantage and then you can exploit that Advantage so it has to do something that helps you and you can then take
advantage of that help you can you know exploit it and that sort of like that's a way to think about the value that the it Army brings like what's the point if it's not helping you what's the point like what's the value so some of the things that have been um amusing have been sort of uh like rationales for why the Cyber Army does what they do um I haven't seen one from them but commentators have said things like um these guys talk about how they want to make sure that the Russian hackers are too busy defending that they don't have time to attack and I would like to believe that that was invented by the reporters and not
actually said by the Army because they if if they said that then they do not understand that there are two completely different resource groups available like the gru is not securing the [ __ ] uh servers for the TV station like that's not a thing that they do you can hack the TV station all you want and it will not interfere with a single minutes worth of work from the gru like that that's like that's not how it works ah anyway so what's actually useful um Espionage Espionage is really good right it's massively underrated but you know in the middle of a war knowing what the adversary knows and what they're doing that's very very useful stuff like
you can actually do something with that um if you know about your enemy you can uh start to influence their thinking you can start to um you know prepare things surprises for them you can start targeting their command centers you can do a lot of stuff that is actually useful in Prosecuting the war um but playing pranks like that's not Mission critical that's not very helpful so sort of uh collection is better than information is better than effects which um you know as I said before like this is a lie that's not really how it works but it's a useful way of thinking about it sort of generally and at a broad level to understand one aspect
um information operations again they're useful right shaping the information environment changes how people behave because you impact their sense making like that's really important it's especially important when you're talking about your allies because you want them to continue to support your efforts um it's useful though not necessarily uh against the enemy because you want to confuse them or deceive them make them depressed make them lose morale distress them you want to do it to your own people to make sure that they maintain the will to fight because you know the war is a contest of wills and so you want to keep that up um and in a way you could sort of say like everything is an information
operation um yeah you could go that far but anyway like they're useful but you know they don't really get the attention that affects operations do because effects operations look really cool and they're flashy and so you sort of um like when we think about effects operations it's worthwhile to sort of break them down into uh sort of elements that they consist of so there's the thing itself like the effect itself like uh if you disable if you deface a website like the website isn't self-defense that's a thing that's the effect but then there's also the perception of the effect like does this mean that the company running that website is no longer secure has other data being
compromised um does this mean that they don't care about their users and they haven't spent enough money on protection you know like there's the perception and then there's sort of like the psychological impact as well which is the like oh my God they're dominating Us in cyber we're being hacked this is terrifying they could be anywhere like what if they do the banks next um these other aspects like the perception and the psychological impact they uh like you acclimate to them like the more it happens the less impressive it is so for example uh now the ukrainians have had eight years of Russian cyber and there's very little psychological impact from being hacked like it just it
doesn't really phase them that much because it's a thing that happens all the time um and it's worth keeping this in mind because the stuff that the civilians are doing as volunteers are effects operations which means that they are making these effects Less impactful in future um not necessarily critical but something to keep in mind um similarly you know the quote from uh Bonaparte of the you must not fight with one enemy for too long or else you will teach him all your Art of War um and that's sort of that's a mistake that the Russians made with cyber in Ukraine so you know takeaways here Espionage is valuable info is critical affects the like contextually they can be useful
they can they can work with supplements they can be enablers there's a lot of ways that effects can be useful but in and of themselves they're not really you know uh as we said earlier cyber attacks are not attacks like they're not that important um they seem like the sort of thing that you'd want to do right like they get all of the uh excitement but the reality is like you just need oil changes like you need Espionage um that's how you win it's not through having something that seems cool and that sort of brings us into like where do these civilian volunteers fit into cyber operations and well they're not very good for Espionage right like
you've got people who are not integrated into the command hierarchy who have made up completely volunteers which means that they're going to include members of the opposition uh the enemy um you cannot tell them like what to get and you know you can't make it so that they collect on things that you actually need to know about because that's a security risk you cannot control where they go where they don't go um because all of this stuff reveals sensitive information about your own actual operations that they have no business knowing and that you do not want to broadcast to the opposition so you can't control them you can't trust any of the data that they get you
can't tell them what to do because you you know like they're civilians that you know not only do they not necessarily take Direction but any direction you give them is basically public so you may as well just print out publicly what you want to know and see if they do it from there and that's also not great um and you cannot trust anything that comes from them like they are as likely to be the enemy as to be trying to help you so anything that you do collect is potentially uh tainted uh messed with contaminated maybe even infected with malware you know it is not really a useful Espionage capability having just random civilians um going out and operating in cyber it's
not to say that there aren't ways that they can help there are certainly channels uh that this can be useful but it's more tactical than strategic it's uh sort of very much the you know where are the tanks now like that's useful uh what is the location of a um you know a bunker or a um Barracks or something like that these specific sorts of information are useful and they can be used and verified and then um you know if they're false it's not a big deal but for example if you were to steal like a male spool that's different um okay why does this matter well because it means that effects operations are basically the only thing that civilians
can do like the only defensive cyber that's left them is effect operations because they cannot do Espionage at a level that's actually useful and unless they're on the ground they can't do the Tactical Espionage so the only thing that sort of really left is [ __ ] around with stuff in a way that's going to cause problems is there a solution um yes there is so the solution I propose is information sharing and uh public private Partnerships um essentially like these are jokes but the the way that I think it could possibly work is if the civilian groups make the information that they have including their targeting and um their planning and sort of their
collection their take if they make that information available in a channel that can be collected and analyzed by state authorities then you know there might be some gold that shows up in that stream like that could be useful uh similarly that information could be useful in informing sort of where not to go because it's going to be ddosed for a while um that's basically the the partnership as well that I'm I'm thinking about so we're coming to the end and I'm only a little bit over so this is great news final thoughts so very very rapid this is one of those I was told that you have to like tell people what you're going to tell them
tell them and then tell them what you told them so this is what I told you strategic operational tactical Espionage info and effects um and also you know basically having a capability that exists in isolation is useless if you have the ability to cause effects but it's not under your control and it happens independently of what you are trying to actually do strategically it's worse than useless so um you know you don't want civilians [ __ ] around in your War um like civilian volunteers like this is um this is something for the guys doing the talent manual I'm sure they're going to be very excited to write about it it's a legal problem for someone else to
deal with um practically a way to organize these sympathizers in a way that's actually productive that's a challenge I don't have an answer I I don't know how you do it I do know that having them do defacements and DDOS and you know other random hacks that is not what you want um that is not helpful so those are the lessons we've learned um civilians must not conduct cyber operations without integration into the Strategic command hierarchy uh basically cyber should be left to state or state Affiliated actors because the stuff that's being done like it's not a game it needs to be integrated and in order to be exploited it has to be controlled and understood and
um you know integrated into the entire system that's you know fighting the war like just showing up and doing stuff on your own is not really helping um like these uncoordinated independent out of nowhere operations they don't really help and they cause more problems than not so if you want to donate to like the war donate donate to charity don't donate to bandwidth to DDOS so you know like where do the civilians go [ __ ] somewhere else like I don't get like don't come here it's a war go away all right that's it thank you uh we now have negative five minutes for questions uh so uh thank you and we have now time
for uh questions and as I we earlier there is already one hand is uh up there can the microphone run to the second third row
yeah there is a bit of a struggle to get the microphone to the Oscar thank you very much for the talk uh my question is how much did you mitigate information operations when preparing for this talk so how do you research something where all parties have incentive to muddle the truth shall we say um yeah like well there's a lot of echo okay so the information operation stuff is very very public um typically in terms of the uh actual stuff going on like I I clearly like obviously I don't have any uh privileged information about Espionage operations or whatever uh what I do have is uh access to people who um like either work in assistant organizations or people who
are familiar with what's going on and like they've passed to me things about like what is um what is the difficulty that they faced because of uh like the I.T cyber Army um in terms of like how things are done during war like um that's a thing I've been researching so I can generically state that like Espionage is a good thing that you want to do um in terms of like the information operations that happen um like we can see like again like that's a thing that I've been involved with is looking at um Russian information operations starting a little bit before 2016 um and again like it's a thing that we have visibility on like we can see
what's going on so it's like it's not as difficult um like it depends on what you're trying to do but like for the the purposes I have it's not that difficult I just need to know generally speaking what are the things they do why are they doing it and um sort of what is the result like and that's sort of that's fairly easy to get okay we have a next question I think thank you hello uh firstly I want to thank you about your presentation in your talk uh I would like to come back on your um the the thing you said about Cyber attack are not attack because nobody dies what do you think about people uh
dying about cyber attacking Hospital like in Germany if I remember well yeah so um it's a like it's a generalization that is useful to think about not that they're not that there are not exceptions but um typically things to things to understand about attacks are uh sort of like the psychological impact that they have so um ways of thinking about this for example are uh like carpet bombing uh the idea with doing strategic carpet bombing of uh an enemy nation is that you are going to beat the population into submission that uh you know dropping all these bombs will make them give up hope and lose support and the reality is that the actual psychological impact of the attack is to
make people draw tighter together and to resist harder so that sort of intended effect of the attacks doesn't happen it actually has the opposite effect cyber also has psychological effects which are uh counter-intuitive in a way so if you attack a nation you are likely to make them draw closer together whereas if you attack an individual you sort of get this um victim blaming thing that happens like in the industry we know like we've been sort of training ourselves and we're trained not to blame the victim but the public doesn't have that um they like they're not going to look at a Cyber attack against something um as equivalent to a kinetic attack against the same Target if you blew up a
hospital and it only killed one person that would still be a significant attack that would have a lot of psychological response that would sort of require a political response of some sort if you do a Cyber attack that kills one person you for example could not use that as justification to invade a country like you would not have public support at the same level because people will be going like why do why does like my brother have to go and die because someone couldn't install some [ __ ] patches right like that I I do not want my um my sons being sent off to die because someone didn't have budget for a firewall so in uh like in that sense as a tax
like they're not really attacks um but similarly like doing DDOS against Russia like it doesn't attack Russia it doesn't do anything that actually helps the war in any way like if attacking Russia in some kinetic fashion would help you know like it doesn't do anything it's inconsequential and it's meaningless in terms of the war itself um except in how it changes the environment and adjusts the security posture of uh people who you know ideally you'd want to have a very weak security posture so that they would be easy pickings for uh the Ukrainian forces so yes like a Cyber attack could kill someone but you know like that's uh like I think that's quibbling about
um specifics when the the point is more about like they don't have the impact of an attack and they don't have the utility of an attack and they're not reproducible in the same way um they're not sort of like instant um like there's a lot about them that are just not very useful in the same way that a bomb is useful but they're far more useful in a lot of other ways so anyway I don't know if that answers your question but that explains a little bit more of my thinking about it I hope thank you very answer that's really appreciate back there okay we will take one one question and after this question there is a question
for the crook which of the three three questions uh is the winning question but the question first the winning question is whoever offers to share the correct question hi thank you very much very much appreciated the talk the one area that I've become greatly concerned with is the bgp rerouting and so it's been publicized in the last few months that Ukrainian operators has been forced right to provide their Transit through a Russian operators so of course you know Russia now has all the intelligence for all of the traffic that's been rerouted to them um I believe that Ukraine is starting to use more of starlink right and so one of the questions that I have for you while
in the beginning months ago the Call to Arms for civilians might have seemed unstructured right it might be that there's actually strategic objectives both on either side but they they really need more manpower that once they then have gathered the intelligence and then maybe have targets and operational aspects that they will then use these volunteers to carry carry that out so do you see from your experience that there's more structure or or not um yeah and I I can see how that's appealing um but as far as I know um that is not the case there is like it's important to realize how State organizations actually work so the intelligence services are like the intelligence Services they're cool they
do Espionage they do Intel they do counter Intel like all this stuff they're civil servants right like that there are bureaucracy that collects information they do not really integrate well with just volunteers right it integrates well if they recruit people you know like they if you become an asset for them that's the thing they know how to do like that is a structure that they have and you can fit into the system that they have for managing um external people if you show up as a volunteer they do not have a way of processing that that's not a thing that they do um it is like and they don't change quickly either right like if if you want
like rapid change doing something in four or five years is considered pretty cool you know like that's that's a speedy flexible organization um so in the time frames that we're looking at like that's not a thing that can actually um like I would be very very surprised if the intelligent Services were able to create a way for civilian volunteers to assist meaningfully in cyber operations in the last six months um like that would Shock Me I I don't think that that's a thing they're going to do because as far as I know there would be more interested in expanding their own capability um which another way of thinking about it is they want more budget and more
head count right like they're gonna they're gonna look at it and someone's gonna say all right um we need more cyber now if you are the head of the Cyber Department the correct response is great I need more money and I need to hire more people because then I can give you more cyber the incorrect response is awesome let's just put something on Telegram and see who shows up all right like that that's not how you get promotions um that's not how you advance your career like that's just like that's not the way that uh State organizations work generally speaking um so like that there was this panicked call that went out and it went out from uh
the what's it like the the developing technology guy whatever like he's not part of the security services right like he's The Tech Guy and it's cool and like um they do good stuff but they are not part of the intelligence services or part of the military in terms of being integrated within what's happening in cyber so uh he was sort of operating on his own on that one and if you look at the um messaging that's happened sort of since I think they got a lot of pushback internally because you can see that the um like the way that they talk about things is very guarded and it's sort of a little bit open to interpretation so
if you're being generous you could go oh okay like these guys like the It Army um but if you know the backstory of how it's caused them problems you can see that they're trying to not say like these guys have [ __ ] us over I wish this hadn't happened without saying that like so um I think one of the recent ones was they were like one of the ministers I think that particular Minister was asked about um like recent uh like DDOS or something like that and his response was along the lines of you know we're happy with everyone that comes and assists Ukraine in our fight for freedom and you know like that's sort of how they're doing it like
they don't really like what's happened okay okay thank you group uh and uh uploads from the talent side thank you thank you and uh but as we have some merch for the those who are asking uh questions uh then you had three questions uh which one of these would you pick the first one about um about hospital and yeah I I actually like the third one because I get to talk about how um civil servants to Empire building which I think is it's a good way of thinking about Cyprus there's two sides to it okay thank you and I I think volunteers will help the win