From the Eyes of Overwatch: Intrusion Threat Landscape
Show transcript [en]
so hey everyone my name is jason and uh basically what i'm gonna go over today is what we're seeing from an intrusion perspective as well as best practices on how we can combat these different intrusions we'll talk about high level trends and a variety of different things we'll also dive deep into a few use cases so uh shouldn't be fairly entertaining let's uh i guess let's see where this goes so here's me i'm the director of the strategic thread advisory group and basically what we do is we help our customers operationalize their threat intelligence as well as their threat hunting capabilities prior to crowdstrike i used to be a uh i used to be in a big4 consulting firm
where i built thread intel programs for fortune 500 companies and government agencies and prior to that i was in the u.s army for about seven years where i did stuff at a nsa in cyber command so here is a here's kind of a review of what we'll be going over we're gonna talk at a high level about the purpose of threat hunting uh we'll go into an intrusion threat landscape so we can have some of the strategic perspective we'll do a few tactical observations all i'm actually going to pick some use cases that i think are going to be relevant to you guys and then we'll talk about how to engage in practice for hunting operations
so on that note let's go ahead and get started um so we'll start with the purpose of threat hunting and uh for me personally it's quite simple actually uh what it comes down to for me is this number right here so we actually took a tabulation of all the av solutions combined and on average and this includes crowdstrike by the way so on on average they all stop about 98.3 percent of attacks so what that implies is about 1.7 percent of things are going to get through so that of course begs the question so what what happens with that 1.7 so when you think about it like when you think about how endpoint security has
evolved you know back in the day you pretty much only have av right and then you know organizations were consistently getting breached and we realized okay that's not enough right in addition to having av we also need to have visibility which is sort of where your edr comes from you know it gives you visibility throughout your environment now you have the capacity to kind of look at these trends find a few more anomalies um the challenge of this of course though is that there will still be things that will defeat even edr as well because again both edr and aav these are automated detection systems right and for a smart adversary they sort of get it they understand how
these detection systems work and ultimately that's that's the purpose of threat hunting you know because like we it's it's the acknowledgment that we're not going to stop everything from an automated perspective no matter how much we want to no matter how hard we try there will always be those anomalies they get through and you know some examples of those anomalies you know let's let's take some let's take some uh you know just some basic ones right like a good a good spearfish something that actually it was is able to deliver either a malicious executable or route someone to a malicious url to where they interface with the url perhaps uh leak their own credentials there's a
lot of things that no matter how hard we try sometimes they're just gonna get through that would be an example of one of them another would be lateral movement so let's take a case where you have maybe a trusted third party or even if you have credentials leaked on somewhere like paceman or whatnot there are some cases where once again if the actor is doing everything in a legitimate manner if they're using legit credentials that are are you know high that are functional then that is still going to work and then same thing with the ability for actors to kind of navigate around on the machine using native tools things that once again aren't necessarily going
to set off you know an alert like let's take like powershell for instance or modifying legitimate binaries or using uh remote administration capabilities such as ps exec or rdp so like things like that right like there will always be things that technology just isn't going to stop and even beyond even beyond some of those fileless technique right techniques there's even advances in malware that are really also kind of changing this and making it to where even from an av perspective there's sometimes you know a pretty strong probability that we're not going to stop those either so here's here are three examples of what we're seeing from an advanced malware perspective in terms of how in terms of like how
these things are causing problems for organizations so the first one is around uh banking trojans that are developed by botnets so the back story behind this is uh i was literally talking to our intelligence lead one time and i noticed that we literally pumped out 400 indicators for trickbot within about two minutes and i talked and was like hey i think we i think there's something wrong with the indicator feed they just created 400 different trick bot variations and he's like nope that's how much these botanists can pump out if they want they can pop out literally a fort like that much in that small of a time span so the challenge of that of course is
now you're going to be overwhelmed by new signatures things that you've never seen before you know and then if you move over one to the right now you have custom compiled ransomware so in this case you know like let's take a lot of these major ransomware attacks that happened last year the organizations that got hit by those they're actually being hit by ransomware variants that were custom compiled just for them so essentially again you're being hit with something that's totally unique that the world has never seen before and then you know then you have the case of polymorphic malware and then with polymorphic malware that's a that's also able to change its hash every time it's leveraged
so you know you're dealing with a lot of different things that create again challenges for av challenges for detection so on and so forth and just to drive the point home you know this is becoming an increasingly costly problem to society here are some of the largest ransom demands that we were able to detect as of last year and as you can see the numbers are consistently going up and what what happens is that basically the more that these attacks succeed the more bold the actors feel in terms of collecting ransom payments um between late 2018 and through the end of 2019 the top actor that we were tracking wizard spider collected about a grand
total of 100 million dollars in bitcoin which once again kind of speaks to the you know to the severity of this problem so ultimately kind of here's you know here's the challenge right once again we have to we have plan to recognize that technology alone cannot stop all breaches and you know obviously like ultimately we want to be able to achieve two goals from a threat hunting perspective we want to be able to harden our security posture and we have to be but we have to be able to do this in a cost effective manner right and also in an efficient manner and then at the same time in addition to hardening our security posture
we also have to manage costs because you know all of us operate within budget constraints we have left and right limits you know we have to actually find effective ways to do things that are consistent with the resources that we are given and there's a lot of considerations here it could you know we want we want to think about things like risk reduction and the ability to acquire talent and then retain the talent so you know all of us you know our cyber security professionals we're aware that you know there's a big cyber security shortage across the industry so you know when you find a talented person it could sometimes be hard to retain them which
is yet another challenge when it comes to threat hunting you know there's stock security efficiencies so how do we do things that help reduce the time it takes for us to do those things that's another objective of threat hunting and then complexity reduction as well if we're using a million different tools that have a million different knobs and buttons and they all interact differently with each other that you know increases the time that it takes for us to react to events and thereby increases the complexity so we want to reduce that so let's go ahead and take a look at some of the strategic trends that we've been seeing from an intrusion threat landscape perspective
um so overall intrusions are increasing across the board oops sorry went backwards and for some reason this is loading the wrong way there we go all right so let's take a look at what we saw last year from an overwatch perspective um so overwatch is our threat hunting capability and what you're looking at here is the amount of intrusions that we saw between quarter one of 2019 and quarter one in 2020. as you can see here the state-sponsored ones remain relatively static and the logic behind that is nation states they sort of just have static operations they you know they have consistent objectives they don't necessarily surge in size or surge in operational capacity they tend to operate at a steady state
and the only things that really make them surge are major geopolitical events whereas if you look at e-crime on the other hand it's exact opposite we're noticing a steady e-crime increase over time and honestly to be kind of blunt what this implies to me is that overall is an industry that we're not doing the right things whatever we are doing it appears to not be as effective as it needs to be which once again really kind of speaks to the problem right we have an adversary that's getting stronger more capable and they're continuing to find ways to bypass our defensive systems so you know again this for me is personally a big reason why threat
hunting matters and you know one of the reasons i circled this quarter over here if you see this large spike within this last quarter uh in my opinion that is because of cobin 19. and what kobe 19 has done to us as a cyber security industry is that it has increased our own our organization's attack surface so think of it like this all of us are using the internet more than we ever have in the past we're making phone calls we're using more applications we're using more tools and all of those things create opportunities for actors to come come at us across our attack surface so that's another you know key theme here as well that we're looking at
this big attack surface expansion which is resulting in more e-crime attacks so moving on intrusions are also becoming more complex as well so i'm going to introduce a term to you guys and it's this term right here called distinct and sophisticated so there are basically two different types of intrusions that we see there are things that we've seen before you know whether it's like powershell scripts or command line scripts and things that we've seen in the past and we kind of know what to hunt against because we've seen it used elsewhere and then there are techniques that we've never seen before and that's what we call distinct and sophisticated intrusions so literally within a quarter time span
over the last quarter there has been a 50 increase in distinct and sophisticated intrusions the challenge of this is now that with these ones no one in the world has ever at least i guess that let me rephrase that not no one in the world but no one in crowdstrike which has a global view has ever seen this before so that's been very problematic for us we've also just we've also seen an increase in the raw amount as well so uh and in terms of as of as of may so as of last month we had observed 81 of the total of 2019 and like i said earlier uh you know the majority of these are e-crime and the
actual total number here is 83 and then also as of may we stopped about 18k total breaches so in addition to an increase in distinct and sophisticated intrusions like i said earlier we're also kind of seeing an increase in the volume as well so in terms of a breakdown like i said like it says up here you know 83 of these are e-crime and again it's not that the nation-states are doing less they're just not increasing or as your criminal actors are increasing exponentially um the top four industries that we've seen be targeted by e-crime actors are the technology industry manufacturing financial and healthcare and then the top five that we've seen being targeted by uh by the nation states are telecom
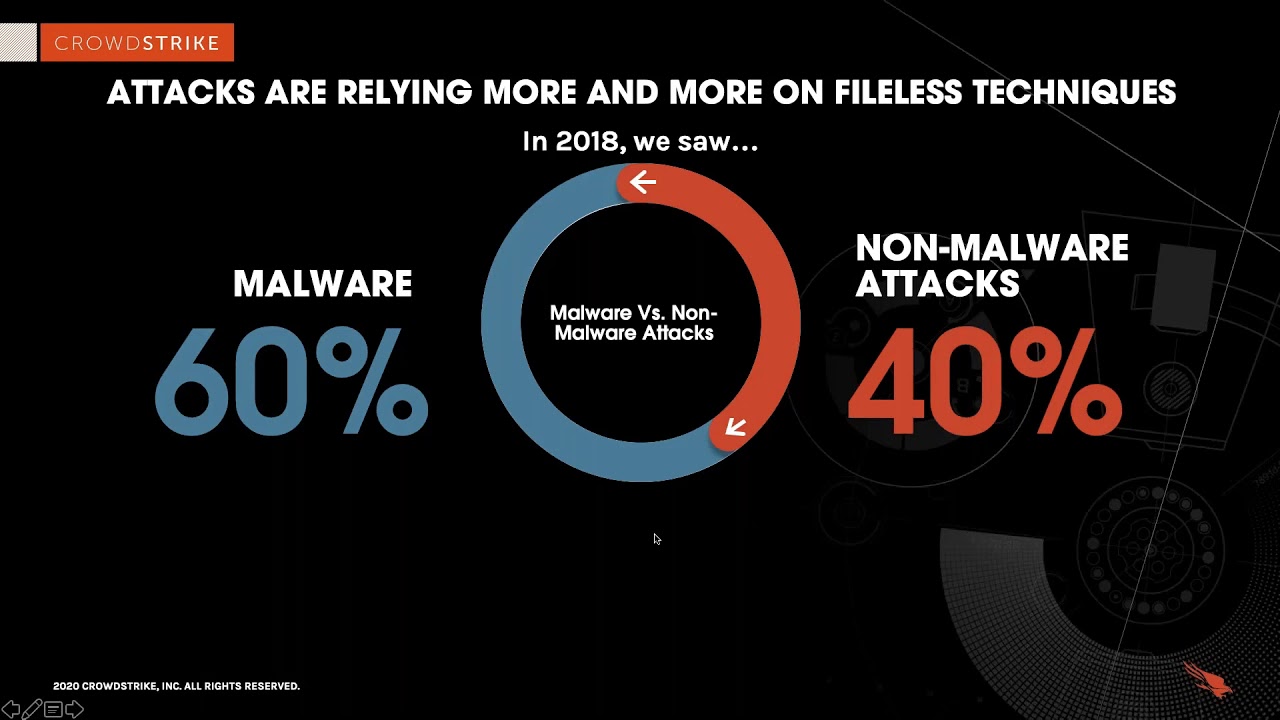
manufacturing healthcare media and government and that of course is the cobit 19 factor uh we we took a measure actually between february and march just to see what was the difference in cobin 19 themed files and literally you have it's it's went from about 10 in february to a well over a thousand within march so again we're noticing this for this tendency for actors to really take advantage of global trends as part of their uh as part of their attack patterns so the other the other thing that we're noticing is that attacks are relying more and more on fileless techniques and just to illustrate this i'm going to show you the difference between what we
saw in 2018 relative to 2019 so in 2018 we saw about 60 malware attacks and about 40 percent non-malware attacks and again non-malwares things like using legitimate credentials power shell rdp ps exec modifying legitimate binaries those kind of things and what we noticed was that the further up the maturity of the actor the better their ability to engage in these non-malware attacks so for instance organized criminal gangs in nation states that demonstrated a pretty a pretty significant capability to leverage those as part of their intrusion campaigns so in 2019 we actually saw for the first time the non-malware attacks be the overall more prevalent than the malware attacks so again this is yet another reason why
hunting is critical right the more time the more the adversary is able to evolve towards things that do not rely on signatures the less effective av will become and it does not matter how advanced the av is av is designed to detect signatures and even in the case of let's say something like crowdstrike right like crowdstrike does a lot of behavioral analysis as well again those things are based off precedent so ultimately unless we have a precedent we cannot create the detections for it so when you take the fact that adversaries are using non-malware attacks and as well as with the fact that we're seeing an increase in sophisticated and distinct intrusions that really creates a
challenge for you know defenders in general because now we're faced with a lot of things that we haven't seen before so here's what we're seeing by region uh basically what you'll observe is that the more mature the region the more likely the adversary is to use malware free attacks so obviously you see north america with now instead of you know 50 not now or free attacks closer to 75 so again this is very problematic right because the more malware free attacks that they use the less likely av is going to work whereas if you compare north america to latin america now you see that the adversary favors almost exclusively malware-based attacks and the logic behind this is very simple
what it really comes down to is the maturity of the market so think of it like this you know actors are opportunist and they're business people they want to they want to save time so like for instance in the case of latin america if they can execute these attacks you know using commodity malware and they can automate the process that's exactly what they're going to do whereas in north america they really they don't have that same luxury because there's a stronger cyber security posture in north america so again you'll notice that actors tend to pivot their techniques based off whatever the path of least resistance is so moving on let's take a look at malware as well because again it's not
necessarily just malware free attacks but we're also seeing consistent malware attacks as well so in general from an intrusion perspective here is that here's the prevalence of malware we're seeing and i want to emphasize that these are non-targeted malware families and what that means is these are the criminal ones that we're seeing so the most common one is andromeda slash gamma ru gamma rho i don't know exactly how to pronounce that but basically think of it as a modular trojan that is passed around by russian criminal communities it is it is a common trojan that they will leverage in order to gain access and then in many cases once the adversary gains access then they'll
actually sell that access to someone else who might be more well suited to exploit the actual uh the actual uh access into the environment second most common was coin miners which very simple just using computing resources to mine bitcoin uh third most common was emote so in this case again a very popular downloader we have js bond app which is basically a data collector that uh collects information from removable drives uh quackbot is another popular banking trojan and then you have go goes the isfv which is uh essentially another banking trojan variant so again this is kind of the prevalence of what we are seeing from a malware perspective so let's go into a few case studies um
i'm going to open up some ones that i think are relevant for you guys and the first one that we're going to talk about is something that we saw wizard spider do so wizard spider for everybody's context is the user of the ryuk ransomware so if you guys remember last year uh ryuk was by far the most effective ransomware used in human history uh in general it disproportionately affected four types of industries that was municipal and state government healthcare manufacturing and the education sector so what you're looking at here is actually a recent attack that we saw uh leveraged by wizard spider where instead of using their normal trickbot banking trojan to engage in the reconnaissance process and
the navigation process they were they actually uh because they saw that it was crowdstrike they actually used different processes so i'm gonna i'm gonna explain how that works so typically the the first thing that wizard spider will do when they gain access to your environment is they will seek to understand your security software so in this case wizard spider sought to understand the security software and they saw that crowdstrike falcon prevent was on the machine so what they did was they changed up their tactics instead of using malware to execute the attack they used things that that did not rely on malware like process injections and powershell and leveraging windows management instrumentation which is a network
management capability so here is the powershell here's the powershell capability that they executed where they're basically looking for different types of certificates and they're looking for information on the system and then here's the with the windows management instrumentation process they executed where they're modifying svchost.exe in order to again uh basically steal credentials that which allows them to move laterally and then ideally in their case what was it spiders seeking to do is find the domain controller we were able to detect these two techniques because we had seen them before leveraged by wizard spider and at this point once they executed these techniques we were able to kick the adversary out of the environment the next tactical case i have for you is
pinchy is an adversary called pinchy spider so pinchy spider actually let me back up all adversaries at crowdstrike have two names a first name and a last name the last name is the type of actor and the first name is the specialty so for instance spider actors are criminals whereas pinchy spider means they specialize in two types of ransomware they have the gan crab ransomware and then they have a more recent variant called the re-evil ransomware as a service so in this case what we're actually looking at is a hospitality entity that was targeted by the re-evil ransomware as a service so this has been problematic for a lot of organizations basically with ransomware as a service
here's what's kind of going on here let's go back to last year to kind of compare and contrast ransomware to ransomware as a service so last year on the large part was dominated by somewhere between five to seven really big ransomware operators and when you think about the majority of the money that was actually stolen last year in terms of bitcoin that was done by these really big ransomware operators you know groups like wizard spider and you know indrik spider and the ones that were leveraging some of the major ransomware types this year what we are seeing is a large preponderance of ransomware as a service ransomware as a service is basically when the ransomware operator
has affiliates so each each of these operators now have up to about 25 different affiliates so ins here's what's going on this year so instead of having five to seven major ransomware operators now you have five to seven ransomware operators who each have 25 affiliates working under them so i mean just some let's do some simple math here five times 25 is about 125. so that's one of the challenges that we're dealing with as an industry right now the velocity of attacks occurring against us is happening at a much higher rate because these ransomware operators are now taking on affiliates to engage in part of their in in attacks so here's what this actor did
this was a this was an attack that i think was enabled by copenhagen so let's think about what coven 19 did you know immediately all like we start we go into quarantine right we all have to work from home and with think about what a lot of businesses went through when they tried to transition to a work from home posture they're trying to set up vpns they're trying to set up you know a good rdp capability and in this case what happened was pinchy spider was able to engage in rdp scanning and they found an rdp connection with a very poor uh a very poor password configuration so they were able to engage in a password
spraying attack and they'd use that to actually get in so once they got in what they tried to do was they tried to stop different uh processes that were running on the machine the reason these actors will try to stop processes before executing the ransomware is because they don't want to they don't want you to be able to engage in incident response a common incident response practice is like let's say your organization's hit by ransomware an incident response team will often try to come back in through a hung process to see if they can remediate without getting the uh decryption keys from the actor so you'll notice that when actors go in they will often try to stop
these uh they're gonna try to stop attacks or i'm sorry stop these processes so ultimately we were able to detect this actor in action we saw them trying to stop the processes and we also saw them use it as a particular binary by modifying svhost.exe so this was another case where we were able to stop this attack simply by having threat hunting you know so again it kind of really illustrates the importance and then the last uh the last tactical use case i'll talk about is actually a nation-state adversary so for uh for pandas what that means what that means is china and what you're looking at is the use of a an implant called the cobalt strike
implant so what china does is they don't have like so i guess actually let me back up so cobalt strike implant the way i would think of this is kind of like metasploit it is a single malware framework that has a lot of capabilities embedded within it so once they are in though they're able to not if they're able to use techniques that are organic to the machine to navigate around things such as process halloween process injection the ability to steal web sessions cookies and then we saw them leverage several command line techniques in order to achieve their objectives uh with with this unidentified panda actor what they were seeking to do was steal credentials
and then navigate around and then ultimately achieve access to a target where they were which would enable them to engage in industrial espionage um this one was easier to detect than most uh and the reason for that is the first the first step that they leveraged was the cobalt strike implant and we had active indicators and yara hunts to be able to detect against that one so that was helpful and then also some of the stuff that they did was very noisy and where we were able to detect it relatively quickly but once again though it was this is what this is another use case where without the threat hunting capability it may not we may not have actually been
successful so those are our tactical uh those are our tactical examples and now we're going to talk about how to engage in proactive threat hunting operations so in my experience with threat hunting it sort of comes down to three big things like when you think about your own threat hunting operation there are really three big factors that you want to consider the first is data invisibility so you have to have something to hunt against you can have the most talented people in the world and the most talented people could have all the coolest and best tools in the world but if you don't actually have a data source and you don't have visibility on that data source
that you're not going to be able to hunt against so hunt against it so that's one factor right and then of course the other factor is the human expertise so you know i keep on going back this and you can't automate everything so if there is something that you're looking at like an automated threat hunting service uh i would question that because ultimately again the whole purpose of threat hunting is to be able to use human ingenuity in order to find and detect the other humans that are on the other side who are attacking us and lastly these humans and the data that they have access to need to now be able to use tools and
techniques in order to exploit this data and i'll talk about so i'll talk about some of these tools and techniques and some of the common ones we see as well uh as we uh continue through the brief so first i'll i'm gonna give you i'm gonna show you how kind of we do to crowdstrike so crowdstrike we use something called threat graph which is represented by this cloud here and then i don't i mean you guys may or may not be aware of this but basically the way that we do endpoint security is we put a single lightweight agent on the machine and instead of engaging in av and edr operations on the machine itself
we send the data to the cloud and then we send that we send that data to a database called threat graph within threat graph that's how we enable our own data and visibility so we have access we have access to you know 30 to somewhere between 30 to 35 million different endpoints across 180 plus countries we're looking at about 3.5 trillion events per week and everything we look at is unencrypted so that's one major advantage for crowdstrike is that we're able to look at this large swath of unencrypted data on the endpoint and something i want to emphasize is the value of data on the endpoint relative to data on at the network level and basically the
logic of it is quite simple network network level data will have more however it tends to be less valuable and it's less valuable in my opinion for two reasons reason number one is that about 60 to 70 percent of network of traffic is encrypted and if something is encrypted what that means is you do not have visibility and then reason number two is around the notion of attack telemetry so think about it from the threat actual perspective threat actors at the end of the day want to attack your endpoints they want to attack your laptops and your servers and your workloads and your mobile devices they go through networks to get to your endpoints so for those two reasons i do consider
the endpoint to be a superior data source when it comes to actually having a visibility the next area over is around human expertise so again it doesn't have to be like it doesn't necessarily have to be this way right but here's what crowdstrike seeks to do we want to if for us and the way that we engage in hunting operations we want to have a broad swath of different people who have different types of expertise so we have a lot of people who have come from commercial backgrounds who work from other vendors we have people like myself who come from military backgrounds law enforcement backgrounds as well as expertise in different systems such as linux or mac or windows you know
or different disciplines like understanding network forensics or being coming maybe coming from an application vulnerability background so again one one advantage or one thing that you would want to seek to really do in your own threat hunting program is to have people from a broad set of backgrounds because you're going to face a broad set of threats and then the other consideration in addition to the people's backgrounds is also the time in which you want to hunt so you know we do 24 7 because we're able to scale as a business and do that however you know that that may not be possible for all organizations maybe some organizations can only hunt from nine to five and you know that
that's okay right you you do what you can and it's all about you know doing what's most efficient for you in the most cost effective manner there is no necessary there isn't necessarily a right or wrong answer i mean obviously 24 7 is better than you know nine to five five days a week but at the same time again we all operate within resource constraints so that of course is a major factor and then lastly let's talk about some of the tools and techniques that we see so i'm going to show you two that we leverage and those are called hypothesis testing and intelligence driven analytics so i'm actually just going to load up this slide and i'll talk about each side
so this first one up here is leveraging thread intelligence to engage in hunting and leveraging threat and leveraging good intelligence basically with this what you are doing is you are leveraging intelligence that you've received from reporting or indicators and things like that in order to engage in your hunting on your in your hunts and the logic behind this one is pretty simple let's say you let's say you get a threat intelligence report about an attack that happened to one of your peers if that peer looks like you if that peer has the same technologies you do if they're at a similar line of business then it's very likely that the same adversary that attacked that peer
will also attack you so that is one area where crowdstrike engages in threat hunting that's one tool that we use is which is intelligence driven analytics and the other is hypothesis testing so hypothesis testing can be derived from a lot of things so for example crowdstrike does this in a variety of ways one way that we do it is that we leverage our understanding of other industries to hunt in the industry that you're in so let's say for example that you are a retail organization and crowdstrike is protecting you as a retail organization in addition to hunting in your environment we're also hunting in hundreds of other retail organization environments and we can take the data that we've seen
there and we can take the trends and then statistics that we've seen there and applied that against your organization so that would be that would be the discipline of hypothesis testing and uh sorry these aren't the only two but these are two of the more common ones that we we leverage so again kind of going back to like what is what is threat hunting it is a combination of these three things and you do want to consider each element you know whether you're going to build it out yourself or whether you're going to go with a with a partner provider so in terms of next steps uh here's kind of like you know coming back to the beginning right and again
let's replace this why crowdstrike with why threat hunting because it doesn't necessarily have to be crowdstrike you know ultimately our goal is to harden your you know the goal is to harden your security posture and also manage cost so i know from a crowdstrike perspective um you know last year we were able to stop about 35 000 potential breaches and we're well on our way to doing uh at least like about 1.5 uh times this number this year and then lastly you want to you want to be able to manage your cost as well right so i know for crowdstrike when we do it when we engage in complexity reduction we're able to save customers about 50k
on average in terms of save costs and tools because now you're consolidating into a single tool into a single pane of glass in a single environment uh on average we save about 120k in cost of the sock because we're able to do things in a more timely manner from a talent acquisition and retention perspective uh what we are observing is that the the average threat hunter when it comes to their fully loaded cost costs about 200k so when i say fully loaded obviously i mean things like salary and bonuses and whatnot but i also mean things like pto and technology costs and healthcare and insurance and 401k matching and all that kind of stuff right
on average what we're finding is that the average 300 cost about 200k total when you consider the fully loaded cost and then in terms of risk reduction you know that's another benefit of foot hunting as well and the cost of that is actually just dependent right you know if you go back if you remember back to that slide where i showed you the different ransomware demands it could depend very heavily you know the cost could be very high or it could be somewhere kind of in the you know the medium to lower range but you know you know ultimately kind of depends on the risk to your organization so that's all i have for today um you
know if you guys are interested in anything that i've talked about if you're ever interested in you know having a conversation about our throat hunting capabilities and how they can support you obviously you could reach out to us as us but again this is not the point of today's conversation the point of today's conversation was to be more so educational and informative about what we've seen from an intrusion perspective so uh on that note all are there any questions is there anything that could provide further clarity on for you guys
thanks jason and i don't know if you uh can see the discord but i can read uh questions to you so one of the questions comes from steve uh can you speak more about the fact that endpoint data is moving to your cloud unencrypted yes so think of it like this um actually i'm gonna find it i'm gonna get another slide that does this better one second
so think of it like this we want to be able to understand exactly what actors are doing for us to understand what actors are doing we want to be able to collect a variety of different events so for crowdstrike personally we collect 300 plus events on the endpoint so by event i mean things like powershell or moving laterally trying to log in changing a binary it could be executing a process it could be whatever right so that's the first portion is how many events are you collecting so traditionally this has been something that's been very hard for av let's take something like mcafee now you know again i'm not trying to knock on mcafee but i'm explaining why the
difference like what the difference is between the cloud and then trying to do it all on your endpoint so mcafee does all av on the endpoint because it does everything on the endpoint it cannot collect as many events it collects about 12 events and it tries to do all that endpoint security on your machine and the challenge of that is that the more it tries to do on your machine the more the more burdensome it becomes from a data perspective so the reason crowdstriking collects so many events is because instead of trying to do everything on your machine we take that data we send it to the cloud do all the heavy analysis there and then what our customers do is even
when they interface with their with their endpoints they're actually interfacing with the data in the cloud so we can process we have a much better processing environment here than we can on the endpoint so that's the reason that we choose to do it that way is that way we can collect more events do better data analysis engage in better protection and ultimately the goal here is to relieve the burden on the endpoint itself sure okay no i appreciate that um hopefully that answers your question steve i'm sure it does let's see another question is do you find it harder for people without a military background to break into cyber or rather do you think it makes it easier
with that military or law enforcement background um here here is my personal observation let's imagine uh let's see if i can find a slide first i always try to find slides to explain things i'm fired with that yeah so i can't find a slide on the top my head but let's imagine that there are three echelons of thinking the strategic the operational and the tactical tactical would be like hands-on keyboard and the ability to code and the ability to engage in malware analysis whereas like operational would be like working in a sock right so being like a sock analyst or a vulnerability management person or ir you know a lot of what we are kind
of on the in this conversation whereas strategic would be much more like higher like the political level and the geopolitical landscape and kind of the you know the strategic threats and that that kind of stuff right so what i find is that the military and law enforcement people they tend to have the better strategic understanding and maybe some operational understanding but their tactical understanding their hands on keyboard tends to be less mature than people who actually come from industry like commercial whereas a lot of my commercial counterparts are very good with the hands-on keyboard stuff they know exactly how all the tools work but then the further up they get towards the strategic that's where they tend to
uh have a few more challenges so i don't think i think it's just different skill sets or i mean that's ultimately what it comes down to for me like for me personally i don't know any coding languages i mean i underst i like i understand what i'm looking at if i see command line but i personally would not be able to enter commands like a hacker i could watch them and know what they're doing but i would not be able to do it myself so i would think of it as just having like different echelons of skill sets and one is not necessarily better than the other and that's ultimately why we work in teams because you know like not
everybody can be good at everything and you want to have you want you want to ultimately have people have different skill sets so i guess that's a long way to be saying that no i i do not think a military or a law enforcement background is at all required um i think the law enforcement background helps because of thinking like a bad guy same thing with a military background like it helps to think like a bad guy and i think maybe that is a benefit of threat hunting but at the same time we also tend to be less technical than a lot of our commercial counterparts so you know there's a little bit give and take ultimately
sure no that makes sense and i think that's what i've i've seen so i 100 agree with that i i spent a year and a half with the seals back in the day and uh definitely you can see where you know that strategic approach is is very strong uh where maybe on you know kind of the other end of the spectrum on on the technical side you're not so much and operationally yeah somewhere kind of a balance in between so yeah absolutely appreciate that yeah definitely let's see another question does crowdstrike have in-house threat hunting teams to hunt for or from external sources like the dark web so think of it as there are many
different operations within crowdstrike so for instance from an intelligence perspective we actually collect from a variety of different sources so on our intelligence helps inform our threat hunting so i've talked a lot about endpoint telemetry so obviously yes crowdstrike is amazing at the endpoint telemetry piece but that's not the only area that we get data from we actually also get data from these five other sources so we get data from our incident response practice so like when we go and remediate when we when we find artifacts and find out about new attacks we get data there we get data from our malware and forensic analysis team who's analyzing about 800 000 uh unique malware samples per day
obviously they're not analyzing all those manually but a good chunk of them they actually are especially particularly when we find new malware we take that malware apart we triage it in a separate environment uh we do hunt in the dark web and we call it underground communities because like honestly something that we're seeing these days is that the adversaries are actually using the dark web less and they're tending to favor things like whatsapp telegram and signal more and the reason they're going more towards these encrypted chat channels is the largest law enforcement and you know all the intelligence agencies they're everywhere in the dark web and you know after the shutdown of alpha bay and hansa market and some of those other
bigger ones a lot of the criminals actually realize like okay we need to stop being in these open environments and we need to go to more to things like encrypted chat channels so that that's actually what we're noticing the majority of bad actor activity is now occurring in encrypted chat channels um and then there's also network telemetry so we have different network devices as well as honey pots and honey nets that we throw into adversarial infrastructure and then of course there's open source data as well so i guess that's a long way to be saying that uh we we use multiple data sources and there is no silver bullet unfortunately i mean i think the closest to a silver
bullet we have is the endpoint telemetry like i think of the six of these probably a good 75 to 80 percent of our valuable stuff comes from endpoint telemetry but nonetheless we still have to do the rest because otherwise you don't have a complete picture sure no that makes complete sense all right i think that looks like it for questions a lot of folks saying thank you for your service and and i can echo that definitely thank you for all you've done thank you all right jason thank you very much for coming really appreciate you sharing uh i said i was really excited for you to come back and i could share with everybody after doing
the threat briefing with you last week so uh yeah i think everybody found it really uh helpful and insightful and uh really interesting so thanks again and uh say hi to josh if he's listening we'll talk to him on the other side but thank you again and take care awesome thanks for having me have a good day