Stranger Danger: Finding Security Vulnerabilities Before They Find You
Show transcript [en]
hello and thank you all for joining my b-sides perth session on stranger danger finding the ones before they find you i'd like to begin by acknowledging the traditional owners of the lands that we which we meet today including a special heartfelt acknowledgement to the wagonja people who are the traditional owners here in naramite i'm going to open with a disclaimer gasp i didn't see the asterisks on the talk no i'm joking um one of the things i always love doing at the start of my talks is i always start with a tech joke because it's important that we always keep smiling particularly in current times this is an open source joke so please feel free to well share
it any way that you want why did the vulnerability get tired because it ran somewhere ah get it hello um so my name is developer steve i'm one of the senior developer advocates here at sneak and i've been a developer advocate or developer evangelist for a number of years now one of the things i love most is just being able to geek out with community folks well all over the world but just in general on a variety of topics from iot to well security to coding to infrastructure as a developer a long time developer and i've been developing for a number of years now it's just one of the one of the things i love the most in particular
sort of talking or talking dealing with or um contributing to open source uh projects which is always one of my favorites well like i said i've been developing for a number of years now actually been coding since the age of eight q basic europe but i've been um also uh spent some time in digital agency building up campaign sites as a cto building out a payments platform um and even sort of building out iot projects or spending time as well i spent time as an analyst for 10 years one of the things i love most about building out code projects or building out applications is for the end users that i build those applications for as a developer as a
devops as an alter or all-round geek really but one of the things i enjoy the most about that is just building out some sort of experience that means a much easier flow of day or brings something to my end users lives in so many different ways if you think a shopping app or some type of entertainment app or a social networking app that just brings people together as devs as technology people we basically build these applications out to make our users lives just that little bit more easier interesting or connected one of the things i've always been mindful of building out applications through any number of different industry types digital agency for example is when
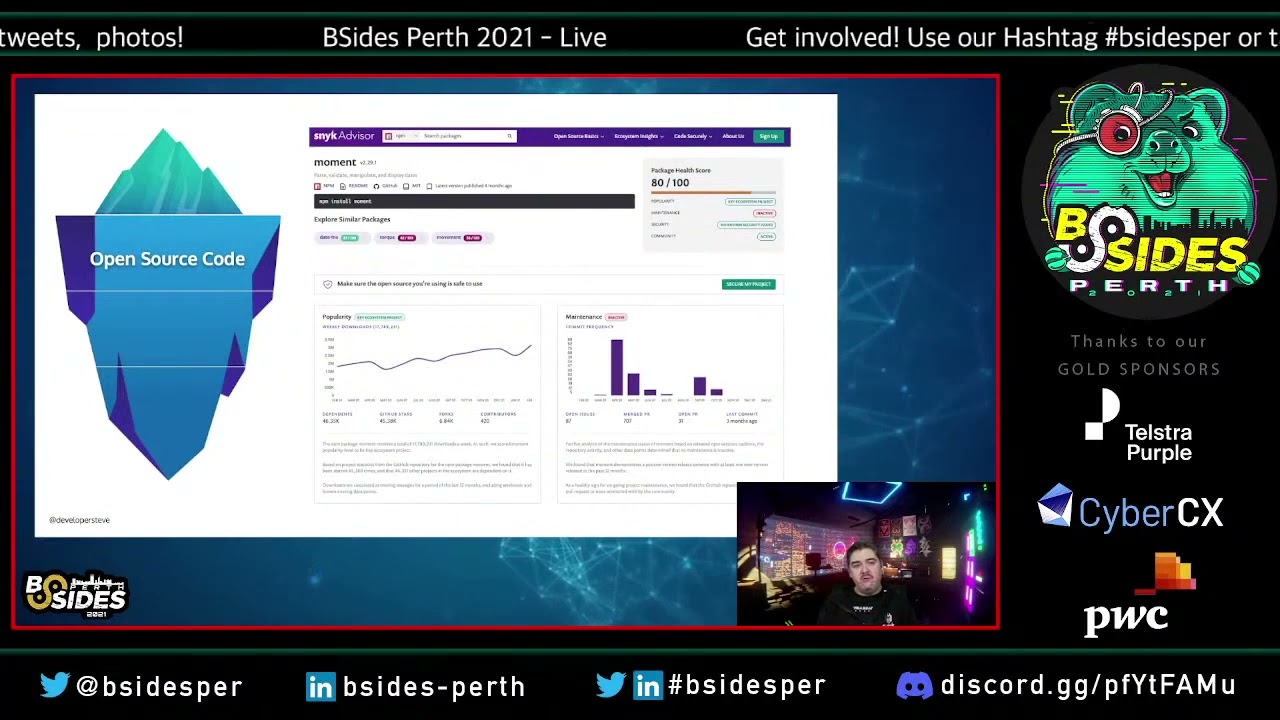
i'm deploying something just what else is being deployed with it even inadvertently if you think of the holistic app stack view as an iceberg the code that we deploy is basically that little bit at the top that's sticking above the water above the surface of the water but inside that there can be hidden things inside dependencies inside libraries the vulnerabilities if you will that expose our holistic iceberg stack application stack to the wider internet and to malicious actors across the interwebs it's no surprise that the there's an exponential there's quite a growth across the open source ecosystems as an adopter as a glo as a lifelong learner of open source stuff that's the the thing i love the most is
how the ecosystems are always constantly growing constantly learning and constantly building out new methodologies new techniques new libraries but with that also comes vulnerabilities being surfaced which we also see in exponential growth across the wider ecosystem or across the ecosystem set if you will so and that's no surprise particularly as new attack vectors are being constantly identified and that new vulnerabilities are being surfaced and indeed new techniques for identifying vulnerabilities being surfaced consistently if we look at the different ecosystem types something we notice um is an emergence of uh different how different vulnerability types are being surfaced in particular ecosystems if you take npm for example 80 of the vulnerabilities that are identified through open source
library use is through indirect dependencies so i install a particular library which in turn pulls in a multiple of other dependency libraries which is where the vulnerability type surface and there's a number of examples that we see in the wider industry ongoingly where a particular malicious dependency is injected into a popular library type which is then dispersed across the holistic ecosystem as updates or as installs happen indeed we've seen npm put out alerts before for particular uh package dependency types and how what sort of effect that that's had on the holistic ecosystem and i just want to take a moment there too to recognize that these open source communities do amazing work i'm a big
fan and advocate of a lot of the communities and the work that they do but more often these are communities run by volunteers so they need our help as technology adopters as to technology folks just to help help with identifying not only of threats but also potential fixes there's sometimes a time delay between the initial security alert being raised against a particular library or community project before that is not only identified but then also fixed patched and then a release candidate goes out so um just wanted to take a moment to mention that um always where possible particularly if you're using something contribute back where you can i know you all do i just like pointing it out
one of the ways we do that at sneak is through a program called sneak advisor which not only allows developers and technology adopters to be able to do some due diligence on the community and on the package in particular if there's any open vulnerability types or if um how quickly uh the vulnerability identified vulnerabilities through cve reporting gets mitigated get fixed and you know patches rolled out but also we work where possible we work with the community groups to be able to help get those patches underway and get those fixes in place we also help manage the uh node.js ecosystem vulnerability disclosure program as well and shout out to security researchers that help contribute to this and we'll just help
keep our end users safe which is what it's all about anyway i have some examples to run through i have an example i'm going to run through um actually i do have a whole bunch of these i can put links in actually while i'm doing this talk it's a bit better anyway let's let's let's hack it up so this first one is a demo app a javascript demo app that we have on the sneak github it's a goof app it's it's a basic to do app which is we use to demonstrate the vulnerability types that we're talking about inside one of the libraries one of the things i always love pointing out is as the 62 known vulnerability
types in this particular uh demo which is why this is uh you can try this at home but this is not for production local only um if you did want to try this at home there's an exploits folder already in the repo which goes through a whole bunch of different vulnerability types but we're just looking at one today so and the one we're looking at is a cross-site scripting attack um it's cross-site scripting vulnerability which is using the marked package uh and anything between versions 0.3.1 and 0.3.6 are well they're basically vulnerable one of the things i love the most particularly from the developer side of things is being able to dig around at the code level and understand the
fundamentals of the vulnerability more which there's all these great links to the the github pull requests and such that as you can see here you can dig into it some more and even see the initial report and then how long until the fix went out or if there's one still pending so you can do some testing on it anyway let's have a look at the app so like i said this is a basic to do app and as a user or as an end user i can basically input a list of items that i can check off or delete or whatever else the marked library which we're using 0.3.5 as you can see there on the
package.json we yeah we're using 0.3.5 essentially what it does it's a it takes user input from that that input box and then outputs that or stores that as markdown so add basic markdown stuff one of the things you can also see here is when we call the library and you can set a sanitized true flag which is super important i mean that should be set to default by oh that should be set to true by default right because we always sanitize user input uh what the sanitization tries to do as part of the user input is well it tries to sanitize it by a series of regexes and a series of match statements to try and determine if
the user input is something we wouldn't want to see stored because it can make the make the stored input vulnerable for the end user so this is a markdown so let's give it a spin this is a bold oops bold statement yes it is this is a bold step one of the things we can do with markdown of course is links so we can do something like that for example which is just standard markdown link and if i hover over it if i click that now it would take me to the place that i thought would think that it was going to take me one of the common xss attack vectors is using javascript wrapped inside a link
particularly when the stored user input is being resurfaced back to the user's browser session this is important because uh well knowing that this is an uh the way that most xss attacks happen because this is one of the vulnerability types that owasp talks about where one of the common vulnerability types that basically allows all sorts of malicious behavior to happen particularly in the user's browser doing all sorts of nasty things with cookie sessions and whatever else so injecting javascript is something that we would hope that sanitization is going to stop and indeed when i click that when i enter that you can see that it's stripped out well one of the other common ways to get
around this is to url encode character sets so doing something very similar but we're going to url some characters to try and get around that sanitization function and so if i enter that now again same thing it's able to identify it and it's stripping it out the way to get around this particular library sanitization what the the vulnerability is is by including a object type in or javascript object type like this means that the characters aren't matched and therefore isn't removed so if i enter that one you can see that that's actually been accepted and if i click that now i get an alert box that pops up and i've basically gotten around the sanitization
cleansing which is our vulnerability type one of the other demos i'm not going to do it today but i did want to did want to highlight it oh it's going to make me log in i did want to highlight it is we've also got this available in java and a few other languages as well this particular app so if you want to play with some of these yourselves please please do so local environments or developer environments only um but don't take this production but i know you won't i just wanted to mention anyway let's switch back to the slides so as developers again it's important why is technology people it's important that we help to protect those end users
that we build these applications for and then we build out and support our technologies for because again if you think back to that holistic stack view we want to do some due diligence first to make sure we know we're letting into our stacks and just taking the time to make sure we keep people nice and safe and secure of course now we have a whole bunch of really cool scalable technologies that add to our holistic iceberg view stack allowing not only some elasticity to be built in but also we can add in all sorts of cool things like redundancies and whatever else essentially our applications now become way more than our code because we can
also control and guide infrastructure as part of our deployments if you take docker for example there's been over 242 billion downloads from docker hub to date which is phenomenal and as like as dev as a devops as a devsecops this just means that i can build out applications in my own containerized local environment and then deploy them and have them elasticity elastically build out as i need them to but it's no surprise that we also see the same vulnerabilities appearing in known docker base images consistently also given that they're built from the same open source components that we've just been talking about consistently year after year we see the top 10 docker base images basically
carry the same vulnerabilities with them one of the things i always love to keep in mind with this is with great containerization comes great responsibility and keeping your application clean at the code front is just one step of that holistic iceberg view to protecting those end users the last part of our iceberg is infrastructure is code where we also get to do some really cool automation stuff and i love automation i'm not a lazy dev or a lazy devops i just love it when automation works first time and i'm always looking at you jenkins anyway one of the things i love most about iac is just being able to set up some nice gate controls so that as i deploy my
application it can go through some automated checks before it finally gets deployed of course it's always important to remember to make sure you're consistently reviewing and checking not only those gate controls but also the files that you de you're delivering and building this infrastructure out with as well because consistently we see as the infrastructure continually updates or continually goes through that whole industry maturing we also see new vulnerabilities surface in the form of configuration vector issues so it's always important to make sure you're constantly reviewing those and checking those as well but we missed something most important the most important part well at least part of the most important part this one actually kind of scares me a
lot given well i have a develop like a local development environment don't we all but we're also seeing the same vulnerabilities now start to surface in developer environments as well or dev environments which i mean that's the plate but like people need to leave that alone that's my place where i build things um what we're seeing now is particularly with the likes of homebrew and also vs code is a lot of the extensions and add-ons for those particular ecosystems are built from the same open source components that we're seeing these vulnerabilities surface in so the likes of latex workshop open in default browser and instant markdown for example we see vulnerabilities like file traversals which are now starting to
create surface vulnerabilities in dev environments instant markdown which i've got the link for on the on the screen well it's on my github as well there's a demo to walking through how to how to basically play with or demo that particular vulnerability if you do install that particular version of the s and sorry the instant markdown please make sure you upgrade to the latest version because that version don't leave that one installed by any means please don't that particular version's vulnerability basically gives a remote attacker to be able to access your password file or basically any file on your mac so um yeah just please be aware of the vulnerabilities that are now starting to surface in your dev
environments as well because we're consistently saying this is an ongoing issue homebrew actually put a a blog post out about this back in it was april or may um saying that there was some vulnerabilities being surfaced so please be aware of what you're installing anyway final takeaways always be scanning source code containers infrastructure just take the time do some due diligence protect those end users because well we love them so much that's why we built the things that we built again please be aware of what you're installing in your local dev environments um there we're seeing this is sort of a growing attack vector now and all sorts of nasty things are starting to creep in so particularly if
you do do install something locally you just brew and store the thing and you're not using it just brew and uninstall that thing that you're not using just remember to clean up your dev environment where you can as well and lastly uh please use your text super powers for good always remember i do love that gif um and always remember to be excellent to each other thank you very much