Clean Forensics: Analyzing Network Traffic of Vacuum Bots
Show original YouTube description
Show transcript [en]
with that uh we're gonna get it started here uh quran with uh google and i don't know i'm a little scared now if i don't want to use my vacuum cleaner um but i'm gonna i'm gonna hope i still wanna use it at the end of this call all right thank you all right welcome everybody i know this is the last talk of the day but i promise i'll keep this short um if i do get audience participation i have a bunch of swag which i'll talk about of how you can get it during the talk so i know people are still trickling in but i'm just gonna get started and we're gonna talk about vacuum bots today so
everybody with me all right that's what i need cool all right so who am i i am karan you can call me kay uh i'm an engineering manager at google um i graduated from carnegie mellon way back in the time i don't want to state my age i write security engineering interviewing articles at my blog and for fun i travel go to the beach quick disclosure like i work for google but this research is done in my own time so there is no relation whatsoever um with them all right so what are we looking at today um we're gonna see why research vacuum bots but like before i go into all of this stuff how many of you here
have a vacuum board or plan to get one oh wow okay how many of us think they are secure awesome i've had i've had people like a few brave souls raised their hands before the talk and after the talk they were all anyway so we're going to talk about why research vacuum bots we're going to see the functionality right how they actually function then i'm going to show you a technique of how you can conduct network forensics by your own at your own home right we'll walk through some security and privacy concerns now the next final part is the most interesting one i'll walk you through how i reported issues with the vendor and the response
and finally i'll take time for q a i think we're allocated about 10 minutes at the end so please hold off your questions and then we can answer them one by one all right all right cool the real agenda is about swag so as as i said uh i have some nice titan security keys with me which i'll be giving out during the course of this talk um as long as i get the right answers from all of you yes okay so let's jump in uh why research vacuum bots so it's very simple right if you look at the market that's uh going on from 2016 and future projections it's very clear that from this graph thank you grandview
research every year the vacuum bar industry is going by 17 given the number of millions of units sold think about that for a second they are there literally everywhere right the market itself in terms of revenue is growing by 23 every year by 2027 there's going to be 60.9 million of these bots around us right if you look at the top [Music] major players in this industry right there are a few i've listed them down on the left but what i want you to take away from this slide is the right hand side right notice that it's not dominated by any particular vendor right but it's also not fragmented so it's kind of in the middle and that's
very interesting from a security point of view because you can have a lot of issues from one vendor but none of them from the other right all right so let's jump into some functionality right i'm going to go a little bit quick but i want to preserve time at the end for the most interesting stuff all right so bots have different functionalities right they can be cleaning modes like you can just say hey bot go clean my house that's an auto mode it's gonna do its job right hopefully um if you say edges is gonna go around the room so like in this room for example edges would mean going all around this room right the rectangle that we are in
the spot cleaning is just like oh here's a dirty spot clean it for me and then manuel is like you direct it step by step right and say go left go right go front go back um what's interesting is you can even set these bots to run on a schedule so for example for somebody like me who doesn't want to get up in the morning i can say hey bart clean my house at 6 00 am let me sleep right so you can set that up and finally you can also monitor some of the health of accessories so i want to know when do i replace the brushes on my bot and my bot can tell me
that that's cool right some bots also come up with a functionality like floor mapping right so let's say you leave a bot here it's going to figure out how this room looks like that's called floor mapping it can also figure out if you have more than one floors so for example you have you know the first floor and then you have the second floor of the house depending on where the bot is it can intelligently figure out which floor it is app so some bots have this feature not every bot has this feature so i just found that in my research and finally in in a few bots there's also live video honestly that scared the out of me
when i saw that i'm like so with that understanding let's go into how you can set up a bot right and this is a generic example right i'm just going to go through a general process it's not true for everything but it's true for most things so let's focus on the diagram on the on the figure here right in the black box you see that's the home network so i have the phone which is you know any smartphone you have just like i have here i have a cable modem in my apartment to talk outside to the internet and then i have a bot at the bottom right in the home network when i just get a bot from you know i
just buy the bot and i get it in my apartment i would install the app on the phone right every manufacturer has an app that you can install create an account the very basic process right when you do that it's going to create an account on the manufacturer's website right that step the first two steps the next thing that's gonna happen is the app is gonna search for a bot near the phone right so it's gonna say hey any bot nearby right it's interesting because these bots are configured to create a wi-fi network right a temporary local wi-fi network and what they're gonna do is they're gonna say oh i'm here join this network and once you join that network all it's
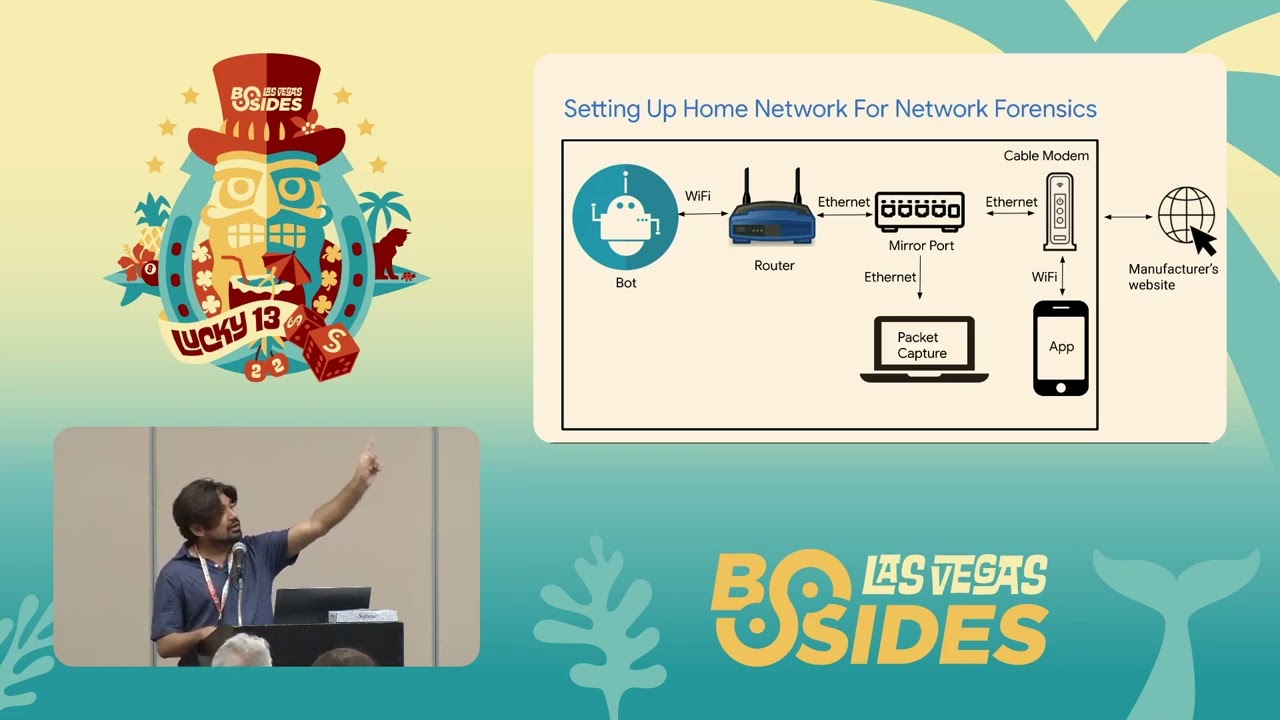
going to do is share your home's wi-fi credentials with the bot so this is just a way of sharing the username actually the the password for your home connection right and once the bots get that they're gonna associate the bot to your account is everybody with me so far cool awesome now that we have an understanding of the bot how to set them up let's talk about how all of you can set up your own home network for cheap so i literally took a screenshot actually sort of sorry a photo of my own apartment when i did this to prove that i actually did this and i have three components to it right three major network components one is a
router on the left the one is a switch in the middle and then there's a cable modem at the right right i'm going to ask a question and i'm going to give out a titan key what do you guys think is the cost of this network equipment including cables approximately the shout out numbers 75 who 400 450. 19500 350. 500. the last one too many too many let's let's go one at a time 50 who's who was who was closest to oh sorry i'll take one last one 125 it's actually 150 bucks so you're the closest i'm gonna give you this
[Applause] [Music] sorry it's hard to hear everybody in this room i apologize yeah so approximately 150 bucks right um i didn't include the cost of the devices i had but it's not very expensive to set this up all right now let's look at the same figure how it looks like you know in an in this icon form just to make things very simple because here the cables are super messy right you cannot tell what's connected to what so let's look to get this from left to right okay so the bot talks to the internal wi-fi network okay which talks to the switch which forwards packet to my cable modem which then talks to the external world so from left
to right is a communication from the bot to the external world all right and the same connection goes back so if the bot gets a response going to come back to the cable modem to the mirror port to sorry to the to the switch to the router to the bot all right to look at all the traffic going and coming from the board i have a mirror put on the switch so i can see everything that the bot sees right and i've connected a machine with running a packet capture right so i can see everything that's going across notice one thing the app is talking directly to the cable modems wi-fi not to the internal wi-fi
and that's because i don't want to see the phone's traffic yet right so i can segregate the networks does it make sense all right so with that setup and with the understanding of bots let's look at how you all can conduct forensics so what i did was i you know i bought bunch of bots right and for every setup and every step that these bots can do for me like for example the setting up that we talked about the move example the clean example the live video example i did all of that for bots and i packet captured everything right that's the methodology i followed and then i took those packet captures and sat down for hours and analyzed them
it's pretty boring work but that's what i did so let's look at an example of how this looks like on the network right so on the network i know it's a little bit small so what i did i wrote stuff down and i want to talk you guys through this so basically the first thing i found when a bot talks outside from your home is a very simple dns request right in most cases these bots are talking outside to a cloud provider right so basically my home is configured to use 8.8.8 which is google's dns um and uh basically the response i get is the cloud provider's ip right so this is obvious step one right
uh-oh
you unfortunately brought this on yourself yes uh you reached the outrageous speaker request portion of the evening our fine friend here has told me that he didn't realize that these things were cool and that uh he was hoping that i would do one for him and i said well do one what he says well i don't know i like root beer so i said okay what we have here is two bottles of root beer chilled delicious high quality however one of these bottles has been shaken and the other has not you're going to join me here at the chair okay the game begins when i put these on the table this is the new mag
over here over here that's why we got the chair the game begins when i put them down between us then you will choose and we will both pick up our bottle and open it we find out who wins and who loses are we gonna do it there
before
guys [Music]
[Applause]
all right thank you for the surprise i just asked for a root beer and i get to play this game so [Applause] it's awesome all right so was everybody did everybody lost track of where i was i did anyway um yeah we looked at the first dns request um so the ip threats return is for the cloud provider right that's the first step after this because the packets are really like big as you can see i captured the essence of the traffic from the following slides so what i observed is when you press move right let's say you say turn right right what happens is i see the following text being exchanged on the network
right so the server to bot says hey bot move turn right and the turn right is actually in xmpp does everybody see xmpp here see that's not it yeah so you see the move and spin right as the action that's what i see on the network pretty straightforward right but then the bot also goes back to the server and says result 85 i think that 85 is the is the id of the request right so that's a very very simple example that i saw on the on the capture similarly when you say oh clean the house right so it's it says okay i have the auto setting on i'll clean it with the speed of strong
this is the extra data i really like to see um and then it finally says okay i cleaned it the clean report is that right so exchange of packets i also saw keeper lives so this is something i didn't really think about but then it really made sense to me right so if your bot is is connected to your home network and it's not running it's not doing anything it may still communicate out and say i'm still here make sense let's talk about authentication because we never talked about this is a security conference so what are we doing right um there are two ways of authentication that i found right one was sasl um sasl can be used with you know a
number of protocols but in this case i actually saw plain text passwords we'll talk about vendor stuff after this so we'll see how that goes and then the bot says success all right fortunately not all bots are like that some bots actually say hey i'm gonna use mqtt mqtt is for iot devices for those who you may not know but it's secure so it can use like 8.8883 and it can communicate out from that port and it does not use plaintext so while that's a relief i was not very happy and finally i also saw something very interesting when i did not do anything so when i when i have a phone right and i open the app on the phone
as soon as i open the app i saw these packets i saw this data and i'll walk you through what that is right so as soon as i open the app i see a request called set time and i see the time those numbers one six five one five right that's an epoch time so time since 1970 is january 1st right in seconds and it says tz timezone i assume minus seven basically what's happening is the bot is getting the time from my phone because i was in california at the time so timezone makes sense to me and it's setting its own time as my phone's time anybody see issues with that people are nodding their heads
you can tell where somebody is exactly i think that's what you were saying thank you yes and we'll get to that uh later all right so i guess people must have figured out the issues but i'm going to walk through them and show you the interesting parts so can somebody control our bots can somebody hijack them right and there are two ways of looking at this one your local network right can somebody be in your home a friend walks in as like hey i want to use your wi-fi cool and starts monitoring your packets can happen um and the second one is remote attackers right can somebody just external you don't know can they hijack
the bar well if somebody is local then yes they can replay commands right if there's no such nonce there's no such identifier that's unique they can do replay and it will work for for remote that's not very easy to do right the easiest way for a remote attacker to get control of your bot is to just attack your credentials figure out a way to get your credentials and they're in and as i kind of expected there is no two-factor auth none whatsoever what about floor plans so we remember the bots can scan your home right all the floors if you want them to the the way these bots store that data is either on the app so locally on your
phone or in the cloud right again like it's it's a part of the app so it's data on your phone so if your phone is vulnerable yes you can get that but app credentials are again the easiest to get through that right and by the way this app does not need to be attacked by its own you can have other vulnerabilities on your phone that can compromise the app so your full plan can be leaked right so there's so many ways that your floor plan can be leaked not just because of a particular app in the research i did i did not explicitly discover that this was being leaked like for example i did not see
any packets but that doesn't mean it's not a possibility right somebody rightly mentioned actually two people course location right and this is this is very spot-on as the user moves around the bot will say oh i am this time zone and actually i actually discovered this accidentally i was i think i was messing with my time so i was traveling i don't remember but as soon as the time change on my phone the bot had a really messy schedule of cleaning and i'm like something is wrong and i figured out that it was this this was the case right so the time zone had changed on my phone the bot thought oh it's like a.m pacific when it's really like 6 a.m
or 12 p.m right so it really messed up the schedule everybody with me so far all right awesome i have two more swags to give so let's talk about video recordings right here i try to show you people how it looks like on the network right i know the text is very small because wireshark but if you see on the right there is some metadata that you can capture just by looking at the traffic so thankfully i don't see video itself like i don't see any video encodings being passed around but i do see metadata involving that recording so for example it can say oh start streaming at this time right so i can figure out when the live video was
started stuff like that as you can see on the left um there's udp traffic so pretty obvious right it's it's video um but yeah nothing very sensitive all right the fun part begins so i took all these findings so i took me a few months to figure this out and i wrote a really long email to the vendor and to prove that i did i took screenshots so you don't have to read this i already described all these issues to you all of you but i just did to show you the dates and my name so notice the dates so right now the first email or first notification was november 18th 2019. i don't know it's a bit small
but i'll say it out loud november 1819 first report right i say hey report of these issues blah blah blah and a big detailed email on how i found them all right i went on to describe more issues so i said okay using insecure protocols xmpp potential man in the middle right course location tracking i go on and on and on i don't know who read that email sorry um and then finally left privacy of floor plans so i wrote all of this and i said help please fix this all right can anybody guess what happened next i'll take one by one i know a lot of hands i'll start from here can you please be can you please be a
little bit louder they sent the lawyers oh god i'm still here but yes that's a good guess i'm sorry it's not a bug it's a feature thank you amazing reply nothing nothing good one sorry let's do it from the front
automated response exactly so they said they said oh hello we love to hear what you think of our service and they asked me to rate the response somebody said no response that was close but i still got a response so she's more accurate [Music] all right so i wasn't particularly happy after putting all these hours and stuff so i followed up and said hey like this is not done i need something back can you please take a look so that's the reply i sent back i basically said you know responsible disclosure you have 90 days right i can go out in the public and talk about this but i'm not going to do it because i
care so you know please take a look december 17th after almost a month i heard back a response right and the parts i want everybody to read are the one in red it basically says we have implemented xmpp which is an older model okay all our new models use secure technology to ensure user security does that mean the older models do not ensure security i don't know so i followed up again and i said hey this is not done right february 19th so we are now from november to february right they said thank you for your concern we appreciate the feedback i'm passing these notes to the application team you know all of that so i said okay i'll wait
i still didn't disclose march 30th i said hey it's been a long time can you assign a cve or cwe something to give me credit um please do not delay this matter any further there are millions of these balls out there thank you for your prompt response okay after seven months july 28th right so from november to july i finally got this response it says thank you for writing i mean they've thanked me three times i i don't think i want that and then they said we have escalated your concerns to the related department what department one final guess what happened next i'm gonna take five people just to save time start right from the back blue gentlemen
please yes they just closed it and they closed it they didn't disclose it i disclosed it oh okay i'm that's what i'm doing here now
so bribe me so the response was they offered me a new model to not disclose this well i it didn't happen and i'm still talking about this three more people um gentlemen here they closed it they ghosted exactly
yep so even today i don't have a response however the newer models seem to be more secure and i wonder why in conclusion if you think about these iot devices they're all over the place right they use insecure protocols it's very challenging to get a response like look i understand that you want to ship to the market right this competition but it's very hard to balance security and privacy right that's where i was coming from and out of this talk if you don't take anything just take that you know cannot trust any device right away right figure out a way to research this on your own that's the real takeaway and you can do this for really cheap cost right you
want to spend a lot of money um and if you have any questions i'm happy to take them now but thanks for keeping it clean [Music] i think i ended like 30 minutes early so uh yes
yeah so the question is did i reach out on twitter and tag them that's a good idea i just didn't want to take anything publicly so i did not i just wanted to document everything in writing but maybe in the future i will yes i'll take all questions now i'm not selecting people so yes
yes so the question is did they issue a cv or no they did not issue anything there's there's no public disclosure or vulnerability around this but yeah uh people can use the mic so i don't have to like come back if you guys don't mind using the mic that'd be awesome um yeah so just from a purely pragmatic perspective of someone who wants a robotic vacuum but hasn't gotten one yet because of all the privacy issues and i don't really care whether it violates my privacy securely or not are you aware of any other any other research or any research you've done yourself into like modifying them just purely for personal privacy or any that are better on that or
anything like that so sorry your mice moisture voice was a bit muffled but i think i understand your question you said are there any other security privacy research around this on other bots and overall right specifically just to a purely pragmatic perspective of like modifying one or which one to buy from a perspective of just enhancing personal privacy while using one yes so we have a conference this week called defcon and uh if you look at previous talks of defcon there is actually i think one or two talks that break down a particular vendor and talk about it so i can share the links later but there are existing work on this yes hey uh thank you very
much for this talk by the way i really appreciate this is really eye-opening um one thing i wanted to ask is do you suppose do you know what maybe hardware they used inside the bot because i i know like esp like 88 32s or whatever i mean they support ssl they're like a dollar and i just don't understand like you can get you can go out and get the certificates you can validate the cert chain i just don't it just seems like even like dog one dollar microcontrollers can do this like what's the point i don't really see the time to market the tcp stack is built into the esps i believe it is right i've done asp and i never had to
do anything tcp it was just there yeah i just don't understand like what they're missing i've done sassel on xmpp but it was encrypted right i i wasn't on a vacuum bot but i just don't understand like do you have any idea like why when it's a dollar to just get this amount just block your thing lock the thing out put ssl on it get the full searching like what are they what are they gaining by this like i just don't understand 10 years from now the bot might not work because a new ca came out or something like that i anyway i'm just curious if you have any ideas on that oh no excellent point right as you said
it's not very expensive to build in security and by the way this is a bot i tested in 2019. so i'm sure it was released a year or two ago so we are talking 2017 time frame maybe um at that time maybe there was a prioritization decision i honestly do not know the answer but i'm going to make some educated guesses right maybe there's a competition to ship products maybe there is something that they want to prioritize as a feature but not as security maybe they said okay a password is good enough we don't really care about like the technology so much it's working let's ship and let's reiterate on this um one of the other reasons i've seen is
they have improved security iteratively so the newer models as i said are better right so maybe that was a backlog i don't really know i'm gonna guess those were some factors if that makes sense yes did you uh can am i muffled can you hear me sorry i can't i have a hard time hearing you i was going to say my mouthful can you hear me um did you try any like so one of the interesting things is that i've found similar vulnerabilities in devices like with network attached devices and when i made the disclosure i explained that you can use the stun protocol in a web browser to be able to detect these devices within the network right and
then send packets from them within the network without having to be physically there did you investigate those kind of things because it looks to me as though you might be able to do a cross protocol attack from a web browser onto the the roomba like device itself without having to physically be in the network and then primary defense was like oh you have to be physically in the know what to do which i disagree with yes so that's a great point so there are some bots for which there's emulators written out if you can find them on github right and you can say oh like i don't need a bot i can emulate the bar
and you could do it on your local network right away and the moment you do that that means that you can send commands to a real bond by capturing how the emulator works so you mentioned stun yeah in this case i didn't observe stun but like that's an example that you can use i wasn't saying that the bot itself was talking stunned but you can use us a couple of different web apis to be able to discover the ip address of these web or it's not actually a web protocol but it's a protocol that is plain text so you can send it over a web browser okay then you can when a victim loads a web
page you can get the web page to send requests to the robot by using these apis to discover its ip address and that would allow you to bypass the whole like you have to be physically in the network restriction yeah i think i understand what they're saying i so for my research the scope was network and not i didn't go to the web browser and send apis hey that can be a follow-up research on top of this yeah you can definitely send xml structures over the network to devices exactly hello uh great talk by the way um i was wondering in regards to the the robot having its own wi-fi uh when you when you initially set it up is this
something that is always exposed and and do you know if there's anything more you can do with that to trick it into taking commands or so yeah so i i didn't dig deep into that specific ssid because it's like temporary they just if you press a button on it that's when it pops up okay but i i will be hesitant to say that they will accept commands because the bot is not set up yet the bot is not registered with an account yet like it's not associated so i'm gonna guess no but given this i don't know there might be some new ones that they have not really you know tracked that really well so
and one more was uh have you have you heard about the incidents where there are just people sending out cleaning commands to their neighbors and stuff and messing around with their bots i have not i mean given shodan and everything around us you you can write to talk and deliver it right here that'll be awesome all right thank you yeah so uh my question is uh did you test the same did you see the same packet uh pattern in the new updated version i did not so they started using ssl that was good so i did buy some recent balls i'm not gonna name them but i could not see anything on the network i was very happy
with that for some reason and did you saw those pattern in one specific vendor or the previous one in one specific vendor or okay i'm not gonna ask vice president or you saw it in multiple vendors yeah yeah so this was one particular one but i did test several of them and i think in the last two or three years most are using ssl so you will not see most things on the network and that's why i'm actually able to give this talk because it's over now thank you thank you so you mentioned that it's more secure are the newer iterations of their products tend to be more secure and i just heard that there's ssl yeah i'm
wondering if there's a if there's still aspects that you want to investigate on these newer devices that you think is probably still an active area of concern it seems to me like the provisioning one where you know there's a step that you're sending maybe credentials over an open temporary network created by the device that it would be a good opportunity to sniff and get a password to somebody's home network but i i mean i just want to hear what other things you think there may be to look at on these newer devices that you think are at least for now more secure yeah i mean great question right this is basically asking how you can extend this
research um a couple of things right look for pinned certificates look for self signed certificates see if you can break ssl that would be awesome not so much for users but for improving security i should be careful this is being recorded um and then um i think other things include like because there's always new manufacturers coming out right if you saw the market it's it's not like super fragmented but there's every time there's new ones on amazon and best buy pick one and see what you can see all right thank you very much thanks for the talk so you're touching this a bit during the qa process can you be a little bit louder please you
touched on this a bit during the qa process right now and you mentioned that there were a couple of the other ones that you tested yes um but specifically the device that was presented here was that one tested because you had it and so you tested it or that was the worst of the bunch do you still have it operating in your house or did you take that one and shut it down and use something that was more secure i feel like i'm socially engineered here i first have to get on your network so yes so apparently it was given to me by somebody i did not go and buy it and i was like i want to see what's happening
on the network and then i found this and i'm like huh i should research this more it's not on my network anymore if that's what you're asking i think the other guy's social engineered you but in short you tested that one specifically just because you had it it wasn't you didn't target that one or test it okay yeah it was out of curiosity awesome thank you so much thank you thank you for thank you for talking two questions the first one is like from what i could see the bots use a password to authenticate to the service was that your password or do they all use the same one excellent question so i think it's a
combination of well they use the password i provided in for the app but it's not directly that password it's like it's encoded and then it's padded with something so yeah you can figure out what what it is just by looking at that okay yeah the second one is i think i heard seven months you waited why didn't you just go public it was seven months away how did i i think i heard you waited once at one point seven months uh for reply why didn't you just go public sooner like why didn't i give this talk sooner or just write something up on the internet and then giving it so yeah i'm impressed with your patience i guess
what i'm saying yeah so actually so i wanted to be a little bit patient with them being able to fix it i give them more time on purpose i actually wanted a cve right away that was my push as long as they have a cve like my intentions are good right like it's publicly resourced um i think there was no cfps at the time i don't know maybe i should find a conference to talk earlier but i just waited just to make sure that i have my bases covered i get approval from where i work to talk about this there was a lot going on at the back end for me to become comfortable talking about this
now i have all the approvals so i was like sure okay yep thank you thank you one more question because i think this would be kind of funny what do you think about the prospects of putting a bot on a bot a botnet if you figure out how i bought assuming that this is their practice in terms of making these devices yeah how easy is it you think to maybe find an overflow or some other thing inject some some kind of program execute a bot i would be very scared by that by that idea um but i give it a shot oh yeah that would be cool to see all right thank you thank you
so should i just clean on my own or should i buy a irobot what's your advice i it seems like a rigged question i think the general advice is don't buy the most cheapest ones i guess in general because by default the cost is a significant amount of investment that goes into building the board and they may not be invested so much into security right so that's general advice but it doesn't mean that every low-cost bot is not secure right if you buy high-end ones most likely fine generally okay all right no further question thank you [Applause]





