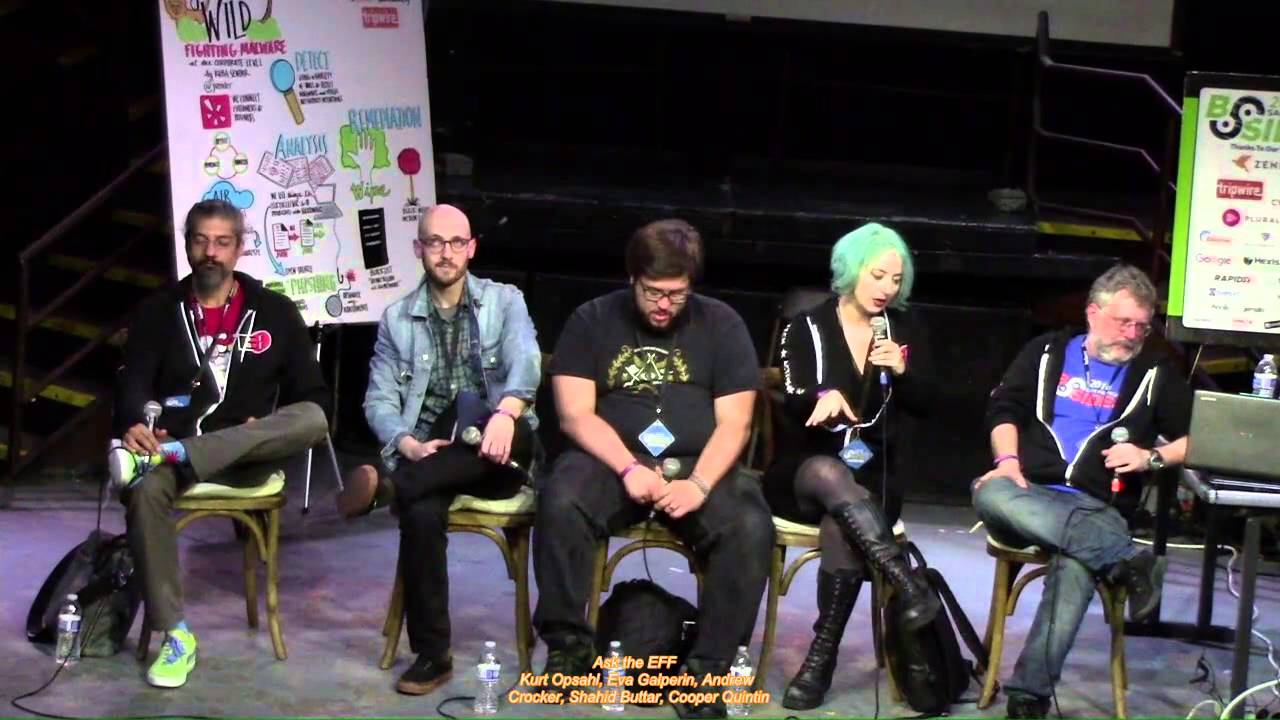
Ask the EFF

Show transcript [en]
all right folks welcome to ask the e FF it is the last session for the day for this room so I'm sure everyone is feeling incredibly fresh and focused and wide-awake yeah raise the roof for the FF by the way so for this talk we won't be using slide o for QA but there will be QA we'll be running a mic around the room yeah that's it take it away Oh hold on yeah David Kenya okay ah there we go uh thank you everybody for coming to ask the e FF my name is Kurt Opsahl I'm the general counsel and deputy executive director at the Electronic Frontier Foundation I assume that many of you came to this and Newt did so because you
knew what FF was but briefly for those who are new we are a nonprofit organization dedicated to defending your rights online we work to defend privacy free expression innovation we try and make a future that you would want to live in and push back against the dystopias that seem to threaten us all so we're gonna very briefly go down the line here so we can introduce our lovely and talented panel and then it's gonna turn it over to your questions we only have 25 minutes so we're going to keep our introductory statements brief to allow time for whatever questions you may have so just a quick word about the questions one of the things we do is
provide legal advice for a lot of people actually in the security community amongst others this is not the time or the place to ask legal questions about your situation you want those things to be in a attorney-client privileged communication we should have those conversations separately and privately this also includes you say well hypothetically if there was somebody not me that probably is you and that's also not not where you want to go so and that actually a good segue one of the things that I do with the FF is the coders rights project where we represent security researchers who have questions about their legal issues that they may face in doing the research and in presenting the research I also work
with Jamie on this project and so if you do have questions about your own situations feel free to reach out to us either after this talk or just by emailing info at EF f dot org and we'll see what we can do to help you understand that situation so with that I'll turn it down to Alexis hello my name is Alexis Hancock I am a staff technologist at the FF I am a lead developer on de HTC everywhere web extension for the Chrome and Firefox browsers we are also packaged within tor if you may or may not know but and also included with brave browser I've been working on this project for a little over a year and a half and I also do a
lot with the security education companion that we have in the SSD companion that we have where we have a lot of tutorials on different technologies and tools but I mainly focus on tour for Linux Windows Mac and now Android and that's about it for me I also do a lot of security research on the side for privacy scanning on consumer devices so a lot goes on there where I try to implement and track things that go on in the background but either way I'll hand it over to my coworker here hi I'm Hayley Tama I'm legislative activist a tff I am on the activism team I focused primarily on state level legislation so if there is a good bill
that we're trying to support or a bad bill that we're trying to stop and you get our emails that's my name on the email hi I'm Jamie Williams and I'm a staff attorney at the Electronic Frontier and obviously I do a lot of work on free speech and civil liberties issues including and also the Computer Fraud and Abuse Act as Kurt said I do work on the quarters Rights team advising security researchers our legal team on the whole does a lot of work in we filed amicus briefs across the country when there's new big issues of tech and law and it's gonna be a groundbreaking decision we tried to file amicus briefs in all those cases we also
have some of our own cases and some of the issues I've been working on recently our compelled decryption also smart cities and I'm testifying on Tuesday for instance on an issue that Haley is working with with cities trying to get access to real-time trip data for scooters and other chute mobility devices it's a range of different issues hi I'm Daly I'm a staff technologist and I work on privacy badger which is a browser extension privacy focus that blocks third-party trackers oh and I also work on like the security education companion and surveillance self-defense guides all right so that gives you a brief overview of some of the things that we're working on which hopefully was enough to inspire some questions do
we have a first question who wants to be bold I see someone in the in the far back also we can't see any of you so speak out basically I'm blinded you'll get that mic on all right all right so yeah I'll repeat the question
great great question so or Peeta for those who might not have heard the the question was about working for a company and wants to make sure the company is doing best practices when it comes to securing the customer data protecting them when the government comes knocking to be sure that you know if a subpoena comes in it's a valid subpoena that if notice can be given to the customer that the notice goes out at how to how to do those best practices and so this is a great question because this is something we care so much about the the FF has been trying to push for these best practices for many years in fact we have
a project called the who has your back project which it's about ten years old and has given out shiny gold stars to companies that adopt some of these best practices for for notification for requiring a warrant before handing over content and so for one part of the question what are the best practices so we we have you can look up there who has your back project we we've done different kinds of things with this project so but maybe two years ago we did one going offer all these practices for ISPs for the like you know facebook twitter x' and telecommunications providers like AT&T what are the practice that they should have and they are the practices
that you spoke of that really give your customers notice so that if they have information that if properly protected from the government they can raise those objections one of the things that he was mentioning in the question was you know you'll get a request and they'll say we have this request we wanna get this customers information and we ask you to please kindly don't tell them about it well as it turns out the government has a process to to go to a court and say give an order saying you can't tell the customer about this information but sometimes they don't don't want to do that they don't want to go prove up to the court why it's necessary why it
meets the legal standard they just rather ask the SBE to please not disclose it but that doesn't have the the force of law and so what I think the best practice there is to say the government say yeah if you think it shouldn't be told to the customer you got to go to a court and prove it up you got to come back with a court order saying this is or we're gonna notify and when we ask for the companies is to notify the customer where they are legally able to do so and if they're not legally able to do so to do it should the gag order eventually expire and that provides people fair notice and the
government has all the opportunities it needs to show to a court why it's not acceptable to give out the information but it needs to make its case and prove what's right so thank you hi I follow you on twitter so I had a question um could you describe the Graham Blumenthal proposal it's not something I've actually seen in the news and what we should be concerned with it is the one Oh looks like a hole in this particular proposal burn it yes okay so so we don't have somebody who's on our federal legislative team Haley works on state but nevertheless I have some familiarity with it because I concur up ssin to something that I do some work on and
this is this is a proposal that as I understand it is sort of the nice section 230 you have there and be shamed for anything happened to it and what it's trying to do is is tie the protections of section 230 which service providers on the internet depend to protect themselves from liability for what the users have done to whether or not they follow best practices and best practices in this context are going to be determined and they're too in all likelihood have a backdoor to encryption like they're there they're beating around the bush but they're not saying explicitly but that is the idea behind this and they have some some reasons why you know well we think this is okay for
example there's gonna be a panel of people who are gonna determine what the best practices are but if they don't determine it correctly then the Attorney General Bill Barr can overrule them and just determine what the best practices are so it's not much of a safeguard and this is this is something that the the government has been trying for for many years probably several decades now in the crypto Wars to try to be able to get access to your unencrypted communications there there was a lull the crypto Wars you could say which crypto Wars part one and the 90s part two now some people say we're in part three but whatever part we're in they
are definitely back and they're interested in getting access to plaintext of communications and they want the companies to figure out a way to do that and the funny thing is that if you if you make a law saying you must put in a backdoor there actually are some reasons why that would be unconstitutional we would put a challenge to that law and I think have a pretty good chance of succeeding if they're saying you simply cannot have strong encryption but instead what trying to do is get around that by saying well you can have strong encryption if you like but if you do so you don't get section 230 and section 230 is the law that says basically that
the soapbox is not liable for what the speaker has said it's come under a fair amount of attack for a variety of reasons these days and so they see this as a threat point for the companies and I would say that it's a lot of is about Facebook's plan to put messenger and encrypted and they're really upset about that I guess I was hearing about the situation but actually what was the specific question you asked about it do you know just getting the details that's that's perfect yeah I just want to start to say first thank you because I used HTTPS Everywhere I use privacy batcher I just let's encrypt so thank you so much because I didn't pay anything for
that by the way I need just call out that it's easy to support you guys there is a booth there and I actually donated so thank you and now to my question because that was important too so I'm actually from Spain so I was wondering if you guys know an equivalent to the uff in Spain or Europe I know we have way stronger laws from privacy but you guys do very important work still will apply there so I'm actually interested in that yeah I don't know what is in Spain in particular in Spain there are several in in Europe that we work with a lot we do a lot of work with European digital rights abbreviated Adri and they
are an umbrella organization which has probably 30 or 40 digital rights organizations that are part of an EFS part of it and so you might want to find one in Spain take a look at the entry site and then look at there member organizations and look for one in Spain we've worked with a lot and other places in Europe and they're like privacy international in the UK like quadrature du net and France bits of freedom in the Netherlands and many and many others but I don't offhand no one's been there is a festival in Spain that happens every year it's not necessary in organization I believe it's Spain based but the Internet freedom festival they
gathered there every year in Spain I believe Valencia so yeah so the e FF normally we have people that show up normally I believe daily plans on attending and a few others from the FF plan on joining so they have that every year in Spain if you're interested in probably getting more people who are interested what you're interested with in privacy and security within that realm definitely I didn't know about that I have a second question oh sorry sorry thank you there's a question way up here you know just give me a second get all my steps in today here we go it was you right yeah you're wearing me down you guys are one of the
organizations i donate to annually I'm very passionate about paying first open source stuff and stuff like what you're doing so can you demystify a bit at least to the extent you're comfortable about your funding sources and why it's so important for I know you have some membership dues things but you also have just regular donators like me so could you talk a little bit about that and how you get your money absolutely glad to so a FF first of all you can get a lot of details just going to our website we publish a annual report that goes over various categories of funding that we have received and you can look at that over the last number of years we also
publish our IRS Form 990 s we are a 501 C 3 non-profit and so this is a tax form that details a lot of the revenues and expenditures so that information is available I would say that like overall we get funding from a couple different sources so one is our members so there's are individuals who join as an annual member and you know it ranges there's student memberships that are at the low end and you can have you know we have tiers that I think it starts out in copper gold we have rare earth is the highest level so a variety of levels depending on your means you get some great swag you could go to the
booth upstairs if you want to join as a member in addition we also have donors who who just donate so either because I don't want to get a membership or some donors who donate above and beyond the the membership level just because they want to have a smart so he's a major donors who are contributing substantially and then we have foundations so we apply for and receive grants from foundations when they have program work that they want to see done that is something that where it's appropriate for us we might apply for that grant and that is probably another substantial chunk of our of our budget we have a couple of things which supplement that one are very all
familiar with the Humble Bundle so the Humble Bundle great great place they have a pay which you could want system and one of the things that they do is in addition to paying for what you want for books or video games or whatever there they're selling you can decide that a certain amount of that goes to a non-profit so sometimes we are on their bundles and we get actually a fair amount of money donated through that we get a fair amount of money from individual donors who have companies they work for who then will do matching to the the donations that we receive and we get some money from from companies directly usually we'll be in the form of
sponsoring an event that's about maybe five percent of our funding and I think that's generally the range of funding sources we haven't got a modest endowment so we get a little bit withdrawn from the endowment every year that also goes into the into the funding we also occasionally get Awards through lawsuits if there's a class action it's called a sigh prey award so if there was a class action and the not everybody like sent their little thing in for their $0.50 or whatever there's a pot of money remaining at the end and sometimes if it's a privacy lawsuit then the the lawyers on each side would get together and sometimes they would pick iff to get
some of the money so we sometimes get decent chunks of money through there and we also like sometimes win our own fees and FOIA cases that we bring will win our own attorneys fees when we bring those cases and those Giz be like they can be pretty substantial depending on how long we've been litigating the case so and then I think we also do Amazon smile donation like that's pretty small but that's that's a that's a tens of thousands of it yeah and all of this is up on our website isn't in the annual report and which i think is a it's a very well done report I used to be a reporter so I'm pretty critical about
those kinds of things and I think ours is pretty well done and I should say too and I think and I haven't looked at it in a while but I think that we're over 50% funded by small donations and thanks to 300 members so thank you everyone who's a Meg here's a member thank you so much whoever donated thank you again and we really appreciate getting the small membership support and that is really it's great to have that kind of grassroots support and also it's very useful in our advocacy when we go speak to like legislators and say you know we have this many members it gives us a little bit more credence when when
making wiser you listen to us every state legislation letter that I send is you know we have over 30,000 members including this many in your States are very helpful it was someone over here yes so we we have a question in the back here and then you said there's someone on the front there there's someone in the on the far side all right I'll need your help waiting when I run back down but here you go okay carry me all right to what degree has tor eroded over time if at all eroded yeah I have any of the computational non triviality elements of tor wrote it anyway to your knowledge especially with endpoints in Western
Europe and the United States oh I don't have any knowledge at the moment of Tor being eroded essentially over time tor has been developed as a network that you know has been hosted and volunteered by many different nodes xing knows entry nodes and I think the entropy between all of them is definitely something to do account for at times and sometimes some sources are reliable and some sources aren't there's been a lot of criticism in the past of the Tor network itself and funding resources and things of that nature but for the most part I haven't heard of anything being eroded in particular is there a particular event you're referring to rumors okay rumors and concerns well right now there
has amazing that comes to light in particular as far as like vulnerability disclosure and I worked particularly with a tor browser so I can only speak for the circuits that go within that as like someone who works with them not necessarily on behalf of the Tor network so I'm not speaking on behalf of them speaking somebody works with them on a daily basis and since HTTPS Everywhere the web extension I work with is packaged within the tor browser normally they have a lot of volunteers people to look over things all the time patch things all the time they have a really vast volunteer network in terms of the reliability of the nose themselves they've been doing a
better job of documentation of how to create entry and exit nodes for the most part and a lot of it I would say if any erosion has occurred there's a lot of websites out there that do blocked or nodes so that has been something that's been more I would say apparent that I've noticed over time especially in the past two years or so a lot of endpoints will block No or exit notes whether or not that's something that's considered a practice that should be put in play from different services especially site reliability services I'm not quite sure what they are told in terms of blocking tour nodes I don't know if they're talking about blocking malicious traffic
they tour often gets labeled as malicious traffic in certain cases so I would say that in that respect I can speak and say that's what I've seen on my end so far I would also add that the tour developers like often say that compromised nodes are in their threat model and tor still works with that in like in in mind all right we have like one minute left let's get at least one more question in here earlier today the you have Twitter accounts made a post regarding facial recognition technology Washington State currently has some facial recognition technology bills in debates and I've given those a review they're not as strong as I would like do
you have comments you'd like to share on on that on other states involved in this and what's going on oh how much time do you have so you're absolutely right so Washington does have they have a couple of bills in the running right now there is a good there is a bill that is sponsored by they silly Washington that we actually think it is fairly strong and that we do like that is a moratorium on government used to face surveillance across the state and until the legislature deems that it would be okay again to restart it so we are a fan of that bill and there is a general sort of they call it a gdpr light bill I would disagree with
that characterization there is a consumer data privacy bill in Washington that includes regulation of face recognition we do not feel that that is a strong bill and I have been working a lot over the past couple of weeks with folks at the ACLU watch a CLU of Washington and other national privacy groups around the country to oppose that bill and it is it is passed the Senate it is in the house committee right now and we are working on comments for that so but yeah I would say in general biometric biometric surveillance moratoria bills are popping up in a lot of places across the country and of course we've seen a lot of work on that
at the municipal level so San Francisco Oakland for example both have ordinances that banned government used to face surveillance in their cities and we are starting to see that bubble up to the state level and but there are also a lot of people who do not want to see moratoria or bands and so you know they're trying to regulate around it but we feel that that is that this is a technology particularly wooden used by the government that is just first of all not ready for prime time it's not accurate enough in a lot of ways and also it is so invasive that we need to really stop the stock use of it and in
our communities and have serious conversations a minute [Music]
interesting um sure yeah are you in law school okay oh maybe you said that um yeah I don't mean the way that I ended up at EF f as I just kind of pursued things I thought were interesting until and I was particularly interested in in privacy issues when I was in law school but but yeah I think like following I think the legislation involving security and encryption I think getting in touch with the with the security research community it's always a good idea just learning the Computer Fraud and Abuse Act and why it's terrible it's a nice idea um no no Kirk do you have any other thoughts well I think about a clerkship yeah you could
do that fellowship yes I did I had I applied for iff for a fellowship and that's how I ended up here and then I became a staff attorney so yeah I think pursuing nonprofit work and if they hit places like the EMF I think the ACLU also does think there's a lot of organizations um on East Coast to to look into to do this kind of work all right there was a woman up there just be very patient
recently the Russian Federation announced that they'd be developing an internal network similar to how the DARPA net is for the US government but a civilian forum does the e FF any if it's the case that they're Russian Federation is successful at this model and other countries look to them as a form of adoption does the FF have any plans to resist like an eventual balkanization of the entire internet into local state forms destroy all privacy as we know it so shall we destroy all privacy as we know it no I know balkanization of the internet I think actually China was really taking the lead there with having a very strong firewall surrounding it and Russia has
I'm not familiar with this DARPA like project but for a while they've had some laws on the books saying that you had to locally host information which is you know the step towards creating that to to try and have it so they could but this actually hasn't been limited to more authoritarian regimes like China and Russia the EU for a while was like should we have our own internet because they were they were more concerned about some of the consumer privacy issues that were arising I mean ultimately the solution to that was the gdpr and trying to regulate the American companies on consumer privacy but was maybe five or six years ago they were still talking
about creating a separate European internet i think these these ideas are generally bad ideas and one of the advantages of the internet is the the free flow of information can be good can be bad on the whole it seems to be for the best and then when particular regions are insisting on having everything in their in their jurisdiction that makes it very tough for the civil liberties of the people inside that juristic and especially in cases where it's a authoritarian regime often where they will you not have to go through any serious legal checks or you know judge to weigh in before gaining information in many cases the government owns the telecommunications infrastructure and if
the material is on their networks then it is really easy to find out who an opposition figure is who is something that's an irritant to the authoritarian regime so we certainly think these are a bad idea I would say like our ability to influence the Russian government is limited so we can tell them it's a bad idea but they may not listen but some of the things that are still useful to do is technology to try ignoring that like the Tor project can help help people sort of disguise where their IP is from and maybe able to get outside of those jurisdictions there are people who do bridges outside of the Chinese firewall so there are some interesting technology
projects to at least provide people with an escape route from a restricted and in places where there is more of a rule of law one thing I thought was interesting that in Turkey there for a while they had a ban on Wikipedia but they didn't like some of the things that Wikipedia was saying and that was that was ruled to be unconstitutional evident from the Turkish law - to block that so that thing to be like a good rule for understanding that things that outside of that local network were valuable resources and blocking access to them was a civil liberties problem but on the negative side in ten places where even having a VPN on your technology on your
and your laptop or your mobile phone can be caused for suspicion even if they don't know that you're using it to access some of these additional resources so it's an ongoing struggle
um curious if you are taking up any act or innocent initially initiating any activity with regard to election security and social media with respect to you know this idea that social media is now essentially may be equivalent to broadcasters like radio and television and should they fall into the nineteen thirty to tell the community Telecommunications Act or if there's any other strategies that you're you know or or ways you're taking up the fight with this regard to disinformation elections community and so on it's being trimmed you know traversing through the social media platforms say a few things yeah so on election security we've looked actually mostly on the security of the the election systems in lecture
infrastructure point of view we've been working with some security researchers who want to be able to do research on the on those systems but I think you're talking about sort of a different sort of thing with the the disinformation aspects of it and so we've done a lot of work on content moderation one of the projects that we and several other civil liberties organizations did was the Santa Clara principles which were principles about how to do content moderation and that is about it all sorts of content moderation including disinformation so it's not targeted specifically about that but as good principles for it thought geology and a lot of times it were we're worried about is over
moderation yeah that the freedom of expression will be overly limited by people's zeal to remove things so we want to ensure that there are appeals processes and ways for people who whose information was taken down inappropriately have a chance to to make their case and say and why shouldn't have been taken down I think there are a lot of things that you can be concerned about with this information how can affect a public discourse I don't believe that we have we don't any current programs at least to to push for having it regulated under as a broadcast medium on our telecommunications system I would say though if you're if you're you know there's a lot that goes with government
led regulation and that involves a lot of trust that the government regulators will be doing a good job at it and on terms of disinformation there's actually like a lot of must-carry kinds of things for political ads where they couldn't on a broadcast medium take something down for having false information and now there's a lot of companies being criticized for choosing not to take coming down for having false information but I think if it was under a under the broadcast standards there are actually less options of choosing what goes up or doesn't go up in political ads one concrete example something we've worked on related to this and this is this is to curt the point about the overreach is
in California last year I think it was last year maybe it was the year before I know that makes me mush together there is a bot labeling go do it 2002 years ago oh my god okay so this was two years ago and it was like a DMCA inspired Botley Boonville we don't like the DMCA if you're familiar with us you probably know that there there's a lot of things that were so in it was it was overreached it would cover any type of bot online and required to be labeled and of course anyone who's a really bad actor wasn't gonna pay attention to this and so we worked with the legislature to try to
and we did actually successfully get them to narrow the bill to the types of I mean what is actually harmful is maybe like BOTS operating at scale to make people appear with people with resources appear that they have way more reach and way more people that agree with them they actually do not just one-off people who like funny BOTS or poetry BOTS or something like that and so for us there were First Amendment implications and we think that if they pass a lot that was as broad as it was when it was initially drafted I was going to create all sorts of First Amendment problem so we worked with the legislature there to get them to narrow
the bill and they ended up passing a bill that went into effect last July I think it's still kind of yet to be seen like how exactly it's going to work out in practice but but that that's one place where and we didn't just completely oppose it we helped them narrow it in a way that we thought would be constitutional so unfortunately we do have work yep sorry about that Hart that hard cutoff but everyone give a great round of applause for the yeah thank you all they this is so good to be here