Stay Safe and Trust No One

Show transcript [en]
hello hi there i'm constantina cuckoo i'm a cyber security expert and i'm currently working in checkpoint software technologies today in besides athens 2022 i want to discuss with you about something that for me it's very interesting it's been around for quite some time i think that you already heard of it's about zero trust model it's a new term everybody is talking about it and maybe has a project on it so i would like to navigate on it uh together so uh before actually start start talking about zero trust model i would like to generally start talking about a little about trust and as a human factor and something that you could trust as a human
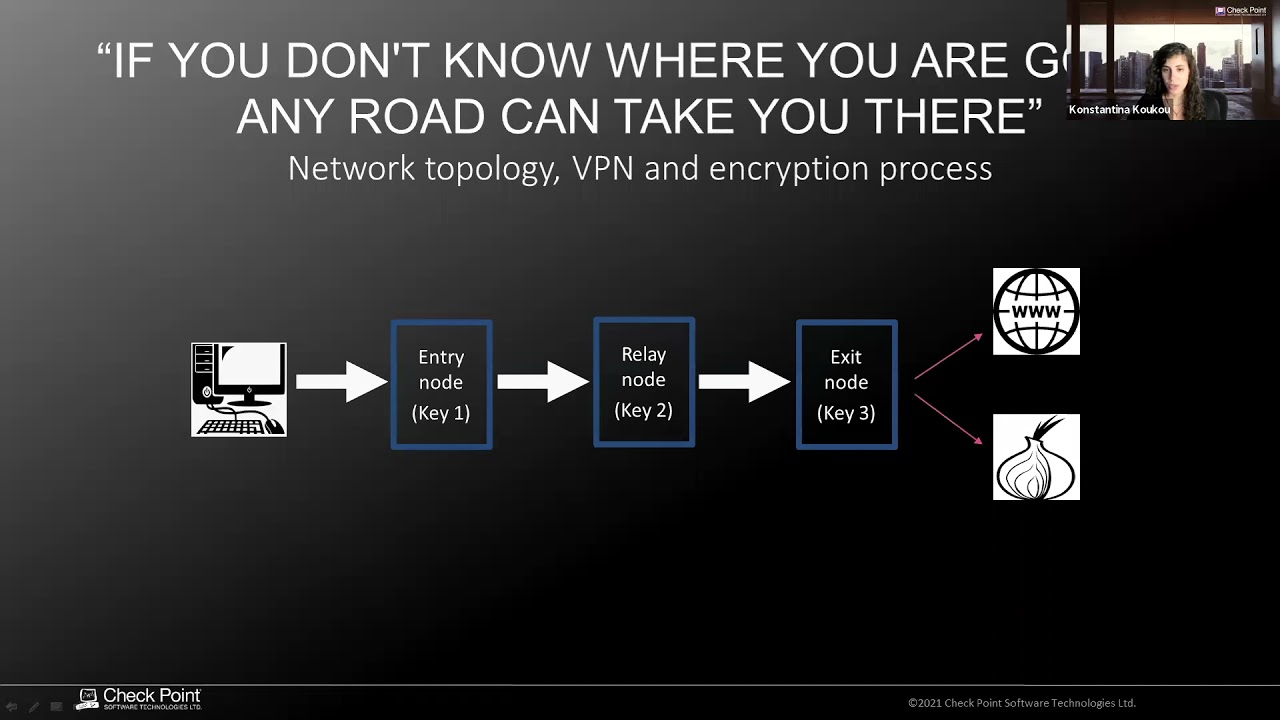
uh personally for me i had i have zero trust in airport sushi i don't know if you have ever tried that it's terrible i would never use a used mattress in my own place i don't believe in competition scam of course as a security person and also i don't have trust in everything that has ip and it's communicating so if traditional access we would say it's about the principle of trust but verify zero trust is rooted around the principle never trust and always verify and on the network level this is a nice picture of what zero thrust would be next i would uh i would like to state that zero trust security is not a product of course as
you may know it's a process there are many best practices there are principles that organizations should observe on the path to zero trust security and to better understand that i would drop an analogy with our physical world in the real world and uh it's not other than uh the airport i think you you you visited quite some times and in doing so i think that we participate in many zero trust experiences and all the the security processes airport security processes are uh consisting a great example of zero trust implementation strategy so to begin with i will start with the basics we are always verifying the person that requests access in the airport the context of the request in a
more generic idea perspective the risk that this request may have and then we are granting access required we require nowadays more than one piece of identification and evidence to authenticate the user and in the case of the airport we use the passport in order to say who to state who we say we are and we are boarding also we are using the boarding pass to board the right place going to the correct destination in many places actually now they are starting using gold to some kind of biometrics for a second factor of authentication and generally authentication could be any combination of of course as you know something you know like a password something you have like a verification
sms and something that you are like a biometric uh users and another principle i think it's very important it's that as we said you will you would never automatically trust anything and in our example this means that we are passing the gate we have zoned uh we have uh uh yes showcased our boarding pass but still you're not quite there you still have so your luggage and this is because even when uh there is nothing wrong with passenger with you of course we have identified you but there is a strict protocol in the airport that yes we have to check what um you may cover in this luggage that you don't even know that people are doing mistakes uh they
sometimes carry the dangerous uh things on the handles without knowing that and the same is uh we would say with the employees in our organization uh there's someone that is really trusted he has passed the door in the morning scan his card came in the office but he's also carrying his laptop we know who he said who he says he is he is also his own but on the other hand we don't know what this device may bring into the organization it could be the mobile the laptop whatever and uh easily it could be carrying uh malware on it uh with the danger of infecting the whole network so principle number three uh for the
zero trust is that uh you have to monitor and audit everything you can protect what you can see that it is known so you have to monitor every activity something that uh usually is checked by security officers to quickly understand and react on something that seems suspicious and this should be of course real time and visibility is especially important for users who have administrative rights due to their serious scope of their access permission the sensitivity of the data that they can reach uh so we need to say also that uh by doing so and by building uh in a security architecture around these principles what it should uh definitely succeed in is that it should have zero false
positives law false positives zero false negatives and it should be usually seamless for uh the user i mean everything we described so far in the airport uh example it was generally speaking quite intuitive for the user it required almost a little experience and awareness of the process and it is very important we always say that that uh for cyber security to be to be consumed it also has to be well understood that uh easily for the user is it for the user and um on the other hand uh of course it should be simple but it should be preventive mean meaning that we should also take uh always take the right decision when there is a suspicious uh incident and it
should be blocked and it should be efficient meaning both for the users as we said but also for the administrators of the infrastructure and it should be complete it should they implement all the principles of zero trust model uh it should increase operational security efficiency overall and uh of course it should be uh protective for uh for the organization against cyber attacks with real-time threat prevention so we're talking about zero trust people uh zero trust people's zero trans passengers in our example zero trust devices luggages syrian trust workloads in this case could be ai belgian zero thrust networks and zero thrust data we're going to go into that a little fast so what we have to do in needs
of this pillar so for zero trust architecture when we are talking about zero trust network of course we have to identify data and assets that are valuable for the organization we should classify the level of sensitivity for its asset we should map all data flows that are happening happening in our organization east west north south everything and northbound and we should also group uh assets with similar functionalities and sensitivity levels into this uh the same microsegment for example all the resources that the r d is using the source code and the ticket management system it would be nice to be in the same microsegment and another thing it uh it would be nice to deploy a segmentation gateway whether
it's physical or virtual in the network and last but not least we should also define a least privileged access policy to each of these assets for example uh the rnd group should access only their own team's source code not the next uh the colleagues that although he's also an engineer he belongs to another group so everyone should access the the things that he's enlisted too so zero trust people uh we're talking about people a lot and they're involved in cyber security and uh the thing is that uh we have of course to authenticate user identities on the network level and not if possible of the application meaning that uh you don't allow authenticating users closer to a security gateway on the
network level that will block hackers uh from getting too close to the system and dramatically minimize the this way the attack service of course you should do and use sso which simplifies the process of authentication uh reassuring how identities with multi-factor authentication is a must and also you should set context aware policies meaning uh narrowing down the definition of authorized connections by adding multiple conditions regarding the context of the connection for example you may think that this resource should be accessed by this partner that connects from greece only nine to five and is something that should be implemented on the network firewood and of course uh we are talking also a lot about that uh detecting
anomalies uh compare connections with the baseline that we have and um for example identify unsuccessful logins unusual times and location more and be able to act on this event zero trans devices also uh when we're talking about that is uh to take a mean a practical approach to minimize the attack surface that comes from the devices uh for all workstations and mobile devices of course no matter no matter if they are corporate or uh also personal it should carry some security controls by the corporation in case it touches corporate data so it should have some kind of protection against the zero day malware around somewhere we should have protection against zero facing and uh all the stuff that we
are currently doing at the endpoint and of course we should block uh corporate uh access to the devices that are infected so positive management and the condition our conditional access should be also a solution of zero thrust devices and of course and the first thing we are talking about segmentation it's always a good idea id iot ot whatever you have in the network it should be segmented on another useful uh on its practical side um when we are talking now about zero trust data we want uh to enforce encryption on the portable media we want to provide secure access for the remote users we want to apply dlp also dlp rules for our users and the classification of the
data that is being used and um a nice tip here is that in order to raise the employees awareness of the data use policies that you have we know that they can be very hard to implement in uh in your organization uh you can release some self-remediation dlp policies that will allow to notify the user for improper data handling that he's making in real time and have the option for him to send this card or review the the issue it's a kind of training uh uh of training technique that it's accommodated in main solution many build the solutions and uh actually now the other part is about uh zero trust workloads and now we are talking about
some application workloads things that are sitting on the private cloud and public cloud and here of course you have to identify all the cloud assets that need to be protected every every all at table point that organization has data needs to be protected with similar protection and with unified policies and uh we should identify everything that is related to the cloud would would have a database server that connects to uh today to the cloud through internet of course it should be also listed and have the the correct way of communication and defined internal segmentation based on list privilege we said that before i think it's very very important visibility and analytics and i think that i'm slowly coming to an end of this
wrap-up of the zero trust model visibility and analytics is very is a key i think in everywhere in order to simplify all these solutions are there they are technical solutions but also we are talking here there is also a framework so we are talking about processes but overall we should have in place some ways to easily check our effective measures to check what we have implemented uh to have our logs and to revisit them in order to daily and in real time of course to understand the anomalies and whenever you can of course you can leverage the credit intelligence services in order to have indicators real-time threat indicators uh that are aggregated in order to share
to have useful information that they sell among all your enforcement points and finally i think that wrapping it up with zero trust is something that uh needs to be discussed it needs to take the right approach see what they control but i think it's more about the mindset about uh how what we can do and all this uh never trust always verify i think it's very important so it's zero trust is here to keep us safe uh the implementations big practical and physical to consume we want to be effective and better security always matters and i think in the future will uh be all an even bigger concern so it's nice that we act practically
so stay safe trust no one i know that this is uh sounding a little strange but this is it when we're talking about cyber attacks uh i have listed here some useful links and maybe you can also uh revisit and that was it thank you very much enjoy the conference bye