Asking Questions and Writing Effectively

Show original YouTube description
Show transcript [en]
[Music]
all right hello uh let's get started so my name is christopher lopez and today we're going to be talking about asking questions and writing effectively so first of all who am i right we always need to have these slides in the beginning of our presentations first and foremost i'm a father that is what's most important to me my second role in life is being a stock analyst i've been a stock analyst now for a few years sometimes i lose count of how long that's been and i consider myself a blue team investigator if i were to say that i had any superpower it is the ability to always keep asking questions and that's what this is all
about our agenda very simple very straightforward uh we're going to talk about investigative questions what that means how to use that to be able to actually draft up some really good write-ups because that is how stock analysts for example um are able to demonstrate their value in their investigations okay tools to be an awesome investigator so it's very simple you don't need that much and we're gonna go over some of these things here uh first and foremost you need your mind right and what i mean with your mind is everything about your mind your questions which we're going to go over a lot here biases perspective experiences how you feel that's all very important to be a good
investigator um also somewhere to take notes uh paper and pencil i still have a notepad on my desk all the time if i need to take a quick note let's say i'm working on an investigation that is interesting or i haven't really seen this before i usually use a pen and paper or paper and pencil just to kind of like walk me through my thought process of course we do a lot of copy pasting right in our roles so text editors really help us with being able to collect notes and i also want us to talk about a loosely defined process and the reason i use the word loosely here is because as you uh put a lot of structure in a process
especially with an investigation i feel like it stifles the creativity of an analyst so just kind of have a process that you walk through in your investigations and lastly team members i would say this is probably more towards the top of importance here uh because when i first started you know as a stock analyst i didn't really understand security very much i came from i.t but very limited in i.t i wasn't like a you know cis admin or anything uh fancy like that i just knew how to like fix certain things and if it wasn't for me being able to lean on team members i wouldn't be where i am now i mean i started out with like
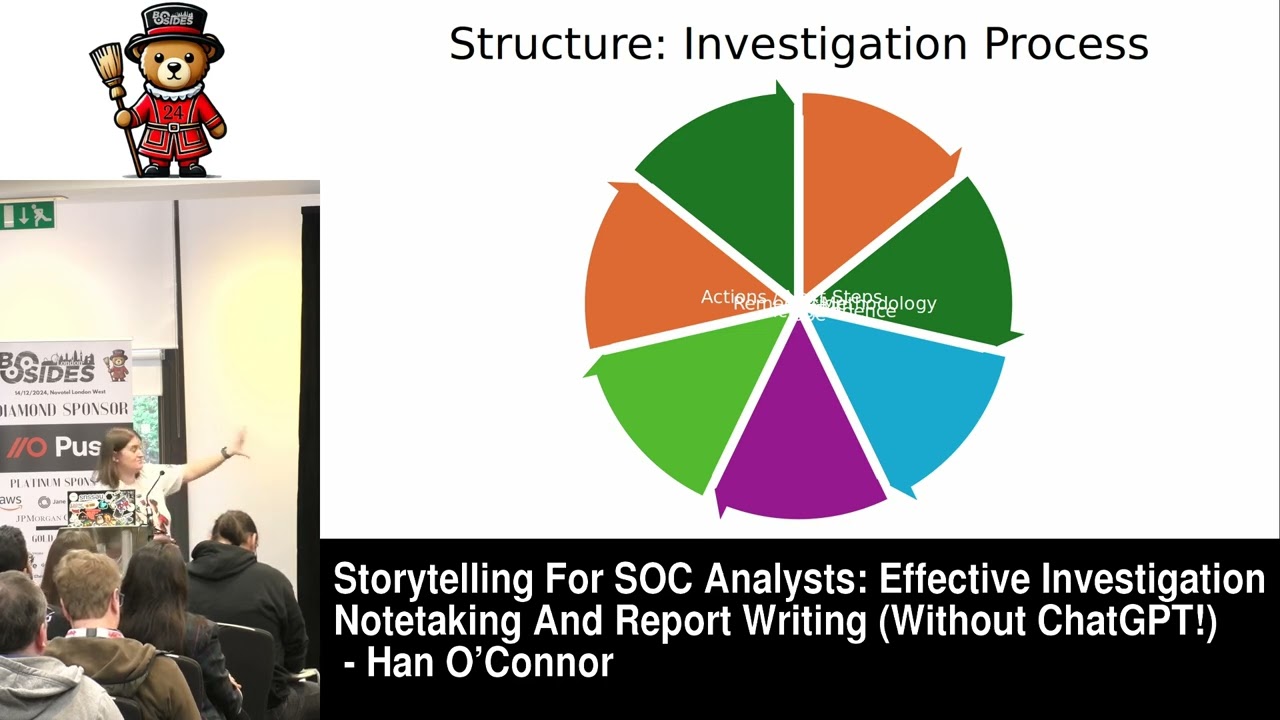
a blank slate of not really knowing how to actually conduct an investigation so very important tool uh at your disposal okay so here is the investigation engine right so this is how investigations work so first you have your questions about what's happening in this investigation with those questions you try to answer them through your artifact collection right you try to get log data you try to understand you know what happened how do i grab something to help me answer this question from this end point for example then we have ragged holes right these are normal uh i always put it in here uh towards the middle because i find myself going down ragged holes trying to
understand something all the time and it's very important to understand when they're occurring and how to climb out of these rabbit holes so of course as you you know collect your artifacts you then compile all of them together and you form a conclusion right so that's what sets us apart from machines right is we're able to grab all this stuff and like think about all of our perspectives and our biases on something and actually form a conclusion that makes the most sense to us and then lastly uh it's very important of course documenting how this all works and what happened when did it happen but this is the engine that we're going to focus on throughout this presentation
so if you notice it looks very similar to something that we've been taught since we were in elementary which is fantastic right so i this is not recreating the wheel this is just changing uh the terminology behind it because it's all basically the same thing right we're making an observation that can be an alert which we're gonna focus more on here as a sock analyst perspective uh we have a question right and we form a hypothesis based on that we experiment i guess in our case it would be we test something or we pull artifacts uh we analyze right we analyze log data and we form a conclusion uh it's the same thing uh just it really
helps me understand that you know we're not going out of our way to recreate anything this is just the way that humanity has you know used a process to answer questions it works okay so these are the questions that we are going to focus on and each one will have like their own section and examples and how this works but uh you know we've seen a lot of these especially you know throughout our lives and as you know again going back to the scientific method this is all not new right so what why when where who and how that's what we're going to focus on throughout this presentation so let's start at the what okay so being a stock analyst i'm going
to come with that perspective and i'm going to focus more on sim detections and alerts but the what is simply the input that's making you even perform an investigation or perform an analysis of something so it's always really important to understand like what the what is as confusing as that may sound right so of course we have the alerts we have threat hunt ideas right you you see something on twitter for example that looks incredibly interesting that the red team is doing and you're a blue teamer like me like i'm gonna look in our environment for that right you have the breach reports we see a lot of those unfortunately but they're really good information for us to
use as an input to analyze our environment and of course one here that happens to all of us all the time usually without warning is a new organizational process an example we're moving this specific thing in our in our environment to the cloud what does that look like well it's time to kind of analyze what that looks like and what changes in your environment and that's going to require some questioning okay so here's something incredibly important and this is something that took me a very long time to understand when i first started investigating always question the alert right so the what being an alert from a sim right so it's looking at potential uh malicious behavior from
an user account right and this is some alert that someone created well before you go down the rabbit hole of trying to understand all this stuff about this alert it's always really important to take a step back and really question if the alert logic is even correct in the first place is it is it able to find what it was intended to find is there any documentation surrounding this detection right so is there someone that created this alert that wrote a wiki somewhere hopefully right that explains what their thought process was around this specific alert because i will tell you that i've had many instances in investigations where i didn't question the alert and i spent
a lot of time trying to answer something that honestly i didn't need to spend my time answering because the alert did not accurately find what it was trying to find so very important when you're thinking about the what in regards to an alert okay so this to me is one of the most important things that an analyst does during investigation you try to answer the why so why did this happen uh why is this here uh why am i looking into this or why did this occur right um this drives your investigation what i still do i write it down let's say i'm using a ticketing system right for an alert i'll probably make that one of my first notes i think that
this happened because of this i believe this is a false positive or i believe this warrants more of an investigation because this thought um and of course as you ask these why questions and you form your hypothesis you're just trying to ask questions to find the answers to make you know to make your hypothesis make sense or prove it wrong right that's always fun so an example examples of these right uh this detective file does not appear malicious let's say that it's a av detection for example um and it looks like something you've seen in the environment before and it may be like a heuristic type uh alert where you notice that it may be
something that your environment is testing well you know you can form the hypothesis this does not appear malicious in nature and of course you get another uh alert which is about a fishing email but it doesn't really look like fishing you know that gut feeling you get which is really important well that's your hypothesis and you drive your analysis and your artifact collection around that okay so leslie at a recent uh wild west hacking fest she said it a lot better than i could have um and i'm really happy she provided these three very easy things to consider when you're building your hypothesis right so is it falsifiable is it testable and what is the scope i
think that this is incredibly important to consider when you're building your hypothesis you want to be able to test it you want to make sure that your hypothesis you know is within scope of your analysis you don't want to you know basically start thinking about something else that may not have to do with this specific investigation so really important here when you're building this out so here goes an example we talked about av a little bit um that's something that many of us in socks we see right uh antivirus detects something so an example alert you know june 5th 2020 uh av detected a potentially malicious file in a user based directory and my hypothesis file did not execute
right so av may have been able to uh you know quarantine or capture this file right we're not even asking why this file is there yet we're just forming a hypothesis a little bit and then we're going to try to test against that right so i believe that the file did not execute so i'm going to pull artifacts and pull data to prove myself wrong right i'm gonna look for evidence that it did execute i'm gonna look for evidence that it was able to bypass av even though av was able to detect it doesn't mean it was able to action it properly so that's kind of how this stuff works with the what and the why when okay
so the reason i put this right after those two that are incredibly important is because time stamps have burned me in the past understanding when something occurred is really important and i'll tell you a little bit of a story here so i was trying to investigate suspicious activity on a machine and you know i was looking in the sim data which is set to my time zone and i started i was able to connect to the machine and i was able to pull log data from the machine but what i didn't consider was that this machine was actually in asia right so completely different time and of course i'm looking in the log data that i for some reason didn't have
in the sim i'm looking for specific things and i'm looking in the completely wrong time zone i'm looking uh i was hours off and i had to revisit the investigation after i took a little break because i couldn't find what i was looking for and that's when i realized that i spent the last two hours looking in the wrong location so it's really important to understand when something occurred when did this alert occur what is the difference between my sim and the logs within the sim and what's the difference between when i pull artifacts from that machine and what time zone that's set to or the time stamps of when something occurred another thing to think about with this
is as you're you know putting down notes and writing things up i think it's really important to put timestamps of when things actually occurred let's say it's a file based detection well it occurred at this specific time or it attempted to execute at this specific time those whens are very important as you start to formulate your write-out of course we gotta we gotta put utc here uh set everything to utc if you can uh it makes everything a lot easier uh with converting and it's just something you'll get used to over time but at least you'll know that everything is on the same thing right so that's really helpful so you don't do what i did and spend
two hours unnecessarily looking at the wrong place where so where is interesting right so i just gave an example about asia and that is answering the where um so this one this question can be answered with when right so that's something to consider so you might you know not two bursts of one stone and these types of questions but this also brings up certain things that are important which is like asset location and asset management is this a server that's sitting in a data center somewhere is this someone's laptop um you know where is this user if it's a laptop like where are they located did they recently get on a plane and go somewhere else like how does that affect
um where like what happened here so really important to consider sometimes can be answered with the wind which is really great okay so who we spoke a little bit about a user so there's something really important to think about when it comes to a user right uh something that took me a long time to understand and that is there's a level of abstraction when it comes to a user account just keep that in mind just because you know you see a specific christopher.lopez user account performing some action it does not necessarily mean that that's me actually doing that um so there's a level of abstraction just something to keep in mind and this kind of leans more
towards attribution like who did what right who's in charge of this or who did that um and if you're looking at more um malicious behavior malicious file stuff this is where you can inject some threat intelligence into your investigations which is really powerful as you're trying to build out your investigation understand more of like the behavioral side of the behavior that you're trying to look for right and of course this also tries to answer the questions of is this an insider an outsider you know how would i know that um how do i prove that and that can help you with your artifact collection and of course you know employees is this a vendor is this some contractor
that we lend a machine to that you know was able to get access to something and did something malicious or potentially malicious right this is a co-worker which is always really difficult but sometimes it's really important to understand that it's really important when you're looking at the who to really think about what this user account really means and how to understand the investigation based on that lens how how is powerful uh i spend more most of my time in the how right so back to the av thing because it happens a lot how did this get here i think that's almost more important than did something execute right so the reason i say that is because
yeah so this uh file was captured by av for example um so the thread is gone right well technically uh it did something right it may have stopped something but why is that there in the first place how did it get there right um and this is usually where the rabbit holes uh come from with the how right you want to understand how this works right if it's a new type of technique or tactic like how does this work and how do i find more of this right and also something to really keep in mind is you know as a saw right an effective sock we're always trying to build better detection capabilities right or
response capabilities we're trying to always make our rules better right so how did we detect this it's really important was this just someone that sent us an email you know which is really awesome when our user base can send us something and say hey this looks a little bit strange take a look at this um or did we actually have a rule that alerted this to us right or alerted us to this specific activity it's really important to understand as you're building out this analysis and of course if you're looking at this through the lens of a tiered based sock you know function how impactful is this do i need to escalate this have i gotten to this
point now where this looks much more malicious than i originally anticipated or my hypothesis has proved this uh to be really bad and i need to like basically let somebody know about you know the the uh severity of this specific thing that's how you answer this right how impactful is this okay so you have all of these things put together right hopefully you've taken notes sometimes i forget to it's okay all right hopefully you have something in your mind and now you need to put it all together uh it's really important to understand and this is something that took me a long time to understand when i first started writing things up i didn't really get how important these write-ups
are right so this is what your management sees this is what your leadership sees right they don't see all the rabbit holes that you may go down right unless you you know do what i do sometimes and copy paste some interesting things that you learned and put it in a chat somewhere but what they really see is what actions did you take what happened here um what answers did you obtain was this escalated did it need to be escalated right and what is your conclusion like what what did you determine from the artifacts that you collected is this bad right is this a false positive do they need to do something because of this right
and you need to be able to equip your leadership to be able to make those difficult decisions right so we're here to provide the facts right that's what our job is and it's something that i had to learn very early on because i like to write a lot i like to talk a lot and uh sometimes i like to really communicate something really interesting technically right and what i what i failed to understand was not everyone has the time to sit there and read a very long write-up right and if you do create a write-up you need to understand that you should include something like a bluff a bottom line up front let them know whomever it is that's
reading this documentation or this report that you wrote like why am i reading this right and something that's really important here is to provide contextual data right so this happened at this point it includes this machine and i explicitly write what this machine is a server laptop whatever and it it had this user account associated to it and here is the osun information right the open source intelligence that i obtained uh regarding this specific file and here's what it means right that's really important so that you know if they have questions you know they can look in their write up the write-up that you created and really try to answer those questions by themselves like they have everything
that they need in that write-up okay so i mentioned this and this is really important and there's a whole slide for this because this is something that i had to learn the hard way bottom line up front people are busy uh people are making decisions left and right they need to understand very clearly um what it is that you're why do they need to read this right so summarize your key information really quickly what did you determine uh what was involved in this why does this matter why do we care right um and it's usually the first paragraph right so right after the hey how are you here goes you know this investigation make it really stand out make it so that
that's where their eyes go to first and something to keep in mind the three z's uh make it concise make it clear and make it correct right really fact check yourself when you make a determination on something have the evidence to back up that determination right or you know sometimes this happen based on our investigation based on the data we have we we're it's inconclusive that's okay too but back that up like really try to be as correct clear and concise as you can be when you're writing this up okay so just one last thing here about the importance your write-ups can invoke change in a process right so that's something we do right so let's say that uh there's this new uh
phishing campaign and we have a certain way of handling that with our users and we found that it's ineffective right write your you know write up with that expectation that it could be used to change a process it's really important so put the put the effort into the writer can someone replicate the actions you took now this is really important especially when it comes to like a tier based sock um can your lead replicate your actions is it clear what you were thinking and what you did to pull these artifacts and what they mean to the investigation right so another thing that's a really good thing and i love this in write-ups is can this lead to a potential improvement
in your detection capabilities did we learn something from this investigation that we can use to find more bad or did we tune this potential false positive out and why and how that helps our efficiency when we're trying to you know deal with the alerts that we deal with another thing is can your senior leadership just forward this on right do they really need to go in there and modify your words and everything that you said or is this good the way that it is so that they can use this write-up to address any concerns or make any decisions right so we're trying to equip our leadership with the facts so that they can make those
decisions that are you know important to the organization can they just use this writer it's really important another thing i love documentation um i spent a lot of time on documentation did you document your findings right this is another question to ask yourself in a wiki or something something that uh your team members can look at something that you can go back and and re-read how it is that you wrote it because we keep you know evolving our writing style is there somewhere that this is stored so you can always reference it okay so uh questions summary an investigation uh really think about what questions you're asking yourself build an effective hypothesis this is what drives your investigation
this is how you're able to collect artifacts and try to prove yourself wrong that's always fun so answers to your questions as you're writing them down form the foundation of your write-up this is how your write-up grows this is the foundation of your writer an analyst reflects their efforts through the house this is where your leadership actually is able to see the value and all the work that you put in it's really important to write it up with that expectation people are busy always include a bluff statement don't do what i did and just send someone like a five page technical report without providing some kind of hey here's what happened here's why this is
important very very important uh you don't wanna be that person all the time keep asking questions that's the most important thing here we're always trying to learn something we're all here to learn something right we're all here to teach each other to keep asking those questions and you'll have everything that you need to be an awesome investigator here goes some resources um you know i think that these are really critical as we learn how to be better investigators uh chris sanders investigation theory course one of my favorite um there's some writing tips here from lenny amazing something that i've used in order to try to write more effectively um you know sans has some things here
for generating hypothesis threat hunting really awesome the book thinking fast and slow that's something that i recommend everyone read just to understand biases and perspectives really powerful and of course this book on intelligence which is all about writing and how to write better and you know how to create a bluff which is really important all right well thank you so much i hope that you know we've all learned something together here and i look forward to seeing everyone be an awesome investigator thank you
you