Simon Cole - Let It BlEeed (You Can't Always Get What You Want)
Show transcript [en]
hi i'm simon welcome to besides liverpool the views expressed in this talk are not the views of my current employer or previous employers what they are are a sort of series of things that i've learned in a fairly long idea career and things that people have shared with me generously and and i'm now sort of passing that on and what we're talking about really is is how to get security implemented how to be effective how to get stuff done um so let's begin just a bit of context and this is applicable really everywhere yeah even at home uh i've got a big list of jobs that i should be doing when i'm doing other things
um but in a work environment you know this this is really true um yeah when i was doing data warehousing when i was doing building ecommerce systems we had more stuff that we needed to deliver we never had the time or all the people we wanted and and budgets were tight and from security this is really important to sort of understand because it actually applies to security projects but more importantly for a lot of projects what we require is other people to implement the controls we want or to build the solutions we want or to change the way they works so that we've got the correct security so to get that we need security agreed
and we need to agree that it's important we need to have it prioritized and we need to get it implemented because if you've got controls aren't implemented they're not really controls so yeah who makes those decisions how do we get this done is really what the basis of what i'm going to talk about for the next 15 to 20 minutes so who makes that call yeah and to be effective and to make sure you've got that buy-in you really need all of the people on the screens to to be bought into to a level um that's appropriate you know i've worked on teams where we've got engineers who are really enthusiastic but actually if the product owner isn't
bought in then it's you know this stuff doesn't get prioritized if the exec sponsor's questioning why we're doing the security stuff but the product owners brought in once again it's that friction and all these people really really want to do the right thing but they've got delivery pressures the same as i've got delivery pressures probably everybody else has delivery pressures if you don't have those delivery pressures well lucky you um it's not a place i've ever worked in so so yeah that's yeah you probably have other problems that you need to solve but but these this is what i'm really focusing on so how do we get that sort of security agreed aligned you know
so the first really important thing is is understanding your company because sometimes you talk to security people and i work for security and it doesn't matter what industry i work for but if you're trying to influence people who actually it does matter yeah that's really not going to help where you're seen as a sort of outsider so if you bought into your company and if you work for a telecoms company in telecoms you understand how to what telecoms is doing how you make money how you what the business goals are you can start to build a business case um around what you want to do and that really can resin start to resonate and one of the key things is what language
you use and each you know groups of people use language in a certain way you know you're one of the group you're one of the tribe if you use this sort of language now if you're trying to get people outside of security to to support you and help you you need to use the language they use rather than expect them to use your language so i've worked in companies where we didn't have users we would have colleagues we didn't have customers we had clients now by using those words appropriately you sort of show that you're part of the group and it's all around you know building those relationships getting that empathy you know because that will help you going forward
also you know what else is happening in the wider environment and i'm not just talking company the industry you know cyber was a huge example which to be honest i had to learn the hard way um 15 years ago cyber came out as this huge buzzword everything was cyber yeah even your toaster was cyber i hated it to me from a logical perspective it was a william gibson word that meant nothing it was just rubbish but one of the bosses took me aside and said yep that might be your view but when i phone the cfos pa and say i need to speak to the cfo about information security i might get to speak to him in two weeks to a
month's time for 15 minutes and i'll get potentially bumped a couple of times if i phone up and say i want to talk about cyber i'll probably get a meeting within two days so by using that wider sort of language environment what's happening that that sort of yeah that was a real eye-opener for me currently zero trust you know who definitely knows what zero trust is and if you do talk to the person next to you because i bet you they definitely know it's something slightly different but what does it mean for you what does it mean for what you're trying to deliver how can you use that phrase that terminology that other people are using
around around your company the wider yeah the wider sort of ecosystem to to get what you need done yeah and plans strategies roadmaps are really important but sometimes things come along that knock that out so you know nobody expected kovid really a few might have done but what we definitely didn't expect was 18 months working from home now how many people have refreshed their vpn infrastructure i would expect lots but while that's happening can you include posture checking can you include linking into mfa are there other things that you can put in place off the back of this change that's already happening to to deliver the security that your company needs um for it to be successful
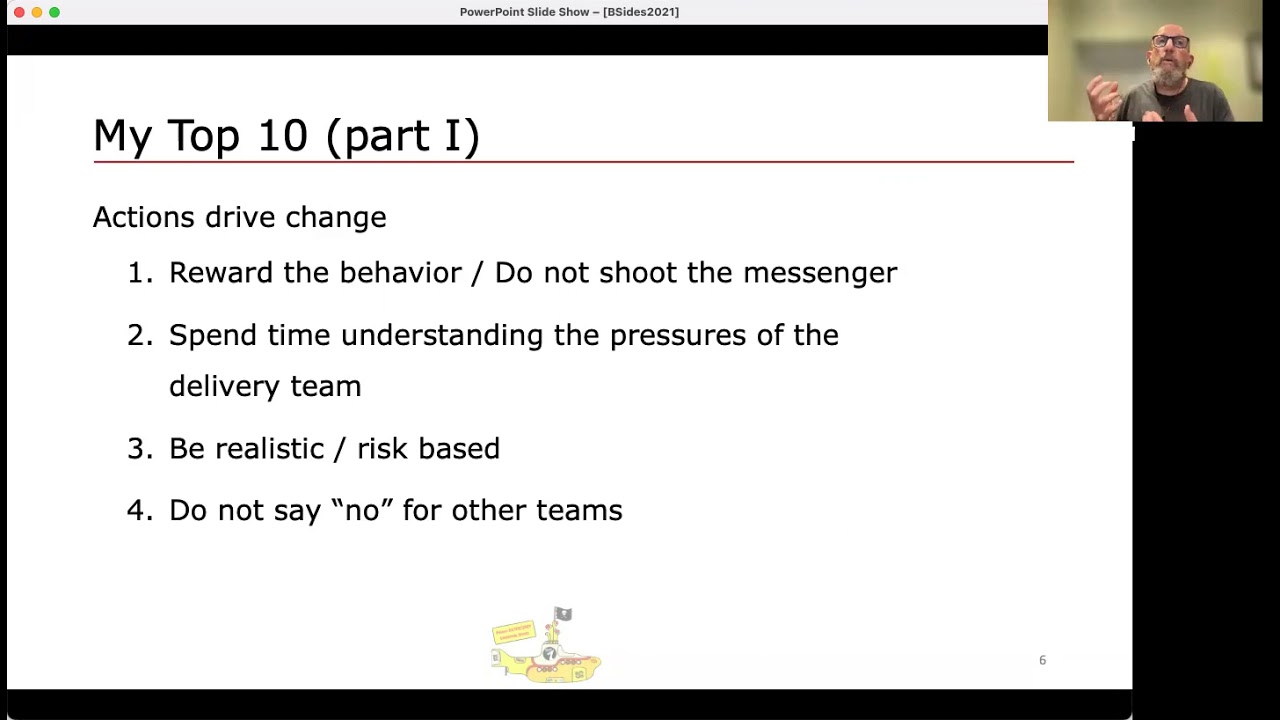
so these are sort of sort of some sort of wider areas the next part couple of few slides are much more around things you can personally do because i actually like things that are actionable and and actions are really important because if you um whatever you say people will take to a certain point if you don't back it up with actions it will just become hollow and the actions that you do really drive the behaviors that you will see and also the behavior the sort of team the culture you want to drive and the first one's probably the most important you know ideally what i want is someone to walk up to me and go
we did something we didn't really understand what we're doing i think we've got a problem and at that point you've got two things you can do you can go firstly thank you for telling me because that person probably doesn't want to admit they're making yeah they've done something wrong and then okay let's sit down let's talk it through let's see what's happening rather than going oh dear and well words that are slightly more robust than agricultural um and really getting angry about because one one way of doing it means somebody will come back again the other means they're never going to come to you with a problem um even better after that event if you
can use company reward system some companies have these things where yeah every month an employee gets a bottle of wine if they get that bottle of wine for bringing the problem to you that's a very visible way of saying we're open we're here to help you know sitting down and understanding the problem and why it happened sort of isn't number two which is you know how do you yeah if you've never worked in a delivery team how do you understand the pressures they're under you know i don't know how many people here have worked on the delivery team i've worked on grad schemes where you've had security grads one of the things i've always recommended is for one of
their six-month rotations they go out and work with a proper application delivery team delivering products for customers colleagues clients yeah because then you understand that and if you do a swap and you get one of their grads into security you have a brilliant thing where when that person goes back that grads like a little beacon of security understanding that that's really really useful um ultimately you know everybody's trying to deliver stuff you've got to be realistic or you should be realistic and look at the real risk yo when someone comes up and says we're using tls version 1.1 is that yeah the world's not going to end um it's not great but i can live
with that for a while so let's take a risk-based approach let's see when they can fit it in and if your standard says it should be within four weeks and they can't do it for six once again what what's the issue there the final one here security yeah we've got a reputation for saying no and and to be fair quite regularly we do say no you know but a lot of other teams are much happier for securities to say no than for them to say no and i really push back i had a great example where a team had built this really lightweight solution for one specific pro problem they were trying to solve and they
talked to us it was they didn't have the budget for the enterprise solution but because the enterprise solution was big it was they didn't have the money so they built their own but they talked to security and they had the right security controls and features it was you know it was fit for purpose from a security perspective enterprise architects did not like it and understandably because if you're an enterprise architect you want one solution the enterprise architects told me that i had to tell them to say you can't use it and the answer is no you're the enterprise architects you go and tell them because from a security perspective it's fine and that there are a number of examples
where people like security you know don't like to tell people no and then much rather security did it and the answer is from me no i'm not telling i'm not i'm not being the bearer of all bad news
the next one was really driven home in an interview i did a while back where um one of the interview guys said engineering teams don't read standards standards aren't what they're into they want to write code you know they want things that make their life easier if you give them a reference architecture that shows you the components the patterns you know potentially the pseudo code and if you've got some shared services even better that's what they want they want to be able to produce the code to write you know deliver the solutions they need to do and our job as securities to make that easy to consume you know are you using the right format you know
does everybody communicate on slack and you send emails because if you do you you're going to miss your target your audience and as much as security is everybody's responsibility sometimes if you they've not read the email because they're on slack all day that's just not going to happen the other thing is looking at how you deliver yeah does everybody you know is security still doing waterfalls and everybody else is on two-week sprints because if you are really you need to change you're not going to get the whole of the company to change to align with the way security wants to deliver and once again this is all about making it consumable making it easy every organization i've worked in
they've been teams that like security to be honest that's how i got into security i was doing e-commerce development i like the security side of it and that got me in my foothold in security where you've got guys that are doing security and they're doing it well there's two things one cut them some slack sometimes because actually if they can't you know if they can't do what they need to do they need a little longer to produce a document they need some more time to deliver this final control really in the grand scheme of things if they're doing the if they're your best examples of security you know be flexible be pragmatic let them do it the other thing though is the
one that really used to annoy me was when the security team needed you know evidence of controls being put in or new control's been put in coming into my team and going you need to do all of these things it's like hold on a second we've got no notice we've talked about backlogs it's too big haven't got much time but also the team over there you're not talking to they don't even do half the stuff we do and now you're expecting us to do more so so although it's sometimes really you know you have to show that you you know you're delivering stuff and it can be very tempting to go to a team that's
already doing security and ask them to do more it's actually long-term counterproductive because if they always feel that they're getting pressured to do more than everybody else that will slowly build resentment finally on this slide is you know what's optional tls 1.3 it would be brilliant if you could do that actually tl ssl v3 that's not optional tls 1.2 is okay tls 1.1 we need to go down the exception route what's that exception and explaining to people that there's an exception route and there's a process that allows yeah risk-based decisions where we can all agree about what's what's acceptable what's not acceptable and that may the decision is made by somebody who is appropriately sort of informed
and and responsible for making that decision allows that sort of visibility of the end-to-end process you know saying you have to do this and that's all it is really doesn't help in the long term so my final two is actually one thing threat modelling i i'm a bit of a threat modelling geek i think it's fantastic um i'm not necessarily talking about tooling the tooling so much better but actually as a process as a um something to to to deliver um into into the um engineering teams into all aspects of delivery this is brilliant and back to the previous slide yeah if you built those good relationships with teams getting this people to start doing this
you know is a lot easier um and it's brilliant it the difference this makes in terms of engagement and ownership is just fantastic the best example i've seen is where a colleague was threat modelling with a team they found some stuff not not critical yeah but stuff that wasn't right um the team they broke for lunch they came back a couple of the engineers were late when they arrived back the question was where you've been said well that thing that you found um we've just gone um and fixed that it's going into test tomorrow it will be released early next week now that level of engagement um i've never seen from a pen test because really if you think about it
you know a threat model and a pen test are the same thing you're just slightly different i suppose but you know one at the beginning of the process one at the end of the process you still get a list of things to fix but that engagement from threat modeling you know is just fantastic and i think the other thing about threat modelling is security can get really excited by it and sort of swarm over it and take it over but the critical thing is if you want it to be sustainable is to get people to do it themselves so that they can do it as part of a stand-up they can do it in their planning sessions they can do it
in new feature development um with security facilitating training and providing more um and like i said threat modeling is just just great there's so many different you know it's growing so much um as you can tell i can talk about this for quite a while um but you know it doesn't matter which one you choose just getting people into that into the processes thinking that mindset is just fantastic so here's the final slide um and i think you know what we've been talking about is i think captured here is is you know effective security has to be implemented there's no point having having that waff and never turning it on uh it might take a compliance box but that's not what i'm
about relationship matter probably far more than you you probably think at times because they they can really turn things around and when you need things done in a positive way and actually when you need someone to really help you out if you've built that if you've done that build those relationships they'll help you yeah think about this as security is customer focused you know what do your customers want what do they need yeah if you think about would they come to you in your organization if they didn't have to uh finally get threat modelling it's just brilliant fun um and it's just great the original call for papers asked this you know uh asked for presentations to
be linked to uh lyrics preferably the beatles i couldn't do the beatles uh what it did get to was the rolling stones and actually i thought this was fantastic when i looked at it you know because of what we're talking about is delivering what we need and as it says if you try sometimes you find you get what you need so thank you for your time um i hope you found it enjoyable if anybody wants to have a chat about any of this just look me up and enjoy the rest of the conference