Keynote Presentation
Show transcript [en]
but without further ado I wanted to talk quickly about b-sides in its history so b-sides started out as one conference that was made because you know not a lot of people got a chance to speak and basically it built out into a community and now we have b-sides Charleston we have besides Charlotte we have besides Augusta and a lot of that is due to our next speaker who we have the honor to bring up the man the beard and the legend Jack Daniel so thanks yeah let's let's do this presentation thing skip this part of it so yeah four acts don't worry three of them are fast I don't want to talk about a few things
but first it's early so let me mess with your head a little bit [Music]
[Music]
[Music] [Applause] [Music] so you didn't expect to hear the phrase shredding on a kekkai him this morning but that's what he was doing there and I don't let you expect today but if you open yourself up you're gonna meet some really amazing people learn some stuff have good conversations it'll be awesome so thanks welcome to security be sides
but as TJ mentioned you're not just here that these sides is a global community and you're part of this you're actually part of all of this you're part of all of this in July of 2009 a handful of us got together and kind of gave a place for folks to give interesting talks that maybe wouldn't fill a room in Def Con or blackhat maybe talks that weren't quite ready for primetime maybe ideas like diversity and InfoSec the first couple of big b-sides we had those panels it took five years for RSA to address that and eight years for blackhat to address diversity in our industry and in our but we're part of this there are four security besides
events today Delaware Boise Lisbon was yesterday here and I'm blanking on one oh uh yeah one more [Music] there have been 373 security besides events since we started in July of Oh 916 cities in 33 countries around the world and it happens because local organizers make it happen that happens because it's about the local community building community creating conversations forgive me for being idealistic making the world a better place and with that I'd like to talk about the security besides founders we're a growing global community and if you've ever you know add an addition to your house or something like that you have to put a foundation under it to support it and so unlike some organizations I like
to think of our founders circle as being every single person who's ever been involved so that means if this is your first event ever I want to welcome you to the founders circle because you're part of the foundation of an amazing movement so sheer I like to remind people that your participants not attendees so since anyone's first besides event haha this is cool anybody's first like Acura security con at all cool let me do this I'm gonna and whether or not it's your first time meet somebody say hello we have some challenges in the industry that we can't fix alone boring that I'm not going to dwell on this I've done a series of presentations on stress and
burnout and survival skills but I will say this this time of year people start to get bleak I mean the horrors of 38 degree weather having spent 40 years in New England the Sun went away that's what do you mean it's dark now and it's end of year and all the pressure is take care of yourselves and take care of others I'm not gonna dwell on it but really and now the keynote a part of the keynote so I've been doing this for a while but not as long as most people think because I'm old and you make assumptions about me [Music] and you're right about the old part but together we have a lot and that's that's
a recurring theme there too two topics on a highly complex timeline we're going to work through here discussing the past present and future of InfoSec and the timeline can be a little overwhelming but you know stick with me and hopefully it'll make sense by the time we get to the end here here we go
you know at one point in time we had really simple systems single user single process we could secure them we didn't they were horribly insecure but if you wanted to know who was using the computer you looked at the console and then as it advanced if you wanted to know who was using the computer you pulled the wire and traced it to the end and whoever was at the other end was who was using it and then we started actually making progress I mean this is even before my time you know early secure operating systems like BBM's 10x we're interesting because it was designed to be secure you really into the history of it it's kind of funny to
see the dumb dumb basic security mistakes they made with it but then things started getting more complex multi-user multi process we were getting better at security but we are also making them more complex which makes everything more interesting I have a reputation for being pretty pretty cynical and it's well deserved it's one of the challenges would burn out in our industry is that you have to be skeptical to be pretty good at this I think and it's easy to cross the line but there are some people that would propose rather than any sort of progression we're just in this hopeless hamster wheel of pain and there's some truth to it but first let's let's look
back a little bit and hopefully you'll see the as far forward as we've come we've also not left a lot of things behind and one of the things that I like to do is adjust the screen before I start giving a talk so I don't look like an idiot as I'm sitting here and that's one of things I like to do I don't always do it though we'll fix that and how us so no matter when you joined the industry or even if you're trying to get in you're still in school whatever as soon as you land all you can do is run to try to keep up we have a dynamic and fast-paced industry and we're tangential
to the tech field in general which is out of Perle insane and all you can do is try to keep up that means we rarely have a chance to stop and look back and say how did we get here why do we do this who is it that got us here you know it and things were different you know in the earlier days there was no security industry security might have been something you did with me worked in technology unless you were OSS during World War two or NSA or GCHQ or whatever you you know security wasn't your job it was just part of what you did and another thing is a lot of the early
stuff is not readily available on Google and for most of us even me I forget that things existed before Google it's like wait there aren't a lot of Bob Abbott's papers that are available on Google without a lot of digging and knowing exactly what they are so with that come on you can do it I want to share a few people and a few ideas give you some ideas this one let's see who tears up on this one we lost Becky earlier this year a truly amazing person if you think about the people like Marcus Ranum Ron gula Rob Graham people that were leaders in the early intrusion detection network behavior analysis fields basically the network
security part of our industry which is a huge foundation of it Becky was a mentor to every single one of them when she was at NSA yeah there's baggage with NSA believe me I'll never get a clearance let's just leave it bad Becky mentored a ton of people she was known as the den mother of intrusion detection she caught me through mutual friend referring to her is that a couple of years ago and she explained she wanted to be known as the cranky broad we lost her at the beginning of this year and a lot of us are still reeling from it anyway she did her time at NSA before 9/11 before they became what they are now politicize just
a little bit then she went into consulting and the thing is she's from South Alabama and when she moved north to get a government job and marry a damn Yankee her father said when you're done with that make sure you come home because we need some help so at the end of her life she spent the last few years of her life at the University of South Alabama setting up the cybersecurity program and making good on a promise to dead most amazing hugs info mom to many many people and we lost her and it kills us most amazing hugs in the world anyway Becky is somebody that any of us in the industry has touched directly or
indirectly you may not know it but somebody like Ron gula or somebody like Rob Graham or Marcus Ranum owes something probably a lot to her so I like to let's go back in time a little bit let's talk about hackers arguably the first electronic or electric hacker Nobel masculine inventor of the pay toilet stage magician he also did a man-in-the-middle attack on Marconi's wireless systems and put ahead of the message that was supposed to be on the wire or on the wireless an obscene Limerick about Marconi himself the guy in receiving that and reading it was reading it aloud before he realized that he was saying naughty things about Marconi that was 1903 did a
wireless man-in-the-middle attack and it was two people that were possibly going to be investors so if you think man-in-the-middle is something new or irrelevant or I wouldn't call it espionage but economic sabotage is something new in her industry this dapper gentleman an was way ahead of us people we all know Alan Turing okay Alan Torrie look you everybody I assume most of you know into the computer well sort of but maybe Ada Lovelace somebody that most people don't know is doc team he was an engineer the ideas that during had weren't something you could actually build it took an engineer to take the ideas from this mad genius and turn them into something that somebody could
assemble and then he supervised dit and you know what it took it took people who knew how to solder and screw things together without cross threading them to actually build it and that's a really important thing to remember is that when you're in the trenches you're part of making stuff happen you may not always understand why you're burning your fingers trying to solder some giant thing that he's calling a computer computational I don't know we're just trying to break codes to defeat the Germans but when it works right we've changed the world wherever we are in that stack and don't forget the engineers and things yeah so he oversaw the bomba called doc because he carried
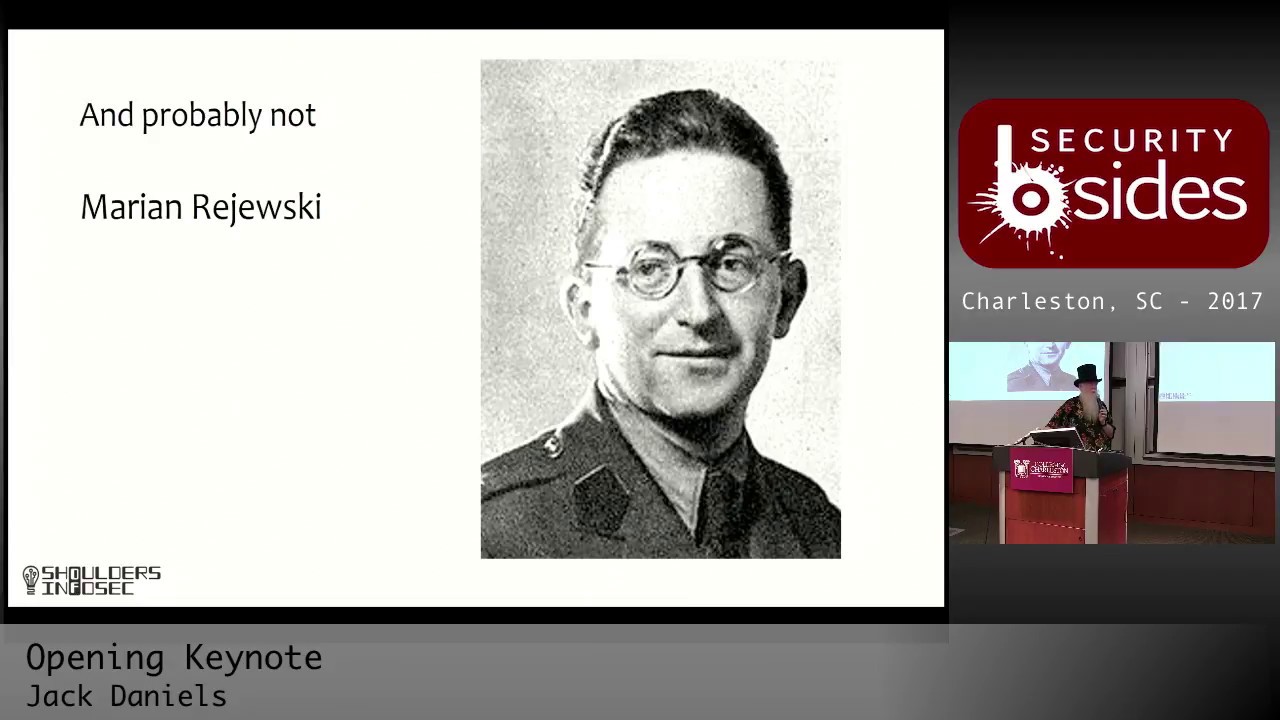
leather basically doctors satchel with all of his tools and stuff but then these are some folks that are often overlooked this dude Henrique zekowski the reason we needed they needed to build the bomba to break the enigma codes was because years before this mathematician came up with these sheets which helped them on paper crack earlier versions of the enigma codes the poles beat the Germans at math did they didn't hold the advantage for long unfortunately he worked with the Jersey risky and marine reishi with this dude this trio of mathematicians and cryptologists had you know probably four stalled invasion and other things because of doing they get overshadowed by Tauron maybe appropriately but their stories should
be heard too if we come forward from ancient history but somebody that was around for part of that the computer will touch men everywhere and in every way almost on a minute-to-minute basis every man will communicate through a computer whatever he does it will change and reshape his life modify his career and force him to accept a life of continuous change there are people in our world today that don't think we're at that point yet when they use landline they're using a computer but I assume most of you would think this is this is a fair statement this assessment of the impact of computers on our lives I don't know how many other people would have
said it in 1966 Willis ware was an amazing amazing guy he also understood the privacy implications of that and he's why we had the first government privacy stuff good old Jerry Ford after pardoning Nixon gave us the first Privacy Act in 1974 the good old days when the government cared about our privacy but anyway Willis where is somebody that again unless you're an old goat er have done some research you probably don't know about and that's unfortunate because this dude was brilliant he was at Rand for 40 years 52 to 92 started his career doing electronic identify Friend or Foe automatic identification of aircraft during World War two took that through decades a couple of things
that he's most notable for the the document called the ware report which pretty much defined government and military security and technology for many years dig into it in a bit it's an amazing report and it's it's remarkably prescient computer the the sexy title of computer controls for computers or security controls for computers 1970 let's see if any of this holds up certainly a security control will be cheapest if it is considered in the system architecture prior to hardware and software design no really user convenience is an important aspect of achieving security control because it determines whether or not users tend to find ways to get around ignore or subvert controls Wow thankfully we've got that salt here is a horribly dated
useless little drawing that is sketched up in that document which was drafted in 67 final edition was 71 and take a look at this and kind of laugh and how heated it is and then change two or three words and maybe a graphic or two and realize that I can do an introductory security course with this dog with this image right here change few words but this is it this is our world today few things have changed but that's that's it the way report actually reads it's not terrible some of it's dated it's worth the read sometime but yeah they're people been doing this I do need to stop and say something I want to make it
clear defining problems is generally speaking weight easier than fixing them so don't get too about how long we've known these from but if you can't figure out what the root problem is then you're probably just gonna put band-aids on it and you'll spend your entire career putting patches on a shitty OS instead of actually making real progress not to editorialize about the state of computers but here's somebody else that very few people outside of government and old timers know about Bob Abbott an amazing guy let's see what did he do author of the first set of privacy and data confidentiality policies for healthcare he he wrote the first multi-user multitasking OS for crate class supercomputers that went into 24
by 7 operation what a project that produced the first physiological monitoring system for open-heart surgery recovery patients he's arguably the first information security professional when he left the government he became a consultant and did security consulting in the early 70s before that was a thing sneakers movie sneakers the team that you saw there was based on Bob Abbott's original red team at NSA every member of that cast that was on that team had personality traits for people that Bob brought in and taught closing scene when we finally find Darth Vader when James Earl Jones appears his name in the show is Bernard Abbott Vinod - Bob Abbott who was
very cool dude and then there was this researching to secure operating systems this is a little bit more dated and a little more tedious to read but if you're really into this stuff there's some interesting things here but there are a few parts of this report again from long ago 71 to 76 that are telling to that I think are interesting I mentioned BB and 10x when I was talking about earlier it was a secure operating system and that means dumb mistakes but anyway let's see if there's anything useful that we got out of this in the early 70s this document will be especially useful if it reduces the current tendency for the same security
flaw to reappear repeatedly in different systems sorry Bob you tried you told this man so there were seven key flaws that they identify again easier to identify them to fix but if we don't identify them we're not gonna get a root cause so incomplete parameter validation maybe it gets better inconsistent oops come on it's got to get better oh oh he warned us about race conditions time to check out time dnews I wish we could get down to worrying about this the first three have kind of beat us up not this one thankfully we have solved Oh prohibitions and limits in that don't actually stick and logic flaws okay so after being making fun of that I will
point out that we have largely moved those out of the operating system firmly deposited them into the application layer where they're actually more dangerous but that's already it's it's progress it's progress of his sort right Jimmy Anderson and I like to talk about because of a quote from spat from when he lost his contributions involved both abstract and practical generally credited with inventing and explaining the reference monitor idea audit trail based intrusion detection yeah using audit trails do IDs before a network IDs was a thing he was a contributor to the where report there was the Anderson report to the Air Force which defined military cyber security cyber security forgive me computer security I work for a vendor I
have to say cyber a lot I feel dirty orange book and a bunch of the rainbow series stuff but this is what I love about staff and it's worth mentioning spaff has become a good friend over the years and one of the things I really hate is that I often refer to his obituaries and tributes to people that we've lost but this is worth a read Anderson had broad interests deep concerns great insight and a rare willingness to operate out of the spotlight says the idiot in the Hawaiian shirt and top hat his his sense of humor and patience with those earnestly seeking knowledge were greatly admired as were his candid responses to the clueless and self-important issued
public recognition preferring that his work speak for itself let me roll back there
sense of humor and patience with those earnestly seeking knowledge that's why we're here if you want to learn you're in the place to learn you're in the place to share even if you've learned something you think everybody else knows you bring a unique perspective to it you just discovered nmap can be useful for diagnosing your mail server you probably came in it from a different path than thousands of other people who've discovered that before share it with somebody who doesn't know it and I want to leave you with two actually there's a certification called certified ethical hacker some folks make fun of us other people use it as a tool as stepping stone I have a real problem with the
term ethical hacker because it implies that hacking needs the title ethical in front of it but if we want to talk about ethical hackers this dude was a punch card systems expert in things you would probably call pre computers computational devices the French used them for the census in a world war two they over the Germans over in France and Rene kept his job working for the Vichy government he was the only person who understood the systems as well as he did he sabotaged the French census for years saving literally untold number of lives because he made sure nobody could know what did it cost him he was eventually towards the end of the war found out
arrested imprisoned and died at Dachau he hacked the system to save lives so when people talked about what hackers do this dude is righteous hacker and I wish we have more people knew that story there are some others I've got a project called the shoulders of InfoSec there's a really hideous wiki I've done a whole series of talks on just some people interesting things and as I was getting ready and thinking about the past couple of years I realized is one more person that needs to be there and he's not a foundational figure in the industry but it really works well with the b-sides idea and that's our friend Rance who passed away a couple of years ago for
those that didn't know him he was an amazing person but he shared what he knew and he would come to events like this and he would DJ at Derby con but one of the most amazing things about Rance the reason they call him a magician is he would walk into Def Con and walk past a bar in the lobby and he would spot the one person who was really having a bad time but doing a really good job of not showing it and then the white Russians would come out and they'd feel their rants and I were good friends but we were never terribly close and I realized why when he passed away I never
needed grants he found the people that needed him and that's amazing there are people like that everywhere especially in this community so you know one find those people and to become one of them so with the highly complex timeline let's come forward let's take a look at a couple of reports that I want to talk about these are not brand new but they're not ancient anymore science of cybersecurity most important attributes you know we're trying to we're trying to professionalize our industry we're trying to be a real thing with these securities is real now it's not joke anymore so coming forward most important thing that we can do most important attributes would be the construction of a common language and
basic concepts in which the security community can develop a shared understanding okay what's machine learning versus artificial intelligence what do you mean by threat intelligence we're not there yet and it's one of our challenges and when you talk to people about things especially it b-sides or other community events if you're not sure how they're using words these should be conversations and you can get wound up about what's right and wrong but at least make sure you have common language it's been a challenge precise definitions matter until their precise set of objects that can be examined carefully and clearly it won't be possible to increase the level of rigor here's one that drives me nuts because
this is those of us who are or have been practitioners live this deep understandings this tends to be the academic versus practical but it's sometimes government versus academic or whatever we spend our lives applying patches and doing bandages I'm not saying take your firewall away but wouldn't it be awesome if things were secure enough that nobody needed to do egress or ingress filtering because really so we apply bandages we build complex bandages meanwhile people think about deep thoughts and the to never get reconciled I won't say never but we have a real challenge of if you try to solve the underlying problems that doesn't if you try to solve underlying problems that doesn't get the you know this
month's patch is installed on the other hand if you don't if we don't work on underlying problems we're just gonna be putting patches on forever I used to know a lot about securing in tea for how much value is that today well there's a couple of environments is actually really important still unfortunately but you know I'm sorry if you work there but it's there I used to be in the Boston area and about three years ago I went back to a meeting where I talked about this when VMware just started becoming a really big thing the in few days I said to the group this is really cool watch this is our virtualized mt4 this is how I
virtualized this thing and there we go and somehow I'm not trapped on the old hardware nobody's like this is cool and I said the problem is this means nt4 will never die and they all laughed at me so a couple of years I went back to the same group and I said you remember when I said that like three people were still in there like yeah who's running in t4 and one guy's head literally hit the desk in front of him hard enough to hear like told you so but anyway for most people my knowledge of in t4 isn't useful I had to have it at the time I'm not trying to be depressing about this
what I'm trying is is that we need to do a better job of crossing the line with with the deep thinkers so that we don't keep staying on this one of the interesting things that often comes up and this documents well this guidance from other sciences and immunology in computer security
for a species to survive and thrive you only need one breeding pair to survive your company survives all the rest of us go out of business when the internet collapses is that an acceptable outcome for us no okay maybe we shouldn't directly apply these without thinking about what we're saying yeah nineteen five 9s mortality rate is acceptable for a species survival I think we should probably aim a little higher but that doesn't mean there aren't things we couldn't learn so we need to break or at least bridge silos one of the things that some of you I'm sure have discovered is we often talk about us education and there's military and there's government and then there's the
industry and then there's us and vendor land horrible people that we are and then if you haven't been in there dealt with them you don't realize that saying government and military don't put those two together that's very different saying intelligence community if you don't separate civilian versus military intelligence that's weird but then there's the stratification we all fight on a daily basis where you're trying to get some of these attention above or below you we just need to get by there we need better language the last two are things people have talked about for years and we finally have the power to do it computers now have enough power to let us do some amazing things
of course we write software like slack which takes more power to run than so anyway let's move forward people and machines here's an interesting thought
[Music] where's just part of what you did for your job anybody anybody work on a team that has too many highly qualified and talented people and you come in on under-budget know we have computer systems that are it is cheaper to run a full operating system on a full computer for any task you want than to run and embedded OS on a custom chip that brings a lot of challenges to it think about that did the idea of running qnx on a modified chip or something running a light OS that takes experts that aren't available and cost too much just throw it on a Raspberry Pi or something like that and just have a stack of them it's okay the
core some lighter things it's running busybox what could possibly go wrong in the middle we had consumerization and commoditization of hardware and software and then we added global interconnectivity and we're screwed at one point in time you can explain everything that happened on a computer it used to be like a computer science thing that you're in at some point an instructor would say hey what's happening on your computer in this period of time can you do that with your video card right now yeah the early days it was all about crypto and confidentiality and now we have to pay real attention to integrity even if you're not running you know centrifuges at Natanz the integrity of your data is
challenging when we encrypt things and store them in cloud if we don't have integrity it's all gone because once bits move around we're hos
here's a terrifying thought who controls most IT spend in organizations these days your marketing department because they spend it on advertising cloud platforms media customer tracking they control our IT spend than IT in many organizations think about that automation yeah that's cool stuff if we do it right it's great if we do it wrong it's not so what about the future Douglas Adams's I really didn't foresee the internet but then neither did the computer industry not that that tells us very much of course the computer industry didn't even foresee that the century was going to end those of you that like me were at work on that Thursday that's another whole nother rent it was a fraud it was a fake no
thousands and thousands and thousands of us busted our asses for a very long time to make sure nothing happened we can actually do this stuff we did this stuff it wasn't overhyped we made sure it didn't create real problems Rudy Giuliani go see so I'm no futurist and certainly not a Willa swear but I'm certain that we'll still have some of the same problems but for all of the horrors of these things would you like to not have computers in your life would you know what not would you prefer that we didn't have an Internet and global interconnectivity we got to remember how much good is done by these things everything old is new again
obsolete network security stuff is relevant again because IOT means we have does this sound like Windows 98 in secure and insecure Bowl systems connected randomly with more ports open than they should be so maybe we need to know what on the network oh right because endpoint security doesn't work on endpoints that's problematic we got rid of agents because they would blow to our systems and now if you don't embed agents in a lot of systems how does that work with container security or even virtually but yeah no we're not embedding agents we have no visibility and anything anymore but the processes are way better now we can do things like you know kernel level micro virtualization we can do micro
virtualization and hardware we can have a reference indicator you know a reference model running on the same chipset as your operating system and see what's shifted there's really cool stuff we can do now and we can run slack you need all of our memory and this is where you expect me to predict amazing things and I'm not going to here's the future recurring theme if you want to be lasting good for security and for yourself make friends here and elsewhere and across communities investment in immediate technology is required but it's ephemeral investment and big problems might solve some things down the road we've got to do it but it's a long game and we've got to work together to do it
and with that I'm done but that's not the end this is just the beginning of besides Charleston so thank you very much you've got time to grab the bio break and maybe a snack and then on with the rest of the conference thank you guys [Applause]





