Sean Eyre & Phelan Guan - Using mathematics to draw usable operational insights from WiFi data
Show transcript [en]
all right good afternoon everybody started running in last minute typical styles you'll see called out later in the slides we we don't show up on time ever all right so math puns weapons of mass construction and mass destruction presented by shauna are failing why next slide please agenda we're gonna talk through our BIOS because we always do that at conferences and then we'll do our obligatory disclaimer followed by a sketch of what we wanted to accomplish with this and then we're gonna talk a lot about science mathematics nerd stuff and then we're gonna draw some hopefully operational insights that both the red team and the blue team can use from this and then one of my former co-workers is
going to judge me really hard at the end of this talk and make fun of you next slide please BIOS I'm Shawn I'm the CEO of air Q security company we provide cyber security services to people who do counter sex trafficking I'm also a Python ISTA an O Center I do a lot of judo and jiu-jitsu so that pretty much describes me and falen can introduce himself alright none of the views or opinions communicated in this talk also make sure your your camera mic is put this onto the camera okay none of the views in this talk reflect our current employer past past employers current employers or future employers next slide please all right so we had an idea so we know
that advertisers ISPs and a whole bunch of other companies collect telemetry on all sorts of users on the internet and then also on devices as you're walking through stores so what's happening is when you're when you're browsing the internet your ISP is collecting that flow on you and they're minding your DNS and nation to build some sort of profile on you whether they know you're particularly more not they can then serve stuff back to you when you go to Amazon you're interacting with tracking cookies and Google's doing tracking cookies and everyone is constantly fighting for your data so that they can find ways to monetize that data on top of that when you pull out your little
personal tracking device right and you leave your weapon when you leave your house your handset is beaconing out saying are you my mommy and then all the other laps around them are saying no but thank you for asking me that question because I've got an orchestrated Wi-Fi platform and my department store that allows me to turn that well signature signal into an idea of how you're walking through the department store and I can combine that with video footage etc so the overall idea here is everyone else is collecting telemetry and they're not open sourcing the code on how they're analyzing it so can we collect telemetry on Wi-Fi in a way that doesn't violate the CFAA Computer Fraud and
Abuse Act for those unfamiliar and then turn that into some sort of insight using math that we can then share back to the community to get people thinking about if I don't have thousands of dollars how can I turn things like signals that are all around me into something that I can help my sock with or help my red team with so we wanted to figure out ways to collect the data pretty straightforward pretty well-documented process apply math to it increasingly well-documented it's still kind of nebulous on the googles and drol insights out of it and then apply those insights back to red and blue team next slide please
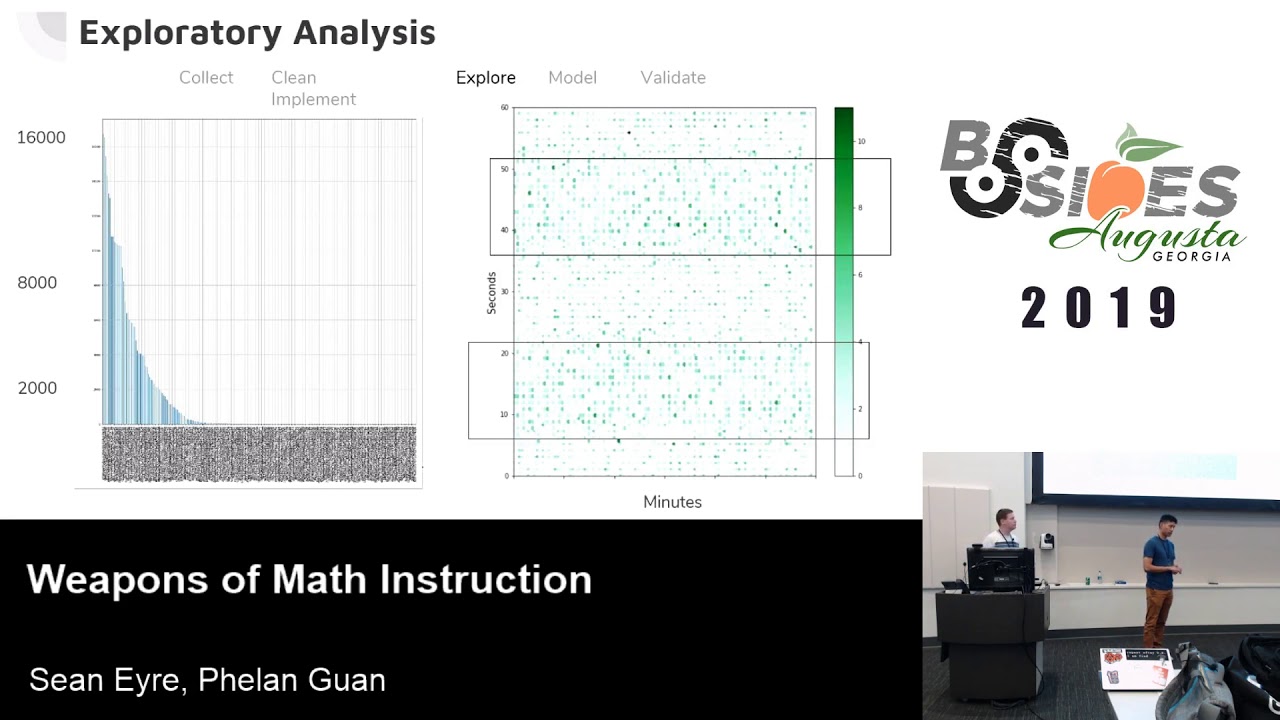
after that we can do some math analytics we'll do some exploratory analysis where I'm kind of okay just do like a sanity check like hey does this look like we can actually understand anything intuitively then we'll finally get to like the actual like pieces like apply some sort of model to to make sense of the data that we've collected well of course make sure that I validate what our data is telling us what we think it's telling us and then finally we'll kind of implement every plan ends with profit so collecting and data cleaning so I'm gonna talk a little bit about the data collection and the falen we'll talk a little bit more about the
cleaning the actual mathematical processing of it so any anyone in here ever done wardriving ever ok wardriving is actually legal so you can admit to it but I'm not your lawyer and I don't play them on TV so don't listen to me so we started with raspberry pi 3 because every fun project starts with a Raspberry Pi and then we connected an alpha antenna to it because we could force that into promiscuous mode to monitor whatever Wi-Fi signals we want to and then we started out by running kiss man and we'll talk about that a little bit more and then ended up writing our own collection script so we collected about 30 days of Wi-Fi Wi-Fi
signals from this one sensor that was sitting in my apartment at the time just watching the Wi-Fi spectrum around me and what is primarily collecting is this skip column zero because it's unnamed at our society that we didn't actually end up going back and collecting the name of the sensor that it was running off of epoch time because I can always process that into a better timestamp later the Oh UI which is always in the bssid otherwise known as the mac than what we have here is a hash of the MAC address combined with the SSID and a salt and then the company name is associated with oh you I and then we break out the epoch
time and to easily Bend Bend value so I could have stored all that information as a timestamp that's human readable instead of just epoch time but if I go ahead and store this as five five or six different columns I'm immediately set up as we'll talk about vectors later just switch from those columns straight into vectors and straight into different types of aggregations so right now what we're talking about is basically your Raspberry Pi alpha antennae collect all the things next slide please so porque no los gets mad um why not use kismet everyone uses kismet for Wi-Fi and kismet 2.0 is awesome it's got a web front-end and like he presents all this really valuable data
unfortunately what kismet is gonna tell me is the number of times I've seen a hotspot the first time I saw a hotspot the last time I saw a hotspot and the rough view the rough the GPS coordinate of the different times that I've seen it what it's not going to tell me is every time I've seen it along the way and at what time hack that was so for the kind of information we were trying to collect we really wanted to get towards what we would call a pattern of life for a particular device so what I need to see is not just the first time I saw it and the last time I ever saw it I need to
see how frequently it stayed in that same spot between that first and last time so instead we go to scape II and we write a pretty easy script and you can find Google stuff on how to do this so we zero in on the beacon frames with 802 111 and then whatever zero and beacon frames and then from there we say if I haven't seen this in a minute put a new log in or if there's some sort of change from the previous time that we've seen seen it even if it's only been two seconds put a new log in and then we implement channel hopping so you can watch across all the channels and now
we've got a collection platform that's saying every device as long as this in my area I'm keeping track of the when it stayed and I get really granular down to about a sixty second gap of when it's walked out of my collection area you want to add here
Collective near an apartment or you can see on whole Wi-Fi maybe the refrigerator and then it starts a tail off towards ya devices that kind of come in and out of the apartment complex those cars they're Wi-Fi hotspots and so from this like initial swag we're kind of looking at well maybe delineation between stationary and some of you are already identifying the the weaknesses with that conclusion and we'll talk through some of the weaknesses that we discovered as well the other thing that we want to point out is this diagram on I can pick up a laser pointer on the right here so this is actually my home Wi-Fi over that month that we collected
and this is it's more apparent over a single day but if you look closely this is basically minutes of the day so every minute of the day was given a value from zero to what five hundred I don't know the five thousandth value or whatever that it is and then seconds of the minute and so every time that we see something that falls into that particular index a minute of the day and that second as an XY coordinate we darken it based on the the number of times we've seen it so darker values are more common values so what I end up having here is this period of relative like relatively less density followed by
a 10 to 15 second of high-density 20 seconds of none or not none low and then a high-density period again what this is showing you is even though my SSA or my own hotspot is responding to probe requests you've got this natural beacon period that is not as dependent on the probe request as interacting with so I my home Wi-Fi hotspot has this period where it starts out for about you know five seconds of just monitoring and responding and then it'll advertise this location go back into monitoring advertise monitor and keep repeating this process so this is starting to lead us down to a couple different threads to pool is that I have a natural polling rate for a Wi-Fi hot
spot and then I also have some devices that I can monitor really really well and I have consistent coverage of and then I've also got devices that I very rarely see but I've got a whole lot of them that are down in the five to ten observation period and again I'm collecting observations on them at a minute polling rate so if I've only seen them one to ten times that means that I've only observed them you know I'd have one maybe a ten minute period and we'll be primarily talking about hot spots for the rest of the talk many of the observations that we have from hot spots which is simplified data collection you can easily extrapolate
out to handsets as well you've just got to tweak your collection to target handset beacons instead of hot spot beacons
[Music]
Google dictionary definition of what a vector is so we're not really talking about directional flights or anything like that what we're talking about in specific to math is next slide a list and then each specific each specific position of that list mean something so you can see from them the second half of the slide there that we have three different vectors wine is a home Wi-Fi Becker one is a fingerprint vector for a my five puck and the third is for like a car and so there are 24 positions there from 0 to 23 and each one of those represents a particular hour today so like John mentioned in our actual data structure it's for every minute but
just for the sake of not putting 5,000 5,000 position list on one slide one hour so for example in the home Wi-Fi let's say over the course of a day we effects over the course of the day we see top bun so home Wi-Fi so at midnight we see see a beacon 10 times great 10 times and a home router liking it all the time where someone's Maathai Punk all right at midnight this device is still here at one of the lorry it's still there and then sometime around 8:00 in the morning the value drop from 10:00 to 5:00 between our way through that our seem like ok just device left the area around 8:30 in the morning and
then it's gone and I'm going to 10 9 and 11 I think that I knew something like that and then they go back to work or run errands go see a movie and then they come back at around 6 p.m. and they're there for the rest of night so this might be something that like work on my thigh hugging you and then finally a car you know that only visits every so often like you don't see it for most of the day most of the morning and then like at 2:00 or 3:00 p.m. stop by Jody you know come comes a-knockin and then there's also the the assumption that for a car like device that the Wi-Fi is only on when
the cars is powering it so even if the car itself was there then we'd only see that when power was being routed to the Wi-Fi hot spot a hot spot for so in classification there's unsupervised learning method a supervised learning method means that [Music] probably Dudley did this wrong and then unsupervised method big boy big girl rules like okay we're gonna say like we don't need you to tell me what this is but I'm kind of gonna figure out on my own whether or not this is right or wrong so we use for this a superbug I'm sorry an unsupervised learning machine learning method normally cook clustering where you take this let's say this is our example data
set we can kind of intuitively see that there's one cluster two cluster three clusters and then your metrics are basically distance or neighbor amiri characteristics etc etcetera and so we start by saying you know what we're going to use a method called uniform manifold not approximation projection start off next and it didn't really turn out to mean anything so when we first kind of ran this like this absolutely nothing to us like we've got MiFi devices kind of everywhere like and like home Wi-Fi devices don't really kind of fit into one area and so this is time over talking about an exploratory analysis where sometimes we apply the wrong model or technique and we have to
kind of just kind of use our best judgment to sell a hate it are we doing the right thing or not in this particular case we really did the wrong thing because we didn't read the fine print in the documentation but later that there are certain assumptions about our data that this particular that you Matt makes assumptions about most notably that you map assumes that your data is a Riemann manifold which is this like nice smooth curve if you kind of plot it out which this thing most certainly was not so R but this was still a great learning point for us because we said like there's a lot there's need to be a lot of noise like a
lot of confusing reasons for why these things are associated together right like Wi-Fi devices are here to here but they're also like here here and here as well so maybe there's something there's confounding factor that's polluting that nice pattern we're looking for so that so then we led us to looking up PCA but what is this PCA sort of thing so if I had to explain to my grandpa walking back on the cornerstone with this car in a bag so you get home watches stories PCA is just a way to take all the factors that you have collected put them in mash them together and then just fill out the most important concepts from that mish-mosh of factors so the this
like nice dog vs cat example that we have here let's say we we want to figure out the differences but we want to say this animal is a dog or so our two first factors we want to use is like the height
but color height and weight and so one ground here to show that one principal component for about 70% and then get to our kind of max saturation around a layman's term example of that is if I make a principal component for every member of my data set then of course I explained my is our data set but what I'm really looking for or what the factors that they share in common that maximize my ability to explain my entire data set
results are humorous what we do see at least is all the green dots are on the right track
well it's called k-means clustering so we're we said hey we want three distinct groups in our data set and then classify that automatically we chose three because even though we promised you guys to either mobile or stationary we wanted to kind of stay like all right these are high confidence definitely they share high calm she's definitely mobile and then like in between we can kind of like play with that and kind of draw some additional insights so what was really encouraging with that all the stuff in this in this red field here we were like pretty sure these were all like home Wi-Fi devices so really great to see and then all the things that we expect to
move around a lot like cars my 5s people's cell phones almost all the way to the left so again pretty pretty and all the stuff in the middle we didn't have like a good explanation for why we'll talk about a little bit later of what we learn so you almost have you can almost speculate with this that you have a fully mobile a semi mobile than a fully stationary camp here with as things start to blend into each other's groups some overlap in that so like the ps4 once so we did some of this analysis the raw data has more detail in it than the hash cleaned-up data that's releasable so we're able to like look at
SS IDs and see things like Nintendo switches and P spores and and stuff in there that are using that are generally staying in the same place but are sometimes activating a hotspot for doing ad hoc communication cetera which starts to explain a little bit of that middle middle area where it's like I'm acting like a mobile device but I'm typically used at the same place that my parents let me be used or let me play my switch every evening or something like that
all right we're going to talk through alerting which is something that every single InfoSec professional understands in some manner and something we'll talk through set three because I love set theory then we'll talk through classification again a little bit and then change detection but first next slide please what we learned about the Wi-Fi so when Wi-Fi sends a beacon is a function of three different things so it's a function because a math nerd of its natural rate remember the slide we showed you where it has a programmatically determined my developer said I'm going to advertise myself this frequently unless my setting gets changed to not advertise my SSID and then I'm going to very quietly advertise
myself instead of it saying nothing and then if a handset sends a probe that has the field basically designated as star wildcard anyone if I'm if I'm a lap and I receive a beacon frame that says anybody out there then I'm programmed to respond to that so that's gonna cost me to send out a beacon frame as well and then finally if someone calls my name and says are you my mommy and I'm the mommy then I have to respond to it right so either either the little ducklings like any mommy's I respond and then says are you my mommy and I have to respond so there are these three different things that cause us that causal app to
send out a beacon then on top of that our ability to detect a beacon is fundamentally impacted by meatspace ie the real world right so it's an analog signal moving through the RF spectrum communicating digital information so if there's a wall between my sensor and the and the web the RSS ID is going to get communicated there and the signal strength is going to be impacted by the presence of the wall but we have some of those effects that cascade through this entire function if someone calls my name through a wall it's harder for me to hear it so sometimes I'm not going here but when I do hear it I'm gonna respond and then the person listening
for that response also has that problem so this is one of the things we picked up that was affecting our ability to classify patterns of life with these devices is there's much more real world impact than maybe we initially assumed
as well as actually collecting the RSSI value so escapee can do that by the way which didn't end up implementing that you don't pull that out of the 802 11 information you actually have to pull it out of a frame called the prism frame which describes the signal strength that it gets passed down at scape ease object model so it's doable but it's a little wonky so we just didn't get around to it next slide please all right so we also learned about undocumented oh you eyes so we have a lot of oh you eyes we parsed him out of the max in our data set that we're like we're gonna discover all sorts of new things about outtie
Wi-Fi hotspots and Ford Focuses and all this stuff and we did discover a little bit of that but nowhere near as much as we hope for so it turns out that your Wi-Fi MAC address has a bit it's the seventh bit from the left it's a very specific random location but it's in the RFC called the locally administered bit and this bit is always zero unless someone has flashed a new mac address on top of the bssid so what that means is any time you have a locally administered or anytime you have a randomized Mac you're most likely going to have a flipped locally administered bit as well and anytime someone is spoofing a MAC
address it's gonna flip that bit so what we end up seeing by doing going back and redoing some of our lit review is that a very high percentage of randomized MAC addresses end up in unallocated oh you eye space so it's not document it's not registered to anyone they're allowed to do that because of randomize and they also have their locally administered bit flips and increasingly with devices after 2014 Apple and a lot of other device providers started working in mac randomization by default and so that disrupts our ability to collect without forcing the locally administered bit into our feature space however there still are some oh you is that weren't in our publicly available document of
registered Lu is from I Tripoli however so we could see they weren't in that document but we could see that all there are societies were consistent in a way that would allow us to assume a device manufacturer which is what the ouy is supposed to communicate so Audi being example we saw a couple Ford cars and then a couple different mobile hotspot devices that were specifically that we could see like oh this is most likely a Samsung or these devices are consistently coming from Verizon kind of thing and then anemone yeah that one wasn't pre-planned we found a really fascinating paper those like 300 pages long that all reference at the end that if you want to know about like whether
or not Mack randomization protects you from nation-states the answer's no but the paper dives into it in detail so alerting all right so we've came up with three types of alert alert when a new app is discovered so I'm sitting and I have imagine for a second that instead of having just one raspberry pie and an apartment I have a campus that I'm responsible for or a campus that I'm targeting and so I've distributed sensors across that campus and I want to start drawing insights from it so the first simplest one I have is every Mac that I see just period no matter how frequently I see it I put it into a lock and then any time
something new pops up that's not been in my log and naturally because I'm writing in Python and I'm lazy I'm gonna keep it in a flat file because that could never go wrong anytime I see a new app I'm going to cause an alert and I'm gonna exhaust the stock because things are coming and going all the time these have potential meetings so if I'm on blue team whenever I see a new app pop up it could be a rogue hotspot and because I'm being proactive now I can immediately walk in on it and turn it off instead of having to pull out my Wi-Fi with the directional antenna and attach it to my laptop and look like
a nerd walking around the halls being like what student in my university just plugged in an illegal router I awesome I also can potentially tell when a mobile hotspot enters the parking lot in the red team's van if I switch this over if I'm in a very controlled facility and I switch this over to looking at handsets instead and red teamer comes in with their cellphone on and doesn't turn off as their Wi-Fi if I have a very good tight understanding of who actually works in my facilities and where cell phones are allowed to go and when they're allowed to go there whatnot I immediately know that a new person or at least a new device is in my facility and
this has incredible OPSEC implications for the red team if the blue team is doing something this advanced now most blue teams don't have the time or the money to do something this advanced this is not expensive but it is time intensive and then if I'm a red team and I'm watching infrastructure new apps potentially mean new infrastructure that I can potentially compromise it also could mean a new person in the facility if I'm watching for a particular target it could be that they showed up the next thing we've got is alerting when a specific laughs is observed so this is very very very doable however it very seldomly has operational meaning unless I can closely tie that device to a
person or situation so once I can closely tie it to a person or situation now having a distributed sensor platform that says when it hits one sensor versus another gives me some kind of operational value this often could be if I you know cheat on a Wi-Fi Fox and Hound exercise at a CTF and like covered the town or raspberry PI's before it before they like exercise goes off I could very quickly find that find the Fox but most people don't have you know what it's like 35 bucks per Raspberry Pi most people don't have the money to cheat on those kind of things speak for yourself alert when a known WAP or handset enters an off-limits area so if
I control the gain of my antennas precisely and I distribute my sensors accordingly I can actually a very detailed sense of am i watching a particular room am i watching multiple rooms and then I can say like cell phones are allowed in this half of the building but Bob is not allowed to take his cell phone into this other half of the building or I can begin to use cell phone monitoring to tell when the migration patterns of my employees this goes back to how's the corporate world using this they're monitoring employees this way it's happening Eadie's kutis is a great talk on it actually he does it to his employees you he does it with his
little automated office to greet them when they walk in the door but he's still spying on them to do it so you can enforce the no cell phone policy you can enforce physical access controls or at least audit physical access controls you can tell when employees get in late or if I'm red team I can find the VP's office or track his movement through the building or out of the building into his car and home kind of thing so you can imagine the kind of nasty things I can do if I tie a device to a person and then can follow that device very easily next slide please so set the reso bucks there's a lot of simple calculations
that we can do with sets by just simply doing set unions intersections and differences so for example one of the common info set questions is how do I know if my monitoring infrastructure is seeing everything that I want it to see so to solve that problem instead of fighting with you know elastic stack I'm going to make a set of all observed IPS by taking all the IPS I've ever seen in my NSM and I'm just going to go into Python and I'm gonna cast them as a set because python knows how to do that and then I'm gonna do that again with my asset inventory by IP and so now I've got two very well managed hash table
based data structures and I'm gonna run a minus B which pythons going to calculate almost instantaneously and it's going to show me all the IPS that are observed but not on the inventory because a is observed and B is inventory and immediately I know what I'm seeing but that I'm not tracking in my asset manager so that could be a rogue device or it could be an out-of-date asset manager and then the flipside is B minus a which are devices that I'm tracking but I'm not seeing and that's either going to be a gap in sensor coverage or an outdated inventory or device that's gone stale when it shouldn't have gone stale so how do we apply this to
laps very very similar manner and I'll actually very shortly skip to X let's go ahead to be the Venn diagrams light if I want to apply this to laps then I need to have monitoring at various different campuses or geo locations where the intersection matters so let's say I'm monitoring in New York Austin and Silicon Valley if I'm seeing just one hit in Silicon Valley that's just a worker but whenever I see someone that in a short time frame hits in both Austin and Mountain View now I have someone that's a little bit higher up in the chain because something caused him to have to be at both campuses within my time frame now if the longer the time
frame the less valuable this is longer the time frame hey it could be an agile developer who just did an analyst analyst exchange or a coder decoder exchange they're the people I really want are the people who go to all my campuses in the shortest period of time that is my biggest target likely the CEO in the middle of an emergency for this organization some of us have cars from the 90s okay like but then what we also want to know is like when relationship overall data said changes that might be a interesting sort of thing to kind of draw out so like if we have if a device is maybe broadcasting all the time but now it's
only broadcasting like every hour wherever so a couple hours that itself is also a change a change detection that we want to process so we talked a lot about like different applications made now we're talking a little bit more about like hey what hope to do in the future it's one big gap and all this is like hey maybe we should have done a little more collection and now so the other Rizzi values the value of how strong your signal is relative to our sense of it so I mean the bottom line is like you can't really do Taggert like come reassociate that one thing to someone without looking at their state example talk about where talk here is like if we
reduce the signal of the antenna gain of sensor to like just a check point or like an area that we're gonna choke point that where panelize people through now we can get to what Shawn was talking about we associated a device with a person we don't have to worry about what everyone else is doing we in the future maybe also wanna do some with randomize max so try to figure out like hey there's specific pattern of distribution to the random acts that we're seeing and then we can might be able to come for a first act like what type of device that random Mac is covered oh like we also said we didn't split our data into like
the usual test train and validate sets of data but that was just kind of our limited data pool apply multiple factors academic standards to this something we definitely want to do in the future and then for this particular thing we only use one sensor if we were to use multiple sensors across multiple different locations we can kind of show and track someone's moved from place to place or how long they spend a light at Starbucks versus Home Depot and then obviously nothing is ever complete without using someone else's data to make sure that we have replicable and we reach the same conclusions using someone else's data to our methods you know someone referenced the huge paper that
Shawn was talking about was this last fingerprinting and tagging countermeasures paper a great read ton ton about Wi-Fi from that one paper and that's what we did guys so yes sir
correct
yes there are so the ones that we know of are the ones referenced in that paper we just pointed out because they use several I think they were government collected but open data systems that were designed to test their specific questions of does anonymization etc work so I think the French a couple French cities opted into those tests and they made their data datasets available so if we were to go back and continue work we would probably pull those and then look at them to see what we could learn on that if you want to find them their reference in that paper pretty clearly so that's the direction I would point you we have to give these away - all
right we got to give away these things and we need trivia questions for that oh my gosh okay so um who here has taken linear algebra yeah I got a couple so who wants to explain eigenvalues and eigenvectors to this this gentleman oh we can fix that we can totally fix that so yeah go take some discrete math and some some wentao and it's beyond the scope of this talk yeah yes sir
if you're gonna share the data it's absolutely a problem and then so anytime you're gonna actually start talking about people you start wandering into this territory that's called international review board territory especially if you're with a university where you're basically going to put out your research plan your data collection plan and talk about all the potentially like previously identified personal information and you're gonna submit it for an ethics review to see if you're actually unintentionally violating privacy etc because we weren't collecting on people and we weren't making any attempt to do to collect on people in this one we didn't do that and that's also why we sanitize the data with a strong of crypto as we can come
up with a lot crypto a strong of hashing as we come up with and will not be releasing the unsanitized data for people to look at but because you ask two questions you get an alpha antenna so huh the other giveaway we have to have go ahead we have not so we did all this in starting with Python for the data collect and then we actually did most of our analysis in Jupiter using pandas I personally use the Anaconda package manager for it and did you see anacondas or just do it so we also another common data science language loath to say this but you could use R if you really wanted to is vector data but
ours not a real programming language because it starts at one with its indexes so let's do that if you like pain yes thank you thank you there there are a lot of data analysis things out there I'm a big fan of Jupiter for therefore this kind of work because especially if you're going to present because it puts all of your Docs and your code in one spot I got a good trivia question for giving away the book it's not really trivia quiz the data science question so great question thanks you have to ask - to get a book though sorry so we're gonna ask this question and whoever can answer it most accurately first will give this packet analysis
book away from no starch press Vanna White will demo it for you okay so somewhat of a softball what is and Charles rvu can't answer this I mean unless you find it hard in which case go ahead but what is the primary like singular biggest limitation of k-means clustering or what's the hardest part of k-means clustering is another way to say that I know you know the answer but no one else all right Tory what is it wait what's that basically the same thing yeah so how many case you have right what k equals no but you don't really need to back it up neither he does yeah okay you have another question give it
away that's that's mr. Williams in the back right like yeah okay
what do you say that they do complain about getting closer now we've covered basically every phase except for the correct one we're almost there okay what's that mmm no close only applies to certain algorithms what's up Tori mmm that's that's one way to phrase it yeah knowing what your problem is that you're trying to solve say what yeah so I would vote that we give the people who tried harness the
good effort guys appreciate it all right last call for questions thank you for coming to our talk sorry for being late got a wonderful great day [Applause]