Ryuk The Shinigami of the Cyber World
Show transcript [en]
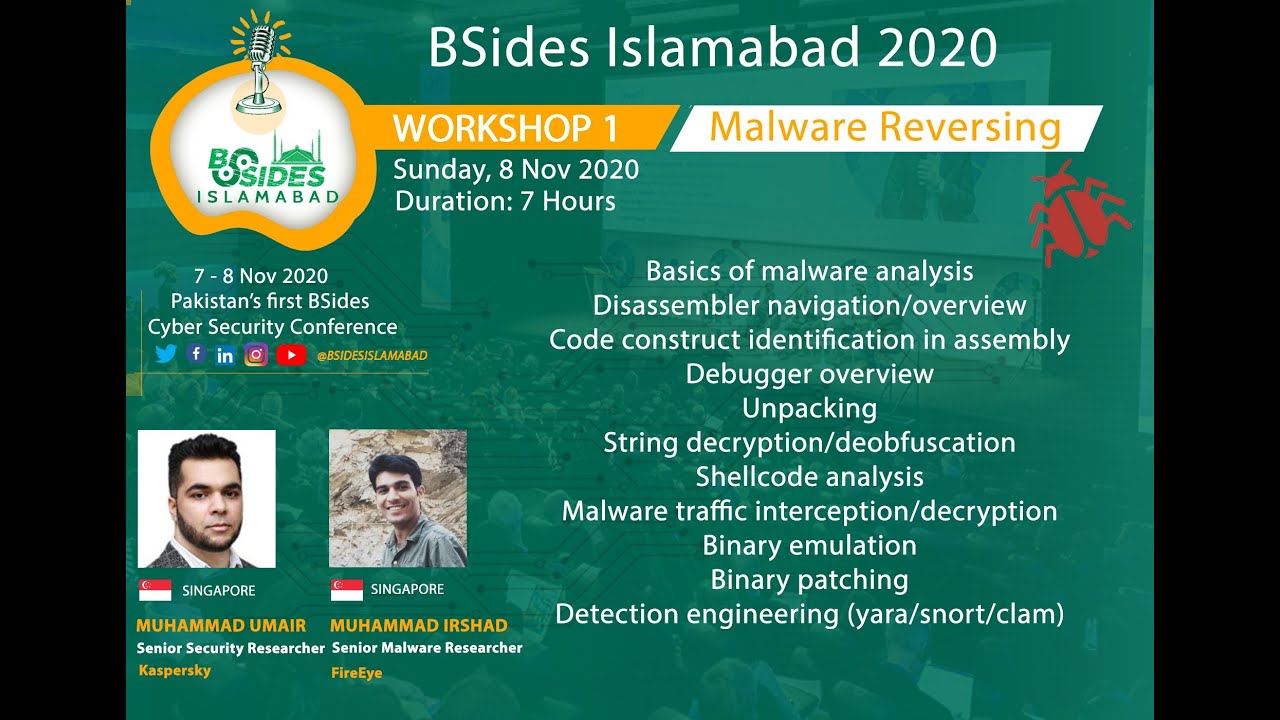
[Music] hi everyone uh we are back so this is the last talk of the day and also last talk of besides islamabad 2021 uh we have sonya shannon with us and she will be discussing about ryuk if you didn't hear about that that would be exciting talk before uh sonya starts i would like to say thank you to our uh you know audience who remained with us all the day and also our sponsors as well uh our silver sponsors we had tcn security ebrix and and applied network defense and we had sport partners undo id academy uh global information security professionals of pakistan gisb shisek women's cyber security uh organization and ultrasound and also uh we will finish on
the finishing of this last talk with the announcement as you know we have workshops tomorrow as well these are hands-on workshops and that will be starting nine o'clock pakistan time tomorrow so we have first workshop at demystifying cyber threat diligence hand zone that starts nine o'clock until 12 30 pm the second workshop we will have wasn't open source intelligencing the unknown by holla karim the third uh hands-on workshop would be writing detection rules effectively by saying hassan from 2 30 to 4 30 pm you must have received already uh the details from uh info beside islamabad.com if you have not received the details for tomorrow uh invites please reach out to discord channel and someone will be there to
help you out thank you so much for being with us and we'll see you next year as well so hand it over to sonia thank you so much and i would like to thank besides firstly to invite me for this conversation and this talk and i'm super excited for everyone to get on board and study and explore the malware ryuk which i like to call the shinigami of the same world so let's move on before we talk a little bit about the actual topic i would like to talk a bit about me because you know i cannot leave my narcissism at home ever so whenever sonia as you already know i have a bachelor's degree in computer
science i started my career off with blockchain development because i was kind of interested in what the technology is and then that ignited my interest towards cyber security then i currently work as a cyber security analyst at growth harbor and most of my work is revolving around grc and offensive security however my personal current focus is apts sorry rapt's or advanced persistent threats cyber terrorism and security regulations within the context of cyber terrorism emma as i said security analyst and by night i'm a student struggling to comprehend sometimes very simple topics so i feel like i just exposed myself quite a bit here let's move on to the actual topic unveiling the shinigami i know a lot of people might be
wondering what a shinigami essential so i'm going to do just that i'm going to tell you guys exactly what this is so shinigami is actually a term from japanese mythology where there's a lot of debate between whether it's a spirit or spirits that call people towards their death so think of it as the angel of death but translated translated into the cyber landscape you would have ryuk ryuk is the shenanigans of the cyber world and there's literally no difference between an actual shinigami and the cyber malware that is reuk and surprisingly it was all found in august the month of freedom so ryuk was like i really need to get out of here and i'm
so tired of being hidden in shadows i'm just going to go out there and cause rampage so the first actual recorded attack that was termed as the malware you was in august of 2018 where multiple enterprises were targeted when i say multiple enterprises i mean very big organizations most of them were government organizations within the us however there were other organizations some were from france someone some were from north america specifically canada uh however the actual list of uh targets we will discuss that further down the uh presentation but for now knowing what ryuk and when sorry not not but when do you actually started its rampage uh was the point and we will move to the
next slide okay before we start what ryuk is and what essentially everything will that will follow afterwards we really need to understand what is a malware a malware is any malicious software that is intended to hurt your system and steal your data and basically make you regret having an online existence and a lot of times there's this question that comes up that what's the difference between a malware and a virus and there isn't any actually in fact when you talk about malware you're talking about viruses because there are categories of malware so every virus is essentially a malware ransomware is a type of malware which is i think a good analogy for a ransomware would be
going to school and your teacher calls your brother and basically she complains about you so you bribe your brother do not tell your mother and so that's pretty much what ransomware is but instead of your brother and your mother and your family it will attack your system and keep it hostage and ask you to pay a ransom now normally these ransoms are financial sums but they could be pretty much anything they could be any informational exchange it could be any physical uh exchange as well so uh the term ransom and malware often is associated to financial sum but it would be associated associated to pretty much anything the victim holds uh there and important to them
so there's another thing which i would like to discuss in the conversation because i feel like a lot of times when we're having uh you know conversations about malware we don't necessarily discuss these things and that is that we need to understand what a malware family is when we talk about malware families uh we are talking about multiple malwares that share the same code base if you're into programming you know what a code base is for all of those who do not know what a code base is it's basically having a similar source code and that is being replicated multiple times so for example ryuk essentially is a family of malware just like there are
families of other malware such as hermes which we will discuss in this slide as well so ryuk isn't a stand alone malware it's actually associated to a whole family which is also called to you family or you ransomware families and in these you will find variation of views which will share the same code base but would have minor changes in the code to basically make itself the reason why there are multiple each attack both the attacker and the defenders are getting very smart because the first time you know they wanna ability is the videotape vulnerability the second time it's not so what we are going to be doing now is that we are going to be
moving on to the next slide because i think i just talked a bit too much on what a malware is but i feel like that's an essential part to understand further down the line what review is
okay so you guys i just mentioned is a malware family and that actually has a huge family and uh i don't think my talk would have sufficient time to cover each and every variant of you but we what we need to know is that when we're discussing multiple uh attacks in ryuk you would find a pattern where the uke is being manually transferred so one thing that i would like everyone to know is that there are certain matters that are essentially provided without any focus targeting of victims so they're just basically spread around the interwebs and whoever whatever becomes victim to it it's just that however you is it targeted nowadays so ryuk is basically customized as per the
reconnaissance phase uh that has data regarding the victim so in offensive security the very first essential step is reconnaissance or gathering information about your target and when it comes to targeted malware such as you that is one of the most crucial phases because that's where you actually sit down and you think about the infrastructure and you find out ways how the infrastructure is what the infrastructure does and what essential loopholes there are that you as an attacker or in this case for you as a malware can exploit so reconnaissance is also essential because that's the very first data that you will utilize to get initial access and that's pretty much why any targeted um malware attack has essentially amazing
osim done before the actual attack or any even you know other very focused strategies for reconnaissance
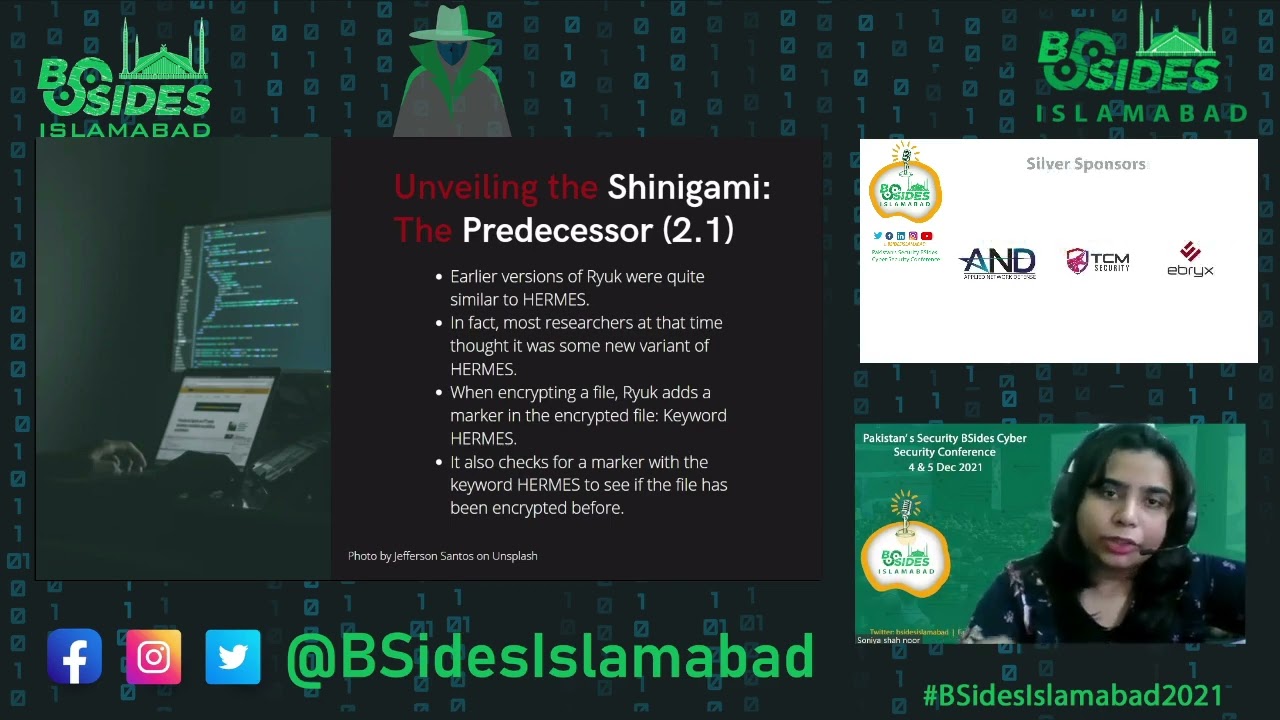
okay so we need to discuss the predecessor of ryuk and the reason for that is well you'll fi you will is eventually find out in the next slides so before you there was a georgian ransomware hermes and hermes was discovered back in 2017. now hermes essentially targeted a lot of uh you know financial institutions and the way hermes worked was that it had these uh similar patterns of initial access and then attacking phase that is why when the use attack happened in in 2018 people thought that this was some type of a variation of hermes and this is pretty much uh what they did because since they thought this was hermes they utilized the steps to stop hermes for
you but they found out that this is a completely different malware and so pretty much that's how the differentiation came into place so i would like to talk a little bit more about um the hermes by hermes malware and why you that is because they there's a similar pattern of encryption between hermes and ryuk which we will discuss in the next slide so when we are talking about encryption that is essentially one of the core features of any malware sorry ransomware because the way a ransomware essentially works is that it gets into your system it gets all of your data or any data that it has been parameterized to consider crucial it keeps it for itself and then
it improves your entire system and that's why you actually need to pay the ransomware for it because the reason you're paying ransom is not to basically get that virus out of your system you're paying ransomware to get your data out of that system and then you want to get that virus also out of the system because if the virus is still in the system you cannot retrieve your data because the virus encrypts it and it actively encrypts to make sure that even if you have some type of back-end strategy you cannot implement it because where are you going to implement it if the data that you're trying to save is already encrypted so the way
you actually encrypts a file that's a whole process and we're going to discuss that also but just a bit of similarities between hermes and view hermes used to leave a marker while encrypting and that with with a keyword of hermes ryu does the same thing so back when the radio kind of came into the whole arena of the demolishing data it kept leaving these these encryption markers called hermes and so when there were forensics that were you know reverse engineering these uh steps that you took they found hermes as the key word and they thought that okay maybe this is hermes and so they started implementing those defense mechanisms that they found were working on hermes but that's when they
found out that these are failing and that's when they came to realize that there's something else at play what exactly that is we're going to get to it so without further ado let's move to the next slide now it's a very interesting question to answer who made ryu well in the world of malware and ransomware and apts it's a lot of hush hush uh because not a lot of people like to own up to the damage they're doing because of the level of sponsors that they're getting apts again i really need to say this um a lot of times what we do not know is that when you're talking specifically about apts you're talking about a very well
organized group of attackers that are very well funded and most of the times apts are gross to their state-sponsored and they are part of cyber soldiers that are attacking countries and cyber wars and so it's a big espionage sort of a situation and to actually pinpoint who made something is quite difficult however allegedly the people behind ryu were a group called wizard spider or grim spider they are essen they're basically a russian-based cyber criminal group now do they have ties with the russian government i'm not sure neither can i comment on it however their origin were found in russia i still want to clarify something even if we have found the origin in russia there is
no evidence to support whether wizard spider is actually made up of russian nationals they could be made up of anyone and again masking that information is very easy and it's also very difficult to get that unmasked information because of the factors behind these types of groups and these types of high-level devastating cyber attacks okay so this is the fun part this is the part we're going to talk about ryuk and for everyone who's actually interested in the mayhem that this malware causes would find these slides very very interesting so how does you basically get in your system wonderful wonderful question and the answer you may think is a bit more technical there are a lot of things
going on but frankly most of the ryuk attacks that will observe were observed in that observation was found that the initial point was a phishing email or an enabled rdp node or basically remote access in phishing emails what are they again the scope of this stock might not go into depth of what phishing emails are because that's a whole new word all on its own but on a surface level definition a phishing email is is an email that has a bait and you as a victim needs to basically eat that bait in order for the attacker to get start fishing get started with fishing so i think that was a bit more complicated let me simple
just simplify it so you go to your email you find an email with the title hey you wanna cruise and you're like whoa i wanna cruise that's amazing you open the email and you have this big ass paragraph of oh this happened that happened and you do this and you did that just click on the following link and you will be allotted with your uh cruise tickets and other further details you not thinking straight click on that link and your credentials are now processed and are delivered hand delivered to the attacker which essentially you don't find out because you're so excited and the website is working and whatnot you think that in front of you it is a legitimate email
from a legitimate source and the link that's taking you to another webpage is a legitimate web page however that's all the rules and you just lost access to your email and maybe do most of your data if you're not careful what is an enabled rdp node well rdp is actually a windows protocol called remote desktop protocol and enabled rdb nodes are basically machines or computers or workstations that have this protocol enabled when you have this protocol enabled what it does is that it allows remote access to be made to your computer so if i have a desktop in my house and i'm at work and i need to access this very important file that's in my
laptop and i somehow forgot i and if this rdp protocol is enabled i can simply connect my office laptop to my home laptop get that file from it and just be you know safe for the day because why not right making life simple however the same protocol can be utilized by attackers from a reuse standpoint efficient email normally has some type of infected url or a weaponized word document i already explained what an infected url is and for a weaponized word document well if you ever work in microsoft office you're well aware of something called macros those macros can be manipulated in a way that that can trigger a download and that's exactly what happens
in the context of youth you get a weaponized word document in this phishing email and then you download that document thinking this is some important piece of document i need to read once you open the document the document triggers the malicious macro code and that initiates the download for the further steps of the pandemic at that point you might not know what's happening because macros are working on the back end of everything so you are just viewing a normal word document however the macro is actually enabling disabling or whatever it's trying to do it whatever it's programmed to do is doing just that okay so in the next slide uh the url or the recognized word document triggers the
download for a dropper malware what is a dropper malware well a dropper malware just like the name states drops some other malware think of it as a carrier or in fact think of it as a truck you have these big cargo trucks where you put some type of cargo and they have some type of you know items that they're carrying from destination a to destination b that's exactly what a drawbar malware does and in case of ryuk most common dropper malwares were either trick port or blades loader okay uh i another thing that i really want to discuss here i have my notes open right here so i might be switching back and forth between two screens please do not
mind that so the reason why you uses a dropper malware is because ryuk is essentially a manual map it's not an automatic auto automatic malware the reason why it's about manual malware in my opinion as per what i've understood through my research on this topic is that it needs certain uh steps to be covered up and it's that root as a matter cannot do those steps very well on its own so it needs some type of protection and that protection is provided through a proper malware because when you have a dropper malware you are not essentially downloading review directly because what a dropper member does is that first it enters in your system and that system
is then being uh used like that proper member is now being used as a reconnaissance staff so you have done your previous step of reconnaissance that these are the avenues i will utilize to deliver that whatever malware or attack i want to deliver the drop of malware gets inside this system and then it essentially starts looking through your system trying to understand the infrastructure is there any type of forensic um you know software enabled is there any uh filters within your os that may stop certain services to run so this the biggest that's the biggest reason for you to you to do these types of proper malware executions okay to the next slide all right
so now you have a dropper malware that enters in your system and it's again it's very very it's stealthy in a way that it makes your endpoint security wander around too much so endpoint security is your essentially your antivirus and every antivirus kind of works with signature a signature is what they use to identify if a program is malicious or not and when you have variations within the same malware the variations are coming to change the signature of the malware so that it may not be detected by a endpoint security when you have a dropper malware that is also being monitored and most of the times it's a cnc server so for example there's a cnc server called for both strike
and a dropper malware here what it would do is that it will get communication established between a command and control server to the victim's machine and when in context of football strike you have something called kabul strike beacons which are essentially payloads uh for those of you who might not know what a payload is it's base think of it as a back door so this secret back door that only you as the attacker know about and through which you're going to get out of the system and get into the system so in case of you you have a dropper malware which drops connects to the cnc server then the cnc server sends a um cnc server sends
a bacon or payload that payload gets inside your system and then it starts getting the further steps down the road so this is a virtual well visual step that i've created that you or any dropper member does the dropper member get into your system proper mirror connects to core strike weekend so it can both strike combo strikes sends a malicious payload that malicious payload starts reaching the net worth such as disabling your antivirus programs uh moving laterally in your system making sure that it's still hidden and it's not visible to your you know essential software security softwares once they have access to the main controller the domain controller the grand master of the entire internet that
is when it calls back it has a callback to the command and control server and from there the uk is downloaded onto that domain controller so that lateral movement that has been done by the very uh you know hard working dropper malware is what is essentially happening for you to start working otherwise you might not be able to work properly because a lot of variation of you have found that if you use ryuk as a standalone now where for all of this it really fails in certain steps and it's not really good at hiding in certain steps at least in these very initial steps of the execution or the exploitation of your system okay so
yeah okay one more thing i would like to discuss before we go further is uh we discussed in the previous slides that the most common malwares for you uh dropper malware for you are trick bot and load bracer a very defining feature of trigbot is that it can it the trickbot and hermes both they can detect virtual environments especially especially hermes hermes can very easily know if the victim's machine is a vm or not and there are certain variations of trigbot that can do just that as well now why knowing this would be very important for an attacker this is just a little bit of virtualization or hypervisor 101 but when we are talking about virtual
machines most people are aware are might not be aware of may be aware that there are two types of fertilization so two type of hypervisors there are type 1 hypervisors which are bare metal hypervisors which means that the virtualization software aka your hypervisor is directly installed on the physical system the other type of hypervisor which is type 2 hypervisor that is a type of hypervisor where this hypervisor software is installed on your os a very common example for the type to hypervisor is personal box or vmware workstation whereas for type 1 we have hyper-v microsoft hyper-v the other one is vmware's exi so when you are in a virtual environment your lateral movement really depends on
your infrastructure for example for type one hypervisor uh the security and performance of that hypervisor is very very very good so there are certain aspects that the dropper member may not be able to handle or may not be able to detect as quickly as it needs to and for the type 2 hypervisor again because it's being hosted on a host os its lateral movement will change as well so knowing the virtual environment if there is any is very very important for well technically any type of attack including redux attack okay again we discussed just that that there is a dropper malware we carry that out and then it does what it needs to do and
you get to the domain controller and that's where you have a holistic idea of the entire network so the reason why lateral movement in any type of attack is done is because you really need to make sure that you are at a place where you can view the entire network otherwise your attack might be stopped in in the initial stages some network infrastructures are developed where you have isolation zones or where you have honey pots involved where the attacker may think that they are utilizing or attacking a very crucial piece of service but they are just stuck in a honeypot and so this gives defenders enough time to isolate systems and make sure that everything is intact and the
attacker can just can easily be removed like you as a cert people might have done such even over tumor it's a difficult thing to remember tumor so is it is to remove a very pesky little maori okay so to the next slide this is again we are discussing about trigbot emote hermes uh all of these softwares are there they can detect vm environments they can also detect sandboxing environment which is very very interesting uh because emote again is a type of dropper malware especially in the context of youth it has been used a lot of times to drop to you in certain attacks especially there were two attacks that were done where we have seen emote being the top
of nowhere and those two attacks had victims that were belonging to united uh states of america's government departments so sandboxing if anyone has done programming they know exactly what it is for people who haven't uh don't worry i would just tell you what it is so sandboxing sorry ahead sandbox and environments are used to test some type of software it's also used to uh test uh malicious code and sandboxing environments are there for malware analysis we have a sandboxing environment and we put a software a malicious code in there and we try to execute it then we see what it does and because it's in a sandboxing environment it will not really harm our actual data
so that's what 10 boxing is and for the dropper malware remote if it detects that there is a sandboxing environment it lays dormant it doesn't do anything it just lays dormant and it communicates that back or basically it doesn't really necessarily communicate anything because if it lays dormant and there's no communication the command and controls our nose to move to the next node or to try a different initial access point because this access point will not work anyways again we are going to be finishing up this section of the slide a little faster because i only have 15 minutes and i have a lot to talk about so in case of any type of proper malware
the reason we are using this is because if there is a point where there is a halt for the execution these proper malwares by the attackers enough time to get out of the system without leaving the trace because during an active attack there are chances to reverse engineer it and get back to the origin including where the attack initiated from so with dropper malwares you have enough time to safely get out of the attack without getting detected okay now let's see what ryuk is actually doing
okay once you is inside your system the very very first thing it does it it stops uh sorry it starts anti-de-assembly and anti-debugging okay what is that what does these thing these words mean so what it does essentially when you say ntd assembling and anti-debugging you you're trying to stop certain services that can detect abnormal behavior most of the times these services are being done by your os okay and the way ryuk stops it is by manipulating windows api what is windows api well windows apis are user written programs that interact with your windows os this is where all your endpoint security is talking to your windows os so basically endpoint security software has an api which is a windows api
it tells the windows what to do and what not to do if xyz is happening and that is why you might have noticed if you have an antivirus installed and you go to a malicious website or if there's a malicious program you're trying to install there's a halt signal from the antivirus that's saying please stop don't do it and the reason why it's all doing it is because it's talking to the windows and then the windows is stopping that service from happening what does ryuk do ryuk goes into your windows api starts manipulating and starts telling windows api to do things that will allow its existence and further process to be done more sequentially without any interruption
right okay so ryu copies itself three times so the first time it copies itself uh three times in the current directory directory all the all of these three copies have different names and different tasks area so the first copy triggers a command line that is responsible for the self replication of each file again there's one file that will be replicated and will be with the attacker the other file will be encrypted the second and third copy triggers a command line that is responsible for sending a wake online packet to other nodes on the network what is wake online well it is a industry level protocol used to get computers to wake up in a low power state so once you are on the
domain controller from there you can actually send this particular packet to every computer on your network right so that is why you need to get to the domain controller to get all of these things done okay before it starts encryption it first kills a list of services and processes again these services and processes mostly are done for security reasons and the termination of these processes will help you to do what it's required to do without any destruction and any botheration so the known uh processes and services the number of the their actual you know type of processes that are stopped [Music]