How to Start a Cyber War: Lessons from Brussels – EU Cyber Warfare Exercises

Show original YouTube description
Show transcript [en]
with that let's get started please help me welcome Chris go Becca alright hello welcome everyone everyone came here stays in my ear it doesn't get well dropped off so welcome to how to start a cyberwar lessons from the European Union and this talk is actually about last year's cyber warfare exercises involving the European Union and NATO that I helped lead in Brussels just a brief introduction there's lots of words basically I can leave to watch the world burn a little bit and have a fun doing so and somewhat responsible way now you might want ask a question why the topic of cyber war and why it's so important to do some of these different types of
exercises now in Europe you may not be aware but we've already had one very major cyber warfare event that happened in 2007 in the country of Estonia now at the time what Sonia was a NATO member which I like to point out and now NATO had set up their cyber center of excellence in Estonia as a show of force basically what had happened there was an old Soviet soldier monument that was being moved in Estonia and suddenly there was a massive ddos attack which tried to shut down the country of Estonia in 2007 launched by supposedly patriotic Russian hackers and Georgia also suffered major cyber warfare events as Russian troops were moving into parts of Georgia South Korea North Korea just
doesn't like them but we'll see what happens in the long run we had a sex net issue with your and that involved critical infrastructure and nuclear enrichment facilities Saudi Aramco this is one of my favorite pictures these are miles and miles of gasoline trucks and what had happened was they were the victim of a cyber warfare attack by the Iranians and the Iranians were able to shut down basically all of the IT infrastructure for the valuable company now who thinks that Apple is the world towards valuable company yeah it doesn't compare so Saudi Aramco is worth about 18 to 20 trillion dollars and that's almost 10 times the GDP of India after that they've been having ongoing attacks they
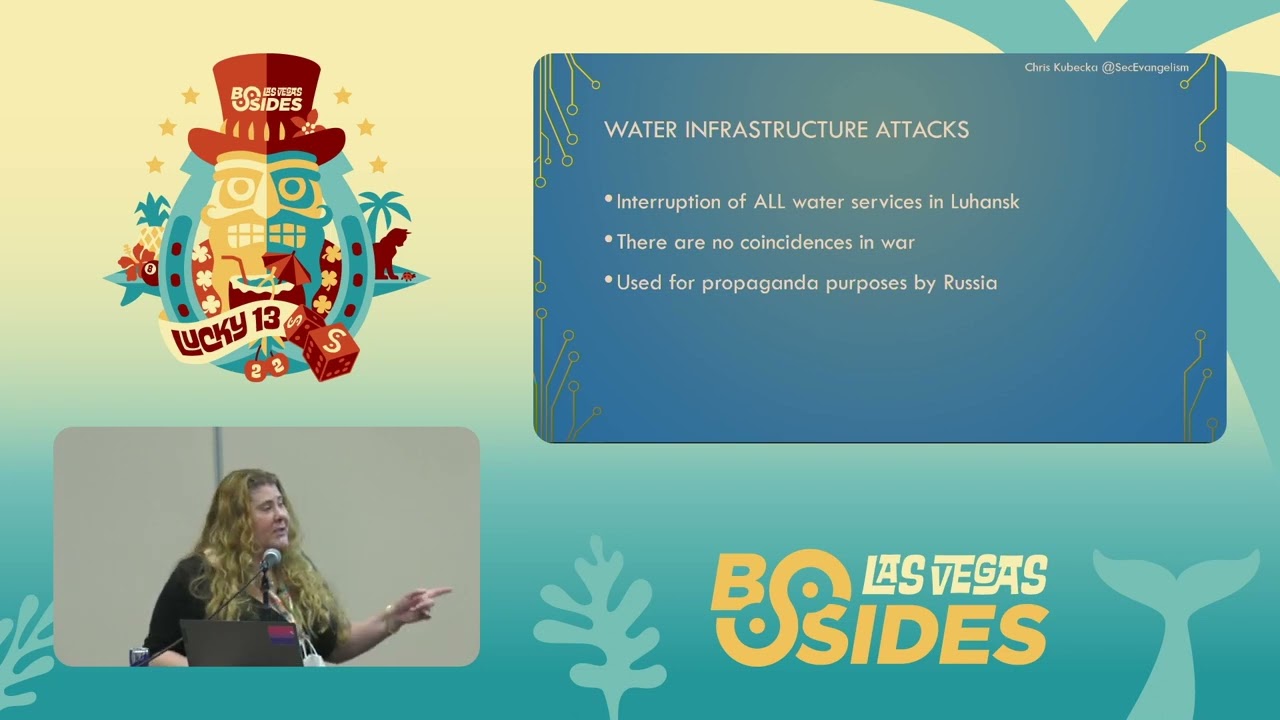
were not able to fuel the country after 13 days her strategic supply was gone so if you called an ambulance you might not get it the supply chain was broken and then we have from 2012 to still ongoing attacks occurring in the Ukraine and especially in pre Crimea about six months before there were any supposed maybe Russian boots on the ground there was an attack that occurred only in a Crimea region attacking Smart TVs forcing the channel to be changed to propaganda television in rebel TV as staging it for positive support before any boots are on the ground and many different types of attacks are ongoing so we've got a lot of challenges in the
European Union and for NATO one of them definitely is Russia and what's been going on with Russia the relationship with the United States itself has been an extreme challenge let's say the least China they have a completely different set of ethics and rules when it comes to testing breaking or doing whatever or say leaking or taking data we'll just say that we've got the rise of popular ISM and politics all throughout the European Union which could be a good thing probably not if you look back at history from the last century it probably won't be a good thing so we're seeing immigration amongst the Member States and also external immigration as a big problem trying to integrate we
don't all talk the same language you don't all have the same system but we're supposed to be sort of like a federation of countries inside our European Union and it's Challenge it's a huge challenge and then we also have foreign and internal interference because not everybody is actually best friends best buds in European Union right and they also have various relationships with say China or Russia especially if you're talking about countries like Bulgaria they've got a completely different relationship than say the United Kingdom so last year we had this great idea thanks to the European Council on Foreign Relations they ran a series of exercises in Brussels and wanted to really shape some things up and use realistic scenarios so
we went ahead and worked on some very very interesting stuff and I hope you'll enjoy we had a bunch of ministers people like what would be the equivalent of the secretary of state of the United States were there we had ambassadors think-tank people all sorts of different types of people mainly people who would make decisions in case of an actual war or who would assist with expert advisement were present so to get them warmed up I led the exercises by just showing them some pretty pictures because diplomats need a lot of pictures and not a lot of words there's some of the things I showed them on this list this is a power plant that is infected by romona
accessed region the same route accessed region was also on this salmon farm and also on a bank called ABM Bank which was government funded from the Netherlands all three cases that I showed the diplomats they were controlled by the same entity behind bimple ISP and Russia same exact remote access Trojan as well and then I also like to have fun with things how to find legal and illegal grow operations if you have a grow tent and it's connected to the Internet that's all I'm saying so a toolkit was built for these ministers and diplomats because this is kind of a new area to consider we have already played books what happens if somebody invades your country
but we don't really have a huge amount of playbooks for what happens if somebody gets into your hospital infrastructure or makes a mistake while they're testing in the Netherlands it was the first country ever that legalized the ability to hack back into any device anywhere in the world by the Dutch police so if they just suspect you of something or me they could actually hit your phone here today great right they also have a weird quirk in the law if you're caught hacking for the good of humanity it's not illegal and not everybody is a nuclear power in Europe and one particular country I can't say which is but will not admit it so there's a whole big mix of people in
their capacity for appropriate response depending on what is occurring so we had three main scenarios to warm them up all the way to the main one clean slate well it's a very interesting one little man involved some hacking back into intelligence agencies and back to the earth and dead canary the big one the funnest one I like it because mass casualties across various nations inside the EU so we talked about clean slate we tried to put a spin on it and do it in a different way for an insider threat so the scenario was there was an embassy employee who was having mental health issues and he began taking documents from the embassy that were classified
highly classified and hoarding them in his house and he began hoarding and what happened was he had had an adult daughter in a scenario who happened to belong to a particular forum for karma was posting some of these documents someone from 4chan picked up that they were classified and disseminated them further and obviously once it's on the Internet it's not coming off the internet I think we all know that by now right and it was a very different way of looking at it on top of which the laptop that she was using was in turn infected with the rat not by an Intelligence Agency but just a regular cybercrime and they also got a copy of all of the
classified documents that hadn't been uploaded yet so I also wrote a note another reason why I did not have children so Oh little man is uh interesting as well there is a security researcher who was trying to responsibly disclose a critical major vulnerability with proof of concept exploit code already testing and the security researcher runs into problems and this is a problem within the European Union responsible disclosure not all of the cert teams actually have the capability to deal with them correctly so then the researcher gets a group of researchers to try to put pressure on that particular government to accept this because it's a major issue in the meantime unfortunately the way that they
were trying to responsibly disclose they did not encrypt the information so there was an intelligence agency that was listening in and found hey you didn't encrypt that email that you were telling me here's the vulnerability here's how you can get it and here's some proof of code concept code and so they were able to surveil figure out and get the information without doing any work and in between they found that at the time there was Shadow Broker subscriptions and they were also had to make the decision if they would purchase a subscription and they were given information that several other countries had already purchased subscriptions and the whole idea is what do you do if a
country's have access to this and our subscribers and are not very friendly to you and I have attacked you before should you also buy the subscription so that you're on equal footing but then again is it actually legal to do so alright what would happen if the press found out on top of which the exploit code and some of the Shadow Broker stuff was used against a particular Intelligence Agency a different one and data was stolen in the meantime the scenario because there's only one country that is allowed to head back the Dutch mistakenly in the scenario hacked a foreign governments hospital system and had to figure out how to notify them before they found out
and cool it down and figure out how to talk to diplomats and all sorts of things so that perhaps the ambassador of that country wouldn't be kicked out after it was found out that the Dutch mistakenly hit a foreign country oops now my favorite one because involves violence is dead canary and what we did was we made it so that was a bit similar to the Shamoon attacks so we staged a pastebin saying you're going to be taken out with a bunch of different threats at a particular time or place and we're going to destroy your systems and what happened was it was staged and timed multiple attacks on different countries and they hit the various areas so the
telecom government websites banking stock exchanges all the way down to London Underground during rush hour so we start and the evening and it starts with one particular country basically getting ddosed in a similar manner as Estonia did in 2007 the next morning ICS systems the SCADA systems are attacked in a shipping lane a water shipping lane which causes a murska cargo ship to capsize by killing or missing all of the sailors on board another country is hit with the nationwide electricity blackout and also transformers are taken out and there are mass transformer fires at the same time they telecommunications systems have already been affected so it's very hard to respond transformers can take up to 18 months to build we're
talking about a country where there are widespread transformer fires 8:45 in the morning London Underground someone gets into these signalling and is able to manipulate the signalling system shut off the auto shutdown systems and all the rest of the safety systems and is able to collide trains in the London Underground during rush hour causing mass casualties National Stock Exchange of another country is manipulated and crashed bringing down their entire financial infrastructure no more stocks are traded the next day I will briefly say a summary Good Morning America we have been made aware that five European Union countries our allies have come under attack and there are mass casualties but when I visited the European Union and spoke to my allies I
warned them I heeded them and I told them that they needed to meet they're spending two percent of the GDP but they did not heed my warning now it's the time for Europe to stand on its own two feet American blood will not be spilled we have put up our digital defence wall and it's the biggest defense wall thing in let me see oh and good night and good bless and God bless america so what happened was we had already anticipated that the united states would not assist in the case of a new ally or NATO ally coming under massive attack why this is important is the first and last time that article 5 of NATO was used with
during the 9/11 attacks and the allies I gave a lot of additional help a lot of ships intelligent supports and so forth and the current situation with European Union right now we're basically surrounded by a ring of fire we have a very terse and difficult relationship with the United States on one side and we've got Russia on the other that's putting a huge amount of pressure there has also been election manipulation inside the European Union specifically France last year and there's also been manipulation in Bulgaria when they had their vote the same time frame I actually went to Bulgaria the weekend before I was at open fest and I showed them in Sofia Bulgaria how to do ascent
on the hardliner that was running in Bulgaria that was very pro-russian so they could find out as much information about him as possible before they went out and voted because I like to do that so it's rather important to think what would happen if some of our allies came under attack in that manner what would you do so it leaves us in a very odd situation now we're dealing with a lot of different countries at this event not everyone's friends not everyone likes each other some do some don't some have different relationships how many of you have experienced decision-makers that cannot make a decision yes yes yeah everybody right so some of the lessons that we learned were there were people
who could not make a decision there are people that did make a decision there was one particular country cannot mention it on every single scenario she just kept saying sanctions sanctions sanctions and I'm like okay all right I get to you let me guess sanctions yes sanctions they could not always decide together right so we then had to do it by table and then switch the people to try to improve that relationship because it was difficult to make a decision if any and it really was and this should be worrisome most of the teams could not come to a consensus in the scenario and another thing was many of the countries were not prepared and that was
one of the things we were trying to drill into them it really is not if it will be win because we've already experienced issues and we will continue to experience issues so with the United States now the night before we did dead canary I love that snare he's my favorite we made a bet amongst the staff to see if anybody could get our teams to agree to consider the nuclear option I won I was able to get my team to consider the use of a nuclear weapon as an EMP device to take out the foreign entity I'm fun at parties so I wanted to give a u.s. audience a little bit of a taste of what we've been experienced in
the European Union and the EU NATO members and the things that we're prepared for the things that we expect so big conclusion we don't have solid definitions of what cyber warfare is yet not all countries agree to it not every country has specific cyber laws like Albania small country packing back sounds cold but what if you get the rolling target and you caused a major international incident because it's pretty easy to mix up an IP address I think we've all done that or had friends who did something like that and another thing I want to stress is public disclosure is very dangerous the reason being is if you hear in the news that someone has
disclosed an intelligence tool and a scenario or it sees me in real life that means that all of the money that they put into developing that tool they have now thrown away because I can't use that tool or the tool and technique combination again because now someone else will know about it that really likes each other and right now if we can't get a definition we believe that the diplomatic route is probably the best before they listen to me about using an EMP device okay so that's what we wanted to really get them ready for so now I am ready for questions and I want to thank you very much for attending my top so who has
questions I fit in here one here one there yep no wait this is more of a comment just on the hacking back as some of us know attribution is hard and you know I'd be a great way to say oh you know let's make these people at Target make it look like it came from them well that was one of the big decision factors because how do you actually prove the whole attribution before you start to declare war and we're talking about a war scenario and if somebody causes mass casualties through cyber attacks in your country that is war but how do you prove it you had a question you might want to kind of keep your your hands a little
raised so that I can get them this one back there lieutenant Wooten Luke don't mouton oh nice okay what level were you simulating these events like how did you actually do the scenario well pre-staged I don't know if this one has any in it different types of news items and then intelligence reports and then updates on top of which we would have headlines and then I also showed real cases on top of it and each one of them were able to talk to me as well to ask the questions and they were also given a glossary because not everybody knows all these terms especially diplomats or ministers and so we also talked them through the
entire thing so we use visual but obviously not physical well yeah then work out very well all right so we had another yes I'm considering traditional Warfare's got quite strict definitions of code of conduct juice foresee that we need something similar for this new theater of warfare and how long do you think it would take for that to well actually it's been referred to as the digital Geneva Convention and that is something that's been discussed last year it was the ung ge team I believe it was I was trying to negotiate that in the United Nations unfortunately one particular country decided to just so there was actually no consensus but they got extremely close they got 7 out of 8
so they're gonna try again we'll see but it's already being discussed things like you cannot test in a hospital or medical areas or electrical or telecommunications certain things like that carry different types of weights because they do in real life next question got one here hi do you have any thoughts on the potentialities are false black operations in cyber war oh absolutely I mean these types of things occur as part of whatever strategy the country happens to have and they've occurred in the past they will continue to occur absolutely I think that they occur on a fairly regular basis as well depending on the country
over there participants in this game are professionals yes so they were the ministers of Defense okay ambassador of Minister of War so I have a question for I was participating in a similar exercise here in the USA in Washington DC we were simulating the escalation of conflict in the Middle East and surprisingly so I'm I see I see a security professional I mean I'm security professionals so I'm not really in these political sciences or politics in general but what's interesting that so you mentioned this situation that people could not meet decisions so like for example and my simulation game people are just like simply ordering assassinate assassinations did you have the same situation yes and surprisingly
basic how many how many simple decision was always assassination yeah yeah yeah you had a tougher crowd so kind of long those lines yes yes yes so kind of so you mentioned that your group was the only one that kind of went for the nuclear option yes what was the kind of average response that most of the other groups or tables had kind of the average response was rebuking removal of diplomats public shaming there was also few teens a couple of teams that shows hiring hackers from their own country as patriotic hackers who a hack back as a response for the country's war was not legal to packback assassination sanctions things of that nature but yes
as someone that would it would be someone that would basically make a statement right I'll refer to it's a nuclear physicist in Iran keep getting shot up and killed by two men on motorcycles and so that's pretty regular and I think it happened with maybe about once every month two months that's so I'm just saying the US was fairly well isolated from or the American public is fairly well isolated from feeling the effects of military action but when we're talking about cyberattacks that might be one where a lot of Americans might be able to feel that firsthand you show that line of gas trucks in Saudi Arabia absolutely do you think what do you think the impact of that would be on
driving US policy to engage in cyber attacks and being sort of a customed to having those impacts felt here domestically well luckily the United States was the first country that established a computer emergency response team associated with Carnegie Mellon in Pittsburgh Pennsylvania and they've actually been charting these things for over 20 years for instance there has been a 390 percent rise in attacks against water infrastructure inside of the United States in the last six years so they've already been planning for things obviously not everything's perfect but they're constantly planning constantly doing and there's also one major difference the national level cert here in the United States is actually rather proactive so they will try to proactively scan
critical infrastructure and tell you hey you've got something real weak all right I've gotten those calls and they're not great calls but the EU cert does not do that that is not their role so they leave that up to individual countries so again I like Albania but they do not have a mature search so they cannot react or do something proactively so what happens if they are the weak point in the system to penetrate into our European Union Network and so these are concerns that we have and I brought up because we need to address them any other question I got one oh yes finally luckily what do you think about active measures perception management campaigns
yep absolutely absolutely yes when I when I first heard about Aramco I proposed a spear phishing attack but using one of the executives and I allowed our managing director to pick the executive and that person was only given the information and it made them extremely aware of how very high-value targets whales we like to call them can be vulnerable and can bring that Molnar ability into our company and we did not want what happened in 2012 which could have raised gasoline prices up to one four hundred and fifty dollars per barrel if Aramco had been shut down they supply 25 percent of the world energy one way or another and Qatar was also affected at the same time with a variant of the
virus they supply about 14 percent so that's reason so I think I still have time I don't thank you thank you for a good talk really interesting I was interesting knowing what the general level of preparedness well to put in participants did any of them had any strategy somehow deal with the situation some do absolutely so some of the countries I do not a Kingdom or the Netherlands Germany France and so forth they've got much more mature models much more mature strategy and military as well and they also have the legislation available to them other countries do not have those capabilities and that's one of the things that was highlighted a key highlight of why we need to work
together more because if one Falls the rest can fall so some came in at very high level some what's a computer right I don't use one of those I just use the you know government-issued whatever the phone I don't touch that side so yeah it was a big MIT question hi I guess it to I guess two questions one is what sort of time constraints were they working on and how did they handle it and then the second question is more around you talked about the lessons learned so some you know things are about like lack of preparedness things like that or the ability to collaborate what are the next steps for that and sort of talk about
that great thanks okay so so at the second part basically they had one full day to go over Cenarion one in Scenario tomb and then scenario three was an entire full day so we're very lucky to actually get them for you know both days there were obviously some time constraints because on day one we had my presentation to basically warm them up and introduce and then some network II you know niche in pieces but the time constraints are actually pretty good they worked pretty well with it which I was surprised I really was the second part yes so what is coming out of this is better legislation because not all the countries actually have cyber
legislation also there is jurisdictional issues so if an attack comes from one country hop-hop-hop through various other countries but trace back to try to prove attribution not you don't cooperate yet completely within Europe so they've now brought that to the European Union Parliament I think actually next week or the week after they're going to be discussing it too put up for a vote to deal with the jurisdictional things because you need that attribution because you really don't want to launch that rocket if you can't prove it because that would be a bad thing so those are the things that are coming out of it as well as there has been discussions to include preparation and training and part of the
2% GDP spending requirements for a member of NATO to include that to then ramp up preparation that's what we discussed at a NATO medium a so that's what's coming out of all of this and it's a good thing because there's funding available so I'm actually quite positive there any other question all right well thanks everyone [Applause]