Mike Carlson: Becoming more intimate with Exploit Kits
Show transcript [en]
my name is mike carlson uh i'm a originally a petroleum engineer when the downturn occurred in the oil and gas industry i went back to school and took information system security at state and i've been working on emails mostly here for the last couple of years as well as some network access control and [Music] a av and one of the things that i've discovered in this process is uh understanding exploit kits is really important for filtering email so i'll get into it here the outline of what i'm going to talk about here is fishing's actually really important it's a major component according to sans and over 90 of breaches uh and when we're looking at
defending we actually only have to break one of those links in order to be successful so one of the things we need to do is understand how an exploit kit works and the exploit kits have been designed basically for the benefit of the hackers they're actually trying to hurt us and i'll give you a little bit about history and then talk a little bit about the tricky part in security which is the techniques tactics and processes uh and the way i've got a nice little picture there of david bianco's pyramid of pain i believe he called it the first thing to understand about an exploit kick is very flexible so you could have a variety of
different ways in which you can access this one of these is somebody goes to a website and then they click on a malicious advertisement link and it sends you to what people call a landing server now there's other ways that you can do this as well you could go to a compromise site directly and it actually automatically takes you to a landing server and then finally and this is where the email comes in with the little yellow arrow there you click on a link inside an email takes you to a landing server now this landing server is an intermediate step after that you end up with what's called the exploit server kit and it actually downloads the malware
and that can take a variety of forms and this is another form of flexibility here it could be ransomware could be a breaking trojan which is very common it could be malware and typically when we're talking about malware we're usually talking about a remote access trojan and it usually leads to some command and control activity so here's where things get a little bit more complex and you'll notice that i've used a series of different diagrams here and that's not really intended to cause confusion although it might a little bit the key thing here is is that there's a not with all this flexibility in all these different exploit kits people have different ways of explaining
what's going on and then also there are also different ways that the exploit kits runs so they're not all exactly the same so once again we see our victim here he goes to a bad malicious website and then it directs somebody else onto uh directs him onto somewhere else and then you'll notice that there's a little zigzag in here and very often this is done for three or four different servers before you finally get to the exploit server and then you can see in this one they've also separated the function of delivering the malware so what does this allow people to do well usually what happens say you get a link from constant contact it's a reputable
company rather than going to that website and going to your website directly it sends you to another website that directs you to another website that sends you to another website that directs you to another website and what they're allowing themselves to do here is if one of their compromised websites which is you know hosting one of the malware servers or exploit servers gets compromised or in other words taken down they can actually zigzag their way through a variety of these things and then finally get you to an exploit server even if some of these sites get taken down if constant contact checks the first redirector and says all right this looks like a legitimate site i don't see any
malware on there it has the redirector on there and so to actually find the malicious website you have to go down three or four layers so this allows you a certain amount of protection and not being caught right up at the front end virustotal won't have all of these different wire website servers on here and it allows you to get to the exploit server or for the hacker that is without actually having any problems there so one of the things that we want to take a look at here is we talked about oops sorry we have this landing server in this landing server we have some decisions that are made on which page gets loaded down
so this is actually from one of the publications of the government in the uk it's the cert uk and what they do here is they take a look is there any av detection on this uh computer can we find it do we know what the os detection is and most browsers will actually serve up that information maybe it's not a target that we're really interested say we're targeting utilities in canada or airlines in canada well it'll say oh look this is actually somebody working in a retail store it's coming from a university what they do then is they send it to a non-malicious web page and what they're trying to do here is they don't want to have somebody
download their malware for something that's not of interest to them and then only to have somebody come along and say hey yeah you know i got undownloaded some malware here and then have somebody sandbox it figure out what it does now here's another really important step it takes a look at the browser can this browser be exploited so in classic terms uh internet explorer had a the microsoft product had a reputation for being full of security holes if that was the case versus say maybe a chromium and there are browser exploits for chromium as well what happens then is it says all right i found a target that i have an exploit for then it takes that exploit and the
exploit may not be directly in the browser itself it might actually be in one of the plugins and then finally here you go do nothing or redirect to a fake page and i think in a lot of cases here that fake page actually turns out to be a credential theft and one of the big advantages of an exploit kit is you always have an exit something that really works so this second star on the page before which is this one here is the origin of what people call the drive-by download if you have the right browser or the right plugin and they have available to them the right exploit and most of these were originally associated with javascript
and or flash player the malware can be downloaded without the user having to click now most of these exploits have now been cleaned up in the last few years however this doesn't mean that uh that's the end of it and i think one of the things that's also important about exploit kits is for the most part what they are serving up is usually not a zero day exploit usually and this is from a number of papers on this you find that the exploits that are actually being used are actually well known and you can see they've got cve numbers some of these are for 2015 which is five years ago some of these go further back some of
the more recent ones aren't included in this paper because it's not super recent but you can see here java is used flash is used the internet explorer itself pdf documents can be used and then adobe flash was immensely popular and actually i think it's it's at the point now where there are relatively few versions of adobe flash that are still operating people have taken those off their systems because they've um this has sort of been the death knell of adobe flash until they come up with something that's substantially more secure you can see that the microsoft silverlight here this is the microsoft server as well that has vulnerabilities in it as well so there's more to an exploit kit yet
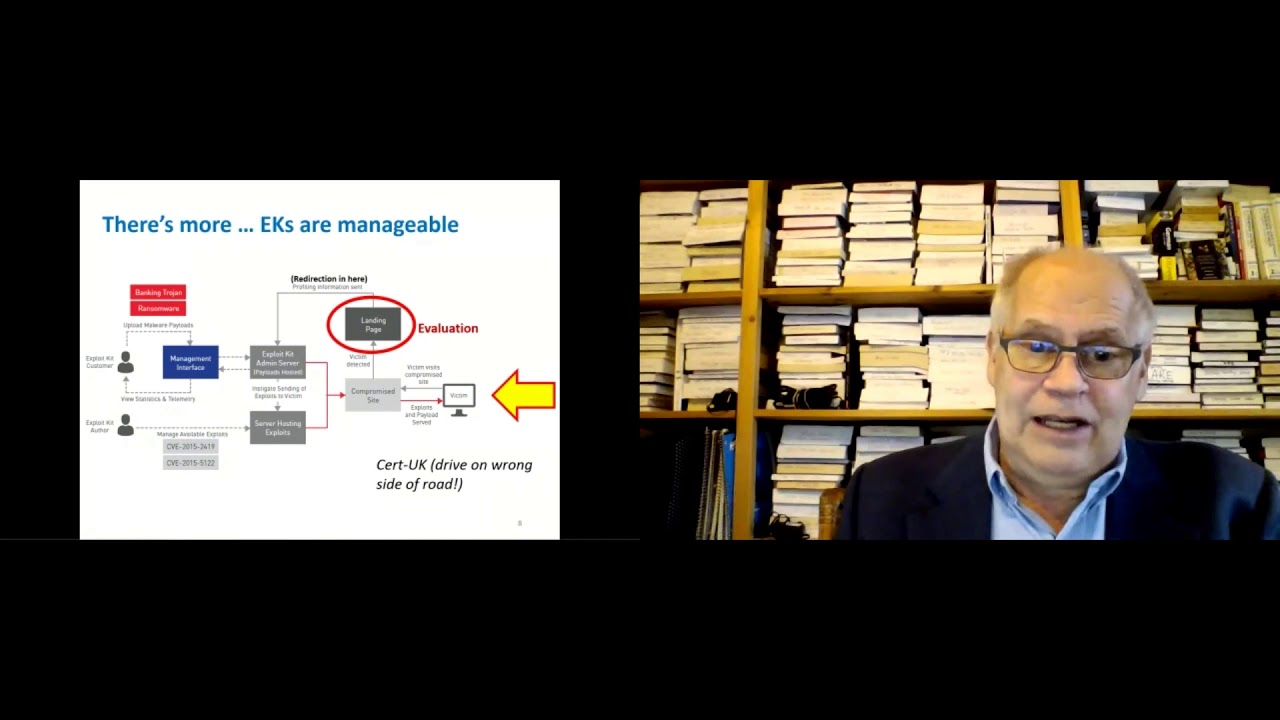
again and the key point here is they're manageable once again here this is from the cert uk this diagram somewhat confusingly starts on the other side of the page i do note that in the uk they drive on the wrong side of the road but we start with our victim here the victim goes to the compromise site gets redirected to a landing page and then you'll see that in here you can see that there's somebody over here on the left height left hand side that's the exploit kit customer he's looking at a management interface can see the exploit kick and he can see as these different exploits are being downloaded and then at the bottom here on the left
hand side again here you can see we've got the reference to two cbes both from 2015 in this case the exploit kid author so now we have a somewhat more complicated situation than just some you know kids you know working in this basement as a quote script kitty we actually have separate players in here and this has actually become a business now and you can see here they've picked banking trojans and ransomwares this evaluation stage once again is very important you can see in this particular case they're only referring to two cves but you know there are more exploits available and this is one of the things that the author will offer is a variety of
different exploits and then the person who buys this thing the exploit kid customer can pick and choose which one of these exploits that he wants to use and there's some of course option or opportunity to figure out what the profile of your customer is say you're working with an oil company in calgary the vast majority of oil companies in calgary the people that are working in there are working on the microsoft environment they're probably not serving up linux exploits they may have some mac exploits and in fact if they're dealing with executives the high proportion of executives and some of the companies i've worked with happen to like maps so here we are we have a cast of
characters now in this particular case i've got a new diagram here somebody sends a spam email our victim goes there and clicks on the link goes to the landing page ends up with an exploit kit being downloaded you can see the customer is in there as well and then you can see that this one here they've got a third character here that i've shown with number four and this person is the kit admin and he's the person that's busy loading these exploits up on various servers so what does that look like
[Music] sorry
so one day in the process of doing a sandbox i came across this funny looking page and you'll notice on here in the left hand side it says infect and what this is is it's a management page for reloading up your exploit kit onto the server and in actual fact the way this works is when they compromise one of these servers and they get into it most commonly it's a wordpress server but you know there's other opportunities as well they install their own web page on that compromise server usually under some other directory so that nobody notices and they have an automated system that does this usually it's uploaded in a zip file and if you'll see a little bit
later in the conversation here when we're talking about this that uh you can sometimes find these zip files or they leave them behind when the website's compromised if you're ever in the position of actually having to clean one of these things up certainly would be nice if somebody kept a copy of these things so that they can be used um or analyzed later on so there's a couple of other things that these exploit kits often have in them and that is you'll find that they now have captchas in them and what they're trying to do here is to stop automated uh processing you talk to your local microsoft salesman he'll tell you about all of the wonderful things that apt
does and that it does an automatic quote detonation which is another word for running a sandbox however if you put one of these captchas in here you'll never get to the point where you download any payload unless you can get past the captcha and i've picked one of the ones here that i happen to like because it's a little bit more unusual it's not the usual picture of a fire hydrant or a crosswalk or a bridge you can see that what they've done is they put in these little random lines in here i call them squiggles and those things help people prevent uh ai from being used on the captchas one of the important implications of
this is that when you're out there trying to decide on which sandbox kit you should use one of the things that could be very important is the ability to do manual input and that's also one of the major limitations of code automatic detonation sounds wonderful but it doesn't necessarily get you to the end which is seeing what the payload is that they're downloading um okay let's move on here oh i know yep so we talked about the kit admin at number four here let's go take a little bit of a look here at our customer at number five so number five here is our customer here he's sitting in there he's hired the kit developer
he gets this package and he too gets a management console so while he's actively running his network of malicious web pages he'll get this kit that shows and it comes this one here is called black hole and actually this is an interesting case as well black hole was little four or five years old it was extremely successful and uh the reason they were able to get this entire kit was somebody actually managed to purchase one as a lab researcher and got the whole kit and there's a really good write-up by dell and you can see exactly how this whole thing works when you look at that so let's get into some of the details here because some of
these details are important so i like this diagram because it's got the victim in here and what happens to him we've got a little bit here about what happens on the websites they visit he goes and visits compromised website he gets redirected to this other website in here this website sends them to a dns server and then you'll see that there's a name server in here that goes on from the primary dns server to the secondary dns server and that they used a lot of dga which is domain generated algorithms are and it creates basically a random number so that you know it's very hard to track these websites it's important it's not on the primary
dns server because that's public and people can follow that it basically goes to a private web server or dns server here and that allows them to redirect you to another website that's very temporary it may be only up for one use and then it sends you back to the landing page you get the x white kit the exploit kit in this case here is shown with the flash when that flash is sent back and forth here it gets obfuscated by using a packer and it not only encrypts it but actually also makes the executable smaller so that it takes up less web web bandwidth then the exploitation gets run the exploitation kit actually downloads malware and then that comes back as
the second event in here and then this is where as such something such as a remote access trojan or ransomware would get installed and then you can see here in this case they've demonstrated this with a malware cnc so this is a very common feature where they use the generated names it's not absolutely necessary a necessity there's a little bit of a page in here that outlines how the dns works it goes to a primary dns server then you can go to a secondary and then you can go to a tertiary dns server and in many cases they will use more than one dns server so that you know nobody can come back later on
and track down the ip for where these things actually occurred so in trying to understand these exploit kits one of the other things we need to do is we need to understand something about the browser now it's actually quite difficult to find information on browsers i have a paper here gross kirth and godfrey this is a group of people that work at the university of waterloo and what they've done there is they've made up a generic and the reason it's so hard to find is many of the briars are proprietary now i'm thinking specifically of something like internet explorer or chromium here in the case of firefox that's actually a public domain thing and it's mozilla
but you'll notice that the way the html documents work are set up they have slightly different terminology although they work functionally more or less the same if you look at a web page in chrome or firefox or in safari they'll always be subtle differences in the layout and that's because the people when they design these things set them up slightly differently so this may be not directly important to what you're doing here but you have to make sure that the sandbox you have has the right browser in there uh you also helps to understand these things so that when you set your sandbox up you want to make sure that you match what's in your actual
production environment so once again going to the nuts and bolts details again here when i talk about eight and nine and the fact that the transfers are obfuscated with encryption and compression this means that if you were to say take a look at this from a network traffic point of view you would not be able to see entirely what's happening here as it's coming into your system so then we can talk a little bit about uh eight nine is where the payload gets delivered and if we look at this as well we can see that there are papers that outline how the obfuscators and packers have been set up and you'll see this is for an exploit
kit that was or two of them actually the nuclear exploit kit and the rig exploit kit and you can see that they change these packers around as time goes by so this is helpful for identifying which of the exploit kits is being used and then maybe more importantly here i've switched to another one here now this is uh the nuclear exploit kit and they've looked at a specific period do any during 2014 you can see that they've got these little hash numbers in here and what's happened is they've changed the key and they've changed the style of the packer and obfuscator and then also as time goes by they also change the payloads so and then on top of that you can have
the same exploit kit with different payloads depending on what it is you want so why did people go to all this bother in here and where would you find out all of this information and the truth is that in exploit kits it can be quite difficult i've got a picture here this is off the cover of the no starch guidra handbook and you know when you take one of these things apart you get into doing disassembly in here of assembly language and when that happens you end up with a very complex flowchart this is specialized very time consuming difficult to obtain as i showed from the previous slide it changes relatively frequently and very often unless you get to the
point where you're fairly far down in the process where you actually got the download to occur and the exploit to be installed you won't necessarily see any of these things because unless you have the exact right exploit it won't actually do anything so i have a little list here i don't think it's uh exhaustive at this point in time here this one's from about two or three years ago you can see that there's an enormous number of exploit kits that have been developed over the years uh they kind of kind of tend to come and go and there's usually about three or four at any one given time that are popular but one of the things i wanted to do was
to contrast this with what happens with traditional malware and this is you know off the cover of once again a no starch book practical malware analysis so in the past when we got malware it came as an attachment it might have been a pdf diagram might be in an html file or it might be an exe file so usually what happens is you downloaded it you could put it in a sandbox and execute it and it would have the entire process in there the unpack the de-obscation you could use a standard you know process that was discussed earlier today by aj elise and which would be contained in this practical malware analysis you'd try and unpack it you'd
scan it for strings load it into a disassembler and somewhere along the way run it in this in a sandbox as well well when we have an exploit kit the links to it are ephemeral they are disappear you've got four or five of them that go in a row so you're basically going through a maze to get there it evaluates your target machine so when it downloads that payload it doesn't download the payload for well if this is like a stuxnet virus you know if this is a siemens controller do this if it's a another brand of controller don't do anything basically it only will get downloaded if there's a viable response and the reason they're doing this is so
that they can minimize the analysis that ex that it gets done on their kits and it extends the tool life so usually their fallback is to a web-based credential fish meaning they take you to something like a microsoft office 365 page and you know because this has now become a business uh there are usually pre-packaged mix and match systems and once again we talked a little bit about this they're now manageable and supported tools people get some fairly direct feedback as to what kind of machines they're running into how quickly people are exploited on them and you know if they have a target they can see whether or not they're actually getting through to that
target so i'm going to go out here on a bit of a limb and make a a prediction here because i think this has already happened i think exploit kits will continue to dominate if you look at the email analysis programs this is uh reports from things like avenon and proofpoint exploits kits are starting to dominate most phishing emails now have links in them they're way more flexible they come pre-packaged readily available you know if the rig exploit kit stops performing you can go out and buy the nuclear one and i think they have a higher damage potential now we also heard a discussion earlier today about threat hunting kyle gave a talk on that i think this is
important here is that every time somebody sends one of these things out you actually have a direct contact with the enemy and they have to show their hand to some degree yes the ips changed a lot yes the web pages come and go however the techniques that they use meaningless exploit kit they choose and we need to take a look a little bit at also the process of how they would do this and sending it out so i have here a picture here of one of the current exploit kits this is from zed scalar and they're looking at their rig exploit kit and you can see that it's being used fairly broadly throughout the world in
europe united states they don't put canada on there but russia seems to be fairly popular as well and what would we do in order to try and stop this we've got this contact with the enemy what we're really trying to do is prevent it so if we look at the process involved in hacking a website or maybe more to the point getting into a company we send out an email email has a link and then we get into this process where we want to get an initial compromise establish a foothold usually that's somebody clicking on an email and they get a cnc server then they want to escalate privileges or do an intertidal recon and i've pulled this one out of another
book here this is how you would get into a cloud service in this case the order has been slightly reversed in here they've gotten an internal recon found a token or a cookie for a website use that to get into a web service and bingo they've got the information they want so we kind of want to understand what it is they're doing in here so that we can find what's happening here we also want to understand how that web how that initial compromise occurs because if we can stop the initial compromise so let's go back to our diagram about how the exploit kit works well if we sandbox or we have somebody that clicks inside
the company and they get compromised we have all the information that's shown in the green box here we can see the html code that came from the compromised website we can see the javascript that'll get recorded we'll get an iframe is one technique that we may use in order to accomplish this in this case they have a flash uh for for the exploit you'll get some fingerprint on the flash and then you can take a look at the malware the malware has to get downloaded and unpacked however that's not our only sort of information we could like i described earlier also do a pcap analysis on all the information as it goes back and forth
and then you'll recall i had a slate a page there where i got into the management page for compromising a website well when that happens you have some insight as to what's going on and if you happen to know somebody that hosted one of these websites you can actually see what's in there and before they take it down you can do a forensic analysis on there and even get the zip file that actually uh i'll sets up the website that does the compromising the exploit kits are usually dispensed separately and this was once again another indication of the compartmentalization that's used to protect the exploit kit if you could get to one of these and
these are normally located offshore but once again law enforcement in france or in russia takes one of these things down and then also you have the opportunity in some circumstances to actually get to the dns server and see how it's set up and see how the domain generation occurs so in most cases we're probably most interested in what's happening in that green area so what have we done historically for counter measures and the answer to that is normally we keep track of the bad ips we would go to virus total and see okay well what we have in here uh in terms of uh do we recognize this website and if the website's recognized well then you have a reputation
but if the website's compromised which is usually the case these days there's no reputation at all it's not a brand new website so it's an established domain usually the spf dkim and arcs are legit and people know these users we still see a lot of office 365 password expiries and html voice mails but i think that the proportion of these is based on my experience getting smaller and lately i've seen a number of fake advertising and some of these are quite technical like literally people talking about technical geology or technical engineering which is in my background geological engineer and i go wow look at that that and then when i uh oh another one would be conferences when
i've gone out sandbox those things i find they come up as being malicious so we need to spend quite a bit of time looking at spam these days these days as well so what are the implications of all this uh we can do forensics on the payload uh usually when the forensics team comes in it's too late you've already got a compromise server uh we have endpoint protections uh we have av and we have uh things like secure connector or sysmon we can buy p caps literally off the web that have the web traffic for these things a number of researchers have set up watering holes in here they set this thing up so that the people send emails
to them and then they go and run this thing so it's not there are ways of getting this done in most cases these links only last for three or four hours if they're not done within three or four hours it's too late people have moved on they've taken down the website or changed and then you have a situation where if you want to understand what happened somebody clicked on a website they tell you about it the next day you can't go back the next day and see what that exploit kit would have done because when you click on the link everything's already dead so there are other opportunities researchers have purchased kits i talked about compromised websites
you know you can get the webkit there and then there's also the possibility that somebody will take a management takedown however in most cases these are conveniently located in difficult jurisdictions and i'm going to suggest that what we really need is something that's actionable for the majority of people like you and i so one of the things that i think is underutilized is recognizing the pattern if we do a simulated phishing program what do we do we prepare an email list how do we do that usually we download a list of all the people in the company from active directory however if we were working at this from the other side we would do an ocean we'd
do an open source intelligence gathering we'd ex select the exploit kit in something like proof point we would select the email template and in that case the payload is just literally going to the software as a service for proof point in a real case it would be different but this is really what we're trying to find we would also set up a schedule on this thing here and then we would monitor our results now we can actually use email spam filters and things like that it does work it works to a point there's things in there that can be triggered off wording but in a lot of cases and i'll give an example of an accounts payable invoice
we get an invoice they commonly come in html files and a lot of the fish we see now look exactly like what would be legitimate emails so this means we need the sandbox sandboxing requires a couple of things one thing we have to get past the first link because it's a redirect some will be down and in fact this is one of the things that we can use as an indicator we'll need to get in many cases pass the captcha and a lot of them actually track to see whether or not there's most movements so if you just moving your mouse around will actually have an effect and then most malware now has detection for virtual
machines and there is the option of actually having little knock type based uh physical sandboxes and you will get different results based on my experimentation and once again the objective here is to get to the payload here's another little trick that i think is underutilized but if you take this thing here through manually and get to the end you'll get to if nothing else the credential page and they'll say enter your credential well you know i put in some dummy credentials you know i put in there you know bang bang bang it you know companyname.com and uh then my password would be don't buy a bad girls but if you actually set that up so that
it set actually went to a mailbox or went to an actual login once again you don't want it connected to anything in your environment you want it to be connected to something isolated all of a sudden now you have a direct connection to where the bad guys are actually sitting and you can see where they are so uh one of the things that's really interesting is these things will actually test in real time while you're actually running that exploit kit it'll come back it'll almost always say oh um you know um uh you know you need to enter your password twice and that's just simply so that they can confirm your password but if you put in
one of these dummy credentials it'll come back and say yeah that password or that that account doesn't exist so they're actually in the background checking to make sure that they can't log into your system so here we go uh one of the things that's really important here and this is what happens if you get a clicker you send out a an alert alert comes back and somebody says hey i'm sorry i clicked on that yesterday and the next question is what do i have to do to remediate this once again we had a discussion earlier today where uh aj lee's talked about remediation and what you would do actually knowing what's in that sandbox results and forwarding those to your
seam or your sock will help those people to know what to look for there may actually be in there things like what cnc ip on there you might know whether or not it was set up to what kind of software it downloaded all very important information so what else can we look for in an email all of these things have styles i saw that these ones that were technical uh conferences and things had a particular style and it wasn't actually that hard very difficult to put that into words to put that into an ai type thing but you'll see a lot of them use a url shorteners a lot of the customer systems are compromised so you know you have a
doctor's office doctor's using constant contact somebody breaks in gets a credential theft in there you use the credential theft to get into the constant contact all of a sudden you know working at a utility company you get this thing from this doctor's office in santa clara and it's all got the links that go to what you would normally think was a safe location which is a constant contact link so they have to prepare these mail lists they're prepared from intelligence one of the things is really interesting is i see in some of these that they'll have the same email list almost identical and there's even the same mistakes somebody's repeated a name twice you'll see that they're often targeted
specifically to only the users very often the size of the list and the variety of the surrenders indicates resources and also you know that people are reusing things so i have an example here uh this is you know actual field data uh you can see here in this particular case that you know we've got this massive campaign 1780 emails you can see there's some 60 70 almost domains that have been used comes from 65 or 63 different countries and then you can take a look at those email lists and they look surprisingly similar so they're very often using that same list you can imagine that to have resources and actually these get progressively more recent as you get up to the top in
here at the bottom here you know they were starting out with 30 or 40 different countries as they get more and more as their network gets bigger they're getting more and more countries in here you see on average they only send an email or a an email in here and this is all designed to prevent automated fish detection they'll have one two or three different emails that come from an individual source so you know if you take say something like the proof point analyzer it sees over 200 emails with the same title and it'll say oh this has got to be a fish you know this is a campaign well you'll find that they have when you
have to take a look at the subjects that the subject has a four sequence number in there of dga numbers that are randomly generated these subjects never appear to be exactly the same all of these are indicators that you can use to find that oh we've got an organized fishing campaign so when we get into the actual sandbox it's tremendously detailed i show some of the uh stuff that was there before when you did actual disassembly but there are some gross sort of overriding things in here and this is actually from joe's sandbox you can see that it takes a look at the functional grouping is this a trojan you know does it have an evasion in it it's in an
exploiter does it have spyware in there it has a little bit of a flow diagram well here i have an example here of a series of different ones that were run you know fairly close together in terms of time we have one in here that shows up as malicious picked up by a snort signature then we have another one that's you know immediately you know almost at exactly the same time two flow charts look exactly the same well depending on the packer or the obfuscated obfuscator and things like that this snort picked this one up but it didn't pick that one up and the truth is sandbox still rely heavily on signatures if you go into cuckoo or something like
that you see one that rates a 10 out of 10 it's usually been picked up by two or more virus signatures but the behavior is almost identical from other ones that you know only rate a two or three or four and then i have another example here once again i'm looking for similarities and i'm looking at the flow chart here you know those two look almost exactly the same you can see it comes down there's two big black boxes there and a smaller one off to the right there this one here is a little bit different it's a big black box too little bit but then you look at this one here in this series in here this one's been
flagged as malicious once again that'll be a signature you can see in a number of these they have some you know snowflake snowflake snowflake you can see they have similar these ones here have similar programs and very often you'll find that that's how you find them is you take a look at these things in here all of these things here are polymorphic enough that they aren't easily recognized so how do you decide which ones are bad and which ones are good i have an example here this happens to be a cuckoo sandbox i ran it against memory express it's a company here in town that sells uh computer hardware computers not so much software but accessories uh probably everybody in
here has been this in calgary has been do uh memory express at some time i looked at their website here you can see they have an ad for uh office opening in ottawa it comes up as a 2.4 out of 10 which is relatively clean you'll notice that once again we go back to an understanding a little bit about running the browsers it loads material on the heap it has some executable files it does a couple of things that you would might not hopefully that it wouldn't do it uses some windows utilities for basic windows functionality potential heat spray 149 megabytes resumed a suspended thread potentially indication potential indication of process injection okay well then let's take a
look at some stuff that came up a little bit worse we've got one that came up as a 4.7 here we are raised to sura cata alert sarakata and snart are both intrusion detection systems dropped 64 unknown file types in here um mime types so this is an attachment indicating ransomware well that's not a good sign so that's probably why this one got a 4.7 you can see this one here is download an agenda it's for a conference uh contact's an ip that is no longer responding and you'll notice we had earlier on that zigzag pattern of slipping through websites this is the indication that some of them have already been taken down heap spray but the heap spray is now
very large it's 2.74 meg or 2740 megabytes or megabytes which is really big that's 2.7 gig that's a big file download you can see in the next one down here communicates to dns uh or commutes to a host without a dns lookup so it's got a hardwired ip that's another indication contacts ips that are no longer responding once again that's similar to the behavior we saw happen here so in this case i'm looking at stuff that it's you know and more in the 4.7 range which is above the 2.4 but then if i look at some other examples and i'll just go to the one here at the end here which was definitely malicious this was a really tricky one
and as an spf fail looked like it came from microsoft in fact it did come from microsoft it came from a hacked server but the score and this one's only 1.7 and here it is microsoft sign in once again another one here at 2 this is a you know a shared business file this is one of these ones where i send out in a proposal once again also another hacked site so you do actually have to look at the screenshots and of course in this case here you can see people are saying oh yeah yeah we'll help you download your new browser update which of course is a polite way of saying please open our malware um
so i have some summary here general cutoff 2.4 look at the login screen if it's got a credit harvest well you know it could be as low as 1.6 look for larger heap sprays uh anything over maybe 250 unknown mine types are a bad sign ips and ids alerts are bad the dead urls bad if you look at this one you'll see this one goes to a website in here it doesn't actually are not a web yeah it's a website but it's called hotwheels.shop and it's got a um a login there's a company logo associated with this that i've waited out uh oops uh and then look at the flow diagrams see what they look like compared to stuff that you
know is malicious and then finally you'll see very often sometimes you get a direct ip without a dns lookup but anything more than one or two is bad sign so we're always hoping that we can make these things automated and i have some automated you know summary here of how you might go about this user awareness of course is really important we spend a lot of money on that now we run all these simulated programs there are for instance say on emails software detection programs out there they usually have a combination of things in there a blacklist heuristics which is basically a rule like an um a transport rule some visual similarity which would be
you're eyeballing the thing and then also machine learning you can key off particular words in there and you can see in here that for instance on spam identification people have used support vector machine and other forms of ai to figure out and then of course you've got your sandbox in here you can automate the sandbox in here as well urls in the memory dropped files behavioral analysis and then i'm almost done here got a couple of other last interesting little things here uh this was a paper on somebody that had been basically trolling the red doing a web mining thing in here and they found all these exploit kits and they found in one address so this is an indicator
of compromise where the people that were running the exploit kits actually had basically had the exploit kit phone home when something happened when they got a got somebody and they found that they had this one wire zed at google docs.org that showed up in 115 different sites so there are based on research uh indicator is a common compromise that you can use so what else can you do and there was an interesting talk here not a lot long ago put on by uh cowsec they had some guys in there with something well one they came in and uh did a simulation with uh that they did with uh mitre on our apt-29 attacks uh sc labs which is a company in the uk
uh they've tested a number of different email uh evaluation packages and um they actually simulate what would be a threat profile for various attackers and see how it works and then there's another company out here this is based in europe i think virus bulletin and they do a comparative review of how these different things work and the difficulty we have here is we've got lots of uh vendors that are you know and they sponsor the conference that are out there marketing their products and you know i think that this is very sincere and that they're doing their best there's a little bit of serendipity and making sure that you get access to all the information on
these uh exploit kits they're difficult to have analyzed because of all these different varieties but you know how do you determine from various marketing claims which one works better than the next and i think for both the companies making these things and also for the potential buyers taking a look at these test examples really helps a lot and overall i think uh it'll be better for both users and suppliers if they have some quantitative method of testing how their products work so here we are at the end i have some conclusions here um exploit kicks are really a dynamic echo system they're very flexible they started out in 2006 and they appear to be persisting a
number of people thought that with the demise of the internet explorer of course microsoft has now migrated to their edge product which is basically a rebranded chromium with microsoft features and that has not actually resulted in the depth of the exploit kits at all the guiding factors or the protection of the exploit kick that makes this popular have not gone away i think they're more dangerous than the traditional malware the traditional malware you could dissect it using conventional malware analysis that's time consuming and difficult but now you only get little bits and pieces unless you work at it really hard and uh i'm going to suggest that you know as you're going through evaluating your emails because these
links are ephemeral and the exploit kits change rapidly if you want to know what you're going to need to do in order to remediate you have to be taking samples every once in a while to see how things are going and finally you know we're in security business and it's a you know people are now calling this a bit of a cyber war and whether that's true or not maybe not important uh know yourself know your enemy you want to be taking a look at these different things and understand what they're doing and that will help you better plan your security program and it's important to know that that's pretty much everything i had to
say it is now currently 1648 which means i got a couple of minutes here before uh 3 50 and that leaves about five minutes for a question so if anybody has any questions please by all means uh fire away okay i had a question here um um dominance of root kits uh root kits are only one aspect of the fishing in there and a lot of what we actually see in in my opinion appears to be command and control and uh that's really a remote access trojan but a rootkit is also of course something else that people could do um don't know if that really answers your question but i i think that uh uh
oh do yeah okay i see yeah you meant the exploitation kit yeah it's not that we don't ever get anything in there we still get the audio htmls and those actually have links in them now so they're actually also a form of of a exploit kit and with people being able to buy these things or on a commercial basis they're um it's very quick to implement and it doesn't take you can imagine that when you set one of these things up there when you build a web page you need a php component to it uh they probably don't have to do a database back end in there but then you've also got some significant programming in terms of
putting in the javascript in there to make the whole thing work and so it would you know you actually need a fair amount of technical expertise to build one of these exploit kits plus then on top of that you have to be able to deliver the actual exploit itself um that's pretty much it uh anybody else have any other questions okay i had a question here on whether i think ipv6 will have any effect in that area um not that i can think of but that may just mean i'm relatively new to the security business so that may just mean i don't know um oh one last thing in here i actually put some references in here as
well if you're interested in knowing uh more information about these specific things you can use the presentation and i'll find some way of getting this uploaded as a pdf so that people can go through it and there's a variety of sources in here i actually find because exploit kits are so new there's less in the academic world and a lot more in the commercial sources and you know you can see some companies have made some really big efforts to track these exploit kits and uh the commercial sources are much more current and um [Music] this of course is also part of what they're trying to do as their quote competitive advantage and providing the best product that they can as well
and i think there are differences there with that i think i'll got two minutes early here so i'll finish up there thanks very much hope you guys all have a good day





