Methods for Parsing New Mobile Apps: All about that data
Show transcript [en]
cuz you know I've gotten 92 slides hi everyone thanks for coming I know it's the end of the day can you all hear me yes whoo all right so today we're going to talk or this afternoon are almost this evening we're going to go ahead and talk about how to parse mobile apps that are unsupported by commercial forensics tools so I work in digital forensics Incident Response have for a while and what that means is after an incident or after a crime I'm going ahead and parsing data and looking at and now actually I worked for a company to feel stupid it if I'm not talking about any of that and I'm talking actually about
what to do when they don't so I guess it's the antithesis of what my company would want me to talk about the bed school the second thing I do is I teach mobile device forensics at George Mason University I've ran two mobile forensics labs in US government as a contractor and I've also worked as a consultant so I've done both sides of the house in terms of commercial and government law enforcement icy investigations how many people in here do forensics all right got like four five of you and the rest of you InfoSec okay hackers just straight-up hackers so it should be all of you you're all hackers and students okay good mix very cool okay kinda tells
me where to go so I have a couple of goals for this session number one is to show you that your commercial tools will never get you all of the data and to inspire you to dig deeper do the manual work and find the second thing is to give you a methodology as to how to do it so I'm gonna show you how you can do it and you can do it okay the third one is to understand how to parse and the importance of validating data even if your commercial tools do it I'll share some stories with you and then overall to give you a methodology to parse apps you've never seen before so why do we care if we have tools well
if you look just at the Google Play Store and the Apple App Store you can see there's over 4 million apps if you take every commercial tool that does mobile forensics combined you're gonna parts about 400 apps so chances are your nefarious actor might doing something different so in this we're actually going to go through built a scenario here to show you this and I made some guidelines I just want to know you didn't know the left and rights I wanted to do Android just for the simple reason and I want to take something really basic because I do have the understanding them unless you have a jailbroken phone unless you're law enforcement you're not gonna get a full
file system image and if we're digging for additional data you're going to need a full file system image I also want to use entirely open source methodology for this demonstration so everything you see here you can do on your own I also wanted to show something that doesn't store in sequel Lite because that would just be cheating okay and then stress the importance of scripting so the entire goal here is the methodology and so this methodology is discover test find parse script you will hear that for me over and over again because it's really simple so starting with discovery how do you discover if there's an application on your phone that you missed when you ran a
commercial tool a celebrate an axiom and X or whatever tool well first you want a physical image or a file system but let's say physical or or a file system image if you have a logical image which is much like a backup that's not going to help you because all of the data that's there it's already been interpreted by the operating system and read you do want to look at what the tools that you do have at your disposal ran and found because you don't necessarily want duplicate work you want to look at what's installed on the device and what's been used as well as look at permissions and we'll talk a bit about what kinds of things you're gonna
look at in permissions and then validating in the app store so first creating that physical image for those of you who may not be familiar with doing this I'm gonna walk you through how to do this in an open source methodology so use whatever your organization's will allow in this instance we're gonna use at warp recovery recovery modes by default have root when you have root on an android phone you can get a physical image that's the the basics of everything so for those case we just used the DD command which is the most simple camp command I did one partition and that's neither here nor there ah so I've been using an Asus Nexus 7 the
reason I was using this is I have two of these I have two of these because I have two children and they are my little data creation monkeys I'm not joking they download every app I approved for them to test and they communicate on them and did my husband make it into my lecture know my husband was playing the CTF so this is what happens when a forensic aider married the red teamer all right so who married when they met in the Marine Corps and neither with the Etta forensic a turn or a nor a pen tester but all you need to do is Google the team win recovery pack the team win recovery project and go ahead and find
at orphanage for your device note warp is a hacker collective I stand not by anything they may have so please test on an exemplar so installing ADB ATP's part of Android studio so just go to Android studio click the download button and download the command-line tools for your operating system pretty simple this is the command you're going to use to connect to your device you're going to do flash adb devices then you're just going to do ADB reboot bootloader in order to go ahead and put your device into the bootloader mode so you can flash at warp image then you're gonna go ahead and flash the recovery to warp image if you want to copy any floods you
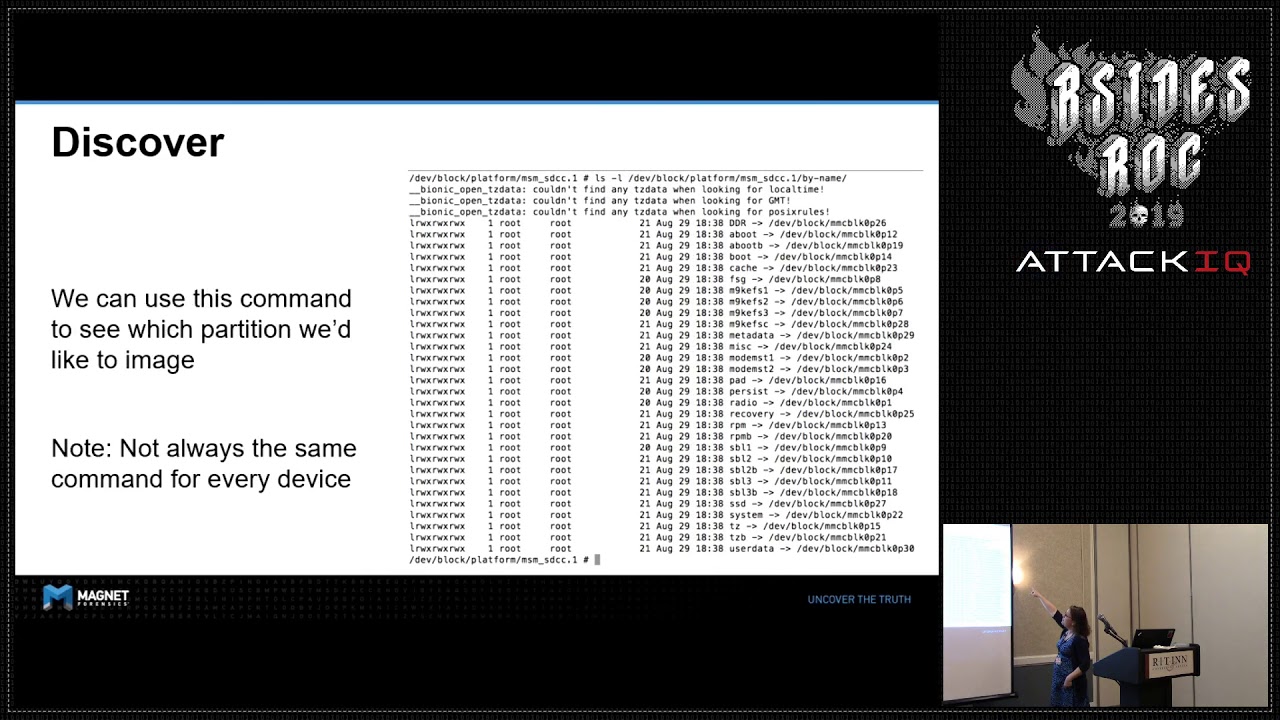
can get them because I know I'm sending command line at you fast and furious I did give you 92 slides today I don't expect you to take a picture of everyone so once you do that you're going to go ahead and go give yourself an adb shell so that you can see all the partitions on your device anybody want to guess how you can identify the user data partition it's the biggest one very good so your MMC block 0 or your your mounted 0 but there's some emulation that happens with Android 8 & 9 we're not going to get into that that will be the full device but will include all the partitions you might not have interest in and
instance it's block 0p 30 it's the one of interest and if we actually run the by name command we can actually get the names of each of those partitions and not the side you can match those up and you now see that two user data well we're going for user data all right so what you need to do to user data is you need to command prompts open to command prompts this is really important you need one where you're going to hit go ahead and get your shell right you're gonna forward your traffic on your port and then you're gonna go ahead and say give me that partition use busybox to netcat it to that port then you need
your second window to go ahead and direct your net cat to go ahead and write your image sound good sometimes people get confused by that to window thing alright so once you've done that go ahead and take your image and run it through your commercial tool this is the only time I will show the commercial to what my company makes because I am showing it failing hashtag worst vendor rep ever the point is it is finding no chats in this data set and trust me I built this data set it's full of chats now what you will find on here is lots of games this is packages that list don't worry I give you a bigger screen caps it'll make
more sense when you take it home so on here it's lots of games I'll tell you funny story about clash of clans I was trying to get chat data and click clash of clans you have to get a level for Town Hall how many of you played clash of clans I am so not a gamer so I'm sitting there with my kid and I'm strategically trying to get the label for Town Hall he's just telling me mom you're playing wrong and I'm like no my objective is different that's okay he learned about objectives so so I get my package inside list and I'm kind of getting the scope that this device has a whole bunch of different games by the
way if you care we're not gonna look at clash of clans clash of clans stores all the data gets we're on the cloud not the device and this is a device forensic class not our lecture this is not a cloud one so we're not going to get into that but at some point if you want to hear that I'm happy to talk about it it's not that you can't find a day that's just a different way all right so here's your package it's that list it lists every single application on the device that's one way to find out what's stored on your device still doesn't tell me what's been you still doesn't tell me what can chat
so what are some other ways comm deafening dot Android will list every single purpose purchased app and you'll see here that scuba lover has purchased conduct Witter at Android and we see an epoch time January 1 1974 for the timestamp but it freakin lies don't trust combat vending and the reason is because if you have multiple users on the same device which you can do on Android it will attribute applications from one user to another that they never owned so for those of you who do forensics investigations don't rely on the second thing I went ahead and took a second device installed the same account through the device into airplane mode before it could download the application
and it said I had them installed and paid for so it can lie two different ways don't trust it it's actually very important I hope you also get out of this that your databases will lie to you you need to know what data means please test so here's some really cool stuff and this is cool because none of commercial tools do this and these next couple of slides and this was stuff that I released in the summer and I'm super excited about the stuff set so there is
guys I run around he knows that I'm so sorry so Android usage stats it tells you exactly which files in the background the foreground it gives you a couple of different folders and then there's the Android usage history XML which tells you the same and it gives you this lovely XML and what's so cool about this XML is you get the last time active you get the package name package names by the way are looks like a domain name in Reverse usually calm company dot platform if you're wondering how you can get those if you ever go to the Play Store and look for an app it's what's in the URL bar I do this all the time to go
back and forth between the thrown I'm looking at and what the name of the app is if I'm starting that way and if I'm looking for particular I look in the Play Store for the app and then pulled a name in a package name from there to move forward so there's also battery status and battery status it's really cool because it's almost like the system resource usage monitor or srem that exists in Windows but it lives on Android and the reason this is cool it's because it gives you a whole bunch more information so battery stats dot XML tells you exactly how much charging is happening but that brings you to the battery stats dump and the
battery stats dump actually tells you a process with a UID now there's obviously a reason I'm telling you about this UID it's cuz it rocks so the UID for Twitter is one zero one zero three can anyone in here remember that no you're full of it no that's okay I promise I'll show you the same thing so alright you know at this side of the room you've got to remember one zero one zero three because there's two things we got a correlate here so then there's recent images recent images is really cool because it saves the icon of the applications you've last look at and it starts the file name with a number this number is the task ID so we've got a UID
and a task ID so task ID two four four it's for Twitter now and what's your number on this side oh you guys are awesome great where are you guys what I'm doing exams is a notepad alright so if we look at two four four we've got our file information we've got a date and time and what that is saved for is you guys know when you change your apps and you go down you hit that button on the well I guess wait sorry how many people in here use Android how many people in here use iOS that's how I know a hacker room or Android and iOS ooh-rah all right how many of you rock boats all
right oh yes those are my people all right how many of you are rocking a Blackberry good no shame in this room oh all right no no windows phones in here right I because you've got a good camera on it right well let's talk after work I'm calling this work now all right so moving on so we look in a recent tasks folder and guess what we're gonna see there we're gonna see that recent task ID with an XML when we go ahead and look at that XML it ties the task ID to the UI d-10 ones here are three people you just got coordinated to 244 and that's cool because now we get the first active time
any pop timestamps in the last epoch time as well as the last time the app was moved so now we've got the task ID for Twitter the new ID for Twitter and the first time it was moved now Jessica why are you telling me all this because we have to figure out what apps have been used on the phone to figure what apps might have been used to communicate and now we have a way to do it we didn't used to have that but there's more so if we actually go to shortcut Services snapshots we actually can find those pictures by task IDs that were saved so that you get that gallery when you hit
the button now what's really cool about this is you would never ever ever find somebody who you're just looking at on Twitter just by pressing this button you wouldn't normally you and your Twitter caches can get things you've looked you know p.m. and you can get history of posts but you can't just get pages you happen to look at but this was the last page that we're on before they switched apps so how do you really know my buddy Alexis Brignoni wrote a script for this about a week ago called us arty he made me so happy it's really cool because it even brings in that image to it but the whole goal here is now you can figure out what
applications were actually being used not just install likewise if you guys know Sarah Edward she is an rit alum and she does a lot of really awesome iOS work and she wrote an app to do the same kind of stuff for a similar type of set of databases called knowledge CDB in iOS so that at that place all right so now you know what apps are used so now you take that information go to package of XML which is going to give you the permissions and why do you want permissions because now he's got to figure out what of those apps might have been used to communicate remember we're looking for chats okay once you've identified the ones
that have the types of permissions you looking for which might be things like read contacts get SMS etc then and only then you're gonna check out on the Play Store and see what functions it have and sometimes you won't get all the functions listed in the app this is a game workshop and the only place that I can find the picture of is a picture of the functionality with a chat bubble so in our image we wound up having three games excluding clash of clans which homie stores in the cloud that are possible to have chatting in and they are chats with friends word chumps and quizup so now that we know that we're gonna go ahead and see if we can find
some parsers in the World Wide Web even though I did run these through six different commercial tools none of which picked up these chats now luckily for me cheeky forensics monkey best person to follow he's really cool he actually does a lot of Windows Phone forensics and forest laughs darn it he had a parser for words with friends and it actually worked on chess with friends because they use the same schema both by Zynga so when a head looked it up pulled out that sequel light database went ahead and parse it and we see this amazing message between Elvis Presley or arm sorry Elvis P 74 and Frankie blue-eyes 2016 where they're talking about chess
it's very exciting not my nefarious activity time for me to move on so now we need to figure out how to get data at a word chumps and quits up our discovery phase is over so now we got a test so our next objective in testing now that we've discovered our apps of interest is to go ahead and create test data now the reasons you're going to create test data or a multitude number one test what you think is happening number two validate your parsing and support number three I'm sure you understand data storage the number one way to understand the data storage is to start with things you know if you have known data it's
gonna help you to code later also this allows you to validate your parsing don't assume when you assume who okay so Quinn's up we're gonna talk about quiz up right and you see quiz up right there quiz up made an entire database of all of these avatars and added all these people to my contacts okay I was creating a test day this wasn't data off evidence right when you start quiz up it starts spinning a world and shows an avatar of ten potential connections that's going to connect you to to play the game okay and then it matches you with one person you play him in my context was not just the people I played
it was everyone I could have potentially played and it wrote it to my Android contact database on my device and had the avatars in there so just because you see data and you can parse data and it makes sense up here doesn't mean it's factual you've got a test so I've already given you two examples of BS data being placed in phones that potentially you could make an assumption that it means something don't let the other side have that reason if you're going to court please so in this I mentioned I was using these Nexus 7 tablets the first thing I do is I build profiles and I saved these profiles I actually keep them in a keep a past
database I just had them here I have lots of profile plots of my profiles talk to each other I actually have made a community we have an actual slack of a whole bunch of people who in forensics create and maintain data test data profile so all our profiles can only talk to each other safely without ever bringing in IRL data and this is critical so if any of you ever are in that position we will vet you first we will go over game round rules with you first but we'd welcome your profiles to talk to our profiles don't worry this password has long been changed don't think that you just pwned Frankie blue eyes all right
so one other thing ensure that the version of your app that you're testing on is the same of your device if you want to know how I do this when I get my full physical image of my evidence I actually steal the apk out of that physical image and load that onto my test no better way to make sure you're on the same malicious version if the person you're investigating malicious version of the app so I also screencap everything as I go and I screen so this was a screencap of me saying now you want to make things move in the character of frankie sim to my buddy who was playing the cane the question was am
i using adb live to capture the screenshot since i'm using test devices no I'm not because sometimes I'm creating geolocation data as well so I'm usually just screenshotting because I know that screenshots are going to go into my DCIM folder so and since it's my test device I actually have my screenshots in my same forensic image where I'm doing all of my other validation and parsley so now we've got to find the data you've got to find where that app developer chose to put all of their databases right now remember if data can be stored in multiple places and just because you find data in one database area doesn't mean you will find in another oh and by
the way when you're testing you're gonna have to test with different storage areas if your app settings allow it because you don't know how your user had their settings right and you don't know what those settings look like in the databases because you haven't set them up yet because it'll just be Flags awesome so it's important to make sure you're denoting and writing down every single step you take when I do my testing I actually wait a minute between each function I do the same thing when I build mobile CTS so data can be stored in multiple places and just because you find some of the data and data slash data does not follow die the package
name does not mean that you're not going to find data in media / 0 these just happen to be two of the most common places look at all the possible files in each path pull any associated key files I definitely keyword search things I expect to see like send or receive chat etc I go ahead and grep and then I use the appropriate viewers if I can I'm actually gonna go back to your question for one second you absolutely can live test across a DB you also can do on jailbroken iOS devices and on jailbroken iOS devices Sarah Edwards at Mac four and six comm wrote an amazing post about how to do it on iOS you also
for Android by the way can do all of this in emulation you can't do that for iOS and there is a great virtualization post out there if you want that that's Alexis Brignoni I'm happy to share that with you you can do that with Andy again all of this is complete open source free methodology that you can do so you don't need difficult devices to test just make sure that your emulations are the same operating system version or otherwise you're gonna be completely out of luck and again just steal side load your apk side loading apk is that's like my favorite hobby you guys have better hobbies alright so we started looking at quiz up and when we started looking at
quiz up we can actually find this data there's actually a cached chat history and cast conversations that I find in media 0 so I'm gonna go ahead and start looking at that and yep I've definitely got data there I think I give you no I don't give you this I'm gonna show you the state of really close up in a little bit then looking forward chumps data is in a completely different place it's in datacom and this is what I keep talking about guys with the package name that comes up datacom then a package name and then I have the multiple chat databases and multiple friend databases alright now it's time to parts now that we found
our data thus calvert tests fine parse script but form parts alright so you got to break down the data next step is to turn it into human readable format right and we don't know what we're gonna see so you may have to correlate tables and databases you're gonna have to decode data and you need to think about the basic fields so you expect to have a center in receiver but sometimes you'll just have one and the opposite one will be your localhost ok so it can be sender receiver two separate columns or fields may not even become so fields this might just be a string an XML or JSON but they may be one and if they're one your
direction is going to determine if it's a sender or receiver you may have time and date they may be one field they may be split direction you may have direction Center received but that may instead be determined by status sent read unread status itself might infer the direction so in a really slim database you could have a party either sender a receiver time date one field and just the status and that's it then hopefully you want to find attachments note attachments oftentimes can be in a completely secondary data storage and sometimes this is one of those things you can do by settings where you're going to actually find attachments in the SD card emulation and remember you may have SD
card folders even if you don't have an SD card slot because an on-board emmc in real life it's just an SD card literally you can pop the chip off put it into an SD card reader suck it into an SD card converter and put it through a write blocker like I've done that many a time they're really just on-board SD cards you want it going to want to find the messages than any geo data it's just the things I'm looking for now I've got like this sometimes less sometimes it's equal light which you kind of pray for because it's so easy sometimes it's open source but sometimes it's gonna be a dot bat with proprietary formatting which is
what we've got here sometimes it's all plain text sometimes it's encoded sometimes just the chat data is encoded and metadata isn't sometimes it's a reverse and sometimes there's just standard encoding that we're gonna find so looking at quizup that is a freaking just a bunch of words right but it's really easy to decode so can you guys see that it's literally a bunch of words it's not that bad I can actually just hit return and make that human readable now that's human readable I can see when it was created who the front player is yes it's an ID but I can convert that later I can see a message ID I can see read equals false
I can see text all this is all clear text all I needed to do was open it in notepad and hit return now to be honest am I going to do this manually no what are the reasons I won't do it manually because one I'm probably going to see it again if it's a nefarious factor and two it's probably I've worked cases where the were it was this really really easy app I could have done it all manually but there were 7,000 entries was I gonna do that for 7,000 no I scripted it right so here this was fantastic because I was playing my friend Caesar and he was the other cat character and we were playing
and the category that we were playing here with Disney Princesses that's the only category where he kicked my ass so I definitely made fun of him for that but in character and told him it was because lisa-marie was his little princess get it the King princess never mind maybe way over all your heads maybe I'm old alright now looking at we're chums this one is not as easy to read I don't see human readable text I see a dot death file that's proprietary but you still can deal with this how do you deal with this you pull it up and you look at your screenshots right you know what you need to find so in my screenshots I have
time date stamps I have who sent the message and I have the calls so I can see that first message of now you want to make things move I can see this oh shoot that message isn't in that screenshot that message is in a different conversation I had two conversations because it's very plausible in a chat message to have conversation IDs and the only way I can check that's a conversation I do is I make sure that those conversations are happening out of order so I don't want to have conversation one between two people and then start conversation to I want to have them intertwine so I can see those differences in my data now I
can start parsing so I'm starting with this UNIX timestamp and the first one I see is the UNIX timestamp for the last message received followed by the number of messages within the database this is really cool because the beginning tells me where I end and from writing a parser perspective thank you thank you silly ass and now I do see that my husband was in a room so I apologize for saying you weren't here before you would sit him behind other people all right here's a game chat ID now I know where the game chat is I've got a user ID and again I know this because I was looking at the two different sets of data and comparing
it to my picture followed by a UNIX timestamp followed by the message I now have a pattern so now I can write a script so again why are you gonna write a script in case you ever see the app again you don't want to do the work again and if you have a script that you can just run in your automated framework be it that you're running something like plazo or in whatever tools you're using that's great the second is if it's too much to parse by hand and since we're chums and this instance was a moment a farías activity that's the one we went ahead and wrote a parser for OOP I had a
video oh there it goes okay so we've got our two databases of interest the chat and the game database and we've got our Python script is it not really playing looks like it's teasing me there it goes and so now that we know we've gotten their folder just going to go ahead and open up Python so opening that word chums parser script Python 3 word shut word foe so word photo pie is a script we get a message it's just gives us that last date stamp and total number of messages and then we'll have an output in a CSV and now we can see all the lovely content and you can see that basically the scenario here
is that Elvis Presley it's very upset that his famous rhinestone suit that he wore at Madison Square Garden has been stolen in his on display at the Hard Rock in Vegas so he confers with Frank Sinatra to go ahead and have Frankie and his brat pack go ahead and steal back his suit and they're gonna meet at New York New York you don't get the puns I'm sorry I'm really am an old lady I put a lot of time into my teddy Jensen I will tell you the funny story is that if you actually go through this whole case I have a whole scenario do lab with us and you know people can go ahead and find
that they screencap the route and set times and everything else but everything cannot be parsed by commercial tools at the end of the day that's the whole point I will tell you that this is Massoud was that was stolen in this scenario and I actually while a hacker summer camp of course decided that I was going to go to the Hard Rock and take pictures of it cuz it really was on display there and edit them into my dataset you know that it actually happened to be on loan with the exception of the belt the belt was on display the suit was on loan to an exhibit in Alaska when I happen to go there but get this in that display case
was a brat pack this way so I worked it to my scenario that Frankie then stole switch suits so that he could walk over any other suits to get it there it was I was so happy so anyway the whole point is a try to get a physical image if possible because only in a physical and filesystem image will you be able to find the types of data that's not going to be parsed because there's over 4 million apps just between Google Play and iTunes and there's only support for around 400 apps by commercial tools to to look for other sources of data so that you can get more information and then that there is a methodology that
you can do discover tests find parse script and that will get you through your analysis so how do you keep up with mobile forensics here is a bunch of really cool mobile forensic aters who are on Twitter who are regularly tweeting out about really cool things questions that was 92 slides no I realized that that was really quick I just ended a half-hour early on 92 slides I'm apparently crazy so questions yes how the question is how hard is it to present data for random apps that no one may have heard of in court that is a great question so when preparing data for a forensic report you need to show what the information is and if you can
show it in a way that's the most understandable that makes the most sense so if I'm showing chat conversation I'm going to show it in a chat bubble format because that's what makes sense to to laypeople how do I prove well my forensic report I talk to and mention the validation I've done in my testing even if it's something that's commercially supported because I'll give you another secret commercial tools are wrong - oh the freaking time because they take that assumptive data and present it right so that's why it's paramount to test paramount to show things in terms of ways that are understandable if I have an Android full forensic image I'll go ahead and run
emulation in order just to screen capture the nefarious activity another cool thing you can do with emulation is if you have an entirely encrypted app secret guys if you own the device and you've gotten into the device and you've got a physical image you have the keys and the app knows how to play the keys so if you actually run emulation it doesn't matter one encryptions layer unless the data stored cloud side in which case guess what the secret is then impersonate the account via token and then you have the data so you can do all of that in emulation screenshot it and then that is very well prepared to present to court for laypeople in terms
of validating and showing your results that is really the importance of explaining your test scenario what you tested how you validated each field and that would go into a deeply technical report that would be an addendum thank you a great question yes what makes me more passionate about mobile forensics as opposed to other parts of forensics a couple things one I started off in a mobile forensics lab so that maybe we're like my my deep-seated passionates but - cuz it's always changing and I love a challenge I love puzzles and three it's not just that it's changing it's harder and it's harder because it's not just the operating system you have to deal with there's differences between the
hardware the operating system the application each one is a different complexity there's less standardization across the environment which means there's more room to play plus I come from kind of a hardware hacker kind of background and it means I still get to solder and if I was just doing dry forensics I wouldn't get to still you know JPEG ISP all that kinds of stuff and if you really want to know where I spend a lot of time now - I'm playing a lot with IOT forensics and it's the same place and to be honest I also like to kind of play on the verge of where there's a lot of questions and some of the other issues with mobile
forensics is when you do a computer forensics image and you're doing something that's dead right you make a computer forensics image you use a write blocker there is no question about the fact you have an altered data when you do a mobile forensics image how are we just doing a mobile forensics image we were doing it live right we were communicating directly to the device I am actually making a footprint I'm changing things at the same reason I like memory forensics because I have to be so much more on my game about my methodologies and what I'm doing and there's so much more complexities and there's so many more version changes regularly yeah it's just fun and to be
honest how many of you have a computer in your pocket no but you all have a mobile phone yeah this is the run with mass it was about 25 percent of you I should know better I mean how many right but let's let's say that right how many of you are rocking more than two phones or how many of your often more than one phone right most of you how many are you rocking more - I got three on me right now I will be I will confess one is a test of ice I'm data populating while I'm here for a CTF I'm building but that's just fun but great question any other questions yes so the question was
how common is it to see applications that aren't the top 400 that are supported or so in actual criminal investigations so as somebody who's done lots of investigation I will assure you that as somebody who looks for it I found it lots of times but if you only pull people who just put rely on their tool outputs they will tell you it never happens so it never happens if you don't know to look for it but if you know to look for it you will find evidence regularly so guess what bad guys do nefarious actors know what tools support and there are actually sometimes share TTP's saying hey guys don't use this anymore the cops know how to parse it and they
share that information amongst each other there it's a it's a game of cat and mouse so if you can parse something not tell them you know how to parse it and then read the content that help they'll find out when you get to court so the entire organization I'll know that and then I'll move on to something else but yeah it is a game of cat and mouse it's a fun game and I'll give you the other tidbit so when I do mobile forensics I'm typically doing mobile forensics on a dead mobile phone most of your applications that tout end-to-end encryption secret that ant and encryption means once it's off the device but I have your device
I have everything especially if I can emulate and lots of things that even store and crypt it can be broken quite easily because the keys are on the device too that's just the application that knows how to run the keys like it's all right there so it it becomes less of a challenge now if you're limited to backups because of scope or time or capabilities you're limited to what you receive because a backup of a phone is just going to be the parts of the information that the developer chose to backup now there are cool ways around that so for example whatsapp stopped backing up user data but you know what you can do you can temporarily push the
old version of the apk on to the device ask that version to push back the data that's called an apk downgrade get the data from that and then swap back the apks it's cool hope you don't break it it's true and again I will I will stress testing is important and please validate and verify anything you're going to do on another device and I will give the big caveat in forensics it depends and there will be things you won't get into so let me that you know caveat it depends and there will be things you can't get into but oftentimes everything from the device you just got to think outside of the box think like a user figure out how
the data had to be made available to the user and a lot of times that'll be your win like the day that Apple changes their iTunes backup right and I'm like oh my gosh none of my tools will support it I can't even get an image Apple still Nia to make the iTunes backup work so I can still just get a backup by the way if you use an iTunes backup in a case to try to pull your data please please please for the love of all things forensic disable or enable the button that says prevent iPad iPads and iPhones from sinking otherwise you will be sharing your data with with your nefarious actor and then you're gonna
wonder why your mom's from the bad guys contact list any other question yes so I have never worked on the defense side so I have lots of friends who do but the forensic methodology doesn't change forensics is forensics and everybody should understand the the right skill now I can use stuff like battery usage monitor and recent tasks to determine what activity has or hasn't been done and I'll actually tell you a quick story about how I wound up with that research that was at the beginning of that where I was able to show the file system actions of the phone and that actually came out of case I was helping a local law enforcement agency
with and the driver had hit and killed a five month old baby horrible case and the year were witnesses who said the driver was texting while driving and the police department asked for my assistance and some research on it because they could find no evidence either vehicle data records or on the phone that the person had been texting or using any other chat application and I was like wow this is really hard cuz usually I prove something occurred not something didn't occur right and so it's like I have to figure out how to prove the timeline if exactly what was brought into foreground and background on this device and that's what the research I did to do that because to be honest
traditionally computer forensic spec to your question has always dealt with looking at the file system and doing filesystem parsing whereas mobile forensics because we started with 18 commands who knows when 80 command is yes this is the right room yes okay sorry that was way too excited but I love it when people actually know what 80 commands are so because we were using modem protocols and we used to just request give me your calls give me your SMS messages we knew what everything we were getting back was so we had this real artifact first approach to mobile forensics and historically nobody has really looked at it from files inside so we didn't have good methodologies to prove what actions were
happening in what order on the device and so when we were able to demonstrate that you could actually determine exactly what app is coming into the foreground into the background and that entire lifecycle of the of what's happening on the device with a game changer and we were able to say it is unlikely that this person was texting while driving because none of that came into the foreground at the time of the incident the battery monitor came into the foreground that's the kind of incident but I can't say that that wasn't from the impact that he wasn't charging his phone and it didn't come loose I don't know but it's interesting because it was it was actually law
enforcement asking but it was a defense scenario of exonerating somebody that that was you so thank you good question
yeah so I can tell you another scenario where we've used to Fitbit to prove someone's innocence and exonerate them in a murder case because they were sleeping with their Fitbit on and luckily for them they got up to use the bathroom and the steps that they took to use the bathroom was enough to prove that they weren't at the murder scene and there was a lot of good police work that was done by that police department because they actually measured his steps tried to make sure that the stride count was accurate etc and they they validated the steps the time of the steps they validated the cloud data on the server side etc so there's a lot of really good forensics
things where your devices can be your alibi and there have been many instances where a device has been an alibi but unfortunately there's been more device instances where nefarious actors are caught doing their nefarious activity because of device but at the end of that day your device doesn't lie and your device is going to tell the truth providing that you understand what the data means and you're only going to get that from testing any other questions yes oh heck yes you mean in huh oh I'm sorry so the question was is there ever collaboration between forensics and developers and my answer was heck yes and I guess it should go to a it depends so so sometimes sometimes forensics
doesn't communicate with developers because in all honesty we take advantage of a lot of exploits and if we were to close this holes that would make our jobs harder and I'm sorry to say that to a roomful of security people but it's the truth sometimes security and forensics are at odds I need open hole sometimes we do vulnerability I've done I've exposed vulnerabilities and forensics that I've released back to vendors for them to fix I've also reached out to organizations to ask questions most of the time they don't help sometimes they do it actually depends on the organization's posture and acceptance of privacy and law enforcement in the scenario and there are lots of times which everybody knows
about in which applications excuted defense have not helped I would point you to the San Bernardino shooting and FBI versus Apple that said what you guys may not be aware of is that prior to iOS 7 iOS 7 and below Apple actually used to assist on warrants and unlocking devices for law enforcement they had an entire division dedicated to it so sometimes times change and organizations change their posture so yes no it depends there are things I have to comply with legally but like I do I call up into more open source projects there are a lot of developers in the forensic space who develop tools open source everybody from Eric Zimmerman and there's a lot of sharing
in the community - Mary de Grazia - there's to Harlan Carvey there's tons of open-source development for looking at forensic images parsing data getting content getting into devices there's entire open-source forensic sweets like autopsy by basis technology there's a lot of open-source development of forensics tools there's a very large open-source forensics community in terms of cooperating with the developers of applications to try to understand why or how they may have stored data there's probably more reverse engineering that happens than that because honestly we'll read a lot of security pubs and sometimes they're not exactly complete factual you know what have you you have to test everything invalidate everything because that's a gentleman ask before you do have to bring it to court often
right so forensic by definition means that the data may go to court no matter what kind of Avenue you're in or if it does or doesn't right you have to treat it as if it might because that could be anything from an incident response to a malware incident somebody leaving a company and stealing the corporate it's leaving and stealing corporate secrets putting things on a USB Drive or somebody completed committing a murder I one time for one last question my wife - I have two minutes and one last question any other question that was your last call all right thank you so much really appreciate your time [Applause]
and it





