A Legend Has Arisen: How to use XXE to your Advantage in any Environment
Show transcript [en]
as a lesson learned so I came back in 2016 I believe and gave this talk and a lot has changed since then I've updated some of this research I've done I'm availing another unveiling but I'm demonstrating this tool that I built so with that in mind I know that they don't have the best lighting in this room so real quick here is where you can find these slides they're already viewed or excuse me they're already live on my website so feel free to go check them out there so something about me so I'm a cyber operations officer I'm also a technical mentor for node SC which is a local nonprofit in Charleston that focuses on entrepreneurs or teaching
entrepreneurship cybersecurity and information technology to high school students college students and just the local community I'm a code monkey I code in a lot of different languages I and by no means a developer but these are just some of the things that I've had to learn not only through my time here at College of Charleston so I graduated in 2016 but also some of the projects that I've been working on over the last X years ten years I like to build a lot of Legos and I'm currently trying to make a be a perfect old fashioned which is still eluded me to this day right so in in doing in doing this talk this started
off as a as a professional development for one of one of the soldiers that works with me however he's not here right now he is in another country called away on business so you're stuck with me and also this is a case you're wondering who this handsome devil is right here this is Clyde the cougar he's a mascot at college it's awesome this is me as the as the mascot at college after all someone he got his class ring his name is Clyde so I put a photo Clyde out there because you know what I look like I'm standing in front of you so here's our roadmap so we're going to talk about what is xxe and what
can we do with it the different types are different xxe attacks and it types that that there are which you can use and just general pin testing but to understand sxe you have to enter and XML right so just a quick down and dirty discussion on that as well and in a demo using our tool Doulos so Doulos is the Greek god of tricks in trickery so that's where that comes from next we'll talk about the defense against xxe after and some limitations of xxe right so depending on how you use your attacks how you actually attack a web app or some other thing that parses xml files we'll talk about those limitations lastly we'll talk about our
red blue and purple teams and how they can use that sexy and then open it up the questions questions that are authorized through any portion of this talk so feel free to just blurt them out so the key takeaways right so if you don't get anything else from this the three things I want you to get away from the takeaway from this is understand XML and how it's used for good and bad understand how web applications are exploited using xxe and then lastly I want you to understand and see the attack through the eyes of the red team the blue team in a purple team so the red team is pretty self-explanatory this talk is more red team based however
in my work as working in security operation centers and working in offensive security there there isn't a very good blend of the two right so this idea of purple teaming isn't new but it's not it's starting to become adopted as people are starting more to more and more to talk about it so I would like for the red teamers to really look not through the eyes of the red team or how I can use this in my toolkit you can always do that later look through the eyes of the blue team so what artifacts am i leaving behind how can I be detected in this right and then the blue team members this is how this is one way
one of you know probably thousands hundreds of thousands of ways web apps can become exploited right so so let's go to begin what does that sexy how do we use it right so xxe by definition from a loss is an XML external entity attack against an application that parses XML input right so this attack occurs when an XML input containing a reference to an external entity is processed by a weakly configured XML parser so weakly configured XML parser is the the key you know to this whole attack right so so what does that mean right so I you know it's basic level you craft some XML payload right and then this payload is pushed to an XML parser right so an XML
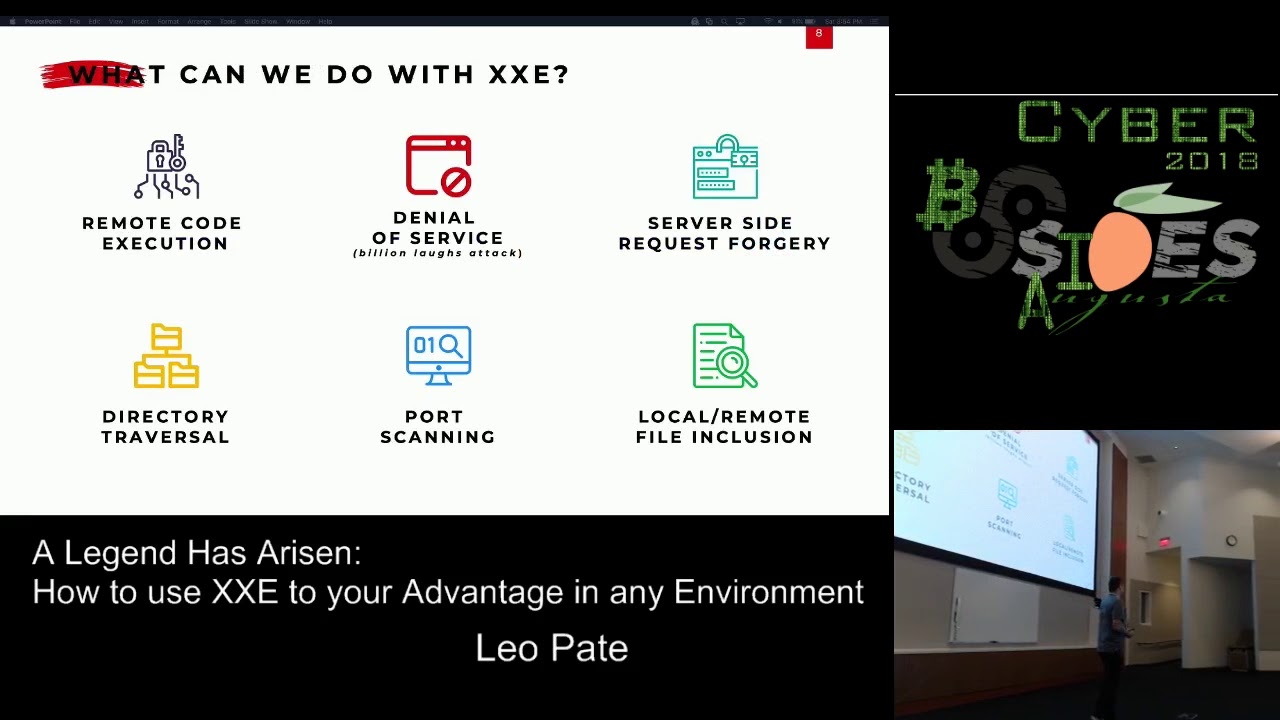
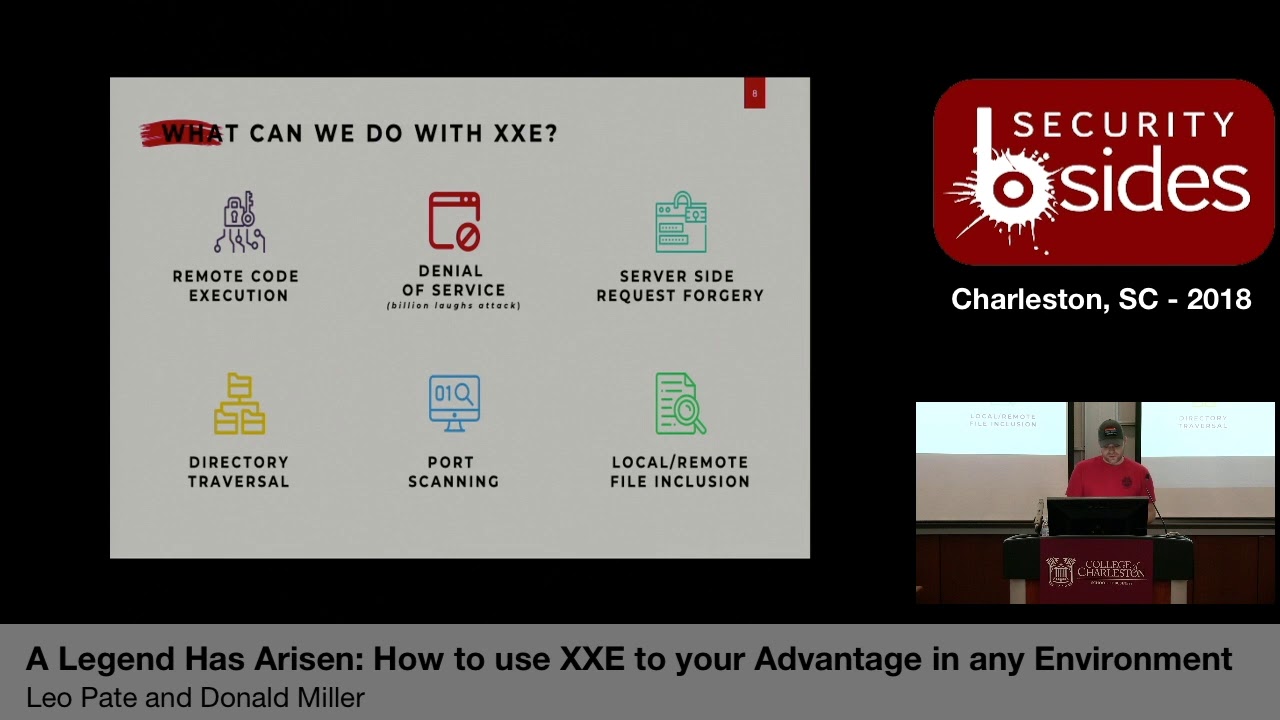
parser can be written in Java PHP really anything that can handle and take in input XML input and an output you know some thing can do some function can do some thing period right the parser will then interpret that payload that's that thing and then pwnage whatever whatever that payload was crafted and designed to do right so some of the attacks you can do remote code execution is number one however is extremely unlikely just in modern web apps you're not really gonna see this but if you're going through this xxe route and you want to test this out through a file upload feature or some other thing it's a simple quick check to see especially if it's a PHP
application just check to see I forgot the the library or excuse me the function but you know if it comes back that it's there you know that's that's a strong indicator next is denial service to the billion last attack so it's really just an entity that calls another entity that within that entity that was called there might be you know like seven A's right and then the the second entity is calling that one four times and in the third entity is calling that one four times so really you see how it can just become exponential right and just toss it next to the server side request forgery this is I want your web app I want it I want you web application
to go grab something and go do something pull something demonstrate something show me something but I want you to do it running as yourself or another thing or another with another permission set I don't want you to tell anybody I don't want any anybody else to know and then when you get that information just display it to me only right excuse me Nexus directory traversal so this is just you know navigating the directory seeing what's there getting a lay of the land essentially port scanning and self-explanatory there local remote file inclusions to see you know what files are there so next let's actually start talking about XML right so XML is just an extensible markup language just
arrived from sgml which is a standard generalized markup language it falls from the same family of HTML so it's really the the HTML is the international standard for defining markup to describe the structure of different types of electronic documents all right HTML being one of them so actual web pages it's software and hardware independent and it's extremely lightweight so there's a simple misconception which you'll see here in the next couple slides but I'll actually show you what a very simple XML file looks like but it looks extremely like HTML but the the core focus and the difference between the two is that XML holds data whereas html's job is to display data right so couple displaying
data with CSS stylesheets and then you've got a pretty hopefully if you know how to style you know website so so what uses XML right so we have Microsoft Office products so this is spreadsheets Word documents powerpoints Apple I work open offer a Libre Office are you seeing the trend so like all these office documents have adopted this new standard which is the OpenOffice standard SVG images are also XML so if you were to really look at these things you would see XML structures and data X HTML and X CSS is HTML and CSS written in XML there's a matter of time someone was going to build it and find some useful it html5 derives from XHTML and X CSS
the RSS and atom feeds are also XML and then you can also use XML through sip and rest web services right so with all this background knowledge now let's actually talk about classifications right so XML has two fossa fication z' it's either valid or it's well-formed so all XML files must be well-formed so well form means that there must be a root element so in the next slide you'll see I will have a root element so it's one element that houses atma this entire file it could be note it could be file it could be whatever you want it to be doesn't XML doesn't care as long as it sees that this is the root and this is
where the root ends right yes
mm-hmm yep so then again if it has a root element obviously it has to have a closing tag so if you have an open tag you need a closing tag right just simple HTML tags are case sensitive and must match right they must be properly nested so exactly what you were saying earlier and then all attribute values must be quoted right so if I say that this is gonna be a string of some sort that string needs to be quoted so it can be interpreted as such XML does not require document type definitions but they can and most definitely do use them so the exploit that you'll see today the proof of concept today you'll you'll see that I
am using a document type definition and well-formed just means your XML file is correct syntax so this is the basic syntax there's a couple more rules if you want to go check out and actually read the manual and the worker that developed XML if you are one of those people then I have the the final slide that's also on my website has all these resources that you can go do for further reading right next is the valid right so valid is what happens when you have a document type definition so if you declare and actually I think this might be a little bit simpler if you declare this document type definition here right XML doesn't even try to guess what it is
that you're the structure of your file or whatever is parsing your XML code right so it says oh you have a document type definition well let me go to this document type definition and understand how you're structuring your code here right so I know what all of this is so I see an element of note should have a two from heading and body section in it right so note here being the root element and then the element two from heading a body is PC data PC data two stands for parsed character data it just says what's there print it like if you can understand the characters within it XML supports Unicode so just go ahead
and print it right so going back here is the exact same that I showed here the only difference is is that there's no DTD right so again like I said you don't need a DTD but you're leaving it up to chance for whatever's parsing your XML file to understand XML and mate and make sure your stuff is written well right so here we have a declaration of the XML version of 1.0 so for my first candy bar what is the latest version of XML and take a guess 1.1 who said that you got it so you can come take your pick up candy up here whatever one you want because if I throw it I'll just I'll nail you and it or I
may miss you completely and hit the person to your left so here you can also set the encoding so you got utf-8 utf-16 and then the standalone so standalone means there's nothing else there's no dependencies anywhere you don't need to go search for it it's all right here right so then we have our note which is our root and then two from heading a body so we have a note from Aubree to keke with a question asking do you love me right so again well-formed example valid example is the exact same note the only difference is is that I am explicitly stating what each of these elements are right so again if it's well if it's
well-formed then it's good if it's valid and it passes the check then it's automatically assumed to be well-formed it's anybody experienced in the room see an issue with us it's automatically assumed that is well-formed right so now let's start getting into the actual xxe exploitation all right so there's three types of attacks you got in-band blunt blind and out-of-band so you might hear these terms you know used around when talking about exploitation so in band you can essentially think of this as it's within the same browser or a terminal window that you're shooting code to write blind is you're all you're gonna get is an error so then at that point you're blind you have you don't
know you only know the errors that you're getting back and through enough errors hopefully you'll be able to get a lay of the land and understand the application that you're dealing with lastly is the out of ban so you may upload a file for something or you may push like through a curl push something to your server to your web server and not get anything back from that same terminal window but you might have an in cat or netcat listener that's waiting for a connection back alright so again here's an in band so this is an example I just grabbed off Google Images of an ex sexy attack using burp suite right so you crafted this
payload it sent some stuff up just to get the etsy password file and then it was the server responded to this within the same window using quotes right next is example two is blind so they try to do the exact same thing again they just sent some random cat just arbitrary commands to the server just let me see what I get back in and you get some error and then some UID that gets back right bless you and then lastly you get out of band right so here we have this Etsy password file that is sent using this login form here and then this is supposed to represent like a netcat listener or terminal of some sort
so here's my callback and then we get to the fun stuff so demo it doulos alright so I made a small sacrifice to the UH you can't see that so I made a small sacrifice to the demo gods last night so hopefully this works if it doesn't work it's all good because I recorded this alright cool so here we're gonna walk through doulos real quick so I presented as Abbie sighs Augusta and I had like some super cool font that had like ghosts and stuff that's why this is orange I had like ghosts and stuff coming off of this this ASCII art loves ASCII art right also fun fact I had a web server selling over speakers
today I had a web server that I my original payload was a dot docx file so it was just a Word document and it worked and then two months later it decided it didn't want to work anymore and I spent like a week or two trying to figure this out figure this out and then I said all right I got a pivot I gotta find something else so then me and Miller came up with this dot txt file and then we just threw this in here made it experimental because you're still playing with it I did not so this tool is on github it's private right now I forgot to set it to public so probably
within the next day or two as I traveled back to where I'm going all my flight so I'll make this public so you guys can poke around and look at my terrible code so anyway so we're gonna create an XML dot txt payload right so we're gonna choose two and what is the IP of your server that is hosting your DTD so I'm just going to do a spike on simple HTTP server on my local machine so that's the IP of it what is the listening port of your server that is hosting your DTD by default that is 8000 what is the IP you want the victim's server the callback to so again that's gonna be the same IP and
then what does the port 1 through 37 because we're elite all right so now we've got it creates our payload spits out where you where it saved and then same thing for your DTD file right so now we're gonna move to our payloads folder do an LS and here we're looking for this actual payload exe which is right here awesome no errors right so now now we're gonna actually start our Python simple HTTP server so something else to note so me and Miller also decided to do this to build our developer chops back up because I haven't coded in a while and he hasn't coded in Python and quite some time also so he wrote it in Python 2.7 and then I
started playing in Python 3 and we couldn't figure out why it wasn't working for either of us and then after some finagling in the python environments we finally figured out like oh you're using Python to syntax and I'm trying to run it Python 3 and it's just not working so I said alright we're at our first crossroads what do we do right do we make it backwards compatible or do we force people to new standards we chose to do we chose to force people to new standards but if you use the Python environment super simple to switch it right so now we have a Python server that sets up also fun fact when you set
up your Python server wherever directory you set that Python server is now your root directories for your web server didn't know that so found that out which is super fun it's like why is they not finding my DTD Oh how do I set a direct route path oh this is how you can do it right so that was fine next we're gonna set and in an Inc hat set it to verbose so show me everything on the screen set it to listen on port 1 3 3 7 awesome so now we have in cat listening on port 1 3 3 7 willing to accept anything that comes its way cool we're now staged for this proof of concept for this attack
right so now let's we're in our payloads folder so now we will curl this payload our curl the payload text to this IP address right so my machine is gonna push this file to the web server for it to interpret so what's on the back end is just an extremely simple PHP XML parser and it's just waiting for XML to get parse right so now we're gonna run it so it's now curl is waiting for a call for something to come back right and it's not gonna get it here here again is our server so if we got an Apache went back and look at our Apache logs or whatever whatever other web platform you're using we see that we get
a get for evil DTD and we get a 200 that's exactly what we wanted so it grabbed it - it grabbed a DTD next you get a whole bunch of gibberish and then we see we now have a call back from somewhere think it yeah so we get a we get a connection from dot 131 on from port four seven zero nine eight and then we get a base64 encoded string super awesome so what do I do now well now you can go into Python write import base64 right so we're gonna import the base64 library and then base64 dot be 64 decode and now we're gonna decode this base64 stream and now we have the Etsy password
file of this of this machine right so looking back now I guess it's important to note that our payload was supposed to grab the Etsy / password file of this machine but that's arbitrary that could be deci shadow file that could be you know it really any file that you wanted so with that proof of concept works this parser is vulnerable to xxe right so now let's go back to our talk alright so we just demonstrated this tool that does this thing that will be public later and it now you know rains from the heavens everybody's high-fiving each other right red team did their job offensive security is cool so what does this mean for your for your defenders right well
in with this defense that you're about to see comes limitations of this exploit just with any other type of exploit it always has its weakness its Achilles heels so XML parsers can break if they don't understand the characters they encounter in your XML / DTD files right so in developing the perfect payload to craft for this tool it's why is my payload not being crafted like why why is my exploit not working right and it goes through trial and error of perfecting you know your actual payload stuff right so that code that you're actually putting in there so see data is another way is similar to the PC data but it just says if I have if I
wanted to grab a file that had characters in it that could not be parse through HTTP whether they be escape characters or something you know and I only get partial or nothing because HTTP is just like I don't know how to handle this so I'm just going to toss it to the side you know what can you do well you can get a little square a little creativity and innovation comes in and you can say well I want you to craft I want you to start this seed data right with start and then end it there and then or create another entity called end and then another one that has all and then within all include this right here
right so now I have now this is exactly what it will look like right so xml knows c data is just execute this right here so file st /s s tab and then parse it down here so put all of this together right it's not as clean as what i did before but it it's it is a way to to manipulate your xml parser to give you what it is that you're looking for right next you know again XML parsers can break if they don't understand characters they encounter and your files if it's a PHP based web application you can base 64 encoded which is how I was able to get that C / password file especially with
the slashes the back or backwards or forward slashes one of the slashes to get through right you got the example in the demo so now how do we detect slash prevent so in talking to a lot blue teamers and and just in my own experience I've I've kind of gotten more from let's keep the bad guys now to a mindset of keep the bad guys out too detecting detecting bad guys are in malicious users or whatever and with that I've I've thought about it and I was like well adversaries have something that traditional people and just generally everybody don't have we they have more time they have more energy and they have more resources so I for one am
juggling like six or seven different projects right now and whereas this adversary might only have one project and it's me right so whereas they can dedicate 12 16 hours a day to why one of my projects I can only dedicate maybe 45 minutes a day so again they have energy time and resources that I don't have so with that being said I'm focusing more on prevention how can we our excuse me detection so how can I detect right so everybody's heard the stat you know adversaries are typically in your network two hundred plus days right before being being detected well how do I get that number down from 200 plus to 90 to thirty to thirty minutes
right so how can i how can I get such a well-oiled machine that is my network in my applications and my stuff down to that level well for this particular case in xxe the first thing you can do is disable the use of external entities right if you're developing custom made XML applications or custom applications that utilize XML to transport data so they could talk to one another I really don't see a need for you to have external entities hosted on someone's github page right you know take that little due diligence and just say well if I have to use external then make it internal right the the next one is verified at the XML
or the XSL which is file upload functionality so if you do have a file upload function Allen your web app is is income it uses it validates the incoming accent XML with XML schema definition right so your watch what your application is expecting to receive is actually what it's receiving so that's a you know that's just an XML way of input validation right and in last patching upgrade your XML parsers using one of the underlying or in underlying OS with the latest version of PHP five if you can support it go to PHP seven if you tested it within your web apps right Oh boss has a super awesome list that continues to grow on
how to defend against xxe in a wide range of applications Java PHP there's even iOS that Olas is covered right so now for the blue teamers and for the red teamers in the room to kind of get a general a little bit better understanding in what you're defenders are actually doing and thinking about how about any content type header is coming across text or XML or application XML when they should be JSON right so typically what I've found in my research and just talking and reading other people's work is that a way of getting around are exploiting these web apps as if they're accepting JSON right so it's super simple just to change the header
information and see if it accepts XML most of the time it does any outbound requests from your web server web app that you shouldn't write so that's a kind of a self-explanatory one if like why is my web server talking to IP address directly like you know hard-coded IP address or you know a random random domain name right so my web server should only be used for file uploading it should not be talking to anything outside internal network right is there any use of basic c4 in your environment right so this one can kind of vary so working as a sake analyst I saw we would see basic c4 stuff come across right instantly and
one of our rule set to a flag I go investigate decode it it's a PowerShell script to upload a remote server somewhere right and they're just like straight pure go out to windows and update yourself right and it's like why are you why are you the administrator like basic C for encoding your updates you know just go out right I you know that's a little suspicious and then is your parser accessing directories and files that it shouldn't right so if you don't limit why is your web server that doesn't have any login authentication whatsoever there's nothing to login to there's no portal why is it accessing the Etsy password file right or why is it accessing areas of your own server
that you shouldn't really be paying attention to or I shouldn't even be touching excuse me not paying attention to you that's bad language you know like the root directory why's your web server going to the server directory not the web root directory all right so with that in mind let's move into the red blue and purple teams and how they can actually use it so we kind of just covered the red team's and we cover the blue teams so there's not a lot of offensive security people in this talk and that's because it's not really sexy alright xxe is not a you know it's not going to get me root it's not gonna get me shell immediately it's not gonna you
know it's not gonna give me that rcee you're not gonna see you know in today's age it's been around for you know at least a decade now this exploit you're not gonna see you know fifty thousand dollar bug bounties go out for this type of deal right but there are some pretty cool research to has been done to show that this can be done this exploit can be used and you know route more in one way of just like give me a shadow file give me a password file this it can be used more for you know like enumerated an internal network that you otherwise can't write it could be a you might have to send a lot of XML files to
this thing for the parse and execute and such but you I think you'll be surprised you know the the what you can do with this and utilizing this really is more about your imagination right so through the red team's eyes this can be used in an adversarial engagement commutes for intelligence gathering obviously it can be used for threat modeling right so if you're dealing with a web app why not throw this on your threat model and see if it's excellent you know applicable right vulnerability analysis is kind of the same thing and in exploitation and employs post exploitation right so it can be used in all of these manners that we've already previously discussed again
less likely to fine our see it's more for it's more mostly used for file inclusion and pivoting to other systems right so I'm able to get in through web server this way and then I'm gonna move to your database server what either weather whatever else is your target right it's more of a way in and a lay of the land right so it's kind of a passing through you're limited in options for exploiting webmaster xic given the protocols that you're using there are other ways you just need creativity right innovation so this is where you get to put your fun hat on and say hmm I wonder what else I can do right so again
let's talk about more about the blue team's eyes right so 200 days how do we get it down well we can use the loop of course so observe orient make a decision in an act so acting is important but only if you do it in the right way right so sometimes you obviously don't want to kick people out of your network immediately cuz and you'll never really know what their true intentions or alright so I recently just finished reading a book called the Cuckoo's egg and if you never read it's by cliff Stoll I highly recommend that you guys take a look at it and check it out it's a pretty simple read it doesn't go way down in the weeds
is an astronomer that wrote this book right so it's it's pretty good and there's even I found surprising today that it's even applicable a lot of the lessons learned in this book and how much it applies today from good taking good documents chain-of-custody and your logs and such you know just really an understanding of how the federal government works in the various agencies and how they still today don't work as well as they could together so I encourage that but getting back to this so you see here that we were using base64 to encode our results back from this web server right so ways that we can you also saw that if I saw that in
the clear I can just snatch that decode it myself and say oh I know what they got I now know where to go but what if I were to encode that 64 then encode that 64 and then encode that 64 then encode that one right there's research shows that the more that you encode something the more the exponential the size will go each time right and if you're already operating on an extremely limited network with a lot of latency right moving a 3 3 Meg file 5 Meg file might not be the best way forward especially with text right so with you you encode it so this is just one example that I thought of but the obviously the more
you encode it the bigger their size and the stronger you're gonna get caught alright so again blue team that's another way of looking at it so xxe 3-d eyes - the purple team right so for my necks I have a lot of candy so for my next candy who can tell me what purple team is makes between blue and red come pick your candy choice right so ecstasy three eyes at a purple team right so we'll just start in a blue so blue team's mostly focus obtain situational awareness of your environment right networks hardware devices users user skill levels you know organization doesn't you know the whole nine yards your key thing is to detect investigate
analyze and mitigate prevent the threat whatever the threat is reka gonna be hardware could be people could be anything and in understand evaluate and then mitigate the risk right so that's really where your blue team comes into play is mitigating that risk to the business owner of your organization and then red teaming goes a lot different it goes a lot deeper excuse me than just ones and zeros right so who can tell me what the neck are where the term red teaming came from wants to take a guess
Tiger teams no it goes it goes way deeper than that way for their bag come further than that there's no permanent revolution here deeper than that maybe maybe so so red teaming the term red team comes down comes from the back in early Catholic days like when the Catholic Church ruled the world for for sainthood for people who were going up for sainthood and the Cardinals would come together and they would discuss amongst themselves who would be deemed a saint it was in the view of the Catholic Church that everyone gets a voice to include the double right so the term red team where that term devil's advocate that's where it comes from so that hurt
there was one person in that person's soul job was to try to discredit every single act that that person did to deny them sainthood you're acting as the adversary that's where the term red team's come from right so there was no one's there's no zeros ones and zeros wasn't probably around then I wasn't there I don't know but I'm assuming but red teaming itself is is significantly deeper it's it's so much more deeper there's there's physiological aspects of it there's sociological aspects right so if you had a problem from adversary or competitors perspective right utilizing alternative analysis and again acting as devil's advocate purple team man which is perfect because I have a blue dot and a red dot and they make
purple when mixed together right so purple team is used to demystify each other's operations right so in a lot of environments red team goes off and does red team things and then they do red team stuff and they and then the blue team goes off and does blue team things and they do blue team stuff right and it's this cat-and-mouse game where the cat and mouse never meet ever right like physically never meet in the same room and if they do it's typically the red team and they're leaning back because I got their feet on their table saying you know we got you here's a report here's how you keep us out we'll check back in six months right we're
we're purple team comes into play is when you say all right I'm gonna pair a blue team member a defender with a red team member an offensive person and piece them together and I'm gonna let both of them come to the table with their own play books and let them just execute their play books and then they communicate with each other right so it's this environment where it's okay to say I don't know to say here's what I'm doing right I may not show you my entire playbook but I'm gonna show you the vast majority of it right so that you can get a better understanding of what I see and where I come from on both sides right so
you've got your blue team person saying well I see you ran this attack I'm showing this NetFlow data I'm showing this peak I captured this pcap I'm doing these things here's what I'm seeing here's what I'm here's my indicators that I'm popping off on here's here's what I'm getting from this attack or I'm not seeing any of this man can you teach me more about this so I can learn to detect this type of stuff right it enhances communication flow between your two teams so it says iron sharpens iron mentality and you know coming from the army communication is everything right especially on the battlefield so the greatest way to cause chaos and mayhem is to prevent two members of the same
team just kill their communication and they can't communicate especially as an officer in a commander level when I have to maneuver my people on the battlefield and I can't communicate to them to direct the fight that becomes a huge huge problem for me right so putting these two people together side by side and and making them communicate with each other will only make in my opinion your organization better if they both come with a good attitude now they come with a bad attitude then you know other than a heavy hand you will do this you know there's nothing else but again that's counterproductive if you go down that rabbit hole and in each element gains
valuable skill since he's behind the curtain of the others right so red teams learn blue team TTP or tie vex techniques procedures they're learning blue team products they're learning how can I take these tools that you use and then mimic them in my own environment to create my own test cases as I test my own stuff right and flipside blue team sees these red team tools maybe cats right all these other in the vast majority doulas you should include out in their library right but they can go back and take a look at it and say well it's creating this payload or it's creating this thing right so maybe we need to be on the lookout for this stuff
I'm not creating a signature for the tool I'm creating a signature for the action right so with that what are your questions anybody have any questions we have like ten more minutes I can just stare awkwardly at everybody I have a lot of candy to nothing okay yeah so yeah it's challenging isn't it
um so PHP is my test case I I didn't test I so my ignorant is showing I really don't know anything about is other than Microsoft I was the market so I I have so that this web server is running Apache on it so I guess what might help it is PHP right but going do I have Internet's I think I have Internet can you guys see that yeah cool so
in my minute trying here you go so oh wow it's cheap seat right so in a lot of these it's really it's for a lot of these it's it's pretty simple you're really just like adding one line to your config file and say don't allow DT DS or analyze certain things right only allow these things right Oh wasps again does a pretty good job of like highlighting those and say include this to prevent this obviously if you can so in in regards to testing like Java applications and other stuff I haven't gone that far in testing it's most definitely on our roadmap me and mill with me and Donald's roadmap that's a pretty good question
PHP was just the base case cuz it's what I've been playing with lately you get a candy again if you want more candy cool yes okay
so uh so for the viewers at home the question was for purple team is there a way to capture blue team stuffs and red team stuffs during an engagement and if there was a commercial product that did that as far as I know there isn't however there's nothing saying that you can't if you do an engagement with the red team and a blue team to say beforehand you guys are gonna do packet captures on your stuff you guys are gonna you know produce your artifacts after the fact you know we're gonna I mean pcaps don't lie right so if you're just gonna do full packet captures of your stuff which obviously you would need to support sighs and are the data
set or the data stores just to port these huge pcaps you're gonna generate anything go through right so in actual automation I'm sure there is that can do that piece but it's not automated so maybe you just came up with a new business right in this room in my talk you heard it here first right maybe I as far as I know no so this is again relatively new and I used quotes because it's been around for you know many many many years it says people are now starting to adopt it so it's more it's more instead of you know a new niche market it's more of a you know a leadership management perspective to
kind of just get your team's collaborating to make them sharper and make them and make your organization better if that makes sense so really again in a long way a long winded way about it's not - each team really to provide those artifacts and maybe your purple team can be your you know your white cell for lack of a better where the person that goes in between and compiles it and then generates the report with representatives from each side to kind of recreate your whole timeline maybe that's it so if you figure out a way to automate that yeah go for it
yes that's a good one yep so so The MITRE attack framework is a it's a framework created by mitre that targets Windows environments so we have the internet we have the internet yeah I spoke about that like two years ago I can't believe I didn't think of it yeah absolutely [Music]
right yeah yeah so um man they've really cleaned up this website last time I was here it was like a wiki so you see you have initial access execution so if we just click on initial access right these are all the techniques that you can do initial access so really they created this wiki that a miner created this wiki through a lot of research that says here are all the ways you can attack a network your all the ways that you can exploit a network or application or whatever right and then broken down by these things like initial access so you do drive-by compromise so within Drive I compromise it gives you all this data
you know all everything you could ever care to know along with examples in the wild so apt 19 32 37 right the list goes on and then a whole bunch of resources about it right so this is an awesome tool for your blue teamers to really look at to say well I supposed to be looking for stuff what do I look for well this is a great place to go look at you're not only gonna get ideas on how to create your signatures and everything but you're also gonna learn to TTP's of your adversary and your offensive people and in right teamers this is a great way to kind of add more stuff to your
PlayBook and more like your more to get more skills if you haven't been exposed to these things before as well so yeah thank you for that that's awesome you get a candy if you want to I know that's what you've been waiting for any other questions awesome well I appreciate it thank you guys so much [Music] [Applause]