Analyzing Network Traffic of Vacuum Bots
Show transcript [en]
all right thank you everybody for taking the time to come here and listen to me for the next 45 minutes I promise dear to God I'll promise I'll end this early if I have good audience participation right and this presentation will get interesting as we go along so that's my promise to all of you all right uh my name is Karan uh and I'm I'll be talking about clean forensics it's some of the work I did around analyzing Network traffic of vacuum bots so with that let's get started so quick intro um I work at Google I'm a security manager I'm actually my manager in this room so hello um please don't throw stuff at me
uh I I graduated from Carnegie Mellon about eight years ago now uh spent a good happy two years in Pittsburgh um I also try to blog around security engineering interviews and that's the link for everybody if you guys are interested um in my spare time I also review like conference Journal papers like to give back to the community and travel and give talks like this so what are we going to talk about today right in short we're going to look at why even research vacuum Bots like what is it about them that is interesting to the security community we're going to look at functionality I know some of you actually let's do a poll how many of you have a vacuum board
or want to have a vacuum board oh wow awesome okay how many of you think they are secure
so I'm seeing somebody like okay I see only two hands that thought they were secure brave brave people okay so we're gonna talk about functionality just so because everybody's on the same page right there's going to be some Basics that I'll cover uh then we'll get into the more fun stuff right we'll talk about how each and every one of you in this room can conduct the same research at home right uh we'll talk about some of the security and privacy concerns that that came out of this research and then I'll walk you a actual real communication with a vendor and I'll show you how that went that will be the most fun part of this
presentation all right cool so let's cover the basics really quickly right why talk about this vacuum bath so I you know took this diagram from grandviewresearch.com basically if you look at this graph it shows you the you know the upward trending Market of vacuum box so estimates say that the market is growing every year by close to 20 percent by 2028 this is going to occupy 15.8 billion dollars and by 2027 don't quote me on that we'll have 60.9 million of these vacuum Lots just imagine these tiny things they're all over who are the key players right who are those manufacturers that dominate the market dominant is the wrong word but let's let's look at some of the market
segmentation right so if you see on the right the right hand side shows you the level of consolidation that's at the top right so as you go up the market gets Consolidated and at the bottom it's more fragmented in this case they're right in the yellow zone like close to the middle a little bit at the bottom right this tells us couple of things right it's not dominated by one particular manufacturer also it's not super fragmented right so basically everybody can build their own and sell it in the market and there's going to be some people who are going to buy it right this is a very interesting observation let's remember this so with that understanding let's let's
talk about functionality what what are Bots doing for us okay so each bot can have different cleaning modes right one is an auto so you tell the bot hey go clean this and it does its job right uh it tries to figure out where it is maybe map your room all of that fancy stuff right it can also actually do Edge cleaning so in this room for example if you have a bot it can go along the edges that's an interesting feature you can do spot training so if somebody spills something they can just say hey clean that's what or you can go all in and say I'm going to direct you at every step
you're going to turn left here turn right there and you could do a manual clean as well right a lot of bots that I research did offer those features okay some of the more um advanced stuff is schedules so for example you can say every Sunday 9am clean my house it'll do its job um a few of them have like Health monitoring and what I mean by health is not like our health as in humans but more so of like accessories like brushes right it will tell you when to replace your brushes you know all that jazz and fun stuff there's some more functionality that comes with a bit more advanced spots like you can have floor mapping right so
this is a diagram I actually mapped one of these Bots and this was the result right so the blue dot is actually the bot right and what it Maps is like my apartment essentially yeah I'm talking about it in a conference so anyway uh talk about privacy so some of the words can also do live video which is very very interesting right for people who said the Bots are secure um anyway some of the features are offered but the live video is actually very limited I can count on my fingers how many manufacturers really offered that but it's growing all right so now with that basic understanding let's go a little bit technical right how do you actually set
up a bot you go to the store you buy one what do you do right so I tried to generalize some of these steps and show you what happens this is not always true but mostly true right so we'll go with that understanding first you have a phone right and I've kind of sorry I've kind of included some of the key components that you know exist in a home network so for example you have a phone with an app installed this app is by the manufacturer of the bot okay they'll probably have an app that you can install create an account register and do all of that jazz you have a cable modem everybody's connected to the internet have a modem
and you have a bot so these three things sit in that boundary which I'm saying oh let's call it our home network okay on the right is your external internet so that's the outside Network uh basically you can imagine a trust boundary between the home and the external internet so what happens right you install the app and you say let's create an account okay so you put in your credentials you know you choose a username password you put in some of the details and then it goes to the manufacturer website creates an account right cool next you turn on the bot all right it will try the app will try to figure out is any of the bot nearby right it's
going to do a local search this is not you know through the internet or something it's just on your local Wi-Fi and something interesting will happen in a lot of cases the bot is going to spin up a new Wi-Fi network it will have its own SSID right the fancy name for Network so it's going to say hey I'm here here's my Wi-Fi connect to me right the app is going to say okay cool let's connect and the only reason for this connection the sole purpose has been to exchange credentials for your home network okay so you're sharing your own credentials to the bot through this wi-fi network and after that when it's gets those
credential it says cool now I can talk outside using your home network I'm going to associate myself with that account I think you are my owner okay and then it's gonna connect and say okay we are all set this bot is in this home for this account really that's what happens when you purchase one of these Bots everybody good thumbs up okay cool people are nodding awesome okay let's talk about how you can set this up yourself so to not Bluff people I did this at my home I promise I swear and I took a picture please do not be afraid of the picture I know there's a bunch of wires so I'm bad at wiring stuff but this thing works
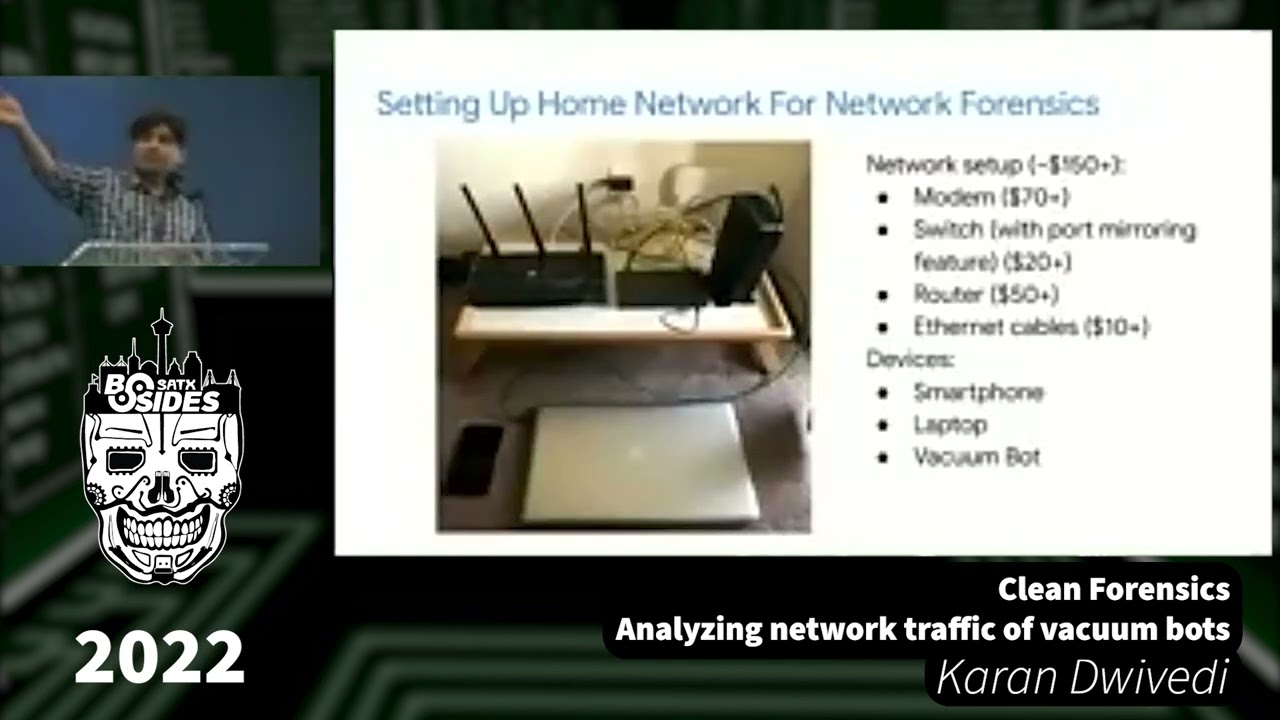
okay but I'll show you in the next cleaner version of this diagram how you can set this up essentially the key components here are the modem which I talked about so that's on the right on the on the table there there's a switch in the middle and there's another router on the left okay typical stuff and then I have you know a phone and a machine actually the set this laptop is on the screen is actually the one that's presenting right now so it's all real um the important thing to note is this setup is relatively inexpensive right I was able to do this in like about a hundred hundred fifty dollars you know give or take
let's look at this with fun icon right so here's here's the simplification of that messed up diagram okay and this this is how you can go about it so in your home network right the black you know box essentially first is the cable modem I assume that's plugged in right all of us are set correct the app is already there we are good there right the bot is powered on connected awesome there's three components that we'll talk about there's an internal router the blue one on the left there is a switch right so I I call that you know it has a mirroring feature mirror Port feature and I'll talk about why that's important and then you have a
machine which is actually running your typical packet capture right nothing fancy actually so when the bot wants to communicate out to the internet on and vice versa it's going to send a packet through the internal router that's going to go to the to the switch that's going to go out to the cable modem and outside the home network does everybody follow that trail from the left to right okay it's also gonna go to the packet capture machine because I'm doing a port mirroring on the entire switch so everything I I can see what's happening in my network through that except the phone because the phone is directly talking outside through the cable model right so this setup will
allow us to really see the traffic related to any bot okay all right we've been getting into the real forensics part so the sorry the way I actually did this is I you know got a bunch of these Bots I'm not going to name them right but I captured traffic by doing certain things after they were on so for example I captured traffic when I was setting them up okay I also captured traffic when I issued certain commands like oh Go Auto clean this stuff what happens on the network turn right what's happening on the network so I'm doing this and I'm capturing right I'm trying to figure out what's being you know what's being
communicated in and out and then I sat down with all those packet captures and analyzed them for hours to really dig down on what's Happening so here's an example right I'm not going to name any vendors or anything else in the stock but I wanted to show everybody an example of you know typical connection setup right I know this this screenshot is a bit small but I'm going to walk everybody through it What's Happening Here is the bot when it comes on and you say hey turn on it's going to make a DNS request out I've seen this generally to a Cloud Server right because it's easy to talk to and apparently cloud is safe as well
so um and then it's going to get back an IP for that particular vendor so it can be like oh like talk to me dot cloudservice.com right something like that and then it will have the IP and then it will communicate to that IP and you know get along with its life so this is a typical connection setup that happens that I saw on the network right and I have blurred out some of the things that would have identify you know vendors or anything else about it but that's typically the first step right let's look at a move example so when I took took the spot and I said hey like can you turn right I want to do a manual
clean so the command went from the app to the Cloud Server and then it was actuated on the bot on the network what I saw I have included on this slide on the right okay I'm not showing fancy Wireshark screenshots because that's a lot of text and bytes and it's confusing so I abstracted out the details and this included this can anybody in the room guess what protocol we are looking at I hear like mumbles UDP mptd like an iot format exit correct it's XML it's sort of like a super response not exactly any more guesses before I actually revealed UPnP um not really but you're getting close to actually iot protocols I wish not uh no it's not
so I think so people who said exam uh sorry XML are closed it's actually XMP yeah so what that does what does that tell us your board is actually a chatbot it's it's just like I am for all of us who say hi on Chat and message comes back that's what really what's happening I'm saying don't write and he's like yeah okay don't write there you go um and the second observation is it's all plain text all right we'll keep going let's look at a clean example because this is the most this is why we buy these things right clean stuff but when you say clean right same thing but look observe on the right
there is a very clear way to figure out what commands you send so it says okay clean Auto with a strong speed I mean yeah you for sure right and it will come back with a clean report and say okay got it right this was very interesting to me it's keep alive so even when the Bots are not cleaning and they have a connection to the Cloud Server they are chatty they are talking and that's what it is so it's gonna say hey are you there but by the way you you cleaned the house right and yes it say yeah I'm still here so that's that's traffic will be visible to you know in the network if you
actually record it and by the way this is not like this is for a particular type of Bot or a particular you know I'm not I'm not generalizing this but these are some interesting findings from the research interesting stuff because we're in a security conference what about Authentication do does anybody see a problem it's bolded yes it's pretty much in bold right yeah so some of these Bots I'm gonna say sum and stop myself there some of because this is being recorded and it's you know will haunt me for the rest of my life uh but you'll see password in plain text in some of these spots especially when they're using the sasl protocol right and I think sasl has you know an
option to set you know plain text passwords and you know the way you configure it it's going to work so anyway saw that freaked out when I said Okay I want to see more why not right okay in some of the Bots I was happy because I saw mqtt a little bit happier because it's it has options to make it more secure so you can have certificates um traffic is not in plain text so Kudos there right and you'll see Port 8883 which is typical for mqtt traffic okay status now this was very interesting this is not security but I'll get to why I'm talking about this so imagine I have this app right on my
phone and I just open the app just like you open any app on your phone like a call or or message right I just open the app and it was funny because when I did that I actually saw traffic on the network and I was like why like I'm not issuing any commands I'm not doing anything yeah it already he will talk about keep alive but this is not keep alive right so what's happening Well turns out it was actually communicating the time from my phone to the server and the bot was assuming that it's in the same time zone do you does anybody see a problem with this much it's getting the time from my phone
somebody said the schedule changes the summer if I'm from somewhere else Bingo exactly like if I go and travel let's say Europe I'm in UTC UTC time this bot in this case I was in California so it's specific time right you see the TZ equals minus seven there like the small in bold that's showing the time zone the time actually is in Epoch time so you see those numbers 1651 in bouldered right if I move the bot is going to assume it's with me all the time so it's gonna mess up schedules this is a this is an issue we'll talk about when I reported it to the vendors but let's remember that for a second
okay so we talked about functionality we talked about some of the concerning stuff we saw let's just say that um let's talk about let's summarize the the security and privacy issues so what about controlling remote controlling and hijacking can anybody hijack this watch and control them well kind of sort of maybe right because you need to be on the local network right imagine right actually remember not imagine uh all of this was on my home network right or in this case anybody doing this research is actually capturing local traffic I didn't see any way that any external remote attacker can actually get control of this but if you're on the same network you can technically replay xmpp
right and it's probably going to take it [Music] what about the app credentials remember the only way you are able to control this bot is through the app right and so if somebody knows your credentials to the app they can control the bot in on your behalf not surprisingly there was no two-factor authentication so you could just username password your way into different Bots all around the world floor plans so we talked about a little bit about scanning right and different floor plans that these Bots can scan I try to look at like where are these stored are they on the local device are they in my account like what's happening so in some cases they were stored with
the app and it's not really a network forensics topics so that's why I didn't go into so much detail here but in a lot of cases they can just be stored in the cloud okay and that's again associated with your account so again the security of your floor plan of your house is also dependent on the security of your Cloud vendor or the manufacturer the whole icon of the cloud I did not discover the good news is in my research I did not discover that you know I saw this going out of my network so you know I can say that but it's just good for us to know right what are we really relying on
Remember the Time Zone thing we just talked about two minutes ago when I change time zones in a way it's leaking my course location right it's on the network it's getting it so somebody's sniffing track traffic at my home can actually figure out which time zone I'm in in a way I see your hand up there
sorry the question is did it go off a VPN server was it affected by VPN yes so who's connecting to the VPN is it are you saying the bot is talking to a VPN or my phone is talking to a VPN and then oh my phone is talking to a VPN I have not tried maybe you can and tell me how it goes in and they'll ever talk here it'll be awesome but thank you for that I wish I had an answer though now you got me thinking but yes the side effect the side effect of this is as the gentleman here in the front pointed out it's going to mess up your cleaning schedules so if you
configure the water you know clean your house at 6 00 am not really not gonna do at 4 pm or maybe worst 2 am who knows and I actually noticed this because of that I it randomly started one day and I'm like something is wrong and it was a time zone all right video recordings we're getting close we're getting close to the more fun stuff in the video recordings I actually took a screenshot to show all of you here the traffic on the left is actually the video traffic that I observed it's very nicely done because it's all UDP right if you see the size it's almost the same chunks the same same size essentially right so if you see one
one six five one zero four five kind of the same right and it's sent very very quickly like my water shot was flooded essentially so I knew it was video and I could tell because I was actually viewing the video at the time when you examine these packets in depth right on your right the part that I've highlighted in red is actually some metadata it's not the real video data so we have some benefit there and some some security but there's stuff like hey message type start streaming right so you can kind of figure out if video is on or off in a way [Music] all right last part reported issue so I took all of this you know after several
months and then I said hey I want to responsibly report this okay so the next set of slides is gonna be bless you um in the next set of flights it's going to be a set of emails I wrote and the responses and I'm gonna let all of you in this room yes what happened all right
so focus on the boxes in red in red it shows that I'm the reporter it's actually from my email so and there's a date associated with each email right I have not faked this this is real and then I actually sat down very nicely and I politely wrote this email explaining how I found the stuff the background and my concerns around this and say hey can we get some action here because these Bots are actually deployed and people are buying this so notice the time Monday uh 18th November 2019. it's a small it's a little bit small for a few of few in this room so I'm just saying it out loud okay 18 November I reported all of the
stuff don't have to read the email but because you guys already know what we talked about right couple of things right insecure protocols we saw XMP SL we also talked about like potential Man In The Middle on the local network keep going right keep writing I don't know who read it because they'll be like really dude it's a long enough not a female course location tracking right through the time zone issue and finally floor plans again I was honest about it right I said hey I didn't find any leaks but maybe have a look right okay game time what happened next they called the cops I'm still here so [Music] no answer any any more guesses thanks but no
thanks oh wow jeez I'll be so somebody said our stuff is secure thank you for telling us okay we're actively looking into this wow you guys are awesome no response actually yes that was correct so for a month I did not hear back in fact they closed my ticket
I should be enjoying enjoyment and they also asked me how would I rate their support uh good I'm satisfied sorry well I had a lot more to say but I didn't anyway so I wasn't happy I actually wrote back and reopened the ticket I reopened and politely reminded say Hey you know um request to reopen can you please give me an official reply and I also stated the responsible disclosure deadline which is 90 days typically I'm not going out in the public like this and talking about even now actually I'm not right but I wanted to raise awareness and I was very serious about this what happened next sorry repeat oh do you mean like closing the ticket
oh okay good one sorry they close it faster I don't know having a bad vacation you know if that happens I'm just trying to start here oh this is not for my workout so disclosure this has nothing to do with my employers right this is all me I have to say that but thank you can't comment but maybe and get in trouble [Music] so I got an acknowledgment actually all right and so I'm not actually saying anybody is bad or maybe they're busy it's December right I'm not making any judgments but I'm really waiting for a good response I did get a response which is good right notice the date December 17th I reported in like 18th November right
so about a month almost you don't have to read the whole response but re focus on the bottom like the last two lines something implemented using xmpp we talked about that right which is an older model I understand I bought a cheaper one okay fine or an old one all our new models now use more secure technology to ensure user information securely like what do you mean by like use more secure are the rest unsecured in sick like what's happening I had questions and I didn't give up I mean heck this was my vacation so I followed up and I said hey no no like okay thanks for the response but you haven't really addressed can you assign
a cve can you give me a cwe something right three months later February and my break is over I'm back right back to work thank you for your concern so somebody did point out right thank you there was somebody in the crowd so you're also right so they can say thank you and say okay appreciate your feedback and they pass the notes to their app team I don't know which team that is but okay should you have any future questions please let us know I actually do a lot I have a lot of questions hey I'm not getting answers so okay oops March 30th so we're kind of ending the you know the break and stuff and I was
like huh is there a response like I've waited more than a month since the last follow-up I reported the issue in November last year it's been four months is there a response have you guys done something blah blah blah right typical stuff in July I was I was tired I I was done man July 28th I got this reply and they're like thank you for writing we have escalated to the relative Department I don't know what what department like I anyway thank you for your patience I'm very patient seven months in eight months in what happened next final question from me lawyers okay good guess sold it to North Korea I can okay
by Design sorry what insecure secure foreign nothing happened actually I'm still waiting for a response that's what happened in conclusion um and that's what I wanted all of you different right I wanted to walk everybody through a method of researching on your own this is this is not you know all fun and games this is serious stuff right I would say that the future models right and this is 2019 2020 time frame we're on the pandemic I have nothing else to do than this so as of today there are more secure versions out there right there's very very few plain text but still you can still repeat this methodology at at your home for just 150 bucks potentially and
figure out all this stuff by yourself for manufacturers it's very challenging right they may use insecure protocols on configurations maybe because they want to ship the Bots really quickly or they have some deadlines right so this is not like saying vendors are bad just I'll be very very clear right I actually appreciated the response but the the concern I have was there's no way for a end user consumers like all of us to actually get guarantees of security when you're buying it off the shelves can you say this is fine right now I cannot right this can be replicated at home and finally it's kind of challenging to talk to vendors I would say that it's hard to
get a timely response fix is also debatable right so with that I'll leave all of you and thank you for keeping it clean
[Music] I had promised I land early so was I on was I on okay and I'll take questions and if you want to ask reach out to me later that's my website uh feel free to reach out anytime there's links to little Twitter Twitter not linked later Twitter LinkedIn all of that but yes I'm open to questions if people have in the room yeah you can do it right now and I'll give you the microphone so everybody online can hear it too
sure for sure this one or the previous ones uh all right go way back foreign have you found that any of these devices were adverse to being set up without a network connection as in to be able to put the device down start it and then proceed without establishing that connection in my research I did not thankfully uh it was it was always like I initiated the connection association with my account and then they started to communicate I didn't see them in the while just talking out that would be really scary yeah thank you thank you we've got one question from online yeah we have one more online oh you've got one question online sure it's uh from your experience what
portion of these Bots utilize certificate pining to harden against reverse engineering slash interception that's a good question I actually uh when I saw like secure traffic I did not go into further detail about it uh that's a follow-up I can take that I can check that but if it's secure like if it's actually doing stuff that I'm not using plain text it's very hard to research further all right three good oh there's more all right thank you so much





