G1234! - Sex, Secret and God: A Brief History of Bad Passwords - Kyle Rankin
Show transcript [en]
my name is Kyle Rankin by day I handle infrastructure and security for a credit card startup called final in my free time I do a lot of technical writing so I write a lot for a Linux Journal and I've written a number of books over the years mostly on Linux and system and type stuff although more recently a lot more on security so I was so close to having a copy in my hand I just came out with a new book Linux hardening and hostile networks that a lot of this talk is based off of the first chapter in that book where I go over I elaborate weight and way more detail but anyway yeah so that's sort of like what this
talk was was based off of and my background so first thing to say so this is a password track right and so there's some hardcore password crackers maybe even in the audience but definitely in the building this talk is not about advanced password cracking this talk is not aimed at advanced password crackers this is a talk for general audiences just about anybody we're not getting into like hardcore technical details of that stuff it's really more about sort of the history of password policy I'm in the failure of password policy so just to let you know ahead of time so what is the talk going to be about so here's the agenda so brief introduction of it I'm
gonna talk about RMS in the MIT password revolt which may not be on every front of everyone's mind as far as password history goes then I'm going to talk about sort of the Golden Age of computer passwords like you see in the movies we'll talk about the dot-com boom and how that changed password policy now that everyone was on like a ad domain and how they changed password policy then I'll discuss sort of what I call the xkcd password Renaissance that started people thinking about passphrases um then I'll dive a little bit that will be sort of the it for password policy and I'll talk a little bit about some some semi modern approaches to cracking
I'm sort of based in the rock you hack era talked about a couple of new approach more modern approaches for password policy touch on 2fa as well password reset attacks and then little conclusion and take questions at the end all right so if you want to hack an account you guess the password it's been the weakest link in security for decades now most people that are in security kind of recognize this and a lot of people in security blame the users but it's not the users fault it's very easy to blame them for a lot of problems but it's this is not their fault it's largely in my opinion the security industry's fault first that's been been passed down to IT who
trusted the security team who then pushed it out to the rest of the users and the rest of this talk will sort of expound on that notion but that's why I blame for it the reason is the security researching industry especially for the last couple of decades up until recently we're focused mostly on theoretical attacks and in other aspects not just password a policy they still kind of focus on either theoretical attacks or hacker movie kinds of stuff and largely ignore what real users will do with security so as a result we've been giving users decades of really bad password advice and policy and then kind of be surprised when they follow our advice and then have passwords that get
correct so in this talk I'm going to talk about first how do we get here how do we get to the point that we have sort of the password mess that we have now based on these decades of bad policy then talk about what the current threats are against passwords today more or less and then talk about what some things that we can do today they try to mitigate those all right so we'd like you normally think of especially if you've been using computers relatively recently you sort of assume it has a password everything has a password this is a security conference people think of computers having passwords but computers didn't always have passwords not just
because they were insecure but passwords weren't always necessarily viewed as a good thing for a computer to have and my favorite example of this is Richard Stallman who if you're familiar with free software in the open the free software movement and open source software he is the founder of the canoe project and the free software foundation and a lot of the open source of free software that you use sort of can be traced back to his work well he view passwords as a means of control not a positive thing most people know about him from his open-source work it's free software work sorry RMS and his free software work but most people don't know the rms is also a
password cracker so to tell the story RMS joined the MIT AI 8 lab in 1971 and he and the team were working on a computer system there the system they built they built intentionally to not have passwords and so here's what he had to say about that we didn't have any passwords the reason was that the hackers who originally designed the system realized that passwords were just a way the administrators could control all the users so they just didn't do it they left that out so he sees it as a way of like top-down like control over people so at one point this horrible thing happens where they put passwords some of the administrators start putting
passwords on the system so in his words when they put passwords onto one of the machines at MIT I didn't like it so I figured out how to decode the passwords so I sit and then I sent messages to people on the network this is probably this is back in the day so this is probably using finger and things like that hello I see that you've chosen the password mumble how about or whatever the password was how about if he just type in err for a password it's much shorter and so he was both like letting them in on the fact that the security was worthless as far as how they were storing passwords there
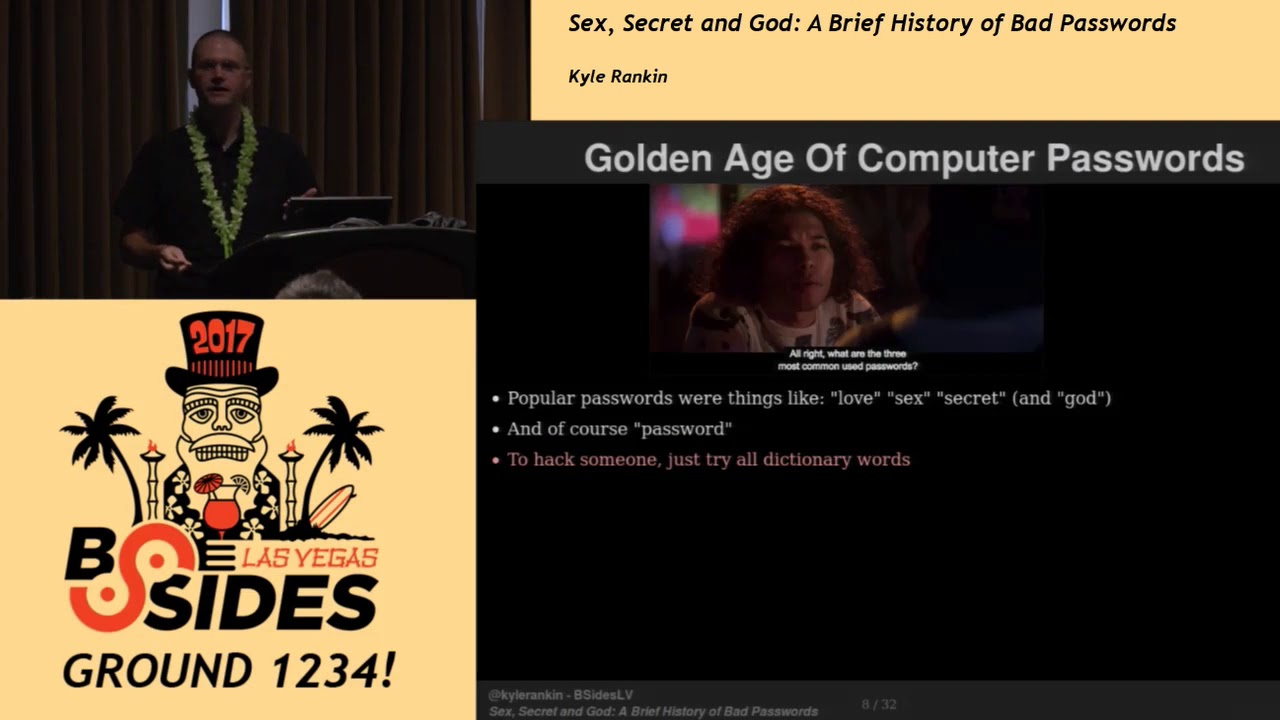
and also trying to subvert the syste Thorat aryan control of passwords on the system by getting them to just have entropy also the system accepted enter as a valid password so that leads us into the golden age of computer passwords so in the beginning a lot of people treated computer passwords like traditional passwords like the kind of thing you would do if you wanted to get into a speakeasy or things like that so they were generally like single words because you know many computers actually didn't support passwords longer than eight characters even computers that claimed to accept passwords longer than eight characters and some semi modern systems actually will truncate it after you type eight characters so you may
think that you can paste it in this crazy password and there just cuts it off it's fine also some computers ignored case so lower case password upper case Pass where it's all the same to it so it doesn't only mean you can mix case all day long and it treats it as the same thing so as a result of this you know most passwords were single words they were generally something based on a dictionary and they were simple they were easy to guess also people when you ask them to pick a pass where people tended to sort of gravitate around the same passwords for things and so there's like certain passwords they were very commonly used so this resulted in
hackers having the sort of inbound knowledge is sort of like this domain knowledge that was passed around of commonly used passwords so for example popular passwords were things like love sex secret and of course God and this was sort of like the hidden handshake if you are a hacker which you would study and memorize where all of the commonly used passwords that everyone picked and when you're cracking somebody you would try those oh and of course password has always it's been a classic password from the beginning so if you want to hack somebody one way to do it is just to try every word in the dictionary and you'll eventually get in but if that's too slow
what you would do is you just guess words that were important to them so those things might be spouse names children pets sports teams things like that and this is also the main way that people get hacked in movies so for instance if you wanted to break in to the Seattle School District you would the password was pencil which makes sense because it's a school you know if you wanted to break into the DoD system responsible for war gaming the password was Joshua because that was the name of the son of the of the primate the main engineer of the system if you want to break into the Gibson he would just type God because that's one of the common
passwords so that sort of thing the classic era but around the time you started getting tools like John the Ripper that automated the process of password cracking and as computers that faster so the dictionary attacks so these these password policies that were just based on allowing single words didn't really work very well as a result IT department started responding with password policies not allowing but they will consider weak passwords to be added to the system this was also sort of comes around the era of centralized windows administration that made this a lot easier if every single system had its own unique password every computer that someone would need to log into maintaining a global policy across
all those computer was challenging but this is the era of Novell NetWare banyan vine then you've got it any Banyan vines people in the house yeah ok that's ok so or they were more popularly active directory right and that allowed IT administrators to get a list of what were approved password policies that security experts said would create a secure password and enforce that across every computer across the board and most of the advances in password policy correspond with advances in Active Directory features or other features for central administration these policies were well-meaning I mean the goal was to protect the user from picking a password that someone could guess but they were misguided and users generally hated them
users still generally hate password policies if you talk to anyone who works for any decently sized corporation and ask them about how they feel about the password policy you'll get an earful and you should because it's they're usually awful so here's some examples minimum password link so the policy would be something like passwords must be at least 6 characters the reason is that would make a dictionary attack take longer than say a 4 character password right so you have to at least have six characters in theory because the theoretical combination is between 1 and 300 million combinations so on paper map the math tells us that you know if 1 million if you allow only numbers if you
allow out like alpha and characters this goes up to 300 million that sounds like a lot of combinations but what our users do so they picked QWERTY they pick secret they pick password and 1 2 3 4 5 6 totally fit the policy what are the attackers do they took their dictionary and removed all the words that were shorter than 6 characters and tried the rest and they got it so now we had a response to that which was password complexity rules so new policy on top of the existing one is now passwords also must contain at least one uppercase letter the reason is that increases the total number of password combinations and it removes passwords
that are just numbers so now we get you know we get up to potentially 19 billion combinations so what did users did they pick QWERTY with an uppercase Q secret with every case and password with an uppercase P right totally fit the policy attackers they took their dictionary and they uppercase the first letter of every word in the dictionary and tried that and they got in so IP responded with more password complexity rules so now the password must contain at least one uppercase letter O and one number two because again it increases the total number of combinations if you do the math you're really making it hard for hackers because brute forcing that we're talking 57 billion combinations no way
they're gonna get in write on paper it's like atoms you start talking about atoms in the universe right so users pick QWERTY and they put a 1 at the end secretly put a 1 at the end and password with a 1 at the end I like the refer to this is like a the password mullet because it's an uppercase in the front and a number in the back so what did attackers do they added 0 through 9 to the end of all their dictionary words and then ran through the dictionary and cracked all the passwords so now even more complexity so ok that's not gonna work so now the new policy is now the password must contain at least one
uppercase letter in two numbers why well because people were just adding a number to the end so if we make them add two numbers to the password then that increases the complexity they're more likely to put it somewhere else again the theoretical combinations are still 57 billion we're not increasing decide the minimum character length but we're saying you have to have at least two numbers to protect against you're setting a number at the end so users picked QWERTY 84 secret 69 and password one more so what attackers would do is they went to the dictionary where it's added two digits to the end of the dictionary words and in particular if you wanted to be faster if you knew something about
the person you would pick significant dates from their life because usually two digits map pretty well two years so like when were they born when they graduate high school college when are their kids born things like that we didn't stop there so now okay fine but so now we're going to use math to save us so passwords must contain at least one upper one number and the symbol Y because it adds an order of magnitude to the entropy and also stops users from just adding numbers to the end because now they have to throw a symbol somewhere in their relationship right the theoretical combinations now jump from these 57 billion to 782 billion again you start talking to people in
this era about this policy and they start talking about every atom in the universe being a computer that can crank through this many passwords and how impossible brute forcing this is so the pet users picked QWERTY 84 bang 6 or 69 Bane password 1 1 bang right attackers added a few symbols to the end you sort of start to get where I'm going here so this also led to another interesting phenomenon specifically went IT people in hackers which was the lead speak so the problem with these complex passwords that everyone now had to do is that they're really hard to remember so I see people are like well I know a clever way to do make a memorable password what I
will do is I will take a dictionary word and apply leet-speak to it and boom instant password that passes all the complexity requirements I can remember it but no one will ever guess it I every IT person did this and every IT person also advised everybody underneath them and every user that they were representing this is how you pick a safe secure password so for example if you're not familiar with lead speak password lower case becomes password like that with that sort of transformation there's some variations on that so if you need symbols for instance it would always be this instead so this was the natural admin password at a job I had before just full disclosure that's how
prevalent this wasn't so it turns out if hackers also know how to speak leet speak yeah it's weird and it turns out computers are really good at applying formulaic transformations to words even though you have to use regular expressions to do that they're really good at doing that so they did all right so that's fine now we have the showstopper that's going to stop everyone in the tracks which is password rotation which everyone loves the password rotation so the policy is now passwords must be changed every three months right why well we need to lip a couple reasons - one we need to limit the time it takes to crack the password before the password changes so for
example if you're saying yeah a really sophisticated attacker might be able to crack that in six months so we'll just change it every three months there's no so then by the time they're halfway through cracking it boom new password done no way the other reason was there is this there's this idea that if a hacker somehow got into your system you would at some point in that three month window changed the password off from under them and they would just be completely locked out of the system and there's no way they could get back in right those are the to me if you ask people about password rotation those are the two main reasons they'll give you so
users would pick password one bang and then the next month or the next three months they pick password to bang and password three bang what attackers would do is they would guess one of the weak passwords and once they guessed one they wouldn't know what your scheme is once they know your scheme they would be able to apply that to guess what your future password was the other thing they would do is you know usually when someone attacks an account one the first things they do is put a backdoor and so they don't have to get in through the normal way so that doesn't really help with that but there's a study that I actually
link to at the end of the talk this is a number of years old it's over a decade old now but they there's as I forget the school now but they did a study where they they they were able to capture all the passwords that people selected that had a password complectation requirement and they were able to accurately guess the next password with about 70 percent accuracy if they knew one or two of the previous passwords so as you might guess there's some problems with these policies right so essentially it's bad for everyone except for hackers the first and this is one that doesn't get talked about a whole lot they waste a whole lot of IT time
troubleshooting account lockout so I'm one job I sit across from the Windows helpdesk team and you always knew when it was password expert a because you would get there maybe before some of the helpdesk people and there would already be someone standing there at the desk who was locked out of their their Windows domain and they couldn't work right and the entire next day or two would be helpdesk folks having to go through and unlock accounts it's a huge burden on IT it also frustrates users who pick what otherwise would legitimately because considered a hard password that then gets rejected imagine you're trying really hard you pick what you think is a good password and they're
like nope no good like okay I'll try it one more time that's no good either okay forget it you know password to bang the other thing is the more complex your password is the more painful it is to rotate if you come up with an actually legitimate difficult password to memorize like these all these passwords are hard to remember but you do it and you finally get the muscle memory going and after a month or so it's not so bad but that's too bad because now you have to rotate it again so after about twice at best most people aren't going to go the trouble of picking a really complicated password even if they like had all the
best intentions at first because it's just too much it makes it too difficult you're encouraging users do you toward pet bad passwords and of course this always led the passwords on post-it notes everyone again dumb users putting password up it's not the users fault they did that because its policy is ridiculous and in encourage users to have to do things like this to work in general these policies and encourage users to pick the weakest possible password that still met the standard so they would do all of these little tricks we're in what Windows 80 domains where they would you know check for a certain percentage of characters in the previous password every little example I gave
though come up with like a short-sighted countermeasure for but in the end all the same every new countermeasure they would come up with still encourage users to pick weak passwords pick the weakest password you can that still fits a standard in the end almost everyone's password ends up being a dictionary word in some kind of transformation and hackers are still able to guess the majority of where otherwise so-called complex passwords because computers can do take a dictionary word and add complex transformations to it they're very good at doing that all right so then we get the xkcd password Renaissance hopefully many of you are familiar with the correct horse battery staple the famous correct word this is
this and Bobby tables seem to be the two ex-ac D comics they get the most these are the kinds that get pinned on the on the cubicle back when remember cubicles by the way back when there are cubicles so this comic I mean you could say maybe this was a response culturally to some groundswell of opinion about password policy and pass raises or you could say this passed this comic started it but either way this really matter because people started shifting away from the notion of password complexity and theoretical mathematical difficulty and brute-forcing and started thinking about long pass phrases and started thinking a little bit about the user so for example this is my current personal corporate
password policy 12 character minimum no rotation no complexity that's it easy for everyone to remember easy to implement the theoretical combinations are 95 quadrillion so compared to that to I think it was 580 some billion for your traditional kind of other complex password even if you compare this to the a character mixed case number symbols that most most people think is a decent password policy from the old school that's seven point two quadrillion combinations so we have more combinations but it generates a better quality password so by not rotating the password we're encouraging people to pick even longer than 12 character passwords we're encouraging the pic complex passwords passwords that may be a little bit difficult in with for them
at first to remember but for example sometimes I will encourage people and we're gonna talk about a footnote to this comment here in another slide but sometimes I would recommend pick a long movie quote or a song lyric things like that because everyone says well I can't remember these things but you can there's at least you know everyone knows something some part of don't stop believin and there's like all these other songs that you know the lyrics to or quotes from your favorite movie or whatever so people can remember long strings of text or if you're concerned about some of the attacks against that you can also use dice for which by the way feels modern
but it was created in 1995 so it's been around for a long time like that notion and so the idea behind dice where is it makes it easy for you you have this dictionary of pre-approved words that have a number assigned to them and you use a series of die rolls to pick different words and you pick say five or six words that that are randomly generated essentially that form your your passphrase the thing is this seems burdensome at first but muscle memory takes over pretty quickly and again we're going to talk about some other things like password managers later but this is for there's there's always a couple of passwords that you can't that
you have to memorize you can't put in a password manager the fact that's after you do this a couple of times whatever your password is there's a lot of passwords I have now that I don't I couldn't tell you what they are I just know how they feel and whether they feel right you know so if you touch type you sort of getting into this mode where you just muscle memory takes over you type your password but you know I'm just some guy so if you go to your IT department say hey this guy just said that your password policy sucks and it's wrong and insecure or I need to change it think about yeah but I have this security
bulletin from 2002 that tells me about how passwords need to be complex right but you're not to think my word for it so the new NIST guidelines also discourage password rotation complex passwords in the encourage passphrases so this is like as officials it's going to get for something that you can show them so here's the here's the perfect paragraph from this so verifiers should not impose other composition rules like mixtures of different character types so no complexity I memorize secrets verifier should not require memorize secrets to be changed arbitrarily so boom no password complexity boom no rotation so flip that out take that back to your IT department it's hyperlinked in there so everyone there's no excuse
for them to not change it not because this is like government documentation kind of you know super super official alright so let's talk a little bit about you know we talked about policy let's talk about some of the current attacks against passwords modern password cracking especially if you've gone to other talks in this track you'll know these very advanced sophisticated tools I mean DEFCON is a sporting event just devoted to doing that right like people do it for fun not just for gain so people and people hone their skills to be very good at this not all but you know most password cracking is up starting with some sort of hashed password database done so it's one-way
hash so they have to do some attempted guessing or brute force to crack these passwords this allows a cracker to brute force offline so they don't have to sit there and Hammer a server that kind of you do you know thousands of comparisons a second on someone's live server they might notice but offline you can just crank away at it also tools like hash cat support a variety of different hashing algorithms and you can point huge dictionaries at them they also support transformation patterns so you can say you know take my huge dictionaries of all these different known passwords and applied lead speak to them or take them all and also just make the last two characters digits too
and it makes it very easy to convert good dictionaries into all these other transformations and as a result you dramatically reduce the actual common that the total combinations you need to prove for us or at least you catch they easy to catch things first so because of all of this you can crack water otherwise would be considered super complex passwords way faster than you think that you would because of all of these different steps to optimize in fact you know ocl hash cat also can use GPU for acceleration so you know back in the day so for example in 2012 I bought some a graphic I decided I wrote a series of articles for latisha
Arnold men on building a password cracking rig and so I invested in what at the time was a decent Bitcoin mining GPU not great but not too expensive either remember back when you could use GPUs to get bitcoins um so this was in 2012 for 280 bucks got a Radeon 69 50 and I could do 350,000 md5 comparisons a second you know that's 2012 obviously people can do way more now with with stacking a lot of different GPUs and things like there's the whole state of the art for that alright so let's talk a little bit about the rock you hack the the unfortunate fact is most people reuse passwords across sites they have a
password or two passwords maybe three passwords that they remember some people will say I have my insecure password that I use for everything then I have my banking password that's slightly better that I use for all my or whoops they have stuff like that right it's a common it's it's a common thing what happens is when a hacker cracks the password on one side the next thing they do because they usually have both the password and an email address for contact they will attempt that username and password across a bunch of other popular sites to see if the user used the same username which they often do and use the same password which they often do if the
attacker can get access to an email account then they trigger a password reset and by doing that they can get all the remaining accounts that they couldn't get any other way in case the user didn't reads the password so back in 2009 and the company rocky was hacked and it exposed when during that hack they dumped a database and they were able to get access to 32 million user accounts the interesting thing about this versus previous hacks where people have dumb password databases was all the passwords were in plain text there wasn't even md5sum hashing so this provided this treasure trove and this great insight into as of 2009 worked the most popular passwords were what all the
passwords at least for these accounts that people would use even very complex passwords right because they weren't hashed so you it gave everyone who wanted to do password cracking does great of current view into popular passwords and immediately everyone added this password dictionary to the dictionary if you get a password cracker today that's one of the common ones that comes along for the ride and rightly so because there's still it's still not used so slightly more advanced cracking so as as we have more password dumps like people use the Rocky password dump to then apply that to other hash databases they're having trouble cracking and they're able to crack more more passwords with that which then led to more and more
passwords being cracked from that password database and that goes on with every site that gets a database dump people start trying to get you know you must crack them all so people aren't satisfied with 90% success rate they want all of them and as you do that you start devoting resources you start building these dictionaries of what would otherwise be pretty difficult to guess passwords also you know computer to get faster GPUs get faster and crack and gets more optimized so we're able to crack better and faster also there's more exotic dictionaries that every you know every year are being added so for example one of my favorites and this was this is again years ago now
but 2013 there's this great Ars Technica article about crackers using the bible wikipedia and youtube comments for dictionaries and by doing that they were able to crack this database they weren't satisfied with getting just like 75% 85% of the hashes correct they wanted all of them and so what better way to get phrases than the entire Bible and Wikipedia which is there's a lot of text on a lot of pass phrases and lyrics and things like that and so for example they were able to crack passwords like give me liberty or give me death or in the beginning was the word which were things that before you would say well that's a pretty solid password
long password but memorable and these are the kind of things that we advise but there are now crackers who are able to you add things like this is the dictionary so this showed that pass phrases if you have a passphrase and there's a chance it might exist on a major internet site it might be at risk so then what do you do right so what's a good password a really good password is one that you can't remember unfortunately right very long so 20-plus characters actually truly random and complex even though we railed against complexity right before that all those numbers of difficulty actually count if it's truly random by the way also do that and also use a new password for
every single account problem is this is really difficult right it's really hard to remember a really complex password if not impossible so this is where password managers come in so for example something like keep s X there's a lot of other cloud-based ones that you can do research on but keep X X is open source it's local it has an encrypted password database locally it has a handy little generator because every site can't come to an agreement about what good password policy is they have different weakness and strength indicators and so you'll generate a password for one you'll generate it randomly paste it in and it will reject it for some dumb reason so this includes a handy generator you can
tweak your policy to match their policy this is good for all of those passwords that for most of your passwords because you're most of your passwords shouldn't don't need to really need to be memorable if you have a password manager but unfortunately some passwords still need to be memorable like them when you use to open your password manager disk encryption logging in to your workstation at work right there's a couple of passwords that you have to commit to memory how strong should those be well that sort of depends on the threat I still hold that you know 12 character plus passphrase with no complexity is decent for your average level of threat average user if you have
a more advanced threat then maybe something like a five or six word I swear password or if you need to pick a passphrase pick one that doesn't exist on the internet just think about does this phrase exist on the internet and then don't search for it let's see if it exists on the internet because now it's on the Internet right if you speak multiple languages and programming languages count why don't you mix and match nothing says that your passphrase has to all be words from one language right all right so let's talk about to a fate because password cracking is one thing but there's other lines of defense that can help protect you against having your
password guessed so there's three main categories of authentication so something you know something you have and something you are so passwords are a prime example of something that you know it's in your head and you spit it out the best insurance against password cracking my opinion is two-factor authentication 2fa so what this means if you're not familiar with this is in addition to the password you need to provide some extra factor ideally from a different category than the first factor so if the first factor is a password ideally your second factor isn't also something you know so for example something you have might be keys a token of some kind of your phone something you
are or biometrics you know fingerprint face your signature things like that once attacker the great thing about this is once an attacker guesses your password they also have to compromise your 2fa device so that just adds this extra layer of defense even if somehow they're able to get through the first one so these things and most 2fa implementations use some kind of form of flow book that's into something you have category here's a couple of examples so when the most basic is SMS so the way this works is you log in to a site with your password and then they will send you a text message that has some random multi digit code you type that code back
in and that proves that you have the phone that has that phone number there of the choices that I'm going to list it's considered the weakest choice because there are some attackers are being able recently to be able to intercept SMS in some cases they do it I compromise by talking to your film company convincing them that they're you and you lost your phone could you please switch over to this phone and they will happily do that sometimes I'm other otherwise there's some flaws in the ss7 I'm protocol that people are exploiting to be able to get SMS messages in mass there's been a whole lot of hand-wringing over SMS and how dare you use SMS for two-factor off but honestly
it's still better than not having any to factor off so if you're completely dissing SMS for to back off because of those those threats which they well they do exist they're still so far relatively rare it's still bet is still required as they attack them to do this extra thing after they've cracked the password so it's still better than nothing another option is pushing other vacations to a phone the way that this usually works is you have some sort of an app that's usually linked to the company or the account that you're using they usually have a corresponding app because every website has an app right you can even browse a website and your phone without getting an invitation to
install the app well sometimes these apps can send a push notification to your phone and there's also two FA providers like they do I was a prime example of this that will can optionally send a push notification to your phone this is nice because it's convenient so instead of having to like look at my phone and look up and then type in numbers and get it wrong or not do it fast enough and then it rotates for whatever you say accept and it's it's really convenient so for example I use this for some of some accounts because when I log in for work for the day I end up because of multiple environments having six different - available
indications that need to happen if I want to work in these multiple environments because they all have different accounts typing in six numbers one after the other into all these different things would be horrible with push notifications it's just kind of horrible that's a lot of it's a lot of 2fa but it's still convenient well the other thing about this sort of move on is the downside to this is that depends on its relying on the security of your phone so hack your phone you're done it also relies on the strength of the app so if the app is insecure has a vulnerability then it's you could potentially intercept push notifications so the next level up would be T LTP this
is time-based one-time pad the idea behind this is you generate this multi digit code on your phone that rotates every 30 seconds so every 30 seconds it gets a new code a lot of there's a lot of implementations of this it's a way more secure approach because it uses it relies on the shared secret that's between the server that's throwing your password anyway and either a hardware token that you have or some sort of software token basically like a half on your phone but when you're logging in there's no communication going back and forth between the server that could be intercepted it's you don't actually have to have if you use a phone it doesn't
have to be on the internet for this to work just use realizing the time and then finally there's u2f it uses a key that's inside of a hardware token to respond to a challenge from the server so the way that this works you log in it says insert your token use usually if it's USB you plug in the USB device you hit a button and then it accepts a challenge from the server and you log in it's simple it's very secure the main downside did this is it's not very widely supported yet and it does require that you buy a device but it's a $20 device so for some people that's that's not a big deal and for other people that
might be a lot but in the past those types of devices way more expensive they've come down more recently in some conferences they hand them out like candy now sometimes alright so last thing to talk about before the conclusion is password reset attacks so passwords aren't always the weakest link to get into an account sometimes it's a lot easier just to attack the account via the password reset so the way that this works is an attacker gets access to your email then they go to to whatever account they want they trigger the password reset they get emailed some sort of either a new password or a link to click on or there's a lot of
different implementations - if a helps with this but if you have access to the email an attacker could potentially socially engineer a way around that talk to the organization say hey I lost my phone could you please disable 2fa if they can convince them to disable 2fa then they're in another option is Facebook is is offering a new service called delegated account recovery where essentially what you do is instead of using email you can use your Facebook account they've built a new protocol around this that it could allow you to use your trusted Facebook account instead of email to do password resets it's a brand new protocol and it's still in a closed beta right now
I'm basically what this comes down to is if you don't necessarily trust the security team behind your email but you trust Facebook security team more than that and this gives you an option to do that right so in conclusion so strong authentication is actually possible today you know it's not hand-wringing in passwords are dead and all of this stuff it's possible to have strong strong authentication the only problem is if the sec can't still agree on what it looks like if you ask a couple different people they will tell you couple different things about what they think strong authentication is and this is not just for password policy but for all of InfoSec we still repeat all of these
same mistakes that led to this bat decades of bad password policy here's the thing attackers from the very beginning have focused on real users and learn from real users they use real users as their data source to understand what to do to attack it's time for defenders to do the same thing you know you didn't have to tell an attacker what a user would guess for a password based on a certain policy they already knew they could already guess because they spent time studying users and understanding what users would do and again defenders need to do the same thing if they want to build adequate defenses researchers need to shift focus away from hacker movies as fun as that
is it's also easier honestly and it you get both this thrill of it being exciting but then in the back of your mind you also know that it's a lot easier problem to solve and solving security for real users that are really using the system um I T also again there's some of the blame because they get these policies handed down and it's a lot easier if you have a checkbox up do you do this do you do this to just say yes yes yes oh I don't do that yet let's just do it and so I can check the box it's a lot easier did I know because like I will for a credit
card company and we do PCI on its right that's a lot of check boxes it takes a lot of energy and a lot of knowledge to push back against one of those policies if you think that it's not good for your interpretive it's not good for your users you think it's a less secure practice in general they should be empowered and and educated to be able to question what our so-called best practices in general but for this to work it requires better security education across the board it doesn't do like people MIT won't be able to question security practices they don't have a decent background in security or they won't feel qualified to question it
to speak up so it's beneficial for everyone to have a decent education around this and finally just stop blaming users for security problems that aren't they're not their fault all right so questions the talk is right there in that URL it's live you can go get the links a lot of this like I said I cover in detail in the first chapter of Linux hardening and hustle networks and then all these different different the NIST guidelines and other of the links there so yeah Jeffrey Goldberg from agile bits I just wanted to add a historical point if Arnold is here you mentioned both dice where and xkcd they are historically linked the xkcd picked that up some actually a blog post that I
wrote three weeks before the kcd came out in which I described I swear well that's awesome so I can give you that bit of history and then just one minor correction it TOTP is behind based 1password not pad okay I've heard it said both but anyway just a minor correction
so I know the talk was mainly around how to generate good passwords what about a future where we don't have passwords do you have any comments on ways that we can try to get rid of passwords using the other types that you mentioned things that are on our person TOTP and other combinations of security techniques to remove the need for passwords at all sure um so just in the time we have here the the only thing I could really elaborate on is a couple that I don't like I'm not a big fan of biometrics for single factor authentication right there there's value in biometrics for single factor authentication when the alternative is no authentication right so if you're say
I will either use that for my lock screen or I won't have a lock screen fine makes sense there's a certain use cases where it totally makes sense but I don't think for people with where that's not the only option where they're choosing between that in a passcode or that in a password I think in general biometrics are a great third factor in some cases can be a decent second factor I'm just not a fan for single factor what I reports on magic links some services like eBay slack I believe in others and nowadays have these magic links that you go to the login page you click a button then you get an email and within that email
there is a link you click on and then you walked in automatically knew your count so what are your thoughts on that versus using a username password based okay sure um it's so weird because I remember long ago we would tell we would tell people to inspect URLs right and train like one of the parts of user training was to look at the URL and make sure that it's a site a domain name that you recognize and things like that and then now we have twitter and so those way too long so you have to have the domains be super short right and so we've taught people that every link you click it's reasonable for
it to go through five levels of redirection and also it's reasonable for a website to pull content from seven different domains so it's I don't know yet how to give a give an end-user good advice on how and whether to trust that kind of thing I guess I kind of know my stand on this and I really don't really like CAPTCHAs and the way you said click that you're not a rowboat person but do you think there might be something in the future that we could probably do to not have those kind of CAPTCHAs just to for the website to know that you you are a person I think those oh I can say that
something is dead okay um so so those are dead and the reason they're dead is if we actually believe all of the hype that were saying about artificial intelligence and we spend all day training all of these bots and particularly mature air-condition and stuff what we're sort of saying is we think that we can create a world where we can create a machine that can impersonate a human right and pass the Turing test and all that stuff so I think tests I think it's going to be harder and harder I think most of those tests now are really useful for people that are building AI because it helps train them against the things that they think machines might not be good at
but again it's that that becomes this big arms race right where I think eventually we will get to a point where it'd be really hard to unless you ask someone about well the only the only example where that's not dead is if you were to take a website and it asks you let's say that you're sitting in a desert and you come across a turtle and the turtle is lying on its back in the hot Sun and the hot Sun is baking its stomach and does that bother you that's a Blade Runner reference Masari for doing a reference but apart from replic even that didn't work out so well for them right and so yeah so anyway I think captures a
bit so I noticed that you talk about TFA and like u2f and and that this effectively solves our problem that we don't trust the phone because we have this this hardened token that we can touch we can trust because it's firm we can trust because the phone is software it's hard to token we can trust because it's hardware and hardware is eminently trustable bar boys are really eminently trustable we just have no real means verifying that this hardware is trusted and and we've effectively just you know when we put our trust into like hardware tokens that people hand out they can't be at conferences we're just pushing the problem to the ground that we can
inspect so I wouldn't go as far to say that to a face solves authentication at all no far be it all it does is add an extra layer security to deal with the problem of a password potentially being guessable by some state of the art it adds this extra layer I mean for every to a failing implementation you can conceive of attacks against it but all that said you still end up the result that you end up with is still stronger security for most users and so it's still worth doing even if you can conceive of a world of untrust untrustworthy hardware it's still largely it's still way better than what the alternative is right now which is a
single factor that's a passphrase or something in your talk you cited nist and said you know password complexity and whatever but then later you said SMS was okay that contradicts this now stance I was wondering yeah so I still hold like I said there's a lot of talk right now about SMS is dead right and so to me again it comes down to my rather nuanced opinion about biometrics if you ask me from a security context what I feel about biometrics a short soundbite would be I don't really like it for authentication because of seven different reasons but there are certain circumstances where when you compare it to the alternative it's better and in case of
SMS to FA it's still better than the alternative of not having so there's a lot of people that don't necessarily have a smartphone or don't necessarily have a hardware token or things like that but they do have a cell phone that can accept SMS and it's still more secure for them to have a 2fa option than to just have the password hey Carl hey um question for you how do you feel about like the browser password managers like Google will remember your passwords for websites and that sort of thing safe not safe ish yeah password yeah browser password managers I I can I can like you mean built into the browser or the ones that sort of use like
JavaScript maybe everything just oh but like or you mean like the cloud-based ones or dmem ones built into like Firefox like good like Google will be like do you want us to remember this password for you or I guess Firefox does the same thing so when you're typing your creds into a web site so you don't have to type them in next time you go to that website yeah um I'm I can it it's better than nothing but it's not as strong as some of the alternative password manager so if you're gonna go full bore into I'm gonna use a password manager and you should the alternatives I think are stronger from a security standpoint I lean more toward local
password manager databases myself because I know where they are and everything I know then I could be monetize and things later but yeah so yeah I subscribe to the same threat of longer wins every time complete random so you don't have to memorize them in better that you don't and I love password managers but my thought on password managers the only critique I have is because you can't memorize them and they're so long you have to copy them to the clipboard and so that's where the vulnerability lies I think like you you know LastPass does a really good job of you know like Tavis came out with that you know exploit their that boner Billy found and
they came out with a fix within three hours or something like that and it's great I love that they're on proactive on that but the clipboard is vulnerable in this sense in on on your average workstation for sure but there for example if there's a distribution of limits called cubes that allows you to segregate your work your work flows into a lot of different themes and they have with the notion of this global clipboard and then clipboards for each VM they do it in a pretty clever way but anyway the long the short of it is it allows you to copy and paste from a trusted VM that kind of acts as a poor-man's hardware security module into a less
trusted VM without other VMs that are running on the same machine being able to intercept the clipboard totally not and they probably shouldn't know cubes is I mean this is this is running on Qt I mean this laptops using and I love it but know it's not for your average user at all I mean that I've been a Linux user for a long time so I'm I can I expect a lot of abuse and things to be difficult and just sort of embrace it but a lot of people don't yeah sure yeah I just wanted to say that the way that the better password managers work is that they do this that they do not use
the clipboard they've got other sorts of inter process communication within their own browser extension so in a sense using a password a password manager that provides a browser integration gets you a support problem so I think I'm just gonna cut her off and so because I wouldn't have people said of it so thanks everybody for coming I would love to talk to you but more like I'll be up here or out there and just grab you in the hallways any other questions [Applause]





