Zero-day .NET and Nvidia GFE Vulnerabilities Explained

Show original YouTube description
Show transcript [en]
so now getting into it um like i said my name is matt batten uh i'm red vaughan on twitter like red team and vulnerability research uh so i'm going over uh net and nvidia gfe vulnerabilities that i've discovered recently also i threw oda bypass uac in there that well it's not odd anymore somebody dropped it um publicly but i discovered it and i was trying to do something else with it and then somebody just publicly put on github and got like 120 stars so good for him um but anyway so like i said matt baden there's my wife my dogs and cats and uh my best friend from the marine corps i love him i love my wife and the animals and
everything so there's my twitter you can email me for my work i work at six shin it's uh it's some of the smartest individuals i've ever been around i'm humbled every day to be there and um my day to day i do red team operations as well as some tool development i write some stuff like c sharp aggressor scripting powershell python i do i do a lot of different stuff or a lot of different hats um but yeah that's a little bit about me and the funny pictures all the animals are in the house somewhere uh so what's going to be covered is uh like the thought process so i i really want after this talk
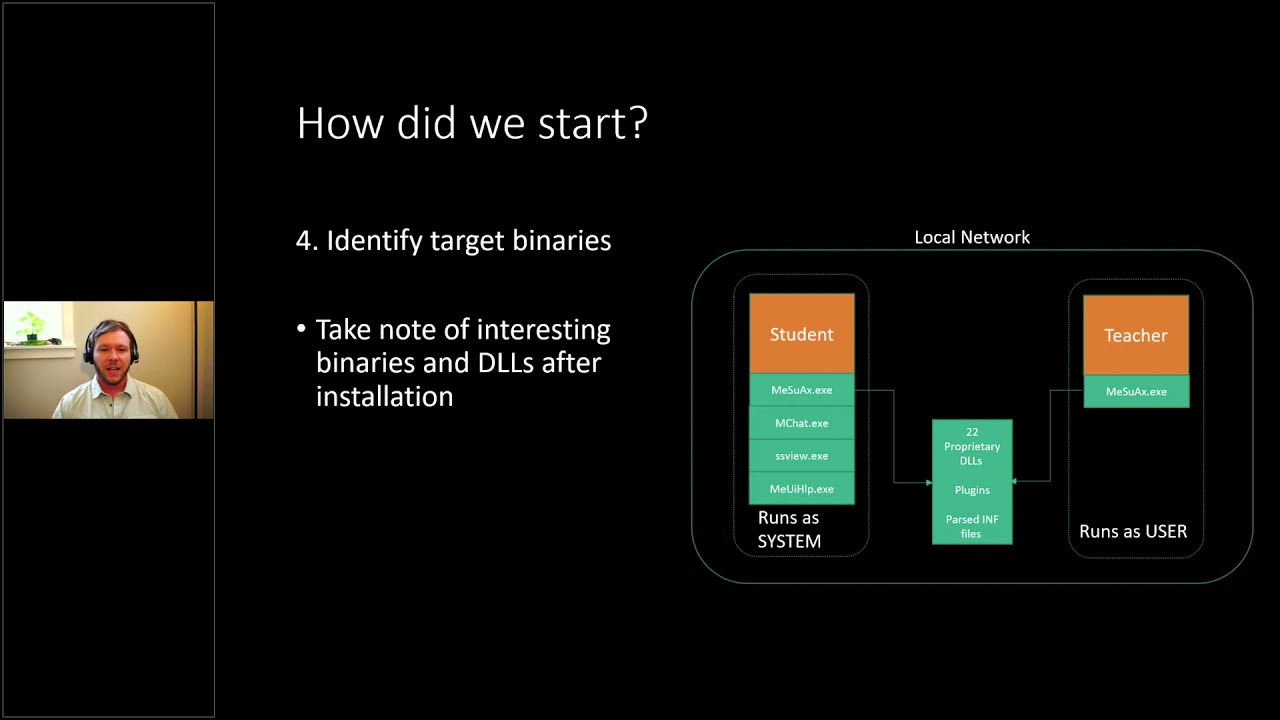
that uh people to actually be able to try to go and find vulnerabilities themselves if they're not already and a lot of people um i'm doing the interview i do the interview i run a lot of interviews uh for six gen for um red team positions with another individual and uh the thought process is a huge deal and talking to so many people i realized like it's not there's not a lot of there is information out there but it's kind of hard to gather and put all together and everyone has their own methodology and i would say like my whole career is based off of um people that are smarter than me i take their methodology and i just combine
them so really i'm just a collection of a lot of people that are way smarter than me which is kind of funny but so just the thought process of going through okay like how does it start out what tools am i going to use which should be the next one and then i'm going to show real examples now that was a big issue i had is like people that talk about the processes but then i don't see examples and i don't know how to implement them and then my closing thoughts and i'm going to go into like solarwinds and the um like companies and the government and in general and like why why this matters
and why people aren't thinking about it um which like and just be what i'm thinking about like the solarwinds thing i find it hilarious that um a bunch of companies that didn't patch solarwinds on time or keep it updated were not able to be compromised by that huge um term events that happened but everybody who was up to date were the ones that ended up getting screwed so it's just it's just funny because as you introduce new um software every time you you update software you introduce new software into your environment you're just you're opening yourself up to more exploits but like i mean if you don't pass there's known you know in days or oh day well known in
days or vulnerabilities are out not no days but as you patch as you update it can break other things or cause more vulnerabilities and these are just some uh examples so the thought process um there's a lot of different ways to do it and there's a lot of experts out there i follow like matt nelson enigma is what he goes by on twitter i follow him very closely in his blogs it helped me get started i would say his is the easiest to read for beginners his blogs he he really breaks it down um right the og of like i would say logical vulnerability research and windows would be like james forshaw i think somebody else can correct me but i read
all james forshaw's blogs i understand like 70 percent of them i would say my dream and my career now would be like to sit next to him for like two weeks and just listen to him ramble about vulnerability i watched all his talks like 20 times and i still don't understand uh some of the things and i i find it uh fascinating but so the funny things is like you're gonna figure out like wow this is like when you see how i walk through it you're gonna think it's dumb but it's it's cool and then you realize like at the end of this talking like i could have i could have done that it's not
that hard um but so there's you know there's the the code analysis well actually i'll go from so i do a lot of behavioral analysis now with dynamic involved so like i would i do a bunch of dumb stuff and then i just i watch what happens and like i i try to narrow down like okay i'm gonna do this and what's all happening on my computer and can can i somehow modify that behavior to my benefit and then the dynamic analysis would be like like uh watching it happen as i do it like if like i don't know for i think like reverse engineering malware or something like if you wanna know if it's calling
out to the internet so you you run inet spy or something and then um you set up a separate vm and then um fake dns and then you you know you double click the executable in the sandbox environment and you actually watch it try to call out to the malicious website so then you know okay it's calling out to the malicious website is there a payload on them list this website there is you go download the malicious payload and then you can start over on behavioral and dynamic and then there's the people who i'm aspiring to be more like and become where it's the actual like static analysis the code analysis where you know um you use um dns by and
um you're actually looking at the the low level code and you're going okay like because this main is being called this programmer because of this api call here and then this is left out i could try this and then it'll work and they go down that whole path and then um so like i said matt nelson and james forshaw and there's other like uh one of the things is the the dot-net vulnerability uh i t men with three in his name he does a really he has an amazing blog that's better than any blog i could have probably written about it where him and uh genocide k actually discovered the same vulnerability for the net but
then like why does this matter to large companies in the government and like i said like the more like every time you patch every time you update every time you add software every time you do anything on that network you you introduce new issues and you're actually going to see something really funny with the bypass uac um oday that i had that it's just stupid and it's funny and it's really easy but like i said so for this for this like these exercises in general all you need is procmond like in james forshaw's tools um which is like sim link it's really it on these and um some of them you don't even need that
and then uh just vms just having dms and understanding what to monitor so i would say the most important part of um the logical side for this for me would be the my filters for procmod and um understanding uh you can enable boot logging so when you enable boot logging in procmond you can actually reboot your box and watch everything that happens as it boots up such like services tasks that run and it makes a lot easier than like clicking through all of them you just have everything that would probably run a system in your machine or a high integrity level um run and that's something that's actually something i'm gonna break out here because it really one of
the biggest pet peeves i have when i interview red teamers sorry i'm close to the camera by the way i feel like i am one of one of the biggest pet peeves i have with uh red teamers is not understanding integrity levels when you're when you're on the machine like even like companies in general like we got a patch we got a pass for privacy and like everyone is a local admin everyone's an administrator on your on the machine so i know that's a no day you know or i know that's a prives that just came out and there's a cbe and you're going to patch it but like right here so i didn't have my size groups
um i just opened up command prompt regularly and you see i'm a medium integrity level right here i'm medium but i'm in the administrator group and everybody at their home that's probably what their computer is and like a lot of companies networks they should probably have users of medium integrity level that are not admins but you'll see a lot of people it's very hard to implement especially when it's been around for a while that everyone does have the administrative permissions group they are a medium integrity level but so there's a difference between so a medium integrity admin right to uh to system or high is a lot different than a medium integrity or a guest user or something
getting this system because there's there's a bypass uac and then there's a privilege escalation so if i do cmd and then right click i do cmd and i right click it i do run as admin oh no i hope i didn't lose everybody all right so if i do cmd and i right click as admin right i do who am i slash groups again and why you might already know this but i it's it's crazy how many people have interviewed that don't know this so it's it's a high integrity level now so i could just run like ps exact i think space tech i tech scmd exe it would give me a system um shell or give me a system yeah cmd
back so then that'd be the highest integrity so going from a medium with admin to high or system well even not well the high that's i mean that's a bypass to ac so there's a huge difference especially in the marketplace if you're trying to sell it a bypass uac does not sell for as much as a lpe local privilege escalation right because you want to go from a guest user a basic user to system every time so um i just find that really important a lot of people don't understand that so the key is medium integrity with admin to higher systems not as impressive at well yeah it's not as impressive as a medium material user that does not have
so if you have a virtual machine you would create uh guest users um or you would create a guest user on there with uh no permissions no admin permissions and then you test these things out right now so the next step i was going to go into is i'm going to talk about um the filters so uh enigma or matt nelson he has a great blog where he i don't know if he means to but i mean he shows some of his filters but if you read all his vlogs i've kind of become a collection of his filters and um james for shaw's filters as well from watching his talks and stuff like um you can see in proc server 32 you'll
see that a lot um because it'll actually call command prompt and i think they use a lot for for escalation if they can depending on what software because there's other software out there like i guarantee that probably 80 percent of the people that are watching right now if you ran if you went looking at enigma's blogs and ran the filters he ran you would find uh probably like 90 though you would find a a dl being called a system or a high integrity when you rebooted the box like 90 and that can be like and like i could have a bunch of other cds i tried like i guess i don't know if i'm greedy i don't know
what the word is like i tried to find cvs where i feel like they're more impactful and they matter like nvidia that's all you know all graphics cards the gfe that's a huge one.net every machine that had.net installed that's a huge one like i have other dumb stuff like photo recovery software and um you know like gaming software because i game like that's you know it's cool but they're not you know when you when you report that you can get the cv if you report it but if you're reported to the company they're going to laugh at you or they'll say yeah we'll look into that and you'll never hear from again and you report to
the company no one cares because um the main thing is for for me is going after you know if it's a a company's network or companies on host machine they're probably not gonna have gaming software or photo recovery software or something like that but if you're just hunting cvs and that's what you want then that's something you can go for you can see like reg low key open key um i'm actually going to give like a real example here as well because i like i like doing it live it makes you feel better um because it helps me and i hope it helps you understand it better where so your filter is like the most
important part here like i was saying but if you the main thing i do is like if i get on a vm especially like a new installation so i'll download the newest version of the dev of uh the windows vms when they come out and then i'll the first thing i'll usually do is options enable boot logging and it's over here it hates me generate thread profiles every 100 milliseconds i hit okay and and then you just restart your computer and leave uh you leave proc mine open you restart your computer and then it's going to save all the events that occur when it boots up and then when you go into it you'll actually
see all the events so right now if you look my filters are crazy and uh man that's a lot but i mean you'll see all my filters so you'll see like integrity so that's a big one so when we talk about that it's really interesting it's like it just if you do high in system for integrity that's that's what you're hunting because you're doing it so you download the dev os for microsoft you you have a guest user and then on the guest user's account is what you run proc model you have to run product mines admin obviously but you run that and then you reboot it and now anything that's running this higher system is fair game because that's
that's a that's a od prives if you can figure out how to get a high integrity or a system integrity from your medium integrity non-admin that's a private that's an od prives and you know microsoft's want to know about it or whatever right you want to go i'll talk about that in a minute about microsoft i've had um not great experiences all the time with them the great people that work there there's some great people not gonna talk bad but it's not the best experience i've had but uh you see set security file they actually permissions create file right file um the red set value that will come into play later query open but you can also see i filter out medium and
low you could try but sometimes medium still comes in even my filter out um i wish i was smarter like development side because i i would love to create a dark mode of procmod i'm sure there's one out there i'm just an idiot probably haven't researched it but um a lot of fun i i push things out like path begins but that's a huge one filter path begins with c windows system32 kick that out because you can't write to that as a medium user so yeah a lot of things would be called a system behind integrity from there no duh so you i try to filter out everything that i know is going to be called as a system or
high for like i can't write to hku i can't write to hkcr um but this actually comes into play later too so i say i can't write to hku but is there something that you can modify or execute that will actually write to hku which would then actually execute something else at system or high which would then give you a private so the whole thing is like there's all these blogs and you read them all and i just combine other people's methodologies and then it's it's pretty crazy what you can do you set all your filters and then and then i just read the lines of code and then when i find something interesting i
said oh that guy called is high integrity um that's crazy and i don't know what's happening before it so i'll just click it in the the filter and then i'll um unfilter everything and just walk backwards and proc mom it's tedious and um you know like i do play video games while you know if i'm dead in a video game i'll just be scrolling through pokemon until i can play again or something like whatever i'm doing but that's the live so the filter is a huge um part of it and then mike so microsoft's actually introduced uh new mitigations for a lot of these things that people will constantly do so that's where um there's
a huge thing on twitter where a bunch of people got pissed off because they actually submitted well there's a specific person but they they submitted before the um mitigations were in place and microsoft waited until after the mitigations happened and then said you know they weren't bounty eligible but like um hard link mitigations which like in junctions right so like the symbolic link and then there's a junction if if something's running a system and you create a symbolic link and then it follows that link the new mitigation is going to make sure it stays at a medium integrity level so it was system but it's going to hit that medium so that you can't just go from system to
system um integrity and then the hard link right i think hard things like carbon copy like you know of the the file symbolic links just a link to the file um excuse me and then uh the the system 32 or temp windows 10. that was a huge thing it was a sandbox escaper had some really awesome uh exploits and i managed to read those blogs before some of them got taken down um and i mean they were amazing i might have you know saved them at some point but um you know sandbox escaper had some really cool uh exploits and oday prives and motivated me as well to get more into it from the write-ups but so they they change to
where it's um it's not going to be world writable which that kind of takes a lot of form abilities out so this is like this is how dumb this uh vulnerability for or this oh day it was a day bypass we see so this guy discloses it i showed a screenshot from like evernote or something i did when i threw it in there so i did find it february 9th and uh the the person burned it on the 16th was it um october 10 is october i mean that was embarrassing um but you can see so uh the fast central silent cleanup which is really cool so like james forshaw found one it was it's like one of the most used
um bypass uacs in like history probably i would say we're like and it's a silent disc cleanup where you call the original is you call this clean up and then if you're a medium integrity with admin permissions when you call the task disk cleanup it actually calls um an execute dissim.exe it calls that executable which then calls a dll is a high integrity and because you can overwrite where that dll is being called from with your current user then you get a high integrity call back because you're an admin right so then you go from medium integrity admin to high and then you can do git system or whatever there's stealthier ways obviously get system not going into tradecraft
but obviously that um that's like that's the most used one i wouldn't say obviously some people that don't know but for this one it's really dumb it's just it was literally um you just ran a newer version of windows 10 came out and then there was just a dll being called as system in a user writable directory which is see user user app data local microsoft windows app so i guess it was a legacy thing where api ms one core kernel 32 legacy um it was just a ghost dll so there's hijackable dlls or like dlls exists and then it's being called into in a user writable directory so user rideable means you have permission as a
low integrity user the user you are without admin permissions to overwrite it or modify it so in a user writable directory um you drop a deal all in there so then you would know during this time you're like okay anyone is 10 anyone has 10 box m1 i can just drop this dll in this directory and reboot the box and i get system which is funny so every machine that the person was like a little admin with medium integrity they could just drop dll here and um they got system where so see user user app data there you go but you can see the icackles you can do access check you can do eye cackles you
can actually the properties actually go into it but um as you can see here you can see the the user cool that was a like a made up user use when i'm testing and uh dog so dog was actually um my my guest user because i wanted to prove that point as well so full access f is and you can look up uh icackles um was a microsoft docs page to actually see what everything means like inherited everything but you can actually see okay wow so that that dll right here is a create file which like there's mitigations being put in place for the crate file right like oh man like if we created this if that was if we had
to create a symbolic link to get to the dll then yeah it would be screwed but it's just it's just a dll being called that did not exist and you can see it being called before that when those program files not may not found they know found high success i was like wow just see user user dll okay so you just literally you get on a box drop deal done all right so that was to get everybody in the right mindset i hope everybody's following along i haven't seen any messages discord i hope that this is people understand what i'm saying i'm trying to break it down to like where i would want it at
to understand better and people would understand as well as i do which is not you know i'm not the best in the world i understand it well enough now so okay this is to prove that i got the.net oh day but they never issued me a cve which i um i did email them every month for like five months if anyone works microsoft um but i got paid so money's you know um uh genuine confusion it's funny so except for net um i mean this is more this is more about vulnerability research than anything so net um this just proves that it's a dot-net privacy so it could be any software it just doesn't have to be
net so this is this is like microsoft specifically like um software and stuff that's on windows so like um so you just see i got the boundary they pay me 6 500. and for this one i said okay and i'm gonna break it down my walk i'm gonna walk everyone backwards so i'm gonna walk you from where i started what i saw sitting at the machine to the point of where i got paid right and that's like i think what people would want like how did you start and then how did the psc happen and then how did you get paid and i hope it makes sense so i was literally i was on my host machine i'm
sitting at home and i'm just running stuff and a lot of times like i'll use my vms a lot and then buy so much dumb stuff installed on my local machine a lot of times i end up breaking it and having to reinstall my os and that's because i have a bunch of stuff running and i'm like okay if i have this stuff running other developers from you know other companies or whoever probably have it running and i can you know um never look through ccr brothers yeah vendors are tough i i agree i'm definitely i'm definitely going through zdi next time i 100 agree with you on that i a lot of my friends made me aware of
that um so so for this one uh so i saw wpts extensions.dl getting called as system which you see on the far right system integrity on the far right it's running a system it's called it's coming from a service right svc host instead of create file to the dll name not found right i'm like man like why why is a dll getting called a system in a user writable directory again and the same name not found but cool the key here though this is a cool part the cool the cool thing is here cool is an admin i'm a medium integrity admin right so that's a bypass to ac that's not an od prives yet
so okay a dll is getting called a system in a user ridable directory so what happens if i drop that dll in that directory i drop it in i have permissions so i look um was it cool has full control allow full control admins full control type full control for control and then you can see i think i can zoom in damn that's bad all right svc host there's a load image success which means you know ran the image of that so i actually get a callback right so you can see that it actually ran it so that means from medium integrity admin it ran it as system i would get a system call back if it was
like cobalt strike beacon if the dll was a cobble strike or empire or whatever it could be covenant whatever mesquite the key here is okay how did it happen so i know right now it's bypass uac oh day but then how why on my windows 10 vm is it not there so i open up my windows 10 vm and i have my local machine and i compare so these are screenshots from um a normal machine and then my local machine okay so i go okay well the path under hku.default environment the path should be percent user profile percent not the user that oh it's the user installed.net from look at that.net tools and just so you know the way i got
here i skipped that part which is bad the way i got here was i filtered so when i filter everything i found wts extensions.dll i i clicked it and proc mom and then i took off all filters and i just walked backwards so i just go okay what happened before and i saw it did like a red set value so it it looked for the a lot of times i was filtering out hku because a basic user can't modify um hku you can only modify hkcu hq current user right you can't modify a local machine hklm you can't modify hku or hkcr so i'm like okay um my registry key that registry key got changed
in hku and i didn't run anything as system or um hi like it just happened i don't remember running it you know command prompt is admin or anything so i was i was really confused i'm like i guess my install.net something happened so so then i go on okay so what happened so there's actually so there's an operation reg set value and then what modified it and it was um when i when i installed net is what modified it so what installs dot net msi files right installer files so the next question and like and this is where it men and uh jonas k they have an amazing write-up which is their blog's fascinating and i did a little bit differently um
they used dns spy and so they're right up they actually get into the code level which is more badass i would i would say it's pretty awesome so i'm i'm getting there i'm getting better i'm messing with dns by a lot and um you know i'm i'm really trying to get more into drivers so i get more my next goal is like windows 10 all around oday prives and then rc hopefully but it's oday professor 110 but anyways um for drivers but for that for this one so i go okay so c1 is installer who has permissions to modify c1 is installer basic user can on execute you see that everyone read execute okay type
so if when you install net it calls the msi file which modifies that registry key but there's no prompt nothing popped up no admin no system so i did trial and error they did a more badass where they actually used unsp and looked at it looked at the code i was like i'm gonna click on every msi file like an idiot after i'm gonna do this clean image i'm install.net and i'm gonna click on every msi file which there's only like 20 or something and i just watched and it changed and i was like okay well how do i find out which msi file and i found out i could filter for the dlls or whatever the
the actual msi or like keywords or whatever um i did it differently than they did too my wording's a little bit different but the way they did it was much cooler on um that level more hackerish than uh the way i did it but i clicked every msi file so i clicked every i'm just being honest this is how i did it so i clicked every msi file and um i saw the registered key path got changed as a guest users dog or whatever so i was like man like so now that means a guest user or a medium integrity user um non-admin thanks chris appreciate you um uh a guest user a non-admin can execute the msi file which then can
modify a registry key in hku which should not be happening so and then it modifies it instead of doing percent user profile for sent it's doing see user the user that installed or the user that executed dot um or the msi so that means any machine that had.net installed any machine a user and this went back like i checked a bunch of net um software that was still available and it was it was working on all of them we're like if you if if you double click to msi you do msi xcc right you can run it but if you just ran it then you just literally any machine that i had.net you'll just get on it run
run the msi file and then you would just drop wcs extension.dll in that directory or in that path and then um it would it would kick off when um i think a task schedule would run and you reboot the box you restart task scheduler and then when i hit like control shift escape run or something i'll just come up um and then i'll get a system call back so that's pretty sick that's a that's a dotnet oh day privacy it was insane that was super that was like my first like big thing i was really excited and then you know i nerded out and then um i t men and jonas uh they actually reached out to me on
twitter and we talked they're really cool and then uh they uh the way they did it was much much cooler though but next one the next one i get all i'll get that one but so for the nvidia one this one's um pretty pretty interesting as well where um they just dropped cbe a few days ago um so i couldn't talk about it before then but i was really excited and this one's not that complicated either you're like wow like so i got 6500 for the other one um nvidia unfortunately right now doesn't have a bug bounty program i thought they might um if i could go back would i do it through zdi maybe
because you probably get paid but here i am and you know i'm doing for the good of everyone you know at home they're gonna be patched and i guess that's what matters at the end of the day is you know taking care of uh you know citizens from day to day and their their systems and permissions and companies but all right so the whole video i showed earlier um it shows the version i have and then there's an operation set rename information file and then matt nelson actually enigma had a really great blog about this and i read through it and um this is what got me starting this was just one of my filters i was running
and i saw i saw the operation set rename information file and i saw it replace the current.log with old.log i was like man like that's it's pretty simple the one that he had he actually had to um the one he had it did a set rename information file and that file never existed but if you gave it a bad uh xml file so he just like did gibberish you know like a one.xml it would say like bad xml and then would move it as system and when it moved he would do a sim link and would give him system so that's what pretty much in essence i ended up doing here so the set rename information file here
we go so this is what it looks like in procmond in essence like when it runs like what happens so i see okay um and that's why the the key here though is the file the file is getting ran there but can i can i delete s or can i delete nvstream svc that's like whenever you see something like this and something's being moved or something's happening you want to sim link it you have to be able to have control of that directory before so the biggest thing is nv stream svc can't do i control what can i do with it so and you can see okay um operation set rename information file success replacement exists true and then
program data and video corporation data so i'm seeing current.log old.log what so then and there there it is and um actually and i think that's test schedule and then uh procmod um you can actually see what it looks like okay current dialogue the proc my information cool and then so and here's the permission so now look okay program data and video corporation if you stream svc everyone has full access so i know that i can do whatever i want all right but the key here is under nvda corporation as well one above right maybe stream svc everyone full and then one above nvidia corporation i still have full access right as everyone so a guest could do it a guest
could do it and anyone can do it so then i go okay well i'm gonna delete the directory and then i'm gonna create sim link i'm gonna see what happens and that's what ended up happening so i bring it together um i put some link in there i say okay i wrote it out i'm gonna upload these slides at the end so people can use it but i literally just uploaded it and that's just this poc showed an example there's other ways they can do it like rhino security um had as an amazing blog as well which actually shows that you like rce and um other things as well than just a private so this is my poc to show them like okay
this is an actual prives and um there's another guy i think voidsec i saw that he got added to the cve afterwards um he looks like he's pretty cool class too from what i was reading i don't know i just saw on twitter but um but anyway so i go okay simlink current.log and then i said move.dll i just i don't know the first word that comes my head i usually do for the dll doesn't make any sense so i delete the directory so pretty much i i i delete i'm pointing at my screen like an idiot so i delete at nvstream svc i delete that so now all this is gone and then i just create
a sim link from mvstreamsvc current.log so this is literally the exact syntax you would use so if you wanted to like do this later on some so pretty much if you filter so if you think about this if you filter and proc mon on your on your machine at home right now if you filter in procmond like and you do the enable boot logging like i showed and then you reboot your box and then you filter for um set rename and information file right yeah set rename information file if you filter for um that api call right the set rename information file or that operation then if you filter for that and you do integrity higher system
and you reboot your box and then use and then you have access you have full access or even like modifiable sometimes but if you have access to that directory above the file then you can just do assembling to system32 and if it writes the file then you know you have a vulnerability and you can see so i did it did a write file it wrote move.dll on system32 pretty cool um so these are all my references let's say like google project zero and i put it in on there for the github and like like i said these sizes are me at the end um the system suite like there's there's also like processor explorer process hacker if you actually
like want to see what's um going on like see the entire levels as they come up um well so i have the youtube set oh that that talk the mitigations at the beginning was from blue hat um i think it was a microsoft employee of 900 sure it was a amazing talk and that's what taught me about mitigations because i i found some other vulnerabilities i thought but then i realized that they had the mitigations in place and um ended up screwing me up so um yeah i i talk really fast fast and i blew through that but um yeah if you if you like the talk and you want to reach out to me you can hit me up on twitter you
can message me um you can also email me if you have any questions um i'm extremely humbled to be an opportunity to speak and for everyone that's still here currently and um i guess yeah yeah that's the name of he's amazing but um so the the gist is like at the end of the day um just for logical stuff it's not that hard where you if you have the right filters in place and then you know whether you use a hard link sim link or um delete something if you just try weird things and like there's still other vulnerabilities like i think i have i have two other bypass aco days i discovered earlier i think
one got disclosed or both now but there's there's always something it's not that hard just from doing the filtering correctly and the logic correctly and then combining it with others tools just going through the blogs and then i mean hey i got i got paid for which i didn't expect um for microsoft after a while i was like 11 months but um i mean that dot net one's a it's an actual true o day uh prives but then if you if you re-look at the actual like vulnerability one last time hopefully it makes more sense in your head where full access because this is like what you would send to the customer like zdi i try to echo a file i try to write it
or touch it nothing's there test file it doesn't exist use the sim link and then you can see the arrow there so you know it's a symbolic link to that directory so it's actually pointing to the current.log to the work.dll and then refresh it in there i am but i did not take as long as the last speaker but um does anyone have any questions that's pretty much it i talk really fast i'm really sorry oh no worries i thought it was great uh but i work adjacent to the space as well
uh so question uh popped up in the discord any other tips for pracman yeah proclaims parkmon's probably like everyone makes fun my my teammates actually make fun of me at sixth gen um about they're like all your own days are pokemon get out of here but just having the right filters like yeah right so dumb um haters um they're they're also brilliant um people it sucks but just having having the right filters and knowings and just like and also like other things to think about like and i've been thinking a lot about it is like so when when you filter when you filter in and a lot of times when you filter out you'll screw up where like i'm filtering
out you know hku like right here path begins with hku like that's kind of that's smart and like saving time kind of way but it's also stupid because what if what if something happens like like the the dot-net ones literally because of red set value that happen in hku so if i would have never seen that if wpts extension.dll never got called in the user writable directory but if like imagine if that that didn't happen that wpts extension.dll never happened because the hku key was never like it said like you know it wasn't found or something happened there if i had that filter off and i saw a red set value and i saw that path
then maybe i could have created the key which would then go but just be aware of what you filter out like my favorite filters are always path i always do paths um and and you realize like too like when you filter things out it can it can screw up a lot of things so i just do path begins with and um a lot of times i'll do like high system for the integrity integrity is high integrity is system but then there's other integrity levels like some use sids it's like that's something to think about like i don't i don't see a lot of um researchers um filtering out for sids instead of integrity and and that bothers me so i would say
the key is reading everyone else's blogs understanding what they do and then thinking outside the box to find something running and then modifying it and just like and just like the mitigations like all those mitigations that i talked about with microsoft sorry i'm rambling but i i find it it's it's fun but like all those mitigations here like that didn't affect the set rename information file you know what i mean like and that that was a sim link which is funny it's the junction mitigation but like i'm wondering is only certain api calls like if if that was a create file then i bet you it wouldn't have worked but because it was a set rename
information file it did work so i'm kind of curious because it's moving it's like a you know it's a cp or like a move command so oh yeah thanks chris yeah that's actually really yeah so why should governments businesses care i did allude to that um yeah so for the for the test environment all the tax deplete unprivileged user yeah so yeah a big a big thing would be um for for companies and businesses in general like i know so many companies and i and it cracks me up and i've had conversations where every user's a local admin like um was it i was working at a big company it was commercial i'm not gonna say the name
but they it was a spec spectre and meltdown happen and they're like we have to patch it we have to patch it and um you know it's like a race condition i think and i figured the other one was but it was funny because it was like a prives i think but then every user was already a local admin so now they decided they're going to spend and it affected the virtual environment so they spent hundreds of thousands of dollars to upgrade the virtual environment and add the infrastructure well the same i guess infrastructure i don't know i'm not a virtual environment guy but they paid hundreds of thousands of dollars to add because licensing that was
licensing hundreds of thousands of licensing because they had to patch specter meltdown the percentage of whatever cpus went down whatever and but everyone's already a local admin so i was like hey like if we're going to fix that we got to fix local admins first and then worry about the patching but um i mean obviously always here we're about patching but like it just doesn't seem like the big picture issue is like i just see so many companies like oh there's a there's a cd nessus said that you know we gotta we gotta patch this because somebody's gonna prove us i'm like the guy's local admin he can run ps exec like why there is no escalation needed right yeah
like it doesn't it's just it doesn't make any sense i don't but i i feel like it's the check box for everyone in like in government governments and businesses the big thing like like and i said in um like solar winds no one talked about that really either from one like i could feel like everyone who didn't update didn't you know they weren't vulnerable the ones who were before that version so like i found that hilarious in a messed up way where i'm like like because people screw like because people didn't do it they were more safe than everyone that was updating at one time so it's just like not and it's um so i don't have the exact answer
like you need to stay updated in patch but then every time you update new new things are introduced in the environment so having somebody who actually understands what's happening um and like the actual image so like actually doing um like looking at the images if it's um across the whole company understanding what's happening in the actual process level and then across the board because you know when attacker gets on the first thing he's going to run is you know win p's or all that basic stuff or well some of them is even dumber ps exact but yeah and i think to that point chris is like uh the the people slow to slow to patch
or like yeah we weren't vulnerable see we we were right but then yeah you should stay on top of patching but i think as any experienced person working in infosec can say is like risk or change management is a big thing and it's for this reason right is we want to make sure that the changes are only are being done are being done with review and not just blindly updating but then you start seeing stuff like slurwins where it's like well they waited six weeks after you know rolling out being in the environment before they even attempted to look around the environment so it's like well how long's your review process are you comfortable not being patched for
six weeks like with a zero day cbs s10 whatever right it's like so i i think the the funny attack factor that i see for for stuff like this is um you you compromise a tool and then you you start dropping zero days out in in the wild so that people start using it so then everybody's like we got a patch we got to fix this thing and then york you're now malicious supply chain gets into everybody's environment because they want to patch inception yeah oh day inception that's scary i didn't think about that sketchy that's how i would do it right is like how do you incentivize people to patch you make you make them have to patch
scary yeah yeah yeah cool i think is that it i think that's it unless anybody has any more questions about hacking cool things and finding cool vulnerabilities through pokemon boom all right yeah lunchtime uh so we'll be going to uh to break we'll be on break from 12 to 1. uh 1pm will be the keynote uh over in track one thanks again matt i thought the talk was awesome thanks bro i appreciate you more uh cvs yeah hopefully hopefully cooler ones driver level we'll see good luck with that man thanks for start reverse engineering stuff i'm doing it i'm doing it