Phishing Testing and Security Metrics
Show transcript [en]
the entirety of the security industry both on the customer side and on the provider side don't have a very good common language with each other and they they oftentimes will ask for things that the testing company won't give them and the lemon mark that's been created in security have a very very high level of knowledge on the tester side and a low level of knowledge on the consumer side so they're not actually getting value out of their test all they're doing is reading a brochure and because that looks pretty they buy it i think it's down to customer education as well as provider education i think a lot of the providers don't know how to provide the
service they're actually selling i sent 95 fishes 93 people clicked on it and then they're like yeah thank you for the metrics which gave them nothing like they got nothing out of that the only thing that they got is that your users will click [ __ ] that's all that's the biggest benefit they got and guess what that will always happen because clicking [ __ ] is the most fun part of using your computer it's the most fun thing that you can do there's nothing else more fun than clicking [ __ ] how do you get to the kitties click [ __ ] how do you get the funny video click [ __ ] right like that's the most fun thing
that you could do so of course you're gonna click out like can we show all the time but you gotta really provide value right it should be testing all sorts of stuff you should be testing intelligence leakage based on how you profile the company and what addresses you can get and how you can find their org chart and who you can set it up to and whether they're vt grads who are [ __ ] for football that you want to be able to specifically fish them with game tickets inside of an excel macro because you dumped a bunch of documents that they had and you found the metadata and you realized that they were using 97 instead
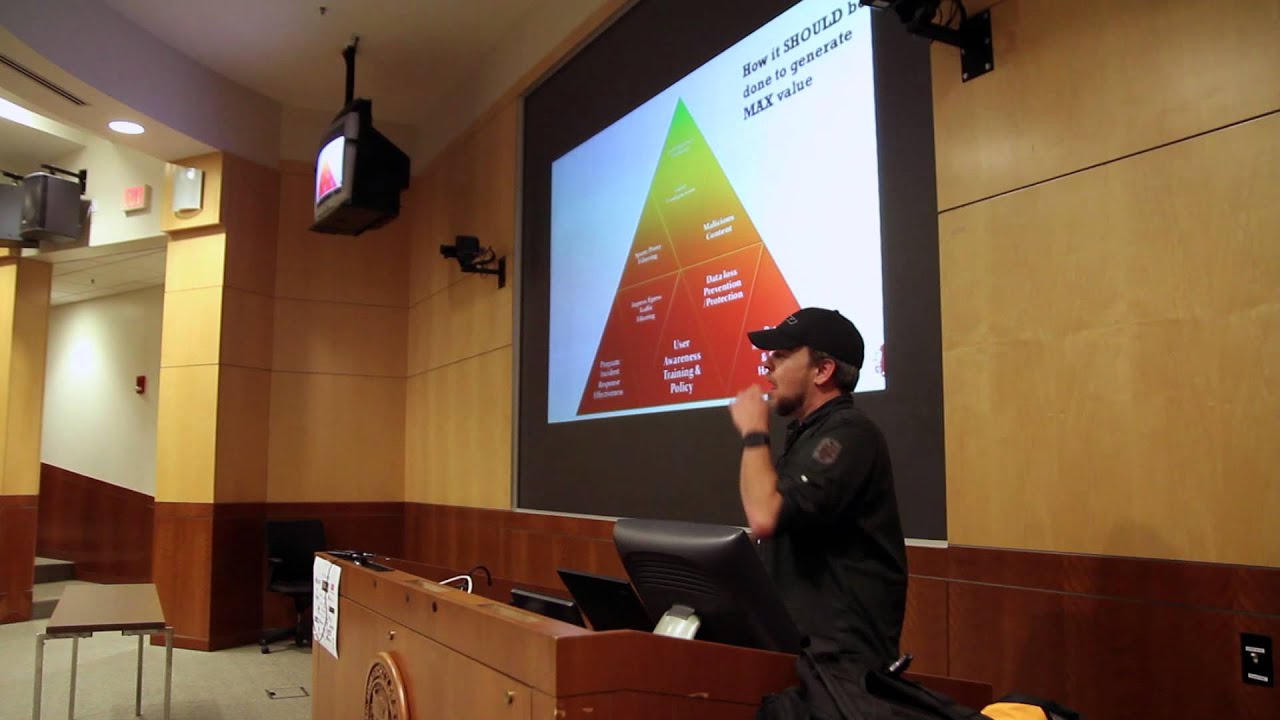
of 2013 and they're old school and you can just jump a macro and that [ __ ] would run automatically like huge finding did you find it when you were doing fishing no it didn't have that in the butt so when companies normally will go through and try and hire someone to do a phishing test oftentimes the metrics that they look for are around what users and how many users clicked and that's actually not providing them any value because we all know that a user is going to click on things that's the function of their computer that's what they do so making security metrics around that is irrelevant to the security program users should definitely do fishing tests
because it gives them the ability to expose multiple different layers and test multiple different layers of the program the problem is is that the tester oftentimes is not aware of all the layers that should be tested and the consumer is not realizing that the tester has the ability to test all those levels i think the best message in all of security is that experience provides you the intelligence and the ability to act in situations that are stressful and when we're in stressful situations whether it's being under attack whether it's a compromise whether it's a system going down whether it's the leak of information all of those are very very stressful situations for a company and
the more that we can train the more that we can get used to being in that type of fight and not some type of very controlled thing where it doesn't put us through the level of stress the more we can get used to the stress we can act cool and calm and collected and follow those distinct standards and guidelines that we've put forth in the stressful situation instead of having some type of arbitrary reaction that we can't anticipate





