Shut the Front Door
Show transcript [en]
all right hello and uh thanks everyone for being here today this is uh shut the front door uh so let's get this out of the way right away i want to thank the uh b-sides guys for doing this uh good work today all right so what's this talk about well i'll be talking to you about rfid access controls uh which are shockingly bad essentially they leave your doors open for anyone with a bit of knowledge and a few dollars so chances are one of the technologies i'm about to talk about is installed in a building that you work in and since you're here i'm assuming that you're security people so this might give you a bit of a headache
hopefully a few laughs so a couple questions has anyone here ever cloned an rfid card couple people three or four or five okay good so hopefully this isn't repetition for too many uh who has one in their pocket oh awesome okay so okay this is like that charlie miller where he tries to get your phone with bluetooth all right
okay so a little about me i work on the attack and pen team at acuvent labs i do netpan vulnerability assessments social engineering and physical penetration testing so the latter is obviously what got me interested in today's topic as i said this stuff i'm about to say it's been said before it's not groundbreaking research but i think maybe no one is listening or people just don't get how bad it is but you know what really grinds my gears i've worked on sites all over north america and europe and apparently no one got the news each time i get to a new site it became more apparent that there was a general lack of understanding of how bad the
problems are if this were like a network vulnerability it'd be like finding out servers in your web farm or vulnerable to an oday with code execution and it's in metasploit and just not bothering to patch so now i realize that most companies basically use these controls to prevent any random from wandering in off the street and using the washrooms but the locks on and the locks on most doors are just as vulnerable but when you see someone picking a lock on a door you know that something's up and when someone beeps through a door it actually lends credibility to them just because of perception and the businesses that we do assessments for they get owned by nation states they're
targets so these guys should be really wanting to lock the front door so that's rant mode off so hid prox which is the technology that i just cloned is completely insecure as demonstrated by this 40 chinese device that any of you can buy from aliexpress or ebay in fact uh prox tags can be read from three feet away with this little toy now this is based on another uh design on the internet but it's it's a parking garage uh reader but it's been modified with some some arduino hardware so there it is an operation up there i just have to walk by someone with this in a book bag and their card is stored on my sd card in memory so i can create
a duplicate later here's an example of the unit in operation and as a pen tester this is what i want easy mode i don't like working hard as a customer or someone designing security products this is exactly the opposite of what you want in most cases rfid credentials in use today are this easy to copy so there are a couple different types of rfid that is used for access control now this is an over gener generalization but for today this is what we're going with low frequency hid procs hid is the brand by the way and in dala they fit into that category both are vulnerable we're only going to talk about procs and high frequency which is a more
modern rfid most most modern rfd is high frequency for access control uh it's icl hidi class and my fare and we've heard all about vulnerabilities in my fare the dutch transit system so on and so forth there's other things like the 407 but they use active transponders that are in the in the 800 900 megahertz range okay so let's get right into it you probably all recognize these readers that's hid 5335 they're everywhere hid was originally formed in 91 and this technology is now 20 over 20 years old it was originally used for animal monitoring and tire tracking so it's by far the most common type of access control system even in my work today uh hid boasts over 200 million
cards sold and i'm betting the lion's share of them are this technology still in the market today so picture on the left is the 5335 very common reader as i said the pearson international airport is full of these things and after you learn how insecure they are you're going to wonder why bother with the x-ray scans and the genital scans and the like that so prox was designed an era when electronics was pretty much the domain of electronics engineers uh it was a bit hard to imagine that electronics would ever be as accessible as they are today but it happened arduino blew the doors open and as you know things are only going that way at a
more accelerated pace uh procs as i said is insecure by design the card is not encrypted at all if you power it it will just start spitting out your identification bits okay neither is the wireless the wireless if you can sit there with an sdr or some other device some radio capable of listening to that frequency you'll hear the bits if you can demodulate them so this attack can theoretically capture signals from even further away by like for in a car for example and the last piece of the puzzle is the communications to the back end now this is uh done with a protocol called weakened and it's also unprotected completely it's it's where the easy
vulners are and it's worth noting that it's still around in the next generation readers so here are the things that you really want to consider when evaluating security of an rfid access control system the card the rf the hardware and the back end communications every factor here must be executed perfectly for a secure system no one really bothered with the hardware on procs because there was no point everything's so broken here's a little tip don't trust an rfid vendor i've been on way too many sites where they're like yeah we're secure we're using these encrypted tokens and it was like i just showed you here beep beep okay i'm in your in your door get a trusted third party to review your
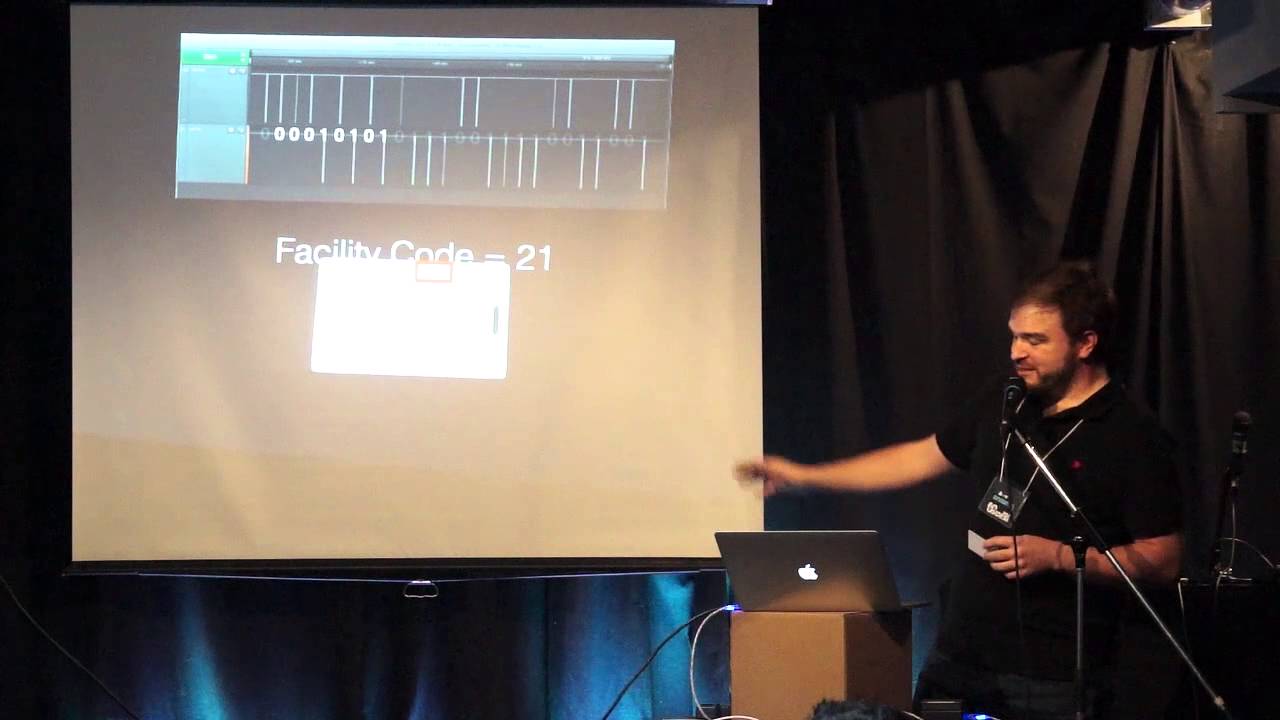
plan and hardware proposed prior to installation for anyone here that's in charge of installing these things okay i talked a little bit about the wigan protocol the weekend interface is remarkably simple and really this is where it's at in terms of having fun with hid procs there are two lines let's let's not talk about ground for a second there's data zero and data one and as you can guess it when it drops to zero volts on one of the lines that's a zero or a one respectively so here we have the slayly logic uh screenshot and you can see the the bit stream here so what can we do with these bits now that we know what they
are well with a standard 26-bit card there's eight bits for the facility code and that's the card i just cloned eight bits so the facility code on the on this card in particular is 21. and that's the only private piece of information on the card every other bit of information you need to make a new card is written on the actual card itself and usually these cards they're ordered in batches of 100 so the facility code is going to be the same for at least 100 cards maybe a thousand you never know okay so and here's an example of where it's printed on the card this is a different card number but uh just for
illustrative purposes so there's the card code right there we're converting of course from binary to decimal and so now now that we have all these bits uh what can we do with them so what does all this mean so we copy the card after that how do we make a copy well the tools that we use to copy it need the card's value in hex so we convert our bit stream into hex so every uh prox card actually has 44 bits of data on it but the reader never transmits some of the bits but luckily they're static so it's easy we can add them in here so those two first bits are what we add to
the pad which is the static bits i told you about and we get that value then we convert the remaining bits and we get those we stick those two together now you can email this card to anyone you can and they can make a new card with with any one of the number of tools that's available on the market today so and getting to the wigan data is remarkably simple hid has gone and labeled things very nicely as you see data zero data one tamper which is never hooked up so the weekend protocol can be exploited in a number of ways like we put little gremlins inside this thing they look they left us like a lot of space for
adding electronics to these things and that's why i could do it there and here for example we could put a microcontroller in that listened to the wigan signal and just recorded everyone's card as they were buzzing in in the morning or for example we could brute force the lines it only takes 50 milliseconds for one card read to go across the wigan line so that's 65 535 theoretical cards in 30 minutes that's pretty easy or we could combine the replay attack idea with the bug add some wireless maybe bluetooth or 802.11 and we have a remote control door opener pretty awesome spoiler alert eric the next guy and i are actually building that hopefully uh
to add to this presentation so in summation the wigan protocol is completely fail and so is hid procs in general now hid came up with this secure alternative called iclass and we've had customers ah i'm my class i'm protected these cars are encrypted well we know a couple years ago from uh a couple smart guys that that's not true i'll get into that iclass uses encrypted credentials and encrypted wireless communications uh poorly encrypted so it turns out jk they're not really secure they just they screwed up you can tell these devices by their curb front and sometimes they have other manufacturers names on them like bosch or honeywell but they're all white labeled they're the same
same device the the weakened attacks we talked about are still good on these devices because the back end still unencrypted why encrypt the card and and the data on the card if you're just going to spit it out in plain text on the back end i have no freaking idea so for eye class henrik plotz and milos mariak figured out how to circumvent the protection of the micro because they put like not a commercial grade micro they put a microchip microcontroller in it which they figured out how to put in a high voltage programming mode and dump the firmware after that it was game over they had the encryption keys and they found that the
encryption keys on this system were used worldwide the same keys so fail now if you find a tool that will decrypt triple des you can read the encrypted portions of the card if you can implement it you're good to go so this image depicts a attack that's a bit different it uses an ftdi cable to bit bang the pick programming header in order to dump the data it's just slightly different so thanks to those guys i just mentioned they created this tool now we can read an iclass card so i read the data from one using a usb reader which i have here today i have pretty much all this stuff here today if you want to see it later the iclass card
has encrypted data on blocks seven to nine which are highlighted there now if you notice blocks eight and nine if you can't see at the back they're the same that tells us whoops hid use triple des in ecb mode which allows us to do some heuristics on the data to see well that's probably all zeros let's see so now i've decrypted it and sure enough yes all zeros and uh doesn't track seven look a lot like the data that was on the old hid prox card well uh spoiler alert it is the same so they they use the same system of facility code and card code on this new card that has a kilobyte of storage
they're using like four bytes here so if we convert the hex data from block seven we can see the same i'll just go through this quickly block seven was this we go to binary and again the the left side is the card code and the right side is sorry other way around the left side is facility right side's card code decode it's 161.89 so it's pretty easy also so as i said the data comes out on the back end unencrypted so if you were to put a logic pro probe on the wigan data output you would see that stream again and some i class even have serial output which we don't have to convert the bits
it just gives them to us and that's uh this one right here has that and i'm going to use use that later on so we just decoded 61.89 in this case that's the actual card and the usb reader that i use to get that data and then so since the encryption key is leaked to clone i class 99 of the time all you need is that block 7 data there are encryption there are exceptions but for the most part this is true and then you just need a way to write to the card so in this instance we can use usb in that program that i showed you but it's not generally available to the
public so i was doing some research one day and i figured out you can do it with just the iclass reader and the serial protocol because this is an rw 300 not not on r300 it's read write 300. so i designed or i put together this portable cloner so i didn't have to use a computer because when on site you don't really want to pull out your laptop and try to convince someone to like scan their card i've done it but it's it takes some explaining so as i said they they this has an rs-232 out so i just need a level converter i first wrote the code in python and then ported it to c the hardest part was you
have to load the actual encryption keys into the reader and do all kinds of like key derivation for triple des and xoring and stuff like that which is not very hard but it's just confusing because they don't implement triple des properly so i took a teensy 3.1 board which is the thing on the bottom there which is very tiny little boards so because i wanted it to be very uh portable and i want to be able to shove this thing in a wall maybe in the future and control the reader and i have this device here today so i'm going to give you a demo shortly and this is just uh for scale we have
the 3.1 arm dev board and they bolted on the ttl converter which is from china and very china is a great place for electronics aliexpress so let's quickly do this demo pray to the demo gods
all right so can everyone read this so this is not on right now let's turn it on success okay so yeah we can uh let's mic this thing we can do all kinds of fun things you can program songs into it and uh as i said uh when when you read a card there you go so 5a is the end end of that string and as you see on this card it's 5a so we'll read it again just to prove if anyone else has an i-class card they can bring it up and i can show you this is show you what your data is this is a different card so each time it just spits out the bytes
unencrypted via serial so i'm going to stick the card there and leave it there this time and then i'm going to try to read a section the block 7 of the memory with the reader so i've got it's been controlled by serial right now but i could put buttons on this all of this is running in the tnc 3.1 so i could put buttons on it and and do all of this uh completely standalone of the computer i just didn't have time to implement that so what we've read here is nothing because i haven't selected the proper key to authenticate to the card yet so you see those ffff that's the data that should be coming back from
block 7. so if i select the key i get a 52 9000 which is the hex code for all good and then i go read and of course now we get the encrypted data and so i'll remind you that this card is ends in 54 when i scan it but if i select the key again and i write the other demo card to it now it's been written take it away and now it's a different card so there you go an i class card cloned which you're not supposed to be able to do especially using the own reader
and just for fun we will change it back so select the key again and then now when we scan it again if it will scan there we go and it's back and one more one more song all right do i have time left here how much time do i have all right so i have a few more slides i thought i think i skipped through some stuff because i was nervous but let's talk about a few other things then
yeah this was my ending slide at first i thought it was pretty clever but apparently you don't so uh this is this is how hid implements security on these readers by the way they pour a bunch of epoxy into them so you can't get access to the electronics so dudes take like pretty dangerous stuff like concentrated nitric acid acid and pour it on there to get to the board and and do reverse engineering on them it's kind of neat and this is absolutely terrifying so these i class devices they hook up to the network so how often do you guys know that of any institution that updates the firmware on their door readers never so if there's bugs i mean and
these things work offline as well which means all of the credentials and the data for authenticating people stored inside the reader terrifying and still advertising the wigan interface complete fail uh here's a my fare card and this card i was on site in germany and the customer is like yeah this is encrypted we're using uh des fire cards and of course i found that they're only using the card's serial number they're not actually using the encrypted portion of the card for the identification purposes so all we did was read the card serial number used a prox mark to uh emulate it and open the door on him and he pooped himself and and this lock is completely offline
so it's not network so you can't even tell when someone has opened it unless you go to the actual door and download the data so my fair i will give them some props you probably can't see it but they actually own up to the the weaknesses in their card uh right on their website you know and this is a huge list of weaknesses and uh they they know that the weaknesses are because they relied on the secrecy of their cryptography algorithm uh for for for the the protection of the data and we know in cryptography that's a huge no-no and then here they explain at the end although original residual risk at may it remains there are techniques and
counter measures to detect cards and data which have been tampered with but they're secret it's like no one can ever learn bruce schneier actually said the security of my fair classic is terrible this is not an exaggeration it's kindergarten cryptography anyone with security experience would be embarrassed to put his name on the design
and this is us in germany again this is my co-worker where we found a myfair classic card that was using a um and used for a cafeteria system and people would actually stick money euros in the machine it would recharge the machine so of course we broke the card and we recharged it ourselves and started buying stuff at the cafeteria and the great thing is you could actually go and get cash refunds so we were making some money on this gig all right so i've got a bunch of links here too if you're interested in some of this stuff as i said this is kind of standing on the shoulders of giants the only original stuff was i worked
with the guy from proxclone.org to understand how to talk to this reader but come to me after for sure i see a is there a hand up there in the back
uh not for the rfid stuff usually i tell them that it's really broken and what they should look for to fix their system uh apparently the new i-class se line has learned from a lot of the problems after like much pain but for example they have readers that are multi-class and this is one of the se readers here it says right on it multi-class se so this will read a standard prox the upgraded i class and then the i class se i'm convinced that there's no way they turn off the legacy portions of this so it's always going to remain vulnerable as well so it's it's i don't know and configuration is also a huge issue because the vendors that's
why i said never trust the vendors they always misconfigure something so we're getting in one way or another
uh i have never encountered one i know that you know in terms of biometrics uh hid originally was they were storing biometric data on the card for verification so if you could get one a reader that was an enrolling reader you could enroll your thumbprint on a card then because we know the where the data how to access the data you can just overwrite someone's legit card with your thumbprint and like and go in and just you'll be valid that your thumb will work
uh no they not in the systems that i'm talking about not that i've ever run into i'm sure that exists but uh again you're talking like military or high some some other high security installation probably all right thank you very much for your time
you





