BadXNU, a rotten apple!
Show transcript [en]
so welcome it's another 3-2 presentation three years ago it was a possible kids again it's the one full kids this time I'm not sick just good routine because I can pretend the insane number of slides that I have for you today ooh am I know me I'm playing it makes since 2007 when i bought my first bike I do a lot of reverse engineering then I started a blog which was mostly dedicated to breaking up productions usually when I download the new program the first thing I do is breaking the protection just for fun and then I testing program I'm not the mac salad people get a lot surprised when they asked me which from the US and
I tell them we just form but where the world OSX reverse yes so I use whatever words whatever I like so I'm not to make sell it if you want to learn about food kids I wrote a very long would kids articles formats for frag last year something or is it is very long you can learn a lot of stuff I'm writing the book or I'm still trying to write a book me and two other guys it takes a lot of time hopefully throughout this year or early next year I think it will be worse wait if you like you Stefan I have really been a bit of creating too many slides this one is 172 in my eyes I see
much here at least 180 or 190 usually the guide my life yeah Venus if you go to see the Siskin presentation you see Thomas Wayne telling me five minutes ten minutes then two years ago we seek one and I took like six shots of whiskey I can also see that because I kept talking and a high just wait I couldn't stop and up to do it so keep drinking and the fun part in Portugal I'm trolling the world with my domain the other part I Spanish in Brazilian understand this one it's very funny because now you have these guys linking to my reminder your CNN you have registered a lot of self and really fun stuff is going down and see
the link to my to my domain video footage the reason is their ultimate sir I say mind I just hope to see this one ever occur with you sky presume they would keep wakin these guys are so what I'm going to talk about how to load Colonel would kill specially by passing out protection set fos I presented least the first time last year in Japan in marching in sis can I'm doing another presentation based on the if I stuff that you probably saw on all the new ones very happy probably parties research breaking stuff and I releases your that if you want to have a very interesting to blog posts if you want to learn about these five go to my blog and
you can learn and then again a week or two you can see the slides about that presentation you can tell you know Rory gets these are big doors or not they are mostly design and implement implementation flaws because I hope usually doesn't know what they are doing they can get to be bad Colonel vulnerabilities i'm going to show you that the bench for his mighty that was released this week still in these two vulnerabilities so I'm unless my job makes my life very easy because I don't need to update the slides it's your work the coats your words funny which is the second one that I'm going to or the third one and they put some features
that we can use to bypass all their protections so I don't know if you can call it back doors or not it's your choice or decision after you see this presentation assumptions if you know me you know that I'm Economist economy's fly to put the assumptions you know big file because you have the IMF failing with their assumptions so but we still like to do this this is our model so this is where we work so the presentation assumes that you already have put in in a machine so I'm not trying to exploit and macros I can show your or I'm not going to show you because it's others did your day stuff but it's not that difficult to get
routine in mac OS if you try to estimate the probability of this happening I think this with you like and very fast because i have this your days for that i can show you the proof but anything below is probably wrong you cannot say it medium or instead base like windows everyone says bad-mouths about windows but windows is the chances are probably much harder than in microwave for example I didn't take this slide this part because once again Apple does my job my life easy because this week they release the patch for 10 10 dot for and if you go to see the amount of vulnerabilities that they bench it's insane a few more from this guy from
ian's beer so you have a single guy from google project european beer alike in two or three men like 10-20 vulnerabilities your days will route with Colonel called the execution all kinds of stuff one game so we can imagine how things are then we aren't funny stuff desire finally pension but you have the funny things like this they patch the tumor abilities in iOS but they don't care about OS X and I put this like playing day it really is a bullet in sight and she denies in micro its baby they don't say anything when I need this presentation for example this vulnerability for which projects he releases the next point of fully working late point that works without any
problems flawless they've already things for us mighty because they they got the bug from google one from matrix they didn't release any badge so you had a fully working next point out there from reliable working and amiable doesn't care about that bench but also these for example another example from a Korean guy friend tree moon is very good and he has a safari browser remote code execution with full local privilege excavation exploit so he go to page they are mikey is over he has a full security it's two words much easier ways to get see you cannot discuss this with me because I will win this fight video you can suffice the user the stupid mac
users give me our admin password and you got this small where I wore that in fact it normally 17k people just wait then please insert your admin password that it more fun stuff a lot of these sounders it updates going over HTTP so if you are a guy say once and you probably shouldn't download this stuff over HTTP you have applications installed with Ron permissions for example they installed themselves with the sweaty binary with on the on the machine with the with information so you can override and play some games then it can easily resolution excavate for example earns the backup help for a formats carbon copy cloner that you can exploit the first time the user execuse
and gives the permission again whatever you want so the question is the tax advice is really big on my knees so the assumption that I do that getting root is not that difficult I Mike so we can continue on hundred good kids so my goal since I like put kids especially the colonel completes because it's low level and it's way more fun intent username stuff please i want to let to load the bed code into the problem while Apple introduced the new policy basically dangerous is code signing in Mavericks in marriage it's not mandatory meaning if you try to load some kernel code that is not find it will complain it will say this this code is not fine but I will
all be genuine if you like sometimes because it's the first time they introduce these so they want to test to see the effect of this finally in use my keys mandatory if you try to load a kernel code that is not sign it will not load so these are three reasons why that's Colonel that hope Blue Mountains in the colonel first there's a good signature so you cannot old anymore if you as user if physical signature is invalid you cannot talk can't flow because it's invalid that was a trick and you could really hold your Colonel extension very early in the system Apple isn't x feature so is here for example unique a security product this brings you some
problems so it basically will put your bundle night competent not they certainly getting education so you cannot use this trick anymore what are the solutions the first one is what the spies are using if you are up to date for example i Dessay or the guys that sucks man and who and all that stuff they are basically with me suing the certificates final it costs you ninety nine dollars to get a certificate then you need to make a request and tell okay i want to build a colonel work drinkies tell them it's not for testing if you say it's for testing they will be knock to request it's just say i want to build a security product and they will give
you the right search be they could disable that feature i'm not sure if eNOS mighty it's it's still available in El Capitan if it's going to still available if you want to get visible as a perimeter inside disable everything you can attack from the e-file this is where I'm movie now this is a really fun world and essentially if you can Bronco that the firmware level it's game over you can be whatever you want which student firewalls
you can attack user this is really stupid you are going to see how good a please main steps you can exploit Carlton abilities because if it's if you can find a way to write to the kernel memory you can do whatever you want and they can abuse existing teachers which is what i'm going to show you last these are lying demons these are ever get me security video they have no idea what they are taking point there is no demon in my code is called kexp what it does it's the immune responsible for doing the co-signatory shank so if one more what do you want to load the trailer it sends a request this demon this theme it
goes to purify the container such as yes or no and that's it the funny detail design this demon is running in pink tree basically it's running gets to use reliable so it's not running in the curve so what you have is something very fine coat that you want to load that the lower prefers from a higher privilege this isn't make any sense because you can attack that process if you attack that forces it's game over they don't seem to learn there's a guy saying we are going to or there is a wee quest for using these to the car balls so they are building new feature in El Capitan you probably heard about it rootless if they
leave these like this it's to wherein the better version did you like this if doing this it's game over it just batteries and let it what you need to do this is the piece of combat unit patch and there's the call that function like static codes check validity this is the certificate related stuff essentially it has the codes shake the certificate see if it's valuable value return yes or no so until you do you attach for example to the process petra discount the shore in the XX or whatever you want to do what is your way of etching stuff and that's it you can load everything and to the current that you want hope and with
code signature or not it's static so you know you really just need a few bites and we bypassed yourself I wrote about it wasn't this specific attack in 2013 it was a variant for mavericks because Mavericks would love anyway at the time I just patched the warning because it will show a warning to the user and this is Colonel extension is not well so just by two medicines the message never appears and that's it so it's more or less the same variant about this so I'm not showing you guys in infinite loop then they were like they're really nice but we really are potheads and it's hopeless so my presentation could essentially end here because it is game over that it there's
nothing else to do but i like to wait for stuff and I like to teach people or charging people and find yourself I love this life and because it says a lot about the security field you have English further we have fireballs encryption antivirus software and is going on ending this farmer we update the date is the human so basically in the human examiner's and it's part of the game this is from always happens and so as long the critical there will always be vulnerable ities so we are going to explain them what I'm interested I'm interested in anything and an internal tomography that allows me to write the kernel memory for example you can get some buffer overflow
or some primitive that allows you to write anywhere in the colonel you can get some custom stuff that is from the specific to the mac which is the colonel test part this comes from the mac design and there is also the host rivlin work if you have access to be sports if you have sport and whatever you want to the colonel in the district of microwaves in the mac kernel which is part of it every process is represented by the task a task is just a container of data then there's a there's a point to respondents between the task and a process because the process is bsd process but the task is the general container the colonel is also a task and
you can't think about that as kids you this concept doesn't exist in other machines if i'm not mistaken in mac OS it exists it's the pto so more fun stuff before snow leopard depth or there was a feature essentially you could access the colonel using the task for p the task for field which is the task port gige beans I want this Pete give me the passport and they can access to to build process so you just say give me the passport for the colonel and you get a net it you have a DC described in that Frank article there were no steroids because we can write to the colonel this is the function and 2 guys I hired TT
organized the conference game in a in Taiwan and they report this very tracing vulnerability the processors fell tasks and insight is also easy and when I saw this woman really rang the bell inside my brain and I didn't know why and someday i was browsing this book it's one of my books thats always it on my desk is very stressing if you are interested in the term in the internal result in my class and i was browsing an exploit the vulnerability was there since the oak tree with nobody notice it but it was there so insight is always easy to after you're not saying it everything is very clear what tomorrow will it does is gives you access to the
colonel passport which is the same result as the best for you this is the function processors i passed see it calls another function this violent as a lot of code and essentially what it does it goes over all tasks that are running in into the season and returns dead part into an array testify stuff that we're done which is the defines to occur I will show you what what this means this is how you get the passports you need to do get some ports this is one of the reasons why you need root access because to get the O's part in row taxes so we feel good we can do this and you get the colonel passport
from the first element of the array that is returned it's dead or so it's very easy to to get as I told you this is your mud patch I was expecting these to be banished at least in El comedic still not back there knowing this page for use my dude it's also not there I have no idea why I hope is not patching this they know because i was showing the slides to them in and right there in one infinite loop i was this is about fitted and i presented to two times and they say use my teens every bit as powerful as it loads i say you've survived it is so what is it from you because they know
what about this file because that's what to secure Colonel define is there because this one doesn't have any nye ways so they had matching the bug in iOS because they understand how powerful the buggies in iOS because if you are then this part it price to iOS and Joan breaks will be much easier I try to patch this park and there are no side effects your Mac will work without any problem so I don't understand why they are not bad genes let's get to the fun part other it spoil please what we can do if you get the kernel corn what can we do with this world we can allocate internal memory we can read and we can
write and modify write whole memory i will show you what i mean by right about dressing in a bit we cannot change the memory protection of kernel code and some beta sections because they are made in the army and we cannot execute code because we just have access to transport but we are from a different from a different task so we cannot change the pointer are directly the colonel watch somewhere else so we need some tricks what are some kernel protections the level guys are really bad at security but they implement some stuff for slowly but they do it the kernel code is reductive you know apples snitches connections to bike home like crazy and the colonel is made Reno me
but this is at page while so you can see this is the code from the kernel that finding the colonel is initializing it changes the page table to reload me this is a reason why we cannot make the code it cannot change the deprivation because a function and is from a higher from a higher level and if we try to change it cannot because the protection is education Bible the same happens to to battle sections they were made with only for example before you could see the data section is writable and you have for example the deceased all tables and the market are tables then you just need to modify a pointer and you can get code
execution now they are they are real and so you cannot detect this is called directly these also happened in seemingly not when I said at a sample durability you could attack the table because it's rideable mouse real ugly there are also another trip they made the table itself read-only but there was a pointer to dead table that was frightful so what you do is create a new table input everything their original you notify the pointer that you want and then you change the pointer that points to the table at it and the technique is always called shadow Siskel table and it comes from windows I think it was some cannot remember the name but it was a
little screw tip that implemented first piece technique most of those pointers from the dead section is the god section so you cannot detect any more like this you cannot put the shadow table in his mighty you can do the same in one every person before they can you can with this is the data section being very naughty also also you have not execute the data protection you cannot execute code from from various the the protection is my that page first level is basically best practices and probably all this stuff was introduced by white parks and gr security because they are the guys that did most of the innovation and last using insecurity if you know
this low level stuff it's possible to provide this protection because there is a register cr0 which is the control register which is change the back piece wpb which is right protection if you send that bit the tunnel will not colonel panicky to try to write to a rebound adventure but these rings you can earn a problem because to build it to change this we need to execute code but we cannot directly execute code yet then you are also the curb this is not very difficult to to bypass in OS X you have a cisco the KS an underscore info that will give you the offset of the of a SLR in iOS this is my this function
doesn't exist once again I don't know why a diplomat leasing OSX you can have infolinks which is what everyone is paying based on to get slightly police and you have something else there are other techniques a reigning rope is chapter for the book and it developed a new technique when the book is out you can can read about it so it's not very difficult which easy easy things we usually work most of the time so my goal is to execute kernel code there already told you about the matter problems we can't execute code we can use the siskel tables we cannot do that trick and the Mavericks are older we can use the the shadows you stable which it's very easy
to implement so for those it's not to be problem how much it should will like that will attract internet the kernel extensions you could try to attack the kernel extensions because we have the Caroline the kernel extensions they are also protected they are made we normally so it's not interesting to to attack what is the solution and become if you come from the good kids you know that this means direct Colonel object manipulation which is finding data objects in in the term that you can't change modify that do something that you want the goal here is to find a writable data structure that we can modify and then somehow it's a code execution we can execute the
small shell tops and disable the the CR 0 protection and then we can do whatever you want in a easy way or you can execute more complex code which means a full root kit from from from there I don't have much time to think about is the trusted vs vehicles just in future very big introduction it is a mandatory access control framework the ball the project started in three BSB ever portrait parts of it to tomorrow s and that the project is called trust VSD market is a subset I think we call it recipes PSD just for for richness but the framework that Apple part is the max frame work of art it is the basis for OS
X and iOS sandbox for example the gatekeeper and the code signing also use this the latest feature ruthless in El Capitan this is the same ruthless is essentially global sandbox if it has an engine a decision engine that's it I want to write the system folder which is protected it goes to the to the colonel axis on the list is these authorized write this to this place yes now and send back the response and if you are used to exploiting you already know that how to exploit this because there will be for example update is an authorization to work the file so attacked the update process and you attack ruthless and / subjects but it
has many hoops available i love i really love this framework and police posing access to it today they say it was never made public and now there are doing some internal changes and they are closing exit this is a very powerful framework because we have many hooks in the kernel that allow you to control a lot of functions in the system so you can build for example your own module 2 to control and stop physical to mind it up for example there's a module that if you try to execute a swanky binary it will send you a warning and back saying this problem this implication wants to execute is slightly better do you want to allow we want to deny you want why
twist for example PS process one to whitelist it's a warning it's some more information I also did something to annoy i think in guys it was the presentation at whiskey turn I don't like having team Excel those guys and it was based also on this framework so it's very powerful you should take a look I haven't really annoying i don't really not ample don't host this stuff because i love this stuff so we can politics you just in the kernel extraction beds heads volume on it has a writable data structures and it leads to call the execution because it essentially a callback system you put your whole bag and your gold is executed under certain
conditions how can we use these to exploit we have a new policy with a single hook we just need 1 1 code execution that will point to our code it this could be the shellcode that disables to CR 0 or it can be the food with root contain a medley and then we call the function that we have the hook and that starts the root case let me quickly go on what to do for this the sex we need a colonel passport because we are writing Colonel we need to find the slide because he will need to change some stuff and the colonel and data structures are somewhere so we need this we need to compute the route concise
because we are going to copy and install it in memory we need to move gate manner to put the work in there or we can find some free space for four days then we need to copy the rootkit to kernel memory remember we are executing from user lines and we have you have to put somehow the coding in the colonel then we need to change memory protections because if we locate the memory is not executable pi by default then we need to fix the simple service external signals and this is the funniest part or the more interesting part at least this one because we don't we are by tracing the colonel linker so we need to do
implement basically implement our own liquor let me install a new recipe policy and execute the hook to start and you probably want to clean up so the forensics guys don't know what's what's happening there and I line what the forensics guys I'm not sure if useful agility for for a while I was playing a little you guys because they have an assumption they think that they can find everything because it's a memory and I show them a few times our few more abilities on that stuff they think they will not find the colonel good kids with their software so don't trust and your tools I did talk about that just rest your tools always be suspicious about
that especially if you are trying to change route kids remember I'm running on that on a level problem lower than your tools so i can men employed all your tools so undress them and use them but be very suspicious about the spoons and this is the hope is all ready to show you to get the colonel test port plussing difficult and this is the code to get a slide using that function the K has info this is basically inline assembly you can import the function is not very difficult math nothing very type of it to compute the rookies sighs there is a small trick usually the site is different from the size on memory because alignment recent so if you want
to compute the brute keys because we are in our memory we need the memory the memory version so it's basically used fuel that gives you the size on memory and hot on disk because if they are different you are going to get round to locate Colonel memory there is a function the map you will see what functions bottles functions Mac on the colonel this is our function that is usually the passport that deal with the mac you can mark layer or our max traps especially what we need we need memory somewhere in the colonel you don't get because we are controlling a pointer we are not playing with offset so we have 64 bits a absolute address so we can we
just need memory somewhere you use the function the colonel part you see then the first parameter is the past is the past sports you can use this function for example to inject coffee to any program as long you are support offense that's the process you can do whatever you want and then we put size and and everything else there are some problems with is because if you do if you use these function like this and for example if you try to locate 100k of memory these you press your system what happens is that the whole memory is not wired why would mean that non wired memory it can be pushed out to this even from the
colonel attempt and what I memory is obvious they're physically for example the colonel grunting in wider memory because if you had a page out or a fishing on the colonel you could risk running the pressure running the pressure to to the to the Beijing system to this and then there is not no co2 to the deck so this is the reason why weather is fair no panic because the colonel do not copy everything when you copy it says it wise to each other I copied everything everything is not there to try to you sometimes line into Carla parents if you are trying to execute sudden just a small shell code this is not for example
of page is cool enough for some stuff for K is is too much you get it set at 64 K it was too much but for Kate and sometimes it's more than enough shell code so the result these thresholds what is the solution the solution is very easy you just need to make bets memory wire there's a kernel function you're telling this piece of memory that I located is wired do not crash out ever it has a small tree first you need to set the memory protection so first you say these memories going to be executable we try to move if you need and then you to change the wire stage with dysfunctional if you try to do
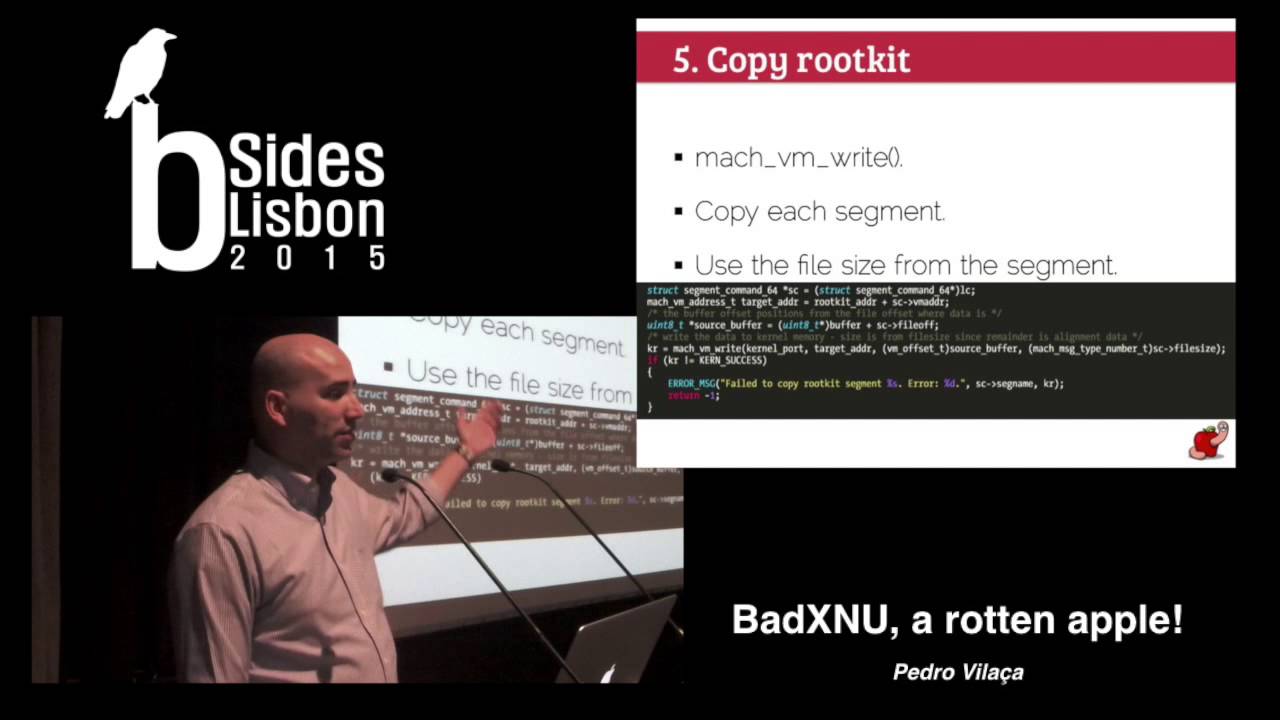
otherwise you will get this function giving the measure and you don't know why I spend some time these and then I translators just the trick to copy the rootkit another my function right you tell if I won't write these that these data to this process that is address we already of the price we know where the good kid is because we located the memory so it's medically hmmm copy in the kernel using the max function same for changing many protections you have a function called my vm protect you probably want to fix for example beta areas to not be executable this is once again to avoid forensics because if you start saying if you are changing
something at you see for example what's memory that is breathe printable and executable this is very suspicious so you want to put changes as normal as possible once again use the beautiful memory size field and because alignment reasons and this is what you will locate it to fix external signals the concern is Colonel aslr the kernel code must be the body positioning panel so you don't need to change the offset and everything in the kernel enduring the curve accidental call them colonel is based on upset so a function is called without an offset so you can put the colonel anywhere you want the offsets say always the same so there is no problem with this what we need to
worry about these days symbols this is the equivalent in is rent for a library usually you link and see if you are doing for linux or any unique system for example stp be able to get functions system functions you do the same in the kernel there are for example string functions that you can access and memory location function design and so on because we are by pressing we are doing we don't use the linker we are talking directly to the colonel week our own Colonel this is very complicated maybe I was like yes this is going to take me a lot of work and I don't want to write linker myself but in the end it's very
easy well all information you have rotation tables these are these are the same tables that the linker the colonel incurred uses it needs to know what needs to be fix it you have the same information in all our other formats be as the same information else as information you can find these information in those two comments then I dynamics in time it's in tap it's there the location where it is table is all the symbols that need to be fixed in and so on complexity and there are 10 different types of publications and you can start restarting okay this is why you need a lot of work but in reality there are only two bit that you between
into to face one is a relative addressing this is if you know if you are used to researching stuff this is basically 32 bits offset to somewhere and using the current instruction pointer so the log says embed equate the instruction pointer address was the instruction sighs end up sides minus or plus the null set and you also have some relocation of which are actual two dresses these are easy because we just need to cite point to this address and that's it I know this because I get the small agility to go to all kernel extensions and get the number of symbols and I know only those two types are used and there are two two and two types
external which are the singles data data linker does and local local are strings for example that you I 1-yard code if you f and some other local kernel extensions symbols for example the stack and stop functions they are theirs so this is not very complicated to to do this is some code there locates and the tables then finds the symbols to which they could respond to then try to solve the current symbol to locate the target signal for example I want to do Mary copy I need to find where did my copies in the relocation them I need to find where the map copy function is implemented the colonel and then you just need to fix the offset yourself
this is what the linker does when is thinking it's very waving this work this is a little code I like these on purpose it does about because offsets here is a 32 bits and interior and there is no guarantee that these all set will be nuts it can also flow and it will point tool to somewhere else written for this is that we are implicating the Tyrell somewhere else in the colonel so we get current memory so we are no guarantee that's the address where it is in 32 bits away from from the colonel and this is an interior signed integer so we have off of the space half of log set unless this year is just as worried what we can
do is using trampoline for example you can put junk from death from the characterization to some space you locate when you kill the colonel session we will cater sprays for for an island that is executable you jump there and from there you can use an absolute address because you have enough space and jump anywhere you want so we are basically in directing the flow of a problem so it's not very difficult to implement it's a very easy way to work around the problem these are the actual defects these are very easy you find a single where the similes and we put the whole offset the whole address and deliveries to process and these are related to the to the local it's
essentially there the local ones are always absent addresses so they are even easier to an end to things so fix to build your own linker it takes like what 200 lines of C so as you see it's very simple it appeared a very complex problem with inning or something that you need to spend some time but in the end it's really easy to build so out of line interesa PSD ah I will not go to how this essentially there is a very important short the one which is a global variable that contains the information but first BSB as the number of policies that executes and all the policies that that are within the system this is the structure for for each
policy this is an array that contains all the policies and this is the policy configuration for example we can see the name and full name and this is one contains a function pointers are the hooks and this point to another starter which is a really big structure with all the hoops available in the system what you do you register call back you say I want to for example to to get a hook that's every time the access its function is executed I want to get the call back so we put the function pointer that to be our function that will process please and
Yahweh go about this because it's which is basically you do yourself the word you install disruptors install a new policy and inside the pointers in that way there's a something to facilitate your work which is the rain is already okay so we don't need to allocate memory they pray locator right with it i think it's 256 or 512 entries so you just find a slot there we put there and at it then to start your model which is what we are going to use to get code execution you just increase inside a system there's another module and then the system will go to the least and see okay this one's to to get a comeback ever sent a call
back that's when we start with roofies in our example i hope this function the task for people because it's very easy very simple you just call a keep an on Pete you can use the big one which is munchie-t which is equivalent to in it in windows so you know that process is always there you call it and their end you probably want to do add some kind of fuse so your code is not executed for example if father hole is an object if you get your route get executed so you just need to execute once you to fuse there and that's it then you want to clean up all the stuff you don't want to
leave a trace that you use the trusted be policy so we decrease the Houston I'm the number of loaded policies there's no problem in doing this and runtime and then you remove all the memory that you located and how that stuff you just leave the Woodley's in memory I'm sure
okay this is the one of the portions I content voters voters the person that uses this way of doing this version also as the the google exploit this one at this version of that one lithium is still vulnerable for to this so i'm going to execute these feral expansion valve Allah controlling our coke quick this is a very cheap this is the colonel extension that I that I built for anti anti debugging so some processes there but involving this will do NT NT debugging for for it so I'm going to connect to betray my attention okay selected and let me show you okay gtv this this is a sample code that is anti debug and running and the debugger is
found so I enabled the anti debugging run again nothing but you're fine so it's running I wanted code from from a normal user using the google exploits we'd be smaller and i can show you there is not mean that in the slaves nothing even the turtle was the colonel accession isn't old using the system stuff was all the directly with a strict and let me show you the last three and because we are living the buffer we need to put get whatever we can for a temple over the remote good case okay and here it is this came from my side this is a reason why it's funny 11 p.m. because i don't know if you can't hide and i will
be demo and getting hacked myself so the variable ford is it's just as a printf view nothing complicated came from my website so for example you can you can have the loader and you can have the payload on remote website then you can clean up and forensics cannot get probably not much information from from the good kids so it's the technique is variable because it's all those allows you to do this kind of stuff to next technique you click on front wheels and sorry for your references to windows I used to work with players a lot and there is to be the device which allows you to access the kernel memory directly it's something that is closed now also the
dev / man is also closed or it's protected because essentially you could act as kernel memory directly from that defines these option exists in Mac OS it's not activated by default because it's so powerful you can enable it for example for testing and debugging you just need to go to that configuration or to any fear am setting and said Kim n equals 1 i'm going to do City metrics is Colonel extension ample HW access Colonel expansion it allows you to write access physical memory this is the trade physical memory so you can read and write up to 64 bits of memory you don't have a full control so you have to send requests for 64 bits it takes a while
but it does this when I saw these i would like a [ __ ] thank you yes baby once again i saw this this the same implemented in a keen Tosh forum which is running mic mac OS e in normal computer hardware and then tonight ok yeah but because the guy was complaining know this can crash the system and a la la la and do you immediately so i was developing the first technique and my break connecting finally a lot i start to use this one you say because I have the core techniques and maybe I can use this this feature to do the same virus diseases the reasons why they went to different work there was a debugging framework
shot it was a canal extension they convert it to a private framework because these this these debugging tools need to connect the colonel they probably created this connection extension because it's not missing I can find in the system that uses this what we can move with this corona extension or this feature we can read and write every single beat available the almost understand why it's there and we can my pants all the read-only protections that I've shown you because we are accessing the physical memory so vegetables protection doesn't matter we cannot allocate memory we cannot change memory protections and we cannot again once again execute code directly till there are some restrictions once again and we
need to bypass this is how to use the function where you bypass is very zzz service to send their only two structures involved that request for in it out if you want with you say i want to read up to 64 bits and I want to read from this address and then you get the contents in the pub start this by Sigma 0 is to read the function is executed then again you can forget that you can copy the data if you are willing to write the more necessary just essentially you give you copy data that you that you want to do i get the structure and doubt you get it went ok or not other it's flightless what we
need again the same steps we need to copy what kid calls me to fix of locations that that's the easy part now I mean we need to start the good kids what are the problems with this we decision we need to find memory because we cannot allocate memory as a Tully we can find free space on honestly for example the colonel Heather usually it's not guaranteed but there is usually spice from the header to the first place where I put where cookies there's usually some alignment space which is essentially 000 ever since you that memory is executable so if you find space there you can use it for for executing stuff good intentions they have also alignment spice we can try to
put there you can / white kernel functions for example what what the morning shelter was doing the Gator gets a function thank you for example NFS stuff if you are attacking a target that you know they are not using an offense and if s is default on my colonel so you just write that stuff and it are you going to locate memory via shell code essentially you just need a few bites for the shellcode allocate memory and then you do whatever you want good execution it's easier ear because TV we can buy protections we can use the fiscal balance you can go very complex and use the same trusted vsb you cannot hope the kernel function because we can
write anywhere so it can be very creative about it sometimes find the you want to find the amount of available memory because we have prior to reads from the from the colonel we need to boot for some stuff so you don't you don't want to go out of bounds because if you go what other funds here it's a kernel panic right away you need to find where the colonel isn't useful number and if you can do the routine size rice and everything else and I decided to attack at cisco table because it's the easiest method there's no point is complicating it's very easy to find the table there are many places that are free you use one of the three places you
know the system remember you called X is calm and is it and then you call that Cisco and start to get this is the same stuff so easy to find the the tournament system early there is a function for for that and it's possible to told you it wasn't real every bit in GMS and there are two solutions 14 there's a smart solution and there's a brute force solution the smart solution is exploiting a subway of the car when in your system starts there's nothing in memory so the colonel is put there in memory and then it's sleep somewhere depending on the offset so what you can do you can read the dress where the
colonel is from to this that is the original address on the system then you're the slide so we know where the colonel is in virtual memory what you can do you clear the highest 32 bit because of physical memory you have 32 bits there and you know what is very easy trick to get the physical location you can use the brute force solution which is start from zero go to to the amount of system and find where the perilous these winter problem was right and remember the time yeah this works on TBN first time I were put on a physical machine and there is a reason of course you have machines exceptions which is you have a lot of stuff devices and
everything that is mapped on physical memory unusual you're very lower oil prices so if you try to read from that stuff Colonel back this is the reason why you cannot do this in Kitty paw machine these are some drinks that left by biases and 12 to two people this is what I told me the language space between the text which contains also the headers and the data segments you can put stuff there for example in May braids it's not enough you cannot put a rootkit there for good kids and just might at least have that version 2.0 there is enough funds you can come to a good hitter so it depends usually my solution or my best
put a small shellcode colgate memory and put everything there just a warning that night sessions are not wired as I told you 32 p.m. we will get pinched folds if you want to use a shellcode to this k mama lupe it's for country which I'll get to continue you can use the normal memory allocation but probably those function is that it's not guaranteed that Vista memory it will be continuous so you will need to find this piece of man where each page will be located this is too much work there is a function that can tease you to give you physical memory that is continue so why complicate what canvassing this is a shuttle we go there and look but in
Thailand as a stylist it's like Twitter bite or something the shellcode battle cage vortex memory and when yes everything that you need to do good kids there I'm saying find ok fun this is called table and you just there are some signatures for example you know where a certain function is because you can read the colonel from the disk you know for the cisco f will be located at this address you just need to go to all the tournament fight workpiece addresses and you know where this is table is and this is how we start the book is just on the cisco that you hooked and that's it and my bestie just once singing point detail
if you want to execute code and multi-part CPUs essentially everything and you is multi board we have a lot of course various dysfunction NV ren days it was presented by nima Frank article it guarantees you execution on 12 cores of the machine so for example if you are using the trick to visit cr0 register you need to guarantee that execution is happens on all the course because this this is racism is per core so for example it is about these not one car that part is okay but then another car price to execute get cold kernel panic because dead car as a protection enabled so this is just a very small let me put another
demo very weakly so these are the mighty that was released this week and time plot for and this is the second portion okay once again the same put it by Road so it's for begging you can see takes a lot more time because it because of the 64 bits maximum request so we need to send a lot of requests exchanging the colonel everything else and okay if I it's there that was executed with using these three so we can do the same would keep bypassing all the protections that there are against this compulsions hopefully i will convince you that or FX cuties don't tell anyone crap total brat there's the funny thing about this as i
told you i presented this first thing in japan and months ago or something i got feedback and the first comment that they sent me was from an attendee fi no web will be broken but it's not nice to call able to find that i love this quote because i don't know what what was the translation to japanese punk wasn't that funny but because the guy was really japanese that will be promotions I hopefully this your you are in these days the colonel extension code signing as it is is useless because it's running on on on reign three if they don't put on rings the bell rings you it's not Allah there is no pointing doing
don't trust it as a security measure there are some plots people telling case there is Colonel extension co-signing it's a security feature dr. soon because it's useless and my question whoever when I was everything [ __ ] teacher dead why's it was even exist because if you are designing something to protect at least give it requires some problems that that I shall be awarded a shortly there is no issue product advertised policy for example Apple releases patches for maple correos mighty doesn't release the veggies except matches for matrix so even though I still run this laptop running kills my food on my plate that stuff is to my friends I don't know for example they release a fiery passion
for Lyman which is a radio version but they don't release security patches so we don't know at least windows you know and Microsoft's told you windows XP it's that unless you pay 20 million light than 80 to the US but this is there an ordinance to know there will be no matches for for this essentially you either upgrade or you more vulnerable and even if you want bring your suit on rule because I end up in touch for a few Apple saw the presentation so it's it's great this is my personal fight I tell them this a lot your strategy is essentially reactive and not proactive and you know this why because I really feel day on the e-file aight three or
four weeks ago and that will this be very surprisingly to me they release the patch today if I back so finally and they released to pop top all machines for example final five year old machines it really is the bed and then they don't do this while it is my personal opinion is that they had bad publicity because that's the point everywhere they don't like publicity and so they react to the issues there and they are not proactive on that they try to be proactive for example they kill to protest but at least the system like these now is a joke because we for example you've attached to the k xt process you patch it these two words are still work
so I don't know what they are doing if you want to look at the gold Barry it's a real one the pita and go there there's tons of code blue code is very well commented people working on the SEC and yes it's amazing one your slides everything is very commented what I don't put it I don't lose comments i like to do it because I never know what a week before while is changing stuff so it's good comments this is my blog it's very easy to memorize part is good you are makita and I feel free to email me if you have any doubts or if you have any issue and there is a small community
on freenode OSX r e if you have any problem with the max or or if you are the first hangover hanging stuff come there you have people there whether non guys from the mac OS machine feel free to come there and feel free to put your problems okay