Actioning ATT&CK
Show transcript [en]
How do we build out those controls and capabilities? And they're executing malware on the endpoints like so many others. They have a good C2 channel like so many others. They're performing lateral movement like so many others. They're doing persistence mechanisms like so many others and data collection. So it's not unique of what they're doing. And I think that there's a couple of different ways that we can start to identify what they're doing there, which then feeds into what we do on our purple teams. Really, it's kind of a driven by what we understand in the field and what we see attackers doing as well as from a pen testing capability. For those not familiar with Purple Teams, really what Purple Teams are is this cross-collaboration
opportunity. And I forgot, whenever I first spoke, I had the picture of an ace up the sleeve. And what I often find is that from a pen testing perspective, we've often had this We're not telling the blue team, those that are in charge with pretending malicious behavior, what the red team is up to. There isn't that collaboration that's meant to take place there. I think we're starting to break down those walls, so I'm excited about that. And I think purple teams is a great way to do it, where you're taking a collaborative approach. You're saying, let's test out what an attacker is doing in the environment. and understand, let's try out each of these different test cases, map them back to ATT&CK, and then understand how can
we create better alerts from this, where are detection visibilities, and where are our gaps. So this is giving you some perspective of, again, aligning an individual test case to the MITRE technique, and then testing against to see what we're able to detect here. And this is actual real world examples. The product names have been scrubbed for the ones that are all not detected. Sorry, those weren't good products, but I'm not going to say who they were. But what we were testing here was really a couple of different EDR tool sets for an individual. I wanted to see what were the capabilities here if we're looking across the MITRE ATT&CK framework What does it look like from a detection standpoint? Really do we have a lot of visibility there?
And is it blocking? Is it detecting? What's it doing if I'm sitting in the admin console and there's an attacker on an endpoint? Am I going to know about it or am I not? And so it was a very valuable exercise and one that we're often doing. And you can see here this is then where we roll those individual test cases up to a percentage perspective of being able to understand what tool sets are maybe deficient, what are advanced, what are intermediate, and then how do we leverage those that we really need to be able to stop attacker behavior and focus on building those out and improving those. Maybe the tool set that made a lot of claims about its capabilities, but it's not really performing here.
Let's not invest in that. Let's not take that energy and effort. Everyone's got limited time, effort, and resources. So let's put it towards the best capabilities that we have there. And we'll say, as I'm thinking through this, the MITRE ATT&CK framework, one thing that's very fascinating to me is that intentionally or not, it's very endpoint focused. Endpoint meaning not necessarily a user endpoint, but endpoint being servers as well as users' workstation. But really, if we dive into it, A lot of this activity happens on an endpoint. It's a lot more challenging from a network perspective to it. There are a lot of it's gonna be, but a lot of the attack endpoint activity that's occurring there. So from an EDR perspective, the endpoint detection and
response capability, I think that weighs heavily into the ability for an organization to detect attacker behavior that might be aligned to the micro attack framework. This is just a little, worksheet that I utilize as well to run through different variants here and I think this is helpful for describing for example, yes they do, but what does that mean? And as we can see here, what I've really tried to identify is ways that attackers can change their techniques to be able to bypass some controls here. This was an example of an ADR tool that If you had download string, so it was a PowerShell one liner. PowerShell one liner is simply a way to simply grab a script and execute it in one line. Often times, maybe you
can add to another tool like PowerUp. and it often encompasses an invoke expression and download string are the two key components for that and there's variance to it, right? And this hits at that variance simply by putting download string in quotes rather than having it be download string, now that EDR tool did not detect it whereas before it said there's an alert, there's something malicious going on here. This time it did not detect it. So it's important for us to continue to test against multiple different capabilities and really to understand how do we identify attacker behavior for the variances they're taking. So I hope I'm not overwhelming, but if it is overwhelming, I wanna touch
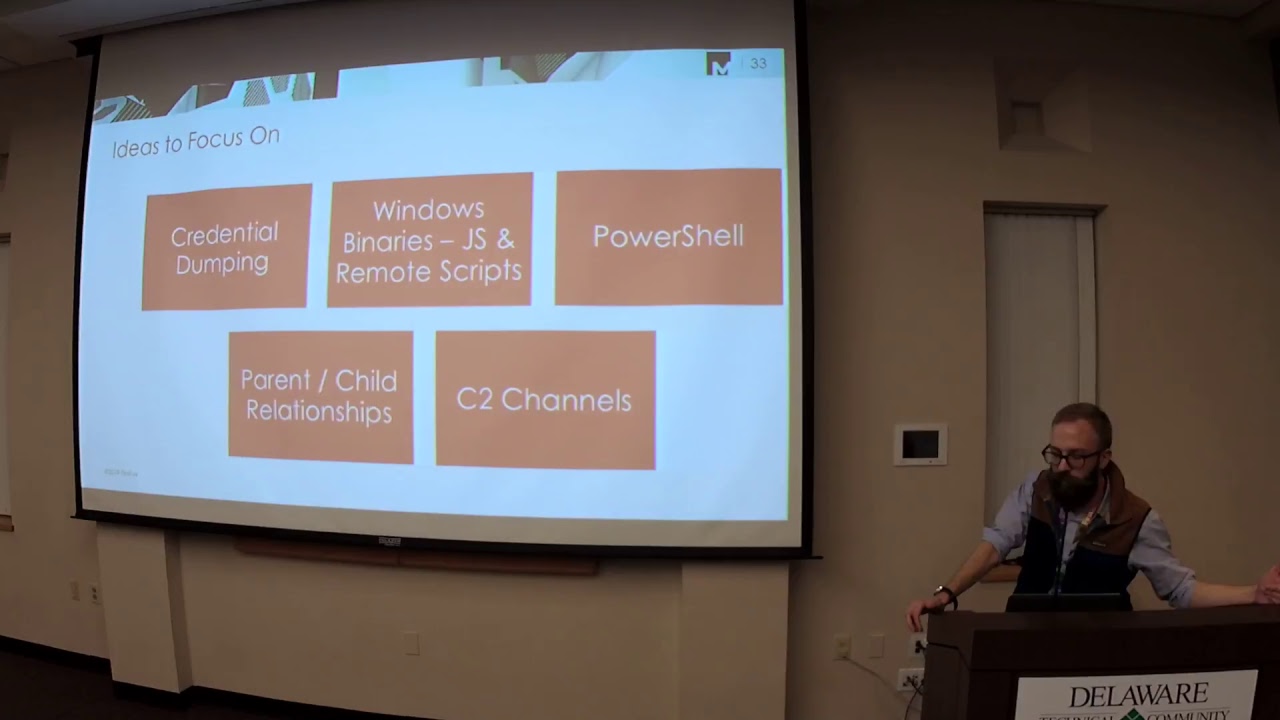
base on what can we focus on in building out those test cases. So as I mentioned, we can dive into those different test cases, We can dive into those test cases for every single MITRE technique. So really, where do we start? Where do we stand? If you're looking to incorporate MITRE ATT&CK at your organization right now, what are the ones that you want to be looking for? I would certainly say building out those test cases around credential dumping. As I said before, credential dumping is really about, a lot of times, from an endpoint privilege escalation perspective, about getting access to that LSATS process within Windows. So what does that look like from being able to detect that? And if we go back to here, you know, you've got
a pretty good solid list to start with, I think, of different test cases that you can try out. You can go through different variants here or being able to identify what this credential dumping look like on an endpoint. Maybe start off, you know, if you've only got Windows event logs on your endpoint, what you'll quickly find is you've got very little visibility. So maybe putting on Sysmon, playing around with that, free Microsoft tools, seeing what capabilities you have there. That's probably still not sufficient. So how do we bring in something like an EDR tool to be able to further detect those capabilities of an attacker on an endpoint there. Another component that I think that we see time and time again is Windows binaries that
are behaving in an atypical way. And this is, Again, there's a component in identifying attacker behavior. You don't have to identify every single thing an attacker does, but you want to be tipped off to it. One of the things that we commonly see is an attacker using something like Rite Server or RunDLL32 that has atypical commands in it, or MSHTA. MSHTA is a prime example of this. It's an old program that is meant to run Windows, sorry, web pages on the Windows system. What attackers like it for is that they can run JavaScript on your host and they can send that JS file right over via email and then you execute it on your host. So there's some things to tag
off here that you can start to play with and identify, being able to identify whenever JavaScript is executed by some of these Windows commands. You'll see that under the execution is the name of the tactic for the minor attack framework and you'll see like right server in there and run DLL32. And it allows some components there. There's a great red canary as an organization and they have what's called the atomic red team. And so there's some test cases that you can start to run. Some examples right here to be able to run those. Likewise, running a remote script from those windows binary is something that is not typical. PowerShell is another component, as I mentioned, that is important to identify malicious attacker
activity and the ways to bypass that, looking through or invoke expression, download the screen, network connectivity from PowerShell that is not typical in the environment, as well as there's some different techniques of conversion downgrade, different attackers looking to bypass logging they'll put in the version 2.5. So playing around with that is great. Something that isn't called out in the MITRE ATT&CK framework, and I don't know if they just don't have a wordy way to put this, but it is around parent-child relationships. I think this is very helpful in identifying what an attacker is doing something. This is an example of this, a common example, time and time again, is the command prompt being launched by Word, or PowerShell being
launched by Word. That's strange, that's not something that someone's doing on a typical process. You will find some within organizations, some of the accounting team might have some reason for doing that. But you can start to whitelist this, start to identify what's normal, what's not. And then from that, start to very quickly identify behavior that's occurring, that's malicious. We see this, especially around that parent-child relationship, during the initial compromise phase. So it's really the attacker, let's say sends a spear phishing email. They want to convince the user. They spawn. They open a Word document. They enable macros. Suddenly, now PowerShell is spawned. It does its thing. It downloads some additional malware, installs that, establishes C2 channels, that sort of thing. So by
identifying that and alerting on that is going to be very beneficial. Command and control channels, I put this in here. as I even put it in here, I can kind of save it towards the last. The reason for that being, one, there's so many different variants here, and how do you separate the noise from what's typical. Command and control is about the network communication going from that endpoint back to the attacker's system to be able to communicate there, to be able to have that persistent mechanism that's in place. These C2 channels, the challenge of it is they can go over multiple different communication paths. So you're going to be looking at a C2 channel that's communicating over DNS and using legitimate DNS traffic. You could also have it going
over a web port. There's multiple different ways that an attacker can leverage this. If you're not doing, let's say, SSL inspection, you're not going to see even that encrypted network communication that's occurring there. However, I think that it's still valuable from a CQ channel perspective to consider what are some of the low hanging fruit that you can start to look for and identify. For example, if you've got a lot of quad A and text records that are occurring from DNS on a magnitude of millions of number higher than normal, that's probably indicative of something that is maybe malicious, maybe further investigated, and that you're not going to see a whole lot. So I think that there is value there. would say let's strive towards identifying
atypical network communications occurring there. I think combining it with these other ones will provide a lot of value. So whenever we want to map these back to the MITRE ATT&CK framework, really it's about that credential dumping, the execution component. Execution is around those Windows binaries, PowerShell, the parent-channel relationship, and the command and control channels. There's going to be additional components that you can start to quickly and easily build into it. For example, there's one piece of that defense evasion within the MITRE attack framework. And there's one that says whenever Windows metlogs are cleared, that's something that attackers have been known to do. One nice thing is Windows metlog, when that happens, if the attacker just clears it right
from WVU till, you can actually, it generates a new alert. So hey, put in that alert. It takes you 10 minutes to do it. Let's continue to get coverage there. There are other components that are going to be more challenging. So it comes back again to that prioritization. How do you prioritize what you want to identify and know what's really going to be legitimate attacker behavior? And if you see this alert pop, that you really want to know that it's something that's legitimate, that you're not getting up at 2 in the morning to deal with, as well as from a severity that is actually an attack of behavior. So I think that's kind of the overview and summary from how I see lighter attack being implemented.
We'd love to open up for questions, and if you want to reach out to me at any time, that's my email as well. Thanks. Any questions? Chris? Sorry.
All right, no questions, no questions. We're at 10-4. So thank you for your time, everyone.





