Fir3Ey3 Mail Scanner

Show transcript [en]
welcome to [Music] my so this afternoon um I will explain you uh the system that I deployed at home on my network to capture a lot of spam a lot of emails and to detect malicious emails like the fire High Why fire first because I was looking for nice for the and always CH name speech just so the first myself so I'm coming from Belgium my name is and I'm freelancer doing security every day doing my day J but I also have a night job so I'm hacker blogger I maintain the blog for years um I'm Co organizer of the security conference nice event by the way in Belgium and for one year approximatively I was also a Handler of Internet St
Center so it means that the internet St Cent I don't know if you know the the organization it's US based but we monitor internet4 hours a day we capture a lot of data using only butons and we write di we try to keep people up to date with the latest TRS the latest it's very very interesting uh my profile so I basically I like data uh and more your data so I like to collect a lot of stuff on the internet running onlys running tools and for example I like grabbing Base website looking for my information certificates Source codes passwords I'm playing active defense uh I prefer t-shirt and tie so that's my business to and I I like C for example
this this kind of project I call this a a one it's my drone I put an Point behind the Drone so I'm able to above my neighbors using the and to capture a lot of nice wireless data so that's I I'm doing such kind of nice stuff usual blah blah blah this is my to I'm only speaking for myself so nothing to Fire and let's drive now to the topic of today spam I presume that in this room everybody gets spam is Spam every day for years and we we like we we receive a lot of spam so basically when you have an email address even if you do not communicate email address you will get
SP by a lot of nice guys trying to to send you messages but but what may be the difference with you that I like really I like to collect a lot of spam all the time but not all of them so basically the different type of stuff that we get for yours it's you can buy for the men in the room blue PS can be interesting some sometimes you can get some nice online games you can buy Rolex you can become millionaire based on the SP that I receive if I'm following all those emails I should be millionaire more than Bill Gates uh and all the G because I receive millions and millions every week
and a lot of special offers but really it's not interesting for me that's not the kind of spam that I'm looking for but basically I'm looking for this you also receive nice invoice also I don't know why but I get invoice I buy a lot of stuff on the internet I get invoice all the time all the time also I'm a good friend of printers and scanners because I got a lot of notification I scan this page I this facts and I get nice documents or from time to time you rece interesting FES so this is really the way the kind of spam that I like to receive when you receive such kind of spam the first that we have is just a
basic attachment so you geta and attached to this email you have a file Z file EX file J file and you people done people just open the file click on it and the file is executed the this is a scope in uh during this presentation because it's very stupid stupid the next type of spam that you can receive is an HTML spam with a link to a malicious file that you have to download so it's not sent in attachment but you click you download it and then you open it same it's autoscope in this case because it's who will open XF who will start EX xile maybe more than more people than you expect but
it's what's really interesting for me is this kind of email so you receive an Excel sheet a document and it contains a mro basically the trick to make you enable macro it's a protected to and for most people if it's protected it means that it should contain very interesting information next time maybe I password I will some financial information from organization some some Bill some some interesting uh projects interesting andot if it's protected by default people think protected so it contains small the other kind of documentation that we the document that we can receive that's really at the a pain at the moment is Javascript files which is so JavaScript it's not JavaScript based on
the web technology that you can receive but you can also have the Microsoft version of JavaScript which is executed via wscript.exe which is standard on all Windows operating system and by default when people double click on the JavaScript uh link it will be executed and usually people will get the characteristic of such message f is that first there is a low detection by basic text fil so a don't have time don't have the capacity to take and very important those files are not man it's just a script which which will execute all the actions and one of them is to download a payload which can be remote or local we will see an example later so it's notu just a and it's scrip
language so we have multile ways to achieve the same music it's like a developer when you ask a developer to do something to ACH some result there are different ways to achieve it and it's the same foring language toload the there are many ways to do this on on window system before going deeper I will give you some quick tips how to protect yourself it's very easy the first one as I said when you receive a Javascript file atgs by default on Windows there is an association with w script. a colleague of mine on the sun's website wrote a diary a few days ago so easy to replace the association and instead of associating the GS with W
script just associate not part of the so if your user will double click on the GS file the not will pop up it will get the script code of the the scpt it will never be executed it's so easy you can deploy this using GPU that's the first the second one is of course disable macro in offices Microsoft aware of this problem and with the latest version of Microsoft Office 2016 there is a way GPU to disable micos honestly some people will always complain I need macro because blah blah blah I think that in 99% of the cases user don't need micros because have a look at a suite like Microsoft Office you the regular user use only 10
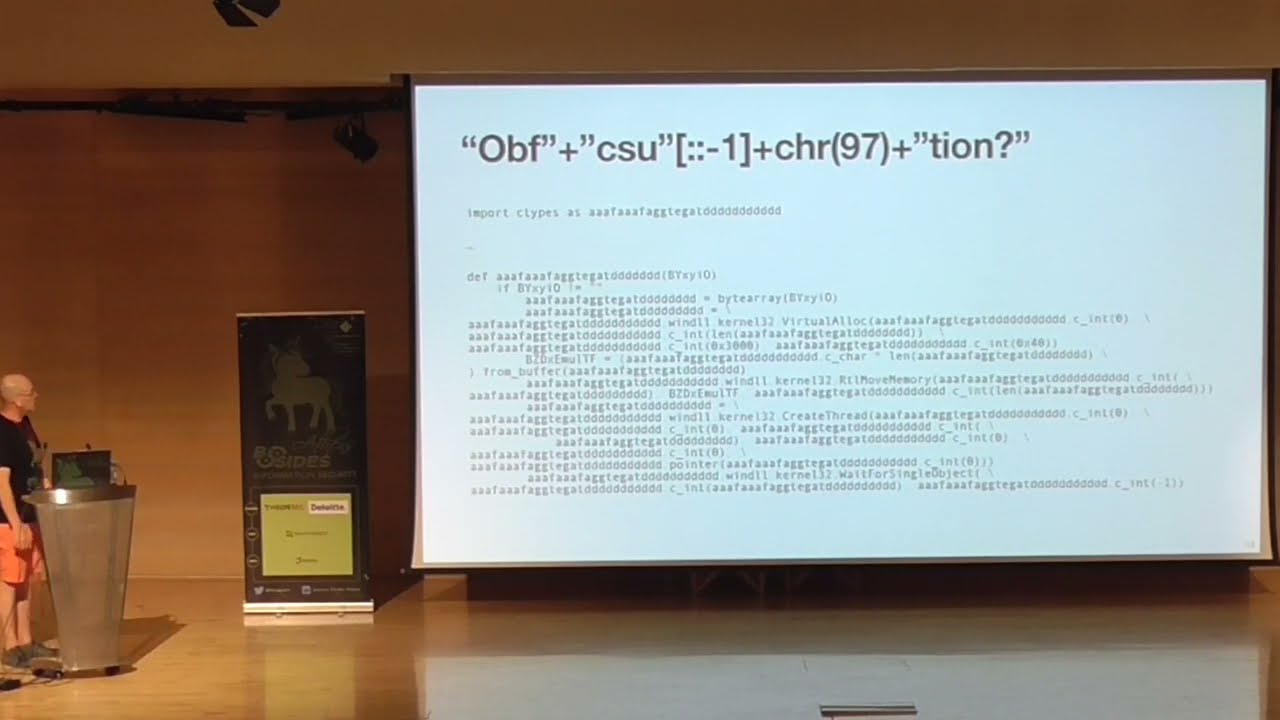
15% of all features so why not enable just disable them GP and if power user needs the micro just the separate group and the stuff so that was too quick too quick to protect yourself so back to use macro of course the macro are OB because if you try to to read the macro by default it's unreadable for the human unre it's very complicated to read them and this is an example so this is the the character uh I made a mistake B I made a mistake in the Shoulda so the go is to off and I will show you some example off that's the kind of script that you can use so this one is quite easy
because the script is split acoss multiple variable and this one is easy because it's just a concatenation with plus of all the characters in in the M that's quite easy to to De with G this one is also nice we have uh a function which will remove all underscore from the string so by default when you read when you read this you see from a human point of view you see that it's HTTP respons so you you see this for
computer this one is also interesting so we have multiple variable again the code split and we have some exal replacement back SL back sln so Line Car return inserted we have some uh another one another one and you see that the code is split across multiple varable and then the goal is to concate them the last example very nice I catch this one from last week that's the latest Loy campaign ongoing for a few days you have double oppostion all the script is in one big variable and this no sorry sorry so this one is um is a nice one every word is in um uh a table and there is a specific function which take the last the last
element from the table so basically what we have we have act X OB X City X and the Environ environment and so on and so on so again very difficult for computer to read this and to see if it's man but I really like this one because you see that the size of the the table is different time you have two three this case you have only an empti string and so it's and about this is the one that I found last week the variable contain the W script so I had to cut it because it's very very long it's a few Kil but this string it's so simply we just split using nothing we reverse because you see
that the script is starting with r space so far blah blah blah and so on we reverse with John and this SCP is also inated so you have two layers ofation that's the latest comp for and of course the system so where is my payload usually payload so the script that you execute is just drer and usually the mici files are downloaded from website read WordPress jumla the classic CMS which are unprotected which are un patch and so on so in most cases it's aable WordPress instance but also sometimes you can find the script add itend to the file itself and this is nice example uh I discuss about it you have the re for the full analy on
theet stor Center website the file was a a link file on Microsoft for Microsoft which contain this small script and the script looks for a specific Str eqq AA that you can find here t2a and the rest of the L so what has been happened the 64 version of the P file so the executed so the script just check search for this Str put the the ring part in a temporary file using decode deod the basic and ex so in this way you download the L file using em but there is no more communication so you can detect any transaction using that's so why fire again OB today because the this presentation has nothing to do with firearm just that in
my de job I'm playing with fire High devices and honestly those are very outome devices they collect a lot of interesting stuff so that's really really nice appliances but I see two main issue with fire ey first they are very expensive when I say expensive really really expensive so it's only for big organization and don't expect to have fire yeah you can buy if you have a lot of money but small companies more than M business they don't have buet to buy fire devices and also the second issue for me is that fire is very conservative because malware IC is the pro business and they don't share that's for me the main reason fire don't share
and yes they write nice block post when they find new attack and so but there is no way to share to share I so my idea was okay I rece I need to analyze this almost real time so what can I do and that's part the first tool that I use well usually when I do manual analysis is thep it's a tool written by D Stevens It's A friend of mine a very nice guy with a lot of background and the tool is quite easy on the first the first examp you just issue the invoice do five as argument and you receive a dum an output of the all document is built and you see
that the section A3 has a h which means thatc so we time the using so we section A3 using V code the macro and we get the code of the which is this one is quite easy but it's also aible because you see that the variable names are unreadable it's that's nice but this tools is requires manual inter so you need to download the file you need to analy the file and so it's very important because I'm a lazy guy I like to automate Stu so the idea is to automate and I was looking for a solution with the following requirements first to extract automatically some my from emails to analy device of course if possible to
block them because by so it's not my goal because my my goal is to collect files and to analyze them but it will be also interesting to block them for the regular people uh of course to collect data samples URLs and to save the result for research propos so I have database of samples when I receive them all the score and and so it's it's very interesting the component of course you need NTA so you need mail server to be able tole Maes you need some nice domain names and miest of course you need to filter all the garbage so I'm using spam assassin and for pre filtering so why do I send emails about blue bills on to my
solution no I just need to collect male suspicious containing juyu so theing is done so I'm dropping already a lot ofs it's based in pythons with some modules of course you need a VT so here is total API and the other tool that I use is o I will talk about it sources of course you need to grab some material you need to grab some spam so I'm the L owner of of some very old domains that I own for more than 10 years so I think that my main domain I home I this domain I registered the domain 15 years ago so it means that I'm the Rie guy who has nail on every
spammer database in the world because my email address is everywhere um and when Once when you have some nice domains just add some on email and some casual mail boxes what does it mean I have some domain that I register a long time ago but I'm also a big fan of nice domain names today to buy a domain name it cost you a few per per year so it's not very expensive so I I have some nice domains that I never used so I just put any on them and a casualx means that if you send something at my domain it will be cash and will be processed by my so send to send to blah blah blah send to this
is email address domain.com it will be cat process so that's and once you did that you can first you can sleep and wait for the spammer to reach you but there are other techniques just use your email address and say em address on nice website B website forums register and so on and you will see that very quickly you will get inter SP to analyze so I took about OA d a few minutes ago so the goal of this tool is like o it does basically the same but the very nice feature is p API so the goal is to EXT to automatically submit the file to the to the API and it will give you interesting result it will
re analy Al extract ioc's and give you a nice overview of uh the result my script is called M why because the name the the first idea that I had when iot the was just to submit the samples to so I extract the Mind Time generate the hash and send the hash to to to see if it's known what's the score and but I added one and more feature so what does the script it extract M attachment from emails you can also of course restrict which kind of attachment unit because it's useless to send to send GI files and so on so just an just juy there are checks or that are submit to V so I first I check the hash if it's
not existing I just submit automatically the file to Total the main issue that I have at the moment that V total is not real time so in real time so it mean if I submit the file to it takes a few a few minutes before getting the result so I'm not able to send the request analyze the file wait for the result and to uh of course it's files because most of the files are coming in in Z archive because usually they can they have a higher chance to be by the classa of course I have a big database of samples also I'm extracting URLs from all emails could be interesting but it's pretty why it's very difficult to
automate the the process because when you you will get a lot of and of because for example you have always the L to subscribe all the links to the product all the links to companies and so so it's very very uh complicated to process them automatically and as a bonus I I can I'm able to send all the data to the processing it's also sending data to CIS my regular sis M so I'm so we can generate my statistics this is an example a classic output so I'm using postfix postfix receive an email from an unknown user the script detect different mind typ so we have a t we have the message we have different uh attachment but nice
msxl I'm also extracting the name if available so that's invoice detail blah blah blah when you read this you have tiue that is prous so the script found an interesting file the file uh has been this is a hash the file has been scanned on VAR total this is the actual score by V total and the file has been scanned at this time stamp and I'm so Computing the time difference so I know immediately if the file is a brand new one so it has been scanned by another guy a few seconds ago a few ago the one because and then I'm also adding some I'm adding a sec database so I'm adding the hash in the database with
information like the F name the first time that I saw the file the last time the score I can also I have the first the initial F total score and the last so I can see if there is a trend more amount I to detect the file uh and uh I have a a graphic about this the number of time that I detected is sample because you will see later that I Reed the same multiple I don't know why so this is the kind of output and that's the output of the analysis returns a lot of information about the the malici so you have is able to detect some interesting strength like warning total because you think that we have a
war and name so that's concatenation for some interesting words we see ioc there is an update WIS we got suspicious update exit and we see all also suspicious API Cod shell run create right if you see this basically the setup it's basic so you can Define your PR toal API be careful so I'm the happy owner of are official key so I mean that I can submit a lot of request because via one of myomer and via the S uh internet Center I API key I can submit a lot of files to VI to but by default if you register an account if you get an API key you get only four requests per minute for a normal user that's nine but
when you automate stuff you will break you will read the total limit and F total will reject all the requests very quickly you can of course excl some my Ty that you are not interested in while submit PNG GI she and so on you can specify which elastic server you need to to send the data to your database and this is a sample of myy so every time I receive an email I'm just doing a carbon copy to my script which use the STD to get the file and process it so based on this so I say I'm collecting a lot of samples so this is uh this graphic represents the number of samples that I got for the
last three months so April May and June you have the different kind of extension that I got and you see nice that's quite a nice number so close to 13,000 samples in fact those are Z files and it you can corate this with new Lo comps that's incredible every time you have a new Lo compaigns on the way I'm SP and able to detect when something specific occurs so that's the nice dashboard now the next one is I get some samples so how do samples are detected by regular antivirus I like the statistics so 43 4.3% half of V above five that's very bad very very bad and you see that what's not detected have
6,000 samples next one is four five and so on and you can see that I also have some HS when the score is no so no f is detected with more than uh yeah more than 20 yeah I have 30 35 but so on are doing very bad another one that's why I said that I receive mle times the same samples this is number of samples that I receive for the last three months it's not bad this one so the this one starting was see so5 I receiv it close to 300 times I don't know why I don't know why this is the so it's msro document uh I have no idea why the the
script was the sample was received so so many times what's good by the way is that by time we see that the the score is increasing all if I checked I I I think that I wrot the slide three days ago so maybe I the the score increased but I I have no idea somebody has suggestion yes it's because they they're basically trying to hit as many people as you can in the organization maybe see it's it's because I C all mail boxes so blah blah blah at the same domain so they same problem London email address there they they just look for every possible variations that's they start they start dumping emails cu the more that they
dump the more likely they're going to get one through and some and the cost of an email is zero it cost nothing to send emails today so so if you want to play my script is available on on my g account uh I'm not developer that means that for me that's really bad code I just it like this and so it's not optimized and I'm sure there are BS and so on but once again the goal of the script is for my usage to collect data but feel free to use it feel free to expand it and I have some I have a wish list so for example I would like to to for M system I see more and more a
lot of hard files also I'm I'm also seeing some cab more and more cab files coming from Microsoft um I have the plan to integrate it with mist to exchange ioc's so I'm a big fan of mist which is a tool to exchange ioc multiple organization so it will be interesting and of course if I cannot y support I can go y rules to better DET so that was my presentation it's almost time for some beers um if you want to reach me so I'm very active on Twitter my private email my company email and of course we have the sons if you want to reach me thank you very [Applause] much