Stop Shooting Blanks: No Magic Bullets in Your Arsenal

Show original YouTube description
Show transcript [en]
[Music] all right before we start just to thank you again our sponsors and turn it over R excellent okay I'm not very good at staying staying in one spot behind the podium I kind of tend to wander anyone who knows me from Dallas know it's like the ADHD Renegade thing it's just what happens so I'll try to beh here all right uh I know all the recommendations are don't do a long intro for yourselves so I won't uh did want to cover a couple of things anyone who knows me or deals with me on a regular basis knows motorcycle video games that's pretty much what I do order changes on a daily basis um drinking I
should probably have highlighted now of course being a computer geek every time I tell people oh yeah you know I love riding motorcycles they kind of already have this preconceived notion and I think that's it they go oh Renegade 6 rise motorcycle are you on the back you know I be plan to answer that I think that's you if you're on the back you got nice leg so actually uh so normal that's uh that's me that's what I enjoy doing it's what gets me out of bed in the morning um long ago I decided if you hate what you do every day you're doing the wrong thing so do that um this what this is my conveyance this is what
gets me from point A to point B unfortunately my point B is usually like getting into trouble so and the nice thing too is with the line of work that I've in with just my day-to-day job and because of my hobbies I I get to beet law enforcement and we get to interact frequently so oh that's the wrong picture I didn't to show one getting fris there's one where I'm shaking his hand friendly this was like 5 minutes after when I asked him a dumb question so all right but that's my intro that's much that going to go into um looking through good no Chris Nickerson I won't get punched in the face okay um I like compliance Frameworks now this
isn't going to be like a compliance framework talk or I'm going to tell you check in the box it's really cool um I like them because they're a road map so if you depend on it for security like you're like oh hey I checked all the boxes I'm good to go uh you're going to have issues so uh I like to pull this one up okay you to talk to bed testers you talk to Red Team folks in general everyone across the board right what's the best environment to test the one where they're like yeah we're comping man we just had the Auditors in here we're good to go you're not going to pop anything right again punch in the face
it's all down uh in the right up you see that I mentioned uh the fourth you know the old magic quadrant fourth you know uh quarter all these things so I worked for a pretty good company for a while and we'd have vendors in all the time like constantly like oh buy our stuff you have a lot of money and we like money so you you give money we'll give you a box and it was like okay that's pretty cool what's your pizza box to do this week you know oh it does XYZ but we're the best at XYZ okay maybe I need ABC whatever So eventually I got to the point where I said you know what I need a good analogy
I need to explain to people why buying fourth quadrant isn't necessarily the best thing out there so came up with this one it this is actually good having the follow on top because I love to eat you wouldn't know it you know back um I realized very quickly one of the best analogist is you're going to have the best products in the world right you're have the best ingredients you can have topnotch everything but if you don't know what the hell you're doing wow that's what you going to end up with you can give me trues you can give me like all this like great a stuff I'm no Chef okay I tell you right now I can
mess up like all your fancy cheeses and you're going to get mac and cheese that's what you're going to get you know it's not cool so my the analogy is really that a framework is a recipe that's what you're doing you're following a recipe right you're doing X you're doing y you're doing Z bought this device and you implemented it bought this device you implemented it not necessarily well but you followed a recipe well chefs follow recipes right but in no way does following a recipe make you this okay you're you're not so you follow the recipe but you're not a chef you make a better dish than if you follow recipes at all no recipe at
all a chef can sit there read a recipe and make something real and I make the argument that's what a compliance framework is so you take a compliance framework you use that as the basis and you make something good out of it okay just can't follow it directly you have to kind of switch it up a little to fit your taste and fit what you're doing so if you're following any of the major compliance Frameworks right any of them right off like PCI you know anything there's certain key devices you're going to have right because you have to check box so even if you just check every box there's a couple of toys that are going
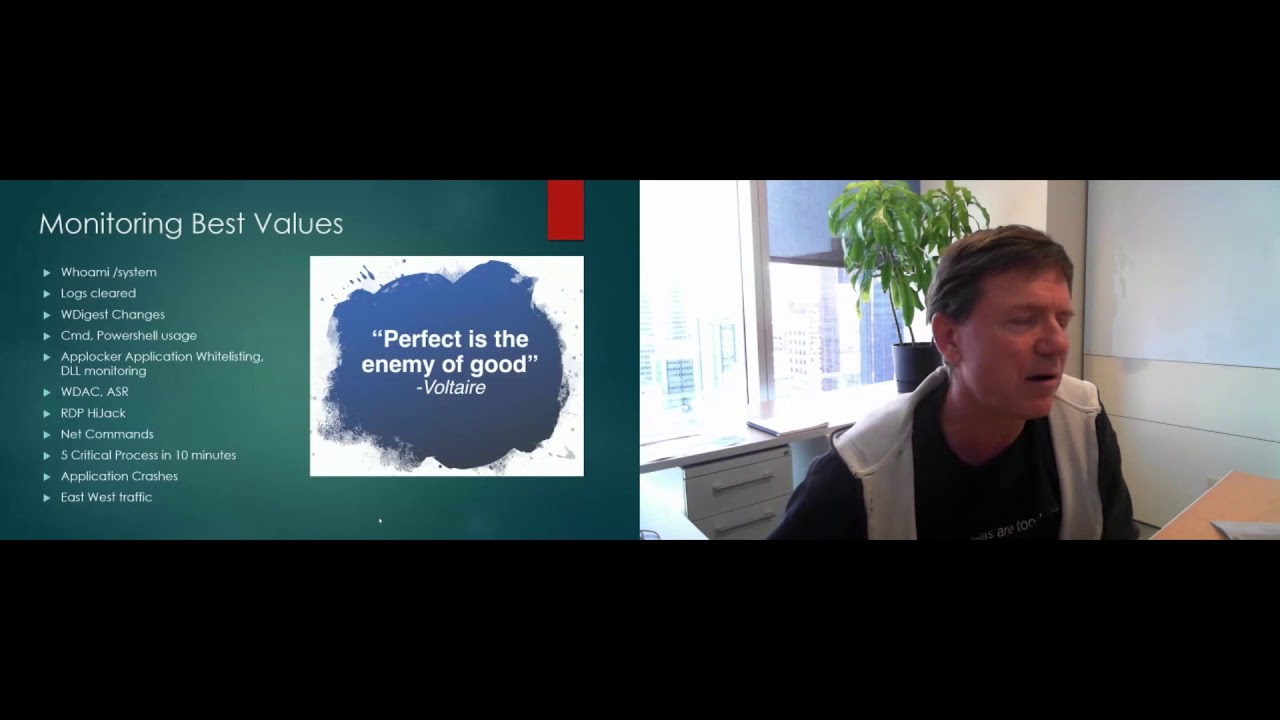
to be on the network that someone like me can come in and use and really what the basis of this is is okay everyone stop buying crap stop buying more tools take the tools you have because of compliance or because you actually just realized you need these things to make an effective security program use what you have all right it's kind of like the old biker thing ride what you bring you know and so I like this because you you're going to have your IDs maybe you have an IPS Maybe not maybe your environment that doesn't fit well you're going to have your firewall you're going to have a right everyone's got a and don't worry we'll talk about
a May you're going to have logging just about every client's framework requires you to have a logging solution what you do with it is up to you okay and your heads your hips you may have them you may not these can actually be something as easy as trip wire just watching a couple of folders on your system or it could be an honest to goodness kids solution like something from the Caff policy orchestrator all right what I'm going to go into is what you're going to do with that H what are you going to look for and what how are you're going to use some of these other products on this list to actually create some security on
your network and do some stuff may not if you can realize you could um and that's you know pretty much the takeaway of I'm hoping here you walk out of here you'll go D I have all of this stuff on my network I can do something with it what will you say that a lot of these products we already have the def configurations the vendors provide to us or that the vendor implementation group their consultancy their people we are don't necessarily Implement them they're you can take all the best ingredients in the world and turn out swiss cheese you can buy your number one fourth quadrant and if you don't tune it to your environment I don't care who
implemented it but if you don't tune it what's really the point and if you don't use it effectively what's the point and so good segue um and so this is what we're going to talk about is here's a couple of things you can do in hindsight I could have called this talk like stupid Network tricks you know I just capitalized on that but I wasn't completely sober when I submitted so so right up front because ad gets pounded so often I am going to mention ad and I'm going to talk a little bit about why it's not cool but it's not an AB bash talk okay we're going to move Beyond why AB sucks we know AB is not
the best but a meets a purpose it does what it's supposed to as long as you remember what it's supposed to do which is you can't face an inent Response Team policy off of it it's there to catch the low hanging fruit okay so what we're going to do not going to replace your a Solutions I'm not saying that detecting malware my idea is going to be like so inherently better that you can fire a maffy okay it's not for that it's just saying hey we're going to work around okay so also um I wish we could we're not going to solve diabetes insomnia or anything else okay but I'm going to show you how you
can may sleep a little bit better at night okay and that for me is a big thing so originally what kind of sent me down this path I'm a busy person I don't have a lot of time time messing around with stupid stuff and to me dealing with AB alerts trying to find room cause I don't have time for D okay so I always thought this picture sumed up pretty nicely I'm busy I got stuff to do I don't need your issues your problem so what I so what I do is I do a lot of instent response and I come up with this as a hey here's how to make your inst response go a little faster a little bit
smoother because a lot of times you're look for that needle in the Hast stack where are you going to look you got to go to these logs you got to look for this you know on your environment this type of alert may be totally natural where on my environment that alert red flags all day so the when you walk out of here like I said some of this stuff I'm hoping you'll just walk right out and go this is what I'm going to do from now on it's not easy you're going to do some work you're going to review a lot of logs uh for a long couple of uh months I think everybody was calling me log lover
um I think at uh one of the Pres one of the groups that I go to uh they played the red and stimy log song for me because every time it's logs I love logs logs logs and there so sick be logs but you need logs and you need logs for everything now a lot of people are like well I have this you know Sim product I have whatever guess what I have a massive s it's arite it's ridiculously large it doesn't do what I need it alerts me on a stu it shows me can Stu it does need things but it's not customizable to what I need out of it so you have to be prepared to parse those
logs yourself and there's a lot of logs um last count the script that I'm running through and logs that I'm parsing it's not uncommon for me to hit about 10 gigs so I have to parse through about 10 gigs with the data why AB sucks right we know this no really AB sucks AB is not designed or is it going to catch some of the things that we need to be alerted to on a network where's sprad test where pen testers red team people always say I took the payload I fed it through I masked it I took the virus total and once it stopped being detected I went ahead and used it in my P test right
okay yeah that should be the key right there we can't depend on AB but if you while back I think AB also gets slammed forist off but they shouldn't um when you had the whole um new New York Times getting compromised right they blame MAA or they blame semantic dude that's your fault you got compromised you didn't pay attention to your systems you didn't enforce baselines you didn't react to alerts your incident response didn't do XYZ how are you going to blame AV AV is not driver for that AB finds simple malware and does a little bit of logic but not much we have to do the actual thinking and find those compromises the other issue is AB isn't
going to pick up system tools when you get attacked the average attacker isn't going to dump all their special tools onto your system why they don't want them compromised they want to use them plus when you're looking at Network traffic for your network and environment you should know you're going to notice odd traffic you're going to see weird tools right many people are going to pick up you know Microsoft's rdd right you have Windows servers someone's logging into Windows servers you have RP traffic on your network if I compromise your system why the heck am I going to use some exotic cat Library when I can fire up Microsoft's RDP and I can blend in with all the rest of the tools
and all the rest of the traffic already on your network I don't want to call attention to myself AV is never going to detect that you've been compromised and registered these bad R connections never was meant to so to expect that out of it it's just unfair I did mention right ad cannot be counted on okay so that's my ad thing of like I said I'm not trying to replace it I'm not unfairly bashing it but at the same time defend it a little bit and you have to be realistic in your expectations of it so let's talk in a t right red team people they have a set Rhythm they go through compromises everything it
follows a set pattern okay and it's that pattern that actually drives a lot of what I do and a lot of what I'm looking at you're going to have a reconnaissance base you're not going to just start tetting to boxes and hope that there's a tet right you're going to know where there's tet okay do day AG we hope nobody's running Tet but you know they are so the Recon phase is not to be overlooked and why because Recon is going to be just before scanning right Recon the network find out what their who their people are what their Network ranges are right it does no good to scan Google for open ports if it's Microsoft
your actor so you better at least know the right IP range obviously from there we can expect to see scanning eventually we should see some exploits against systems right and then they're going to want to keep access and they're going to try to cover their tries so what I'm going to do is I'm going to talk a little bit about these different phases and what that means for us and what we can do with it so Recon Recon is kind of hard to detect um you can't see what people are Googling well unless you're Google and then you just track it right but as a general Joe myself I don't know if somebody Googled me or not I have no
idea doesn't pop up a little Twitter thing and say hey you have a new follower I wish you did but I can also get really annoying web searches who is I can't do a lot about that what I can do is I can set up alerting for DNS Zone transfers right why are my DNS records being transferred out of my network if I'm not partnered with you I don't want you to know where my boxes are so I can monitor for that um axfr and isfr I added that U that was a favorite trick of mine for a long time in isfr if you're not familiar with an incremental you tell the server hey we've exchanged data once before but my
cash copies from 1903 could you just send me your updates at news flash if the last time you exchanged DNS Zone trans Records Was 1903 essentially your update is going to be everything in their DNS record um that trick actually does work so I alert on that I want to know if someone is trying to transfer and then of course U looking for the reverse lookups if you have a lot of DNS entries coming in and they're trying to enumerate your systems you'll see that in logs you want to alert on that for just it it kills me you can find and group force a lot of the systems on a network who some really
dumb tricks IE the company's name with DC at the end DNS at the end or as you see with logical right I'm sure everyone here knows they work for a company and they have like a machine named four or you guys like oh seriously come on if I find one more G I'm just going to like n it okay so basic monitoring is what we're going to do here we got to get we have to have logs to review the logs so that's my thing on you know just you got to make sure you're logging cuz without it you're going to have a hard time detecting the Recon phase and also for all of you people who have Sims or
whatever for the love of any higher power that you do like red yellow orange green all that yeah Skittles and jelly beans that's all it's for okay it may say well we only had a yellow attack what doesn't matter if I just took your entire DMC infrastructure whatever you have data leakage you know whatever and I see a lot in Mark side people get hung up on the colors and they don't look at the impact of what's actually Happ so all right detecting scans I actually had a guy last week who told me it wasn't worth the bandwidth trying to detect scans what if you're being FTP Brute forc from China I think that's worth
detecting I don't do business with anyone in China I kind of want to know that my FTP servers are being improv for or that I'm being scanned or you know Port scans things like that so I think it is absolutely worth you know having uh those logs and we can visualize those logs to get some added benefit out of it because how many people have seen this that sucks right it's like o look I had log five I'm going to tell you right now my ADHD prohibits me from reviewing more than 10 lines down in that log five okay but what if your logs look like that this is ridiculously easy to do and makes a much more of an impact on it
okay that's pretty straightforward right it's Port SC really common ports right three your Microsoft maybe your R database it's like okay it's pretty simplistic but this can be cut straight out of your network logs and sometimes visualization can actually just help out again you're with three targets right with one source like okay but how effective is that on a much bigger event that pulls me up to this this is actually the UPnP scan by HD more because I do record scans and because I do vog them and then because I can feed them in and do a quick visualization this is what's going to kill you guys has anyone figure out anyone know what this
is this is maligo see everyone thinks multigo as an open source o right that's what it's marketed at what does it do it draws relations between data and draws pictures okay I suck at drawing pictures I can't do a stick man okay but you take your logs and with a real simple just a few Cuts here and there bam so HDM releases his UPnP um results in February February March of earlier this year before he had released it we were one of the few companies that had actually picked up the fact that he was doing the up& scans the uh top there which those are actually HDs machines that he was running the scans from and
those are with my machines and the next day I sent him a nice email said hey long time fan first time emailer love Med project first would you uh oh I'm sure I'm not the first time Target I said what would you mind not scanning my systems for a bit I'm really busy and I could use a break and uh he responded back he was like yeah no problem and he did um now showan has picked up the slack and I have those games every day for UPnP but the reason I like this is uh when I got a chance to sit down and attend hd's talk he said very very few people had detected it let alone said anything
about it I would not have seen it if not for this my logs are easily millions of lines every day you get lost the lines lead into other lines you don't see the relationships you don't see that you have one system who scanned maybe a thousand machines on one single port when because of time and because of the mass amount of data you're dealing with it's buried in there so I find a quick uh visualization comes out with that and so that's uh like I said I wouldn't I had no idea you're going to be scanned by HD until I did this and immediately this stood out and just kind of went you know ding ding ding you have a problem
so and in general it just makes it easier to read okay those logs don't mean anything you just look at them you got to be able to do something it's got to be actionable this helps draw that so it can be something as easy as this I mean I throw in time stamps I throw in my source my destination what the what was the detection on the power so all right for all the stuff on scanning um you can see a lot of these watching for service scans your FTP DNS all that um just holding on to those logs now I go down this path because I am going to tie this in uh towards the
end I'm going to show a couple of different things and we're going to tie them all together just before we uh finish this off so jumping gears U the big one right we're all worried about our users right there certain key things about our users now we would hope users don't have admin rights should understand they just want to go see kitties you know little cats is awesome and yes I spend quite a few hours my entire life worrying about what my users are doing at the moment at the same time you got to be nice to them right without what's users and no systems unemployed okay so since they're not admins this is one of the things
that I noticed real fast working with syst of compromises when you're looking at a system you start seeing the patterns and the patterns for infections almost all the time fall in the same areas you see files being written to assessed from pretty much your internet local temp your app data local temp and temporary internet files right now you make the point internet local Tab and temporary internet files pry much the same thing Vista versus Windows 7 you know minor changes things like that now the reason for that obviously is when you are in the web browser anything that happens obviously dumps where the web browser reads and writes this data from and internet local temp be one of the
major ones if you decide to run an application from the internet but you don't download it completely it will download to inter local temp and then execute out of the temp but that's also where hidden eye frames Drive buys and everything else they dump it all to that folder so one of the thing like I said we started noticing this right away I started monitoring for it and right away we started seeing uh results from it yeah so what we did was just set up some simple hips rules and uh or HS both HS mostly for the detection hips if you're going to try to prevent it let them run and then every time they trigger send
that over to your logging solution so now you have your network logs and now you have programs executing out of Internet local town you have those logs all right and like I said we're going to throw all these things together before we leave here and I'll show you why that's actually important so exploiting systems right pretty much you know we know that they're going to exploit our systems through our web browsers Java and anything adobe's ever made I bring that up because that's where you're going to find your exploits on your system if they exploited Java where do you find the malicious Jones in the cash in the Sun and all that if the do is getting popped you
find it in the Doby trees so by using app data but then monitoring the different products you can actually get a kind of a heads up to what product was exploited bed off of what folder the tree are pay from so indicators of compromise this slide is hard to read on purpose trust me indicators of compromise are essentially XML stylesheets that have the key data in them one of the things again right off you start realizing is if you notice the first one is the zero access um we have our wind login and we have the troen right you see it again there if you look on the third line down you'll see um I'm
sorry it's actually the second one when you see local settings application data uh the temp again and all users application data okay so what we do now is we started monitoring those areas waiting for the triggers and then we alert so does this work right this is why everyone's here this is part of it either that or it was a really good talk see you came to see me either way I don't mind thank you um so our user right oh my God what did you do that for so typical AB alerts like lock files they suck to read right who wants you don't want to review that so in trying to make them easier to read
and trying to detect them faster I found a neat little trick so most of people in here if I did tell you you can detect Mal way faster and without a signature that's that's a bonus right I mean I think that's pretty hot stuff well here was my first stab at it ugly system log right now there is actually this system was compromised and one of the things that I keyed in on was all of the command tool access by Network aware application should Network aware applications be accessing the command line your user maybe but even then most users don't use command line they flip out and you see a little that red you know black box and you tell them
dude you're going to type IP fig they go not me right so in this case why is command exe being called you know or you know being accessed by explorer.exe right that's no point there that's no good so I was like okay this is kind of Handy it's heading in the right direction I'm getting notified um and in this case uh we did actually find um it was compromised and then these were the applications that were on it uh I don't know about you but if I install oh I don't know Microsoft messenger I expect it to be called Microsoft messenger. exe or something similar not yeah you can't pronounce that right not randomers so I was like okay this is
good this is a head start you know this is heading in the right direction well then I started looking at some more of my alerts and I started seeing a lot of these ActiveX loaders but then I said you know this has got to be a precursor to something the system gets this ActiveX loader warning and then so what well you started noticing six days later right after this thing's happened it's being picked up so what this is uh you're seeing is so on the fifth I get this alert about this ActiveX loader that was coming out and either you know Windows Explorer or adobe or whatever then six days later the thing sets off
the ad alert as having a Java exploit on it I'm like oh wait a minute this is happening more than what could be H you know happen stains this is happening too often I see of X loer where I see the legal API call or I see this and then that exact same system just a little bit later now comes up as a virus aler so I said I wonder I bet we could do some more digging that so typical virus alert right came out 30 April PS password stealing right everything's cool pre pre generic this is what we expect until we go back and look and see that at least five days beforehand I had
already picked the system up because we were monitoring all of we were using the HS on the system to monitor those local internet TS all that monitoring the registry keys and right in here you can see the uh SNK 00 PT exe being added and the registry keys for that executable which were the ones that were marked out as being the actual executables for the PSW uh uh Trojan so right away I was like okay slay I'm now going Beyond just saying oh this is odd whatever we're now getting to a point where we can now start detecting systems on the network that have been compromised or infected before the ab signature has even been
released and you know it makes sense because we're looking at what's going on in the system we're not depending on this on this whole concept of you know a signature signatures will always be a little bit behind because malware has to be detected it has to be submitted it has to be studied the signature has to be written the signature has to be QA then it has to be released to the public you have to download it you have to QA it again before you deploy it to your environment or have every server not act right use Cathy products on right so you test it then you deploy it to your entire infrastructure but then what do
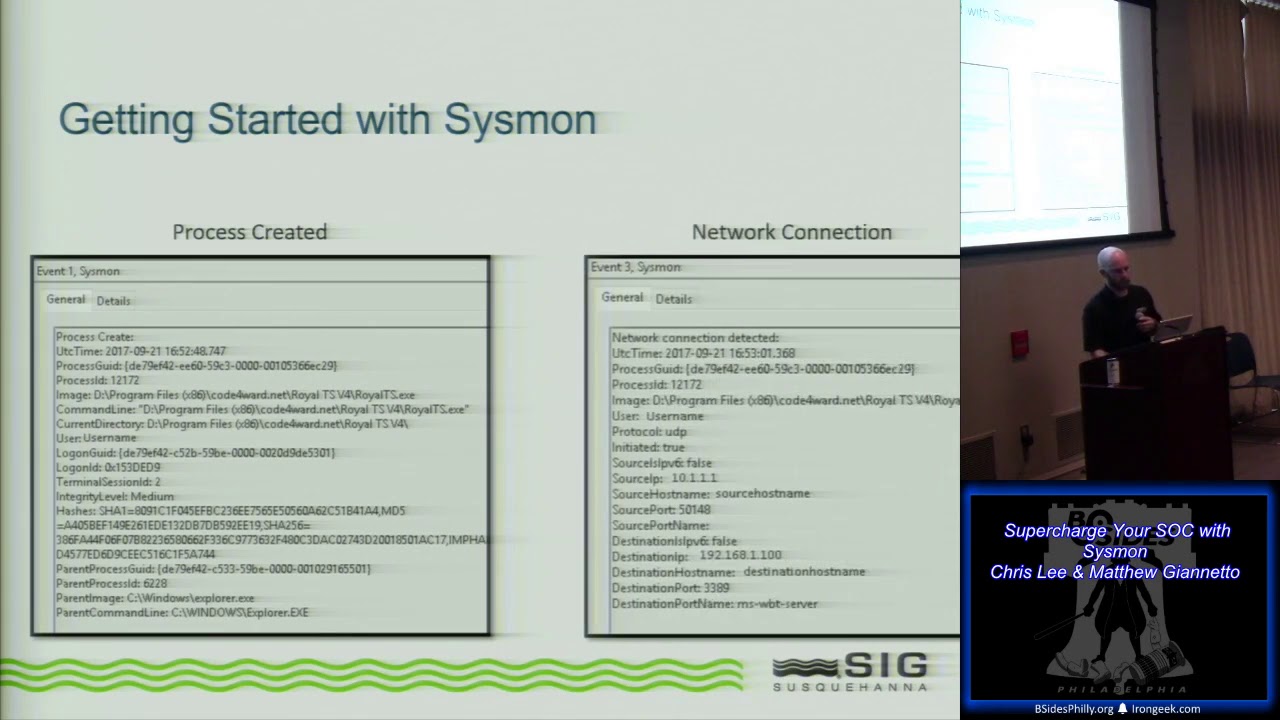
you have to do either catch it on an on an access scan or wait till Sunday when the system doesn't pull system SC by that point you're now talking about 15 20 maybe 30 days and some malware will never be detected so you're already behind the power curve before you even started so if you are based off the signature only type you know activity you're always going to be behind you can't become proactive you start in and reacting to things that are you know without signatures so because I like the pictures okay I had to diagram it and this is actually uh there's time stamps on the connection lines and what you are uh what I'm actually able to do is I can
see like say the ActiveX loader then you know mware later things like that so man sorry gross dve water before came up so um this is worked in real life besides just the diagram have I detected malware you know on a system have we been able to react to it have we been able to actually know do some good uh this is a cutout one of our forensics investigations the system was indeed popped it was owned we did full forensics on it and one of the things that we found was they had used a renam dll right Ms g.d is the normal one this was MSG D.A um the reason it's in here you look
at semantic the line for semantic and you look for maffy none of them detected it during the time so again if you're dealing with a signature based AB you're going to be behind the power C this was only detectable because of us being proactive um this was another one these were more of the files here they Rel label jpegs because you're looking for executables and you're not hung up say on a file type you're really looking at anything being either accessed or running out of temp doesn't matter if you see a JPEG you know of course you're going to why is a JPEG being labeled as an executable in this case the malware was calling these jpegs and using them
for execution and you can see only one of them was even picked up it was picked up by semantic and even then he didn't know what the heck it was it just kind of was like yeah whatever okay and uh again like I said you know all the rest of the mods w't picked up at all we found all these we were able to study them look at what they did and my favorite was the jpeg it's actually a keyer with mpm div so it really wasn't a JPEG it was exec so obviously bad news there and if we had waited for again like I said waited for ab to find it' still be waiting so also um so moving on you know
we covered the SC we talked about you know exploit we see the traffic on the systems um and actually I was going I was going to say last night I was talking to someone and I realized we have a great way of explaining a lot of how these detections how the monitoring and watching these systems work and that's you pop a box it's like you punch someone in the face every time you punch someone in the face it leaves a part essentially what we want to do is f you pop a box there's there's going to be a mark somewhere I don't care how weak you are because you have to change something on the box so it's looking for that
change like I said something access out of the temp out of whatever an illegal API called you know a buffer overflow all those things cause errors on a system you're researching a buffer Overflow what are the first things they tell you blue screen your box because that's the idea want to crash it so that you then know what you have as far as room to play with so yeah good punch the face leave a mar that's what I'm looking for on these systems is the mar now you have to try to catch that early because once theyve established the foot then it becomes much harder because they're no longer using ver tools against you or
exploiting something right now you have to start tracking your own tools right I said before about networks you get po they not going to use some custom endat Cat super duper BNC fire Microsoft's RP and just start extending with regular traffic once that happens there's still ways to pick it out there's still things you can do and visualization and having logs will come back and really help you in this realistically should anyone see okay maybe you have really proactive with those agents but I don't I do not see RDP connections at 3 a.m. from them fixing boxes doesn't happen but if I see RDP at 3:00 a.m. going into very you know select systems especially systems
that recently triggered any kind of security alert big red FL hey this is an issue you need to look at it so um obviously you know your hips heads and sequencing those laws are really going to help and then being able to draw the pictures to show so as a case of point this is kind of a busy slide and this is not just for one area what this actually was is this was a actual um uh problem we had on our Network it was the systems got you know there was a few different actal areas to it it was an AP of we had malicious emails from the email was a PDF attachment that was
then ran compromised the box that box was get used to harvest credentials and then as a pivot to attack other boxes on our Network now it gets hard to follow when you're trying to timeline stuff but because of having logs because of using U multigo to draw the pictures and all of that it makes it really easy to follow um this for me I know for the rest of you guys you're like the hell I'm so um up near the top what you can actually is our people that were emailed obviously the names have been Chang change to protect the Dum um they executed something out of the email L but this's PDM um and from there you can
see the actual the PDF attachment reached out compromised certain IPS at that point one of the system administrators remoted into one of the infected machines which was used had a key logger installed once he logged in they harvested his credentials and they then proceeded to act as him so um this was the actual account here that they were able to harvest it when he remoted back to here and then they then used his account to leverage out and uh attack the rest of the machines so being able to do this like I said it's not super super clear but it's really easy to show an executive or show someone this is the picture of what happened to you you know
like how you have kind of taken over the barrel yeah these are your people who open the PD app this was the payload for the PDF this is what happened in the systems and this was the compromise and I do that because again information has to be actionable you need to be able to do something with what you see for the longest time a lot of what we go on in the network was reviewed by only a certain you know group of people your firewall people would only look at firewall alerts your IDs IPS team would just look at IDs IPS events how many times has there been a phone call where someone says oh the the world's ending the sky is
falling there's you know I exploits okay we only have Apache web servers I'm not a fear what what's going on and it happens some really good companies too uh Bruce schne had counter pain and I can remember being run very drunk and getting called like oh you have to head into work I'm like you understand that's not that's not an option why would you have back orice raging on your network wait back orice on my network yeah you're riddled with it really back orifice for 95 is all over my 2012 Network maybe it's Cisco VPN they use the same UDP traffic and that's what it was and I'm like okay listen if you ever wake me up at 2 a.m.
again for something as stupid as this I'm going to curve stop your face just to let you know I'm going to pop your box punch you in the face and leave a mark so and then uh the other one that of course um I did want to hit a little bit data extration uh data extration can be kind of tricky right what's the common stuff hey we'll bury it in a stream we'll do whatever again uh log files and log file visualization helps immensely um had a system I was fairly confident you know Zone I was worried about data xill I said man what if this guy's like stealing stuff what if what if you just not seeing it so I went
ahead went back to the logs pulled all the IDS IPS network based IDs IPS firewalls and used bro IDs um read through a bunch of stuff visualized it bam what stands out immediately this guy was a massive tour user and when we actually went back started looking there was some of our data in that tour he was using tour to xill data so you know again being able to visualize you know what you have on hand helps quite a bit on that um covering tracks this uh this is a hard one and you actually if you're doing all of the stuff from before fairly well you'll detect this because you won't have anything which I know sounds pretty dumb
but if they delete all their logs it's what happens to your log log analysis frameware method of doing business there's no F and logs to look at and so uh that's actually the detection for this so I would be like yeah you can graph it but that would just be this slide of white so how it works so deleting logs hiding logs your tunnels when you start when you have such a when you have a framework that's so focused around logs the lack of logs is actually like say that's what's going to ke you up now I realized that I kind of gone through you know actually gone through fairly quick there was some points that I wanted to
cover I realized I missed one uh the DNS poisoning would have been uh back a few with the U Network portion I do a lot of DNS poisoning and I highly recommend that DNS poisoning gets added to your repertoire of tools you're already looking for network based you know detections you're looking for the signatures that are coming across the wire you're looking for possible host compromises however what do most people do when they find a bad domain they may poison the DNS right now how many times have you seen the DNS gets poisoned to be 1271 right I feel you lose a lot of data to do that um you don't see the three-way handshake you don't see the
URL that was requested you don't see the ports necessarily you just know that when this malware tries to execute you tell it that it's command and control channel is Local Host you get nothing so one of the things that I have added and it's one of the few things where I'm like okay let's get an additional tool you can't really do it with what you have on your network is uh an actual web server that doesn't matter what you ask of it it gives you a status code to you say hey I want like the hot firefighter you know swimsuit calendar it says 200 like you didn't give me anything 200 no seriously I want like a recipe for like
Bas 200 give me a kitty 200 all right I do that on purpose uh the idea is that when a system does get compromised malware reaches out you at least get more info like I said if you may not know that there's a JPEG that gets downloaded and there's info in it that then gets added to this to this that causes it to know which bot that you know controller to reach out to but when you start intercepting all of those calls and then reverting them to your log files you can actually add just that one more layer AC one more later you see um but one word of warning if you do take a system that responds to 200 to
everything um let your vulnerability scanning team know because your vulnerability scanner will cry and the person who reviews the report will be like oh my God there is a system on our Network and it's vulnerable to everything wait what do you mean it's vulnerable to everything like what about this no it's vulnerable to everything um yeah I kind of forgot to tell the U the scan team and it was a Monday by Wednesday they finally called me and they're like look this thing is so jacked up you're the only person who possibly be at you know to blame for this and I was like oh I forgot what I did with that oh cool thanks you know
they're like no no no this wasn't like a request of oh hey by the way we found the server it was the damn thing off the network I explains what it was um what we do though is f the logs from that server get added to the Sim and so we get that so again it's that one more layer of now we have a network-based you know signature coming in we know this system was targeted with something then we have the host ID the AV alerts and the monitoring and we see oh Not only was it targeted by something that's something executed and did XYZ on the system and then we have corresponding Network traffic for going out now we
have a full picture of a system that's been compromised or possibly now you don't have these vague threats going to a system you have no idea if even happened at all or not just Pi on network people you don't have a system that's suddenly randomly starts issuing alerts and you never know like well nobody talks to this thing it just sits on this network and does XYZ well you won't get that network data unless it's being a system and most people aren't storing that level of Ls so the only way to find and to do that is to correlate all of your logs to all your different sources sequence them timeline them and then from there like I
said AB becomes a non issue who cares you don't even have to really refer to your ab because you can just say this attack targeted these 30 Machines of those 30 machines 15 exhibited the following behavior and of those 15 these 15 had outgoing connections you now like I said you know everything about that machine maybe finally 3 weeks later fires yeah thanks thanks for the heads up I already knew so and then for the last one because this is um something that I put together your mileage may vary of Effectiveness um it works for me might not work for you so I thought this sumed it up pretty nicely um you know using this kind of system trying to move
down the log analysis trying to uh implement this in your network go one or two ways so like I said the mileage been vary U I've had pretty good luck with it um hopefully you know like I said take some of those system folders think of ways you can monitor them uh on the network uh look at your sim solution see if you can't sequence those logs A Better Way um monitor for a few different things may not have thought of to Monitor and like I said the big thing is just mashing those things together trying to trying to get some good data out of there um and then of course you know there's people out there are hell
of a lot smarter than me doing this stuff um actually I see them in the I see them in the crowd um Mike's going to be talking about some stuff tomorrow uh it's actually extremely Eerie the um similarities um like you said my system is I really try to say hey look stop buying all this garbage don't buy fourth quadrant don't buy Mag quad it doesn't matter if you don't leverage it it's doing nothing for you you're going to buy someone a new boat you're going to put someone's kids in college that's fine and fantastic but leverage the stuff you have you're generating logs review those logs throw a simple visualization out of it bam You're Gold so that's it that's
it for
me questions comments you Su that any of those are all oh do I have to be circumcised to use this tool no nice um like some of the guys um like there have seen this before um I've done bits and pieces of it um I like to try to get usually a little bit more animated try and really H to stay so it has you know it's affected it a little bit um come on real question testing with this yes something about how you have billions of lines of logs coming in what do you use to process that visualization I didn't throw it in here um well I'm sorry I could I I started talking before you you said the
visual I was looking at the visualizations nice cute little visualizations you those billions L I love my visualizations all right let's see if I can do this CU last time so it's not ready for like prime time um I would like it to have been um I sat down and what I did cuz you're you're exactly right now I'm not going to show my desktop until I get to the cool spot because I want you to see like all my like total stuff that I do stuff like that all the inapo stuff actually you know how they say you can tell a lot by a guy by his toolbar currently I'm very dull because the only
thing on my system is like core impact and U whatever and that's not like saying oh hey um everyone go out and ride core impact I'm just saying like I'm one of the lucky people got a key for my organization otherwise the very all right so he's nothing much to you this is my working folders uh that I walk out of um so most of my log files just like that hey look at that you all know my last name now in case R6 wasn't enough um so this is what the Elin is you can see moderate sizes some can get pretty big but obviously it's kind of hard to work with that so what I
actually do is I use a I've got a couple of um python uh that I I don't want to say scripts but then again if I say that they're actual programs someone who does c will walk up and like punch this apparently I'm very nervous about face punching I don't know what it is so um what I did was again I told you that it has to be U pretty actionable I've got one script that will go through it goes ahead and strips all of those uh zip files it opens them up and then pulls out the files runs uh through cleans them and then splits them into these uh csbs so what these are for me is I take all
of the sequencing down all those like Millions thousands whatever um I split them into all the events per machine so if you've got 20,000 machines on your network if 20,000 machines fired off an alert then they'll end up as one of these sub csbs the python script works pretty well but if I release it to the public current state I will be ridicule on Twitter non-stop because I'm like the worst python person ever um but I can I can parse over 10 gigs of it uh without memory errors due to a nice trick uh I love this community you tell someone you're having a problem and they're like oh I fixed that I just did XYZ and
you're like oh and I don't even know your real name so I don't even have to give you credit lock on um I had a guy who uh told me about re X read and that's how I um avoid the memory issue where so it won't blow up on me I use XP lines uh it'll parse through everything just fine um and so like I said I just I take all those all those log files I've got them uh in a moderate order that I can depend on you know the columns and what I do is just go ahead and I split them and um I take all of the system names throw them into a set I
mean Python's fantastic for that I take all of the network detection all the signatures that were fired throw those into a set take all the user accounts throw them into another set reason I do sets there's no sorting involved sets only hold unique values so originally I used to try to sort the values and grab unique and do all this stuff and my script would take like nine hours to run I was like wait that's stupid why don't I just throw them all to a set and let you know alut take its scores so um I throw everything into a set and then I just enumerate to the set I create one CSV uh for every machine CSV for every
user and one CSV for every Network signature and then I just read through and I just parse the heck out of it because you only have about about 100 Network signatures that are unique I can then uh query the 10 gig log file for just those U threat signatures I write them out but then I found that if you search the same way with machines it'll take you eight hours to run so instead after that point what I do is I take the reopen the log file and then I then take the line and I split that line to the corresponding machine CSV and user CSV and then once it's done I'll open the threat csvs I'll see a gear snip uh
ActiveX loader whatever I'll grab the ActiveX loader I throw it up and just take a quick peek at it maybe throw it into maltego and once I know all the machines that fire for say ActiveX I'll go back into that pull out the machine's csb and see everything that machine has to trigger for the last like say 30 60 or 90 days I'll see all of its i i virus scan info uh ActiveX loader info all those different things I go ahead look at the total machine and that's what I'll throw into Malo and uh sometimes you got to here it down a lot of those mteos are really actually just cuts what I do is I throw everything into Migo go
to the event or sorry the um the third tab uh blows my mind at the second um the n list and then I'll pull out say A system that I'm pretty confident is been compromised right click export it to a new map with all of its child you know dependencies maybe three or four down let mul for you I like if Mulo can Harvest Facebook tie-ins for CEOs it can totally visualize blog plot and I don't even think the tur knows I'm doing it they probably just think I'm like some random person who bought a maltego server because I'm like really like altigo no actually I have a multigo server to eat my vog files because it
doesn't matter than say I love spunk but it doesn't visualize it it shows me patterns it shows me how many beaconing events happen but it doesn't draw the pictur I like the pictures most you very easily entertained so that's about that was uh pretty much everything I had said um I should have hid multigo how I par the laws I really wish I can change I I I'll share my script with you there's no secret sauce to it you just can't blast me on Twitter for being the worst python script youve ever SE okay that's my only C anyone else quick question all right cool I'll step down turn this over to someone else sure next
I'm sure tell so um if you do have any followup or you're just curious in general Twitter I'm a renegade 0x6 um just you know whatever have like 56 followers so if I some be 57 I'll know it's one of you guys