Security can do better: Think Security Architecture
Show transcript [en]
i'm jason maynard i'm a secure or senior technical solutions architect um i actually work at cisco uh focused on cyber security so live and breathe uh security uh every day um this session i've done this at b-sides edmonton a few years ago it's a little bit of a combination of of um some of the things that are happening today as well as taking a step back and looking at security a little bit differently and more specifically around an architectural approach to security and so this is a method that that you can use it's a hundred percent product agnostic has nothing to do with product is all about capabilities um and so we'll get started okay so we'll talk a little bit real
quick about who can benefit from the session uh we'll talk about industry challenges we'll talk about the point product approach and then we'll do a security as an architectural approach we'll do a kind of a walkthrough and kind of some of the outputs that you probably like to get doing this session but it's really about taking a step back also i'm not on video because i'm on a satellite uplink and uh so there's about a thousand millisecond latency and i thought you know seeing some of the other videos um today they're a little bit choppy and i thought it'd be best to have that off all right so who can benefit um it could be anybody
right on uh that has a that dabbles in security it could be on the red team it could be on the blue team it could be a combination of these teams right um and you may have seen this before but this just talks about you know the red team's more the attacker side right you got the blue team that defends there's a yellow team or a sub team that's kind of created called uh the the build team so building the infrastructure and then there's these sub teams it doesn't really matter that the the team that you're on i think this is a valuable exercise for all teams so if you have a security hat even if it's not a core competency you
certainly should be in these discussions also even if you're on help desk and don't have a security role or you're an application developer or in compliance risk you should certainly think about um including these people because they're going to provide tremendous value during this these sessions so the image here i stole off of the i found it on calgary youtube channel um and so uh you know give credit to whoever created it but uh that that's where the image came from [Music] so what are some of the challenges right um and i kind of break them out here and there's so many everybody that's on the defense side knows about it and if you've been on the
the the adversarial side like from a red teamer perspective um you certainly know there's a tremendous opportunity out there right and so we got things like fishing right malware forensics right you got system hygiene you've got um you know direct internet connectivity right work from home the challenges with work from home now right and i heard some sessions earlier everyone rushed to get work from home up and running and i think security took a back seat and now we're starting to see people circle back you've got social engineering you've got dns outages you've got split tunneling credential theft the adversary is well funded you got water holding attacks sextortion right the the adversarial side now is
more profitable um than the drug trade right so the point being here is is that we're up against a tremendous adversary right that's well funded um and has very very strong skill sets so if cyber crime was a country it would have the 13th largest gdp just to put it in perspective right and and really taking the approach to security that we have up to now is is not done us um the service that we we probably deserve right and a lot of times it's more reactionary and i'll talk a little bit about that you know 1.5 trillion in profit in 2018 again well-funded skill set shortages right internally all all you wonderful folks that are are
attending b-sides right are trying to change the the the the game but we need more and more and more people uh from every single background right um and uh i think canada's got 8 000 cyber security skill set shortages coming up in the next two years i've seen numbers of 350 000 open head count in the us uh 3.5 million globally right by 2021 or 2022. whether you buy into those numbers and what those roles might be i think it does tend to lean towards their there is a shortage period and there's more right and then you get complexity right and this is this is something that's interesting really around security or the security um space in general right because if you
look at other architectures they don't have the same levels of complexity and so you know for the most part as a defender you're going to have capabilities like this right and you're going to go to market and you have lots of vendors to choose from so much that you could actually make things up right and i've done this i've learned not to do this because i ended up calling somebody out but i was at a government uh organization and i talked about a a new uh endpoint capability and i called it cyber security ninja and i talked and described about it and then i asked the room of about 20 people if anybody heard about it
and somebody raised their hand i i made it up like unless maybe they knew something i didn't but i i made it up i was just going on about trying to prove the point that this market is very very saturated and so you've got these up and comers that have new features and and gets people excited um and they fizzle away or they get uh you know bought out by a larger organization there's just so many vendors and and the problem is is really pulling it all together making it work and there's much more right that's just an example of it right and rsa had hundreds and hundreds of vendors um attend we're not talking about
attendees we're talking about vendors and and to put it in perspective think about it right if i was asking anybody in the networking field to name 10 to 15 vendors they would struggle right same thing with systems storage right again in security i can make things up i can say whatever i want um and most most often you're gonna have to google it to see whether or not it's true right um and that just it exudes the the complexity that exists out there and so what i've always said is what are you doing different than everybody else right because the model that we've chosen this fragmented security approach um to security has been done by
every single person out there right like if you look at it if anything a lot of these organizations have bigger budgets not seeing file share oh sorry that was that was my message that's hilarious um anyways um lots of other organizations have already been there done that right they probably have larger budgets and they may have as good as skill sets as you but more of you right and the challenge is is that they've been down this path trying to make it work and it's failed and so what i always ask is what are you doing differently if you take the same recipe what is the end result it's probably going to be the same right
you got to start modifying the recipe right and so what are you doing to modify it and so we've done this point product approach um to security and so if we take a step back and we look at how we built our infrastructure we can see some of the problems right and so as an example again this is the walkthrough because i know there's many different skill sets here today um some people with advanced skill sets that building and architecting security infrastructure for a very very long time and there's people that are new to the field and so when you break it down you know we started out with a firewall blocking the internet right the big bad
internet and then we we've got a campus network and you might have a couple of vlans right magical stuff happening here right you've got host maybe with anti-virus as it starts to evolve we start looking at web content we start seeing some malicious activities so we add some web security uh capabilities more traditionally proxy focused at the time and then we might have added ips right we're feeling pretty confident but the adversary continues to mature their capabilities right as we start using ai and ml there's nothing stopping the adversary from doing the same right and so they continue to advance their capabilities we continue to build out more services the clients and customers and business partners all
want data data is you know the new oil or the new gold right everything's all about data and so they want more of it right um and they want to run mi or ai and ml against that right and maybe create services or optimizations that sets them apart from their competitors and so we might be exposing more services right we might have av as we move along might add ips maybe even a web application firewall right you might have other things right here as well you got a data center network you got vlans again servers av right you get the theme here and maybe you have a firewall i still don't see this in many organizations
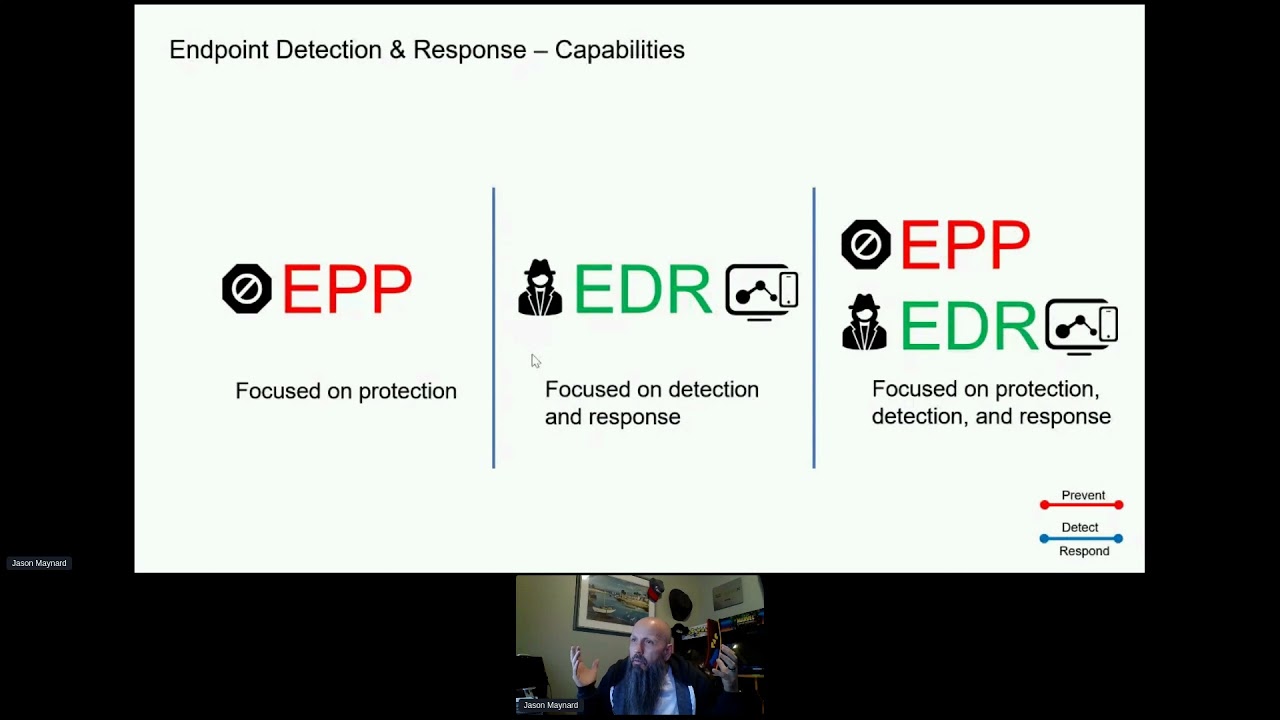
right is a firewall to block um or some type of advanced inspection mechanism from the campus to the data center a lot of times we're still seeing this open in a lot of organizations and so maybe you have a firewall you add ips maybe a web application firewall as well among other things and as time goes on you might add email security right lots of threats come in through the in the form of email we we get more advanced we get endpoint detection response we add dns layer protection now we're moving to the cloud right i forget who it was earlier talked about cloud security right all the components you've got to think about around cloud
security but that's exactly it you have to take a step back and not look at it going i need a casb because it's more than that right it might be an element of that but you have to think of the broader picture and so you might have a you might have added a cloud access security broker and a lot of these again are more tactical now i know we've gotten better to take a step back and think about the integrations of some of these technologies or using open uh protocols right um but they're still a challenge and i see it in a lot of organizations flow analysis right so understanding what the network looks like and
baselining the environment because all of these controls no matter who you go with whatever vendors you deploy are gonna fail right they're gonna fail there's nothing here that's gonna provide 100 percent security effectiveness period and so the challenge now becomes right how do i know what's happening in the network if these defenses fail so you know detection or prevention is key but detection and response are just as important and so we continue to build this out we get knack right we're advancing again and you know what the environment's getting more and more secure but as it's getting more and more secure our challenge now becomes the complexity that we've introduced right is managing this can i
ask a question and get an answer back right am i building data lakes to pull all that data in and so i can run some type of analytics engine on top of it right it becomes much much more complicated then you got macro and micro type segmentation in the campus environment you start looking at doing a little bit of this in the data center as well so we're certainly tightening up uh our posture but then what about decryption tls 1.3 right application segmentation you've got private cloud public cloud hybrid cloud right you've got database security you've got vulnerability scanning you've got mobility right you've got sim sandboxing and it goes on and on and on
and the problem with that is that's the the the easier part right trying to understand a little bit of the controls that you might need but now it's really trying to do something different with the recipe right is okay if i did take this approach and it's fragmented what about intelligent sharing right what about integration right does my endpoint tell my firewall about the threat that it just saw right does it tell my email security that it saw something right like these are things that we've got to think about these things have to work together as a system you've got systemic response and so what happens is is now it's time to renew right you've got a firewall it's up for
renewal i have an l3 l4 type control i've got a broken up ips i've got this content security that's all by itself what do we do we go to market we put in a next-gen firewall right the next-gen label that never expires right it's always fresh or is it right and so we may be adding next-gen firewall capabilities and we might be sacrificing some of those capabilities right because now it's a feature within the platform and it may not be a core competency of that platform here or there again we're adding these layers and we throw it in so now we've got a next-gen firewall and we simplified our infrastructure moving forward right and then it comes
iot right now all of a sudden new devices get added to the environment how do you profile them how do you posture them how do you secure them can you install an agent most likely you can't right and you can think of this of any environment right whether it's ot or it and then all of a sudden things start to break things become very challenging right a user comes in plugs into the network the entire segment gets taken down completely compromised how did it happen did it happen off premise did it happen on premise was it based uh did do i have all the forensic data i need do i have all the dns queries that were
made do i have all the flow analytics do i have all the logs right all of these are things that we've got to think about and so what we think is a better approach right we as defenders is is really taking a step back and truly understanding um the risk right of the flows so if we take us a step back and say wait a minute let me understand the business for a second and what we're driving towards right and this could be from a security lens perspective right you've taken the the core um executive drivers and you translated this a little bit better um in regards to uh security and so some of that might be simplification of
the security stock right improve threat intelligence ingestion and consumption right reduce time to detect right and ultimately time to respond right reduce the number of vendors while increasing integration right remember i i'm not saying that a widget from one company is better than another what i'm saying is there's too many products right and how can we be expert in all these different products and and be expected to make them all work and integrate and share data it's very very hard to do protect sas based application right we're moving some of these services to sas right especially during coven we've seen an uptick in that right people moved faster to cloud just because they can offer those services and use things like
native tls to secure that channel as opposed to forcing users back through a vpn or traditional vpn tunnel increase automated response or action uh to threats in progress so again this is reduce the time to respond maybe simplify the end point right for advanced threat both on and off premise right maybe we want to have integration as part of that right and whatever else that you might collect but it's important to understand what we're driving towards the next thing that we probably want to focus on is what is what are we what are we trying to protect against right what are the threats and risks to the business and so it could be simple things like
compromise of cust a customer data it could be credentials stolen and compromised lack of visibility on the network during an incident right um risk of compromised asset off premise right if i can't if especially with work from home and now we're split tunneling you know i've now opened myself up and there could be times when they're completely disconnected from the environment that they get compromised do i have the intelligence captured right if they do get compromised and plugged in to my network because now they're coming back into the office and maybe it moves laterally within the environment can i put in a control to mitigate my risk well i'm missing a piece of the puzzle
so i might figure out that this asset was compromised i clean it up but i don't realize that it's a domain that they're going through that pulled a pdf maybe right or you know it was an exploit kit server that they hit and compromise the vulnerability maybe i don't know that right that's the piece of information i'm missing and what's happening is even though i'm trying to put these controls to mitigate the risk they're constantly coming back in as compromised right because they haven't changed their behavior nor have you put a control to mitigate the original reason why they were compromised iot devices do not support agents i mentioned this earlier right you can't install an edr product on a light bulb
just can't do it but it might need network connectivity right or a ups or a printer right all of these devices are added to the environment service impact due to breach right and whatever else right but get an idea of the executive drivers the threats and risks to the business and then we move into the next piece of this right and that is the architecture and unders sorry not the architecture understanding the existing technologies in place that makes up our architecture and so the the reason this is a valuable this is going to identify where you have gaps and where you uh may not have gaps or where you have a complementing control um and so
a vendor might be vendor a provides av and advanced malware protection vendor b might provide email security vendor c might provide knack right and whatever feature capability again we want to understand that and make sure the team understands the capabilities so when we go through the exercise of really tearing down that use case um we can fill in the holes right so that's kind of the the first steps right understanding the executive drivers the threats and risks to the business and then ultimately the existing investments that we have and so we'll look at a company and i choose acme um but the one thing i did not realize uh was products um from acme corporation are
often gener are often generic right so basic and failure prone or explosive i didn't know that right i always thought you know wiley coyote was an idiot and didn't know how to operate um the products that he was purchasing i did not know he was the ceo of acme but anyways this is the company right and so they do stuff right and we've captured the executive drivers we've captured the threats and risks to the business we know what technologies they have in place and now what we want to do is take a step back and say here's a as an example an internal it user needs access to the internet what security elements are required to
secure the flow right contractor maybe has access to a data center service or maybe an operational technology right what security elements are required to secure that flow and you get the idea here right a light bulb a light bulb needs access to a building management system what's the security elements that are required to secure that flow and so taking a step back and going through this is actually going to highlight more of a storyboard approach to security than i need a firewall i need email security it's going to fill in the gaps it's going to highlight the gaps and it's a better conversation that you'll have with your executive teams right is this is why we need this this
is how we went through um evaluating where our concerns are and you shouldn't think about this as budget you shouldn't think about this of complexity about deploying multiple different technologies per potentially you don't look at that remove all of those barriers and go in and say i am a security engineer or i am somebody from the application team or whatever it might be i'm an auditor what things would i need in order to feel comfortable that we've got enough controls in place to mitigate the risks and so these are what we call places in the network so we define them right remote access data center campus etc and what we have here is an admin
on-premise user that's accessing the internet okay and usually this is a very interactive whiteboard type session that you would have and here's the capabilities map right so green means i've got a capability orange means i've got partially addressed or i purchased but not deployed so it's on the shelf right we haven't had time but at least we own it um and then i'll ultimately you know the red axes capability not addressed right so we've we've identified a a significant gap orange is still a gap but potentially a path forward is it might be easier right because you don't have to acquire maybe a technology all right so let's zoom in a little bit here right
so we've got this flow and this is kind of how it looks right and so i've obviously walked through adding some components right that are very common in most environments so endpoint antivirus yep firewall application control next gen ips yeah that's what i have url filtering right maybe i've got active va scanning don't see enough of this um but certainly maybe this organization has it right sim uh maybe in place so this is this was captured from the existing technologies right so we already know that there's certain components here that we work we we already have so we can fill that in but now this is where the conversation gets explored from a different lens so what
we want to do is look at this from an auditor perspective or maybe an adversarial perspective right um and now we want to challenge that now i know most people are probably sitting at the edge of their their seat going well i'd have more than that well i hope you do um but let's assume that this particular flow and what you'll find is some flows will have more controls or capabilities than others let's assume this is what you have so this is what we want to do next right we want to start asking questions right should i be able to connect any asset and get access to the wired network right and most people are going to say
probably not okay so i need identity ah and and some type of authorization mechanism do i need to understand the type and state of the asset so when i connect to the asset is it fit to connect to my organization all right i need device profiling and posture see there's no there's no technology here right there's no vendor here these are strictly capabilities do i need dynamic control based on context of an asset so if the asset um says that it has been uh maybe compromised over uh once it's been authenticated do i want to be able to change the the original disposition of that asset moving into a quarantine or a forensic vlan um
or when they connect and they unplug and another device gets plugged in can i dynamically configure the port with the right access control right things like that and maybe yeah i need that so let's software defined access segmentation dynamic control what about dns security now remember this is an on-premise user going to the internet the flow for an off-premise user going to the internet may be a little bit different you may not have all the same freedoms in regards to the capabilities that you would have on premise now the industry's changing um and shifting to provide those capabilities in the cloud but there's still an immaturity in that market right so you add uh some type of recursion
right with dns layer security do i need flow analytics right is it important for me to be able to harvest network data and be able to store it uh maybe run some uh algorithms against that data understand what normal looks like if the if and again this is about the group agreeing that yes we would need that and so we add flow analytics what about network based malware right so you get the idea here right challenge the flow right make sure that you're asking the questions the teams ask some questions and having a room full of people is certainly going to push the limits right everyone's going to have something to offer um and and make people ponder and think
right right you're right maybe we do need that what about endpoint detection response right what about passive vulnerability scanning right maybe you don't have active va right maybe maybe having both or having the va scan also provide context to other security platforms these are things that we'll probably want to think about right what about tls inspection right that's key right i think i've seen numbers 80 to 90 depending on who you read uh the internet is is encrypted right so are we blind now what are we going to be able to do to to get past that and then finally what we're going to do is wrap this all up right now we've we know the greens and the oranges maybe
because we have them and maybe we don't have them fully deployed for this particular flow but now we've identified we've got multiple vendors three that's pretty good actually right and we've got 15 gaps right in this case maybe not so good right the gaps and and now we've got an idea and and almost a recipe on how to move forward and this is going to be a journey right but we've got to think about what technologies or capabilities are going to satisfy satisfy these gaps again we're not talking about vendors here now we look at this we got endpoint security we've got dns security maybe matt can do these functions right maybe next gen firewall can do all of this
right we've got some network behavioral analytics we've got active va scanning we've got sim now we've got a plan forward but the thing you don't want to lose sight of is how do these technologies work together right um and this is kind of where architecture starts to come in or platform or fabric whatever you want to call it i might need my endpoint security to update next so nat can maybe take action once the assets connected to the network passes the authorization or authentication authorization uh step but then later gets compromised right through whatever means maybe this technology failed but gets compromised but i have an indicator of compromise that lets my knack know about it right
you get the idea same thing with endpoint in your firewall is there some integration here can i move the defensive capability farther away from the asset that i'm protecting ultimately as defenders you don't want to protect at the end point now don't say but what are you talking about don't don't be too quick to to judge me here what i'm saying is you need the controls here there's no doubt about it because these these defensive capabilities will fail but this is not where you want to defend you the defending at the end point means you have to be 100 correct or you're compromised right there's no way around it the goal as a defender is to push the prevention
capability or defensive capability as far away from the asset you're protecting so maybe it's in dns maybe it's at the perimeter maybe it's right in email right but i don't want it to be done on the endpoint the only reason why i have prevention capabilities on the end point is in case those other mechanisms fail and so again you get the idea think about the integrations and how this all comes together right especially if you're starting a refresh and you're looking at firewalls you might want to look at how does the rest of the other stuff fit right and how does it come together so how do i share intelligence how supported is the integration
how much do i have to do out of out of my team versus natively supported do i get systemic response right how much complexity did i introduce so again there's probably a couple other things you can think of that you could add to this but that's the thing you want to challenge this right another option and this is what i did recently around work from home and the focus at the uh the other b-sides event that i presented at was really around looking at work from home and so there's three kind of core elements there's one that's um uh vpn based one sas base and one one might be direct to internet as an example
and i took a different approach here at where i made sure that the detection and response capabilities were just as important or called out not just the defensive capability but also the detection and response capability and so i'm going to move a little bit faster here um just because i think everyone gets an idea of kind of taking that step back but this is a work from home user going to connect to the internet right and so you've got things like patching right how do i patch that work from home user that's interesting because you didn't think that that was too much of a challenge right but now it might be right um how much sass based services
are they using are they even vpn in right can my patching technology get back to the end point to patch it right am i using native tls and internet connectivity to manage that device you got exploit prevention system process protection or you got advanced malware right av right malicious activity protection things like what if an activity starts that's encrypting the drive right and all the files on the drive can i mitigate that based on the behavior right or the activity you know application blocking you got network blocking usb blocking you get ips firewall fileless malware you've got you know the buzz terms ai or ml right but algorithms that can help make sense of of what's happening um and get better
efficacy levels for more advanced threats and so that's kind of a prevention look at it right and again these controls may exist on the endpoint they may actually be extended out somewhere in the cloud they might also be something backhauled and in in in the uh on-premise environment but you gotta think about them right and now we've got detect and response so you got edr right lots of talk around xdr now right because the endpoint is only is our edr is only as good as the endpoint it's installed on right it's not going to help my light bulb but any of the network devices that are communicating right the the camera that starts doing a port scan
right edr's not going to help me there at all so xdr is probably a more broader approach to it but yeah forensic snapshot how do i take a snapshot of the endpoint if it's off premise and not connected to the vpn right host isolation what if it is popped right and compromised can i isolate it right um cloud-based iocs you've got command line capture you've got sandboxing you've got vulnerability software ipfix uh so this is flow correlation you might think well wait a minute i've got edr don't i get you know network-based connectivity based on the process that i invoke the behavior well you might but usually it's limited to a subset of number of connections
might be you know 10 or whatever where ipfix if you can get ipfix flow data that's every process with every network connection it's all logged right there's nothing missed here again think about on-premise versus off-premise right in this case the flow is really specific to the off-premise user connecting to our vpn and then you got dns security you got web proxy you've got dlp you've got tls decryption right av and advanced malware and you might be saying wait a minute i thought we've got something on the endpoint so it's in clear text so why do i need tls decryption well you're right but you're defending here which is much too late so ultimately you want to push these
capabilities to far away from the asset that means this flow if it's an https connection is encrypted in order for me to be able to detect it i've got to tear it apart right advanced malware protection again i need the capability here but if i can stop it here i should right now think about the forensic side of it right the detect and response can i capture all dns requests centrally located use it for forensics what about full uri capture right not just the domain now i want the full uri sandbox and file analysis so the reason why i put sandboxing here is more of a detect or respond is because if this is an http stream as
an example it's very difficult for you to be able to to sandbox a file in this enough time and get a disposition back without breaking you know the time delivers within an http uh connection right so it'll timeout that that it'll end up timing out so it's more of a a detect response capability versus a prevent capability and then as we extend it out again you've got ddos you've got tls decryption multi-factor authentication endpoint posture geocontrol and you get the idea here right continue to broaden this out you've got a bunch of defensive capabilities or preventive capabilities here but think about the forensic side the detect and response side right the the um data that's going to help
you as a threat hunter or incident responder understand what took place so device insight right denied authentications host profiling impact analysis right i wanted to do i want the technologies to tell me where i need to focus my time think about sandboxing again right and now this is more that this might be more of a web protection this might be more of a next-gen firewall capability right more of a network uh l3 l4 type control that seems to have to you know a file come in and now you're going to submit it analytics event packet capture event flow correlation right these are all things to think about and then you have a service on the
other end that's going to have a whole bunch of other security capabilities as well right and so that's pretty good right um we've got some capabilities here um we're securing our environment we probably want to run this through and you can see there's some differences here right here's an internet connectivity again accessing maybe us uh you know email uh the device this could almost look kind of like sas here and this is more sas based right again you can pull out this and put whatever service you want here um and now we've got a good idea but then you've got to come back and think about those questions again right what about integration what about
systemic response right how do i mitigate risk and so um you know systemically and so we've got this this kind of you know understanding of the gaps and what we need to do but now we've got to think about threat hunting and instant response you probably want something api based right and again turning every one of these technologies essentially into i don't know maybe data ponds right they're little pawns everywhere that have real-time data that's on them now right sure i might need to still send them to a sim or a data lake but maybe during hunting i want to go real time and hit the boxes that are seeing this happen right so api base would be certainly an
advantage to that and be able to query it then you get into orchestration automation right playbook type styles i give a phishing attempt happens execute a a forensic snapshot on the endpoint grab the observations within the email um maybe that's a sha-256 it's a link and query the rest of my technologies that i have and tell me real time whether or not they've seen anybody try to connect to any of these if they have now i want to create a teams room as an example i want to put in all the right people in the room automatically i want to create a servicenow ticket and um and maybe pause at that point because i need a human intervention
right that may want to approve or deny any additional steps but automate a portion if not all of that workflow right um because again we want to keep the job interesting to the people that are are there because i mentioned earlier there's a shortage a skill set shortage in the industry and that means you know anybody in security is gonna be very marketable and if they're in an organization where they're not adding value and they're they're they're chasing false positives there's a good chance that they're not gonna stay for long right so let's get rid of the noise let them focus on things that really add value to the business i heard earlier that security
is more around a cost center and it shouldn't be looked as that it's definitely something that should accelerate the business right people want to do business with organizations with strong security postures and we've got to change that mindset for people to start thinking about that right if i have a good security um architecture i should be able to go to market faster i shouldn't have to worry about that you're now building out this new services and i don't have capacity or capabilities right i should be able to to fully accommodate that and allow that service to go live securely sooner and then you've got threat intelligence right and what you want to do is go through all your major
flows and continue that process and again you end up with that storyboard in closing there's a couple of other outputs that you want you probably want to collect all your mitigation uh priorities or your gaps right now identify it so it could be network segmentation it could be firewall it could be you know um ddos it could be sim it could be whatever it is highlight it where you are in the world of uh licensed or partially deployed you move into maybe some type of matrix that visualizes the gaps um you can put the green ones in here um i most people i talk to don't care about the things that they've already been able to
satisfy they're more interested in focusing on the things that they need to address and this is an example right so you can see each one of these flows have a tremendous amount of red and orange and this is common in a lot of environments right um and so you might sit there and say wow that looks really bad yeah because it is right and visuals matter and then maybe specific recommendations and those recommendations might be um the priority of things right but the problem with this is you might have a priority to deploy as an example knack because there's a gap but the effort of that is significant right it's not trivial to deploy knack properly end to end because it
touches a lot of different things um in a very short period of time and so what you might want to do is reorder this a little bit right and um and and put it in an order that allow you to get the most out of existing investments as an example or ease of use of deployment right like for example um you have investments in a next-gen firewall and you're not using a capability maybe you're not decrypting payloads so you're blind to some of that maybe it's you know after you do you know your analysis around the performance of the box maybe you turn on tls decryption right or maybe there's dns uh capabilities that don't exist today
but you go to market and find that you know it's very trivial to deploy maybe a dns based security technology same thing with sim and anything else that that falls under the gaps that you might have uh have identified and that's it so um so anyways my my my thought here around is is real i think we need as as as an industry we need to really take a step back forget about the vendors forget about the products that exist forget about all the bells and whistles and really understand what we're trying to secure and take a step back and understand our environment what are the drivers what are the threats and risks and focus on those elements and figuring
out what capability we need then go to market right for the things that we need to you know you know fill in those gaps you know talk to the vendors at that point in time but before that it's good to have a true understanding of what you're trying to build towards and this might be a three to five year journey but it's a journey that you need to start at some point right and you know obviously work from home covered phase two whatever you want to call it is certainly a driver to maybe take that step especially for those flows alone [Music] and i'll look here to see if there's any questions let's see what is the typical
security flow for organization who has fully cloud-based infrastructure so that's a great point right so again depending on what it is that you're servicing it could be your web tier your app tier and your database tier right that you could look at the web tier to the app tier as a flow right because they communicate to each other the the act here to the database tier again that's a separate flow right you'll have different controls one of which could be database security right and then you also have your your customers or your your employees that need to access that web front end so that web from that user to that web front end is a different
flow right you'll have internal users might access those resources a little bit differently and then you also have things like customers that may access those resources and need certain levels of control or mitigate you need additional mitigating controls right because now you have you know somebody accessing a an application um for example that you don't have any control of the disposition of that that asset right it could be fully compromised um and so things like maybe uh you highlight the need for two-factor authentication right not just username and password but also two-factor authentication right as an example so a really round um yes around architecture and um certifications togaf is obviously one of them that
there's a lot out there um so i i don't know that i have a recommendations per se i've not done togaf so i couldn't recommend that uh per se but i know lots of people that have done it i i think there's there's value in doing that brody so i would just check it and do a little bit more research around it see michael there thanks michael arlene thank you i don't know if we have to the top of the hour if i'm over but
awesome so i will share the slides in pdf form uh to the b-sides group and um yeah thanks and have a great a great rest of uh your b-sides calgary um two-day event