The Fresh Smell of Ransom Coffee

Show original YouTube description
Show transcript [en]
but for now we have Martin fron who's going to give a talk on the fresh smell of rants and copies so can we please welcome Martin to the stage thank you welcome everybody to my talk this is the last talk of a day it has been a long day so I'm here to entertain you a bit and what could be more entertaining than a live demo that could possibly fail right so let's dive into the presentation so Who am I actually I work as a security researcher at security vendor Avast and to be honest this talk is not my area of expertise it's more like a personal story because I love coffee you probably seen this that's
exactly the moment when you want to cry right this is a run somewhere and it's a well-known and big strain or run somewhere called wanna cry and you you can easily spot what's wrong with your computer right because if you see this you are doomed but what about devices that doesn't have any screen or keyboard like IOT devices there is a running joke that the s in IOT stands for security and we will dive more into how bad the situation is right so as I said I'm a coffee addict I love coffee so let me ask you a question how many of you like coffee okay how many of you can't live without the coffee we are developers
right most of us IT persons okay so what do you think what happens when you deny a developer a decent cup of coffee this could happen right it could be it could be a crisis for the whole industry right what what about like developers without coffee that's gonna be disaster so that was the initial impulse because I'm like I can't live without the coffee so my idea was let's research on coffee makers particularly on smart coffee makers because these devices are connected to the Internet to our Wi-Fi networks and unfortunately it's quite easy to misuse them and I pick this one it's called small coffee maker and the smart functionality here is basically just to be able to control the coffee
maker using your mobile application so you have your coffee already in the kitchen before you get out of a bed that's as simple as it is it's a really simple device it has like four buttons small display nothing really fancy on a technical side it when you take the device out of a box it creates its own Wi-Fi network for setup which is called smarter coffee xx and these two X stand for the last byte of the MAC address so that's kind of a unique identification of the Wi-Fi for set up it listens on the porch TCP to old a1 that's the only port which is open and it uses a very simple binary protocol we don't know how Turing
authentication no authorization whatsoever so I was quite curious like what can you do even without like connecting the coffee maker into your own network because that's the purpose of this set up network right and it turned out that you can do anything it comes with the company application as a set for iOS for Android as well and it's pretty simple you can prepare your own formula for a coffee like the strength number of cups and you can brew the coffee from the application so that's as simple as as it looks like in terms of a protocol this protocol has been already documented on the Internet to do some extent and it's really really simple so
the whole protocol cons is basically a few bytes the first byte is a comment then followed by n bytes depending on the comment and then there is like a terminator which is 7 a hex always the response is very simple as well so the response basically starts with the response type then followed by and data and bytes of data again and a terminator so in case the response type is a just a neck or acknowledgment response the response type is always 3 so that's the whole protocol as I said it has been documented on the internet so you can find for example this comment which one sent to a coffee maker it brews you a
nice cup of coffee with the default settings of the coffee maker so just this 2 bytes to port 20 81 there is also one comment where specific moment which is like documented truth only some extent and this command is 6d what it does it turns the coffeemaker into an update mode and it looks like this so once you send this command the coffeemaker switches itself into a update mode and waits for another comments it turned out that all the documented comments didn't work in this mode and I was quite a puzzled what's like what's going on what's how how should I proceed to to get to know how the update process works so I try to use
the application because the application is able to update a firmware or the on the coffeemaker the problem with the application or with my coffeemaker was that the firmware was up-to-date so that that wasn't the way to go but something has changed when the coffee maker is an update mode it changes its Wi-Fi network into smarter coffee update xx again exact stands for last byte of the MAC address so I've tried everything the only open port again is 2081 I tried everything to connect the coffee makers and all the commands to fast the protocol nothing basically worked so how you should approach such a situation there are actually the easiest way is to get the firmware because by reverse engineering
the firmware you can get the three C's what's a description of the protocol and exactly how it works so how can you get the firmware there are again several options one pretty obvious google it that didn't work in this case there is no firmware for this coffee maker on the internet you can snip the traffic between the company application and the coffee maker that didn't work as well because the coffeemaker was up to date next option is to dismount the device and download the firmware directly from the CPU or from the chip that's kind of a tedious process and I would like to avoid that so the last option is to reverse the company application itself
and because it's Android and it's an MP apk it's pretty easy to do so and it turns out when you open the application itself it has two very interesting files in it in its assets it has like binary file kofi dirt bin and binary file cattle dog bin it's turned out that these are basically a firmware images for all two products that the company does which is so smart coffee maker and a smart kettle so when you open the file it's obviously obviously an unencrypted anybody knows what these strings are so our typical 8080 common so used for modems in this particular case it's a it's basically common strings or these are common strings for for esp8266 chip
which is the Wi-Fi modem which is probably or at this time I really don't know what what's inside which is probably inside the coffee maker I guess most of you know the esp8266 if you are tinkering with the IOT is the most common Wi-Fi modem okay so I the compiled the company and application which basically proved my point that the update process is same for both products and it only depends on a on a type of the device that's being read from from the device itself so it serves either the binary coffee that being or binary file capital or been depending on a type of a device so let's have a look into a binary file coffee road bin like if you
have a firmware image you need like the next step is probably to get to know what architecture is it intended for again you have several options you can you can guess you can use some auto detection features for example for either pro but for me because I like to dismount devices and eventually putting them together I dismounted a coffee maker that was the easiest option for me so this is the whole coffee maker basically this is the whole logic of the coffee maker you can see there the esp8266 chip which is the modem and after a while I basically identified like four main components on the board the one is as I said esp8266 then the
second the number two is basically ARM Cortex and 0 which turned out it's a brain of the whole coffee maker and it's kind of a funny because this chip has like 64 kilobytes of memory and comparing to es pH 266 it's way less powerful it's like 10 times or 12 times less powerful than number actual Wi-Fi modem but that's how it works there are also like four debug pins or debug headers with the ports used for programming and also for communication with the modem so you can basically using these pins you can tap into the communication between the modem and the main CPU ok so the next logical step is to get a data sheet
for a CPU that's how it works right and because I already knew what type of CPU is inside I was able to to load the file into either and started to decompiling or reverse-engineering the whole thing usually the easiest way how to reverse engineer some firmware is start with the strings because that gives you a pretty good clue what what these strings are used for and by referencing them to a code which uses them you can pretty fast get to main functions and it turned out this is probably the most complex and the main function of the whole coffeemaker it's a big switch and that switch is basically the whole handler for all the commands that the
coffeemaker is able to to run by proceeding further this is basically just like close up of this function so you can see there are like already known comments for example 6d and I'm not sure if this is the 6d comment which is basically the star of the update ok so let's fast forward a bit after 5 days I bet I was basically able to to reverse engineer the whole firmware and get all the main functions like it's easy because the firmware itself is like 49 kilobytes so it's pretty small it's really dumb device there is no no fancy OS nothing like this and I came up with this architecture or diagram of the coffee maker so you can
see it's pretty simple very few detectors basically wired into into the i/o pins of the CPU directly which is like missing carafe detector so when you when you take out the carafe the coffeemaker basically doesn't allow you to coffee then there is a grinder motor heating element hotbed like it's pretty simple control buttons the the only interesting part would be a coffee flap which is basically the flat between the grinder and the filter which opens at the moment when when the coffee is ground so I'm three what are a lot of sensors if you if you look at the base picture you can see there is no security measure in hardware so everything every security measure in this coffee maker is
in software so once you change the firmware once you patch the firmware you can potentially create a really dangerous machine which overheats which runs the grinder forever for example which basically runs the coffee forever right after a while after reversing the component application I was also able to identify the exact process of the update and it turned out it's very simple again no authorization no authentication no signature the only thing is the CRC at the end so it works basically like this so once you switch the coffeemaker in to update mode it changes the Wi-Fi network waits for a start of the update and then block-by-block each of size two five six bytes basically it uploads the new firmware
into a coffee maker following by CRC and the command which which signal to a coffee maker that that's the end of update so it's pretty simple so if you have the knowledge about how the coffeemaker works how the update process takes place the easiest and next logical step is to try to update the firmware right so this is the first attempt I made updating the firmware ok to be honest I've cheated in this case because I've only replaced the image which says that there is no carafe because there is no carafe but and it also turned out that there is no font in a coffee maker so everything you see it's an image so there is like there are
like 12 images 4 cups start medium beans everything is basically just the image so it's pretty easy easy to tinker with that ok so the next logical step is to create something more complex right so I've created a payroll because it turns out there is no space at the end of the firmware which is freely available and could be used so I replace the original handler for a join to Wi-Fi comment which is kind of you know like interesting so you you basically create a malicious payload that activates on a try of the user to join the coffeemaker into his or her Network ok so that's a time for a demo fingers crossed and I
will show you what I've created in five days
so if everything works you can see the display of the coffee maker here so that's my hand and let's upload the payload I know if you can see the terminal is it readable so I've made a little application for that because that's the tedious process okay I need so the first stage is to switch the coffee maker into a update mode which is basically by sending to these two bytes ok that was pretty quick so now the coffeemaker is in update mode but Wi-Fi changed and it right likes comment so the next logical step is to upload the payload and the modified firmware
and sometimes take a while depending on the Wi-Fi
okay so that that's exactly the case if something goes wrong there we go update completed it should restart automatically as you seen there is no interaction from the user needed so everything was just automatic Ottoman so now the coffeemaker is tears itself and it contains the malicious payload so the third stage which I have here as a setting on fire is basically to run the command or to send the command to a coffeemaker to join to a Wi-Fi and this is the outcome again thanks a while because it needs to change the Wi-Fi network again it needs to connect to the Wi-Fi okay
and this is how it works and if you if you wait a while it gets mad I think it's like 10 repetition of these two images so what what it's now doing is heating up the element but because there is no water you can't see it and now it runs the grinder and runs the Grider for forever basically so you can't use your coffeemaker anymore and so smells good so the only thing I can do is unplug the coffeemaker and the other thing is that you can even change the comment or overwrite or patch the comment that basically says update so in that case you break the device and unless someone like take it apart and replace the
firmware using the debug port or the programming port it won't work anymore okay so that went pretty smooth actually this is in case the demo won't work and I can like quickly show you oops that wasn't what I wanted to show you okay - that was too easy right come on show me okay let's fast-forward to the part which is here
let's hope it's going to work if I fast forward it has a nice steam effect when the water starts dripping through the coffeemaker without the car off so it's just to entertain you even more okay so this is just another case okay so let's discuss the attack vector how you can misuse this actually this device I don't know if you recognize that if if you have a kids and even the Lego Mindstorms that's a smart brick which basically powers the whole way go I was able to create this version of uploader into that brick so you can easily visit your neighbor who who has this coffee maker so obvious there are like few versions of attack vectors so the first one is
many in the middle attack because in the new firmware they actually edit a functionality that needs the user to press update I'm a coffee maker but if you think about it because there is no authorization authentication the open the Wi-Fi is basically opened it's pretty easy to do am an intimate man in the middle attack and to make the application belief that the coffeemaker really needs an update and in that case the user will happily press update the coffeemaker and also press the update on the coffee maker itself so that's one possibility obviously the proximity proximity attack so you can as I said you can be like passing by your neighbor or a company because this device is also or these
devices you can find these devices also in companies and that one which I want to show you is a social engineering attack that's my favorite one because it does any special equipment and then obviously you can for example sniff the SSID and the password for the network that the coffeemaker is being connected to and the social engineering attack is pretty simple just send the packet which starts the update on the coffeemaker and the prompt spells to a user that the coffeemaker needs an update and basically ask them to to either either confirm the update by pressing ok or pressing cancel but I've tried it on my wife and if you're sending the packet start update over and over it there is
basically no way how we can cancel because if you press the cancel it displays again the update so after some try or number of tries everybody gave up and press the update so that's the simplest social engineering attack you can do and it turned out also that probably users don't really need a smart coffee makers because if you go to Viggo which is you know like the database or or map of all Wi-Fi networks around the globe you can easily find like two thousand and five hundred coffee makers with the open Wi-Fi that has that have been never that never have been set up so yes the question is if we really need a smart coffee maker so to conclude my
talk the one problem with most IOT devices is so-called out of a box problem so we have a lot of IOT devices that just works when you when you basically take them out of a box and connect them and that's an issue because for example my personal experience from the apartment where where I moved to is that there was a Ethernet socket for Internet so I've connected my laptop and because I'm curious I was curious what's what's behind the walls I've connected to my default gateway and it's turned out that my default gateway asked me to set up the password for the first time and that's a problem that's a problem like these IOT devices like we
we've exchanged the convenience for security that's a really big issue so we should we should really make these devices you know parable until you properly setup them firmware is no longer firm but it I think this the statement is valid for for some time all right and the other thing is you need to build the security for the bottom up so if you are planning to create any IOT device you should start with the secure OTA update first because if you have a secure device on a user level which with the generated username and password for example and you have a vulnerable firmware update process you basically broke the whole security and the question at the end is would you really
trust any device today because this could be a great example of supply chain attack using IOT devices we've seen this today using a software using a repositories but the same thing could be achieved by IOT devices and the problem is bigger because nobody really knows what's inside the device ok so this talk is Memoriam of this device which I unintentionally bricked and shortly after this talk when I get my cup of coffee and some rest I will upload all the software you've seen and all the documentation for the coffee maker to this github repository so if you want to download it just in the QR code okay that's it I don't know if we have a time for any
bonus or Q&A we can take one or two questions yep do we have a mic right up high it looked like the other ASP pins we sold it in did they go anywhere sorry so the ESP chip that was soldered onto the motherboard it looked like that was being well more than just the serial pins were sold into something did they actually go anywhere on the traces or were they just yes basically from the esp8266 the pins that had been used were TX Eric so basically rs-232 communication pins and and the power that was that's basically it and you can you can even like there is a functionality inside the ARM Cortex and 0 which allows you to even update the
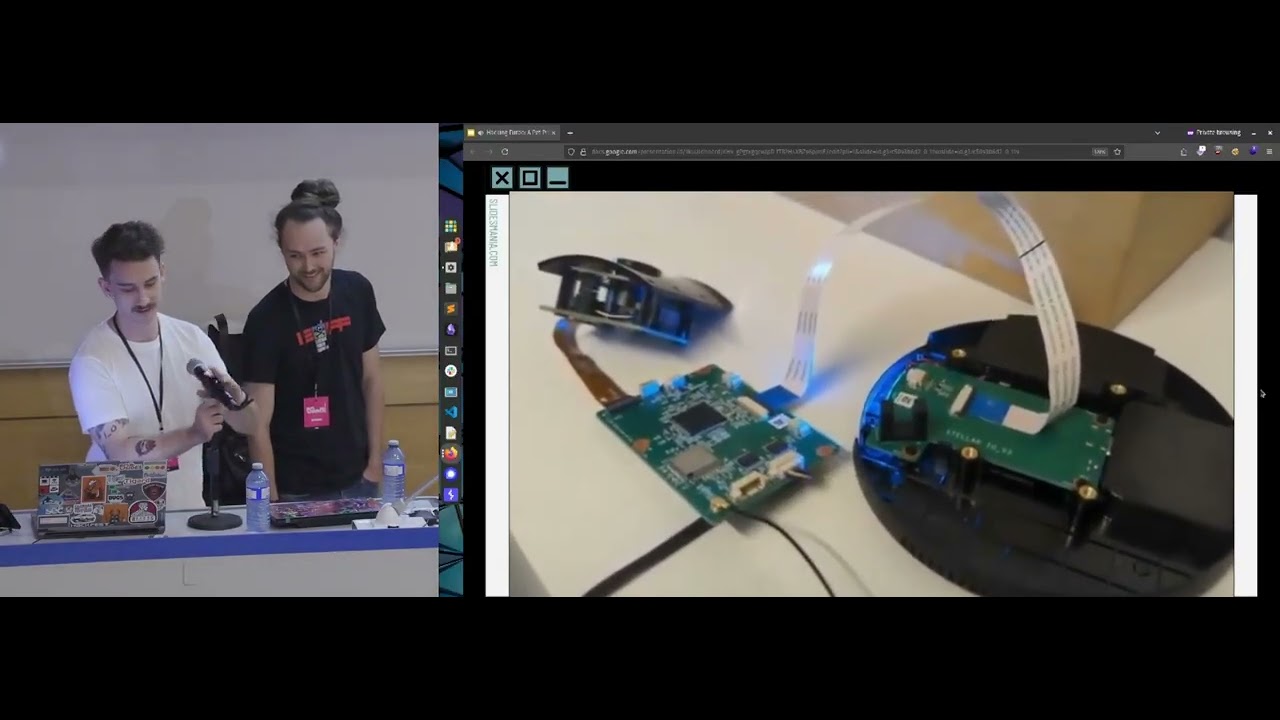
firmware on the esp8266 but it this goes like through the vendor update process like the vendor of the asph 266 and it's like known to be pretty secure in this case question over there as well have you been to own a coffee yet in Canberra is actually very good coffee I like it very much okay I need to get some coffee really and some sleep are there any other questions one behind the camera over there yeah actually I can show you a little bit of spoiler this is my upcoming project
hello yes yes perhaps one of the vendor responses to these convenience versus security thing is to now provide pseudo secure cloud services whereby your iot will connect to a vendor supported cloud surface and then you login to that by your phone up how do you see this is a compromise between security and control of the device as well as convenience for the operator user it always depends what protocol they use because that like in IOT world is the problem here is that many vendors are using like you know like obscure protocols it's like the security by obscurity you don't really know what's inside and they they are basically relying on the fact that if it's unknown and obscure
nobody will like dive into that because nobody understands that protocol and sometimes it it turns out that the protocol is basically a plaintext just you know put into a nice nice series of bytes so I think like the communication with with cloud is not kind of a proof that the setup is secure for example there are light bulbs that are connected to a cloud and the only identification that they are using when connecting through your Wi-Fi to to a cloud is their MAC address so there is no password no authorization the only thing the only ID they are using is is the MAC address and the whole protocol again is plain text and it's susceptible to a dos
attack because if you connect your script through the same cloud with the same identifier it disconnects the original device because it can handle only one connection so it I think there is no guaranteed and when the configuration is done through a cloud that it's secure it really depends on the Wonder and the implementation may be time for one more question will you have one well let's thank Martin for a great talk thank you