Tales from the Crypt: A History of Cryptography from Manual Systems to Modern Algorithms

Show transcript [en]
the b-sides DC 2016 videos are brought to you by clear jobs net and cybersex jobs.com tools for your next career move and antietam technologies focusing on advanced cyber detection analysis and mitigation that's probably the least interesting intro I've ever had does anybody else cold in here do you guys mind if I'm gonna put on a sweatshirt real quick if you guys can mute the mic maybe
[Music]
[Laughter] you can't get this from PFF I
was thinking I was gonna sweat having to wear this thing through the talk I'm actually glad I have it now so good afternoon my name is Jeff Mahin I hope you're not here to learn a whole lot today I don't feel like I'm gonna be teaching as much as just kind of sharing stories of my past if you're into history this is really more of a history lesson you might find some interest in it and certainly if you have questions feel free to shout them out or hopefully we'll have some time towards the end to discuss a little bit if you're interested that's what I used to look like about 20-25 years ago back when I was young
and more nimble my contact information there not working for any company right now I'm currently unaffiliated so if any of you are hiring feel free to approach me afterwards a little bit about me and how this talk came about I was I was I think it was at Abby's side's earlier this year and somebody was giving the talk on the history of crypto and I'm and I'm a ex crippie so I'm always interested in that so I went to the talk and as I'm sitting there listening I heard to me gee I could give this talk so that's how this talk came about I've been doing information security for over 30 years first third of that time approximately
was at NSA I did some work for the DoD as well before I went to the to NSA been out in the private sector for a little over 20 years and for better for worse for about half that time I got involved in PCI so you can love me or hate me but it wasn't my fault it was purgatory maybe but I'm out of it now if I look familiar if any of you guys watch Paul security weekly and sometimes a host on that so in fact I think I'll be heading up there this week I don't know who we're talking to yet but it's usually a good time i and i'm i'm one of
the honorary curmudgeons that gets to be on security weekly and I'm also a Jedi Master talk I've been giving a lot this year's been on the art of the Jedi mind-trick which is really about how to communicate you know we know a lot about security we know a lot about how networks and systems work and how to break them but we as a community don't always do a good job communicating that to others so as a consultant for 20 years I think I've learned some techniques so I did a conference earlier this year where I actually had a stormtrooper escort which was kind of cool which is the highlight of my speaking career and this two
sticks is probably the other side of that no offense guys so a really really brief history of cryptography codes and ciphers I am technically trained as what's called a manual crypt analyst paper systems some of these concepts should look familiar to you because they apply forward today to modern cryptography and and and really what we've come to know is cybersecurity the idea of you're trying to protect some sort of information some sort of data that you want to keep secret classically there's three different things that you three different goals for using cryptography its confidentiality integrity and availability using codes and ciphers is primarily the confidential things at least historically there's two classic types of crypto
systems a code and a cipher in modern times these days these terms are sort of used interchangeably but historically codes were a method of basically shortening a message maybe by using some sort of a symbol or some sort of a word that means a phrase or a sentence or something like that but generally speaking a code was some sort of method of shortening a message making it short and quick so that you could get the message through to the other person quicker more easily more simply less likelihood of losing it in translation or losing it in transit and and also keeping it secret ciphers are what we're more familiar with that's some sort of application of
cryptography encryption there's two types of ciphers transposition and substitution transposition means you're taking what's there and just scrambling it substitution is where you're applying some sort of different alphabet some sort of different set of characters usually that's where you start thinking of algorithms and keys what I used to do for a living the way you broke cryptography historically there's several different methods but the very first thing you would do typically is take whatever scrambled message you had and just start doing counts you know if it was scrambled letters just start counting the letters and see how many of them there are if they were symbols you try to look for symbols you'd also try to look for
patterns [Music] people much smarter than me over the years I have I have a few Show and Tell items you guys can come up afterwards and see these books military Crypt analytics part one and two they used to be classified they are no longer classified they have the official magic marker scratching out the confidential classification they really are Declassified these books are full of frequency analysis information everything you could possibly think of about how to break systems vol 1 is mostly manual vol 2 actually gets into machine cryptography a little bit feel free to come up and peruse these later after the top as time allows you find out what's there and you start looking for patterns you start looking
for telltale signs just a very simple example the in English as you're writing down angle language there are frequencies of letters certain letters are used more than others and this is a graph of the typical usage of the English language in the frequencies of letters in the English language you know for example the letter e is the most common letter used in the English language you can imagine letters like Q and K and J or use less frequently so when it comes to a transposition system again you're just taking what's there and scrambling it around and I know what movie that was from very good you passed the first quiz where as a substitution system is you're
taking the letters and most people have heard of a Caesar cipher of rotation of the alphabet against itself substituting the regular letters for a different letter using various methods of how do you determine what slide you're using and you can even scramble up there's lots of lots of applications of that but basically the the the Caesar cipher was something that was actually used in the Civil War and that's an actual Confederate cipher wheel or cipher disk they called it you've probably seen puzzles and you know those of you who are old enough to remember newspapers you know the funny pages used to have the little crypto puzzles and crypto quizzes and things like that these are
all simple substitution systems so if you're doing counsel the letters trying to figure out how many letters are there if you're looking for patterns you know like the one on the right you can see the the size of the word is preserved and and the separation of words is preserved well that's a big clue when you're a crypt analyst because there's only so many 1 letter words in the English language assuming that's the language that you're going after two letter words there's only so many of them you can start noticing different letter combinations and things like that but most importantly you need to realize that with a simple substitution while you're scrambling the letters you're
preserving the frequency range it's just in a different order so you know if if this was the statistical analysis of some Seifer that i was looking at and that's the the graph on the right you know I would start out by guessing gee it looks like the letter y is substituted for the letter e let me fill that in everywhere there's a Y let me write in E and let me see if that helps me detect any patterns of words and things like that where I can guess the next letter and so on and so forth and at some point you get enough letters you can start figuring out what alphabet or what slides been
used sometimes it's trial and error there's different methods to do it but that's essentially what cryptography was for many hundreds of years what takes it to the next level then is when you start introducing some sort of random stream of characters to add to your message primarily to try to disguise the characteristics that carried over and this is where we start talking about having a key involved the thing that I used to work with and you know in my early days of learning about cryptography and working in this field I learned and it's still true today the thing called the one-time pad is the most perfect crypto system around it cannot be broken statistically any type of analysis any
kind of frequency checks it's unbreakable as long as you're using this random stream of characters the key one time in one time only it absolutely falls apart if you think well it's it worked once ok I can use it again and again and again that actually creates cryptographic vulnerabilities where it can be broken but if you use it only once it's unbreakable and that's sometimes a hard concept for us to think about in in terms of modern cryptography where it's all about key sizes and key lengths and and really what's it take comp with computation with you know computer power to brute force a system but there is no brute force in a one-time pad
the algorithm as it were is very commonly and this is one that I used to use all the time this happens to be called a vinny a VIN yay was I guess some French mathematician I always said Visionnaire because I'm an ugly American that if you're French its vision a but it's basically the alphabet reversed in 26 different offsets written out in a complete table what this gives you then is the ability to it doesn't really matter you know whether it's row or column but find your your plaintext your message letter on one you know down one side if you will wait can I use the laser thing area say you're your plaintext letters down one side your
keys down the middle you line it up and find a third letter and that is basically the cipher the message the code that you'll send on I think I have an example here so a one-time pad literally was a pad of paper think of like a note pad or a you know a sticky pad notes it was typically sealed on all four sides with one corner left unglued so you could peel up a page at a time because it was very important to use at one time only so if you had a message that you wanted to encrypt you would write it out letter by letter so gosh that's really far away I'm gonna read it from here enemy
sighted on border stop stop is like Morse code for period end of the sentence attack at dawn stop and then a string of characters like X's just to let you know that the message over you can stop if you're on the other side decrypting you can stop now so you you use that Visionnaire Square as a technique to find the third letters your cypher you write them out and that's the message that you send now you notice I didn't start with the first what's called an octet I'm sorry not octet but the first five characters wasn't used that's your that's your code for which page to use if you're on the receiving end you look at the first
characters and you find the page that matches hopefully it's the one on the you know the top page but you know messages could be sent multiple times and conceivably be received in a different order so if you're on the receiving end you have to check that so if you do that you've got your own copy of the one time there's usually two in existence for you know end-to-end communications you write down your message and you simply reverse the process and you get back to the plain text message that's how one-time pads work the beauty of one-time pads from a cryptographic from an analysis perspective is you're taking the characteristics of the the underlying plaintext and you're eliminating it
there are no spikes there now that really stick out and there really is no way to guest letter for letter because any letter will work it'll always go back to something you can actually potentially decrypt this message to anything you want it to say because it works that way there is no way to get the one right answer so that's a little bit of background that's the kind of stuff that I was involved with so some tales about my time at NSA chapter one I started out in the end of 1986 about 30 years ago working for what was called the manual crypto systems branch within the defensive side of the house which was called information security or infoset
they hired me and decided to train me to be a crypt analyst because they were going through a review of all the paper systems that they had deployed over the years oh and in case you didn't know it NSA provided and provides all the crypto systems for the DoD for the military and and most of the government if you're dealing with classified information certain mail servers possibly accepted so in the early days I did cryptography that's the NSA building there to put things in context I started at the end of 1986 anybody know what that is it is the Enigma machine when I started working at NSA it was still considered a secret that the US
and the you know in in the UK and its allies had broken the cryptography of that system anybody want to guess why it was still being used in fact it was still being used I think I should look this up and actually have the answer it 88-89 is when it when it stopped being used it was being used by certain countries that maybe were considered adversarial to the US and its allies and as long as it was still being used it was a secret that we knew how to break the messages one of the very first jobs I did in this office was associated with the paper systems but the paper systems had been kind of neglected because from like
the the the late 60s or mid note the the Vietnam era if you will things like machine cryptography started becoming popular as anybody a veteran some of you might recognize some of these devices and I'm sorry if it brings back painful memories because I know these things were painful to use gosh I got a look at this I might have a picture of that or I might have opted out this is actually one of the early versions of an encrypted phone and it was actually a couple different devices starting with the phone which was kind of like a walkie talkie it had a little clicker on the side that she pushed to talk and then you had to
release to listen that's that's called half duplex it's one-way communication so you can't be talking at the same time you have to talk stop wait for the other person to respond and it was attached to a separate piece of equipment that was doing encryption of the signal using and that's what we considered machine cryptography this is a device that actually took analog took a voice and converted it to digital and and then did the encryption so on the other end the mission the device would take the digital signal signal decrypt it convert it back to an analog signal and you'd hear the voice again you can imagine this is Vietnam War era if anybody anybody want to admit to
having used it how did it sound
uh-huh yeah you would sound the voice all the voices you couldn't get you can really tell who you were talking to because it it all sounded like Donald Duck it was very kind of muted and crackly and just wearing and it didn't improve with other technology that used later on this is the radio the sink gars radio which is really just the phone set all these devices had to have key they had to have King information and that keying information was generated in these systems and the little things sticking out at the top was sort of like the key loader that you you would fill it with key and then plug it into these different devices and load
the key or inject the key so this was stuff that was happening sort of all around me I was working on the paper systems that were ignored and neglected because everybody was using this and they just assumed that paper was going away just as a real quick quick note and I know who this guy is Oliver North why do I have him in my talk anybody here ever a comic OD COMSEC a custodian yes this talk is for you I guess contact custodian all this keying information all these key equipments the one-time pads the paper all this kind of stuff had to be distributed securely to person control signing off on everything obviously the security of the one-time
pad relies on the fact that nobody steals it or copies it so it has to have absolute total control eyes on it everybody's keeping it locked up two people are trans you know signing for it and this was all done by something called a Conseco count so my office was responsible for the COMSEC account that would ship all the paper out and and different systems to different customers if you will well Mike I was the new member of the office I guess I got stuck with being the comms COMSEC custodian the one that was the keeper of this account and my account happened to be the one that was used it was before my time to send crypto equipment out to
alley north this guy from the White House to call said I need all these devices that he then used to do the stuff that he did so that's like my little you know connection dolly North for better for worse but you know all the crypto gear it had to be signed out the one-time pads the paper systems and another type of paper system called an authentication system all that kind of stuff had to be shipped out through the COMSEC account the the more modern version of crypto that I was familiar with when I started there was something called the stew three telephone so the key was actually that little key device on the side stuck
it in turn did it would load the key and you could use the phone in a secure manner and you still sounded like Donald Duck still half duplex I think there were three different models one I think was full duplex I forget which one it was but it was it was revolutionary because NSA made the design and then shipped it out to private contractors to actually build the devices so Motorola had one I want to say RCA had one and GE was the third I think and I think GE was the one that was full duplex so you could actually listen and hear inflections and get you know talk back and forth anyway I had a customer very very early on when
I started it and in this office that came to me and the customer happened to be people to do this the spooky kind of stuff for the DoD and they said you know we're using one-time pads we're talking to people that are our friends and people that we were talking to that are in places where it's very important to keep it secret that they're talking to us and we have to communicate with one-time pads but we've got this new thing sitting on our desk and is there any way we can use this to speed up the process because sometimes it would take them hours to do that encryption and decryption manually of the one-time pad messages so
I thought well gee that makes sense why not use it so I developed and became a project manager for what my knowledge is the first software based crypto system that was ever produced by NSA and all we did was write a program that would do this algorithm this encryption decryption process wrote it into a program I want to say it was turbo Pascal so I remember turbo Pascal and it was and and the magic of it was we took the one-time pad and put it on a floppy disk and we had to emulate a page of key we had to emulate the method of doing the encryption in the decryption and most importantly we had to emulate the
secure destruction of the page when it was done it actually had to be erased or deleted off the off the floppy disk so that it couldn't be accidentally reused I had to follow the specs that were written for Hardware I think there was a slide earlier I didn't point it out but I had a chief scientist that worked in my organization at the time I heard him say you know there's really no such thing as software there's only hardware NSA built little boxes you've seen pictures of him that did this crypto stuff and you would plug things like phones and radios into it and magic would happen and the signal would come out the other end and the reverse
process would happen so I had to write software design specs essentially that modeled what we were supposed to follow but from the perspective of software and and this system would totally not work today in our networked world but back then the desktops were stand-alones and so there was and it was in a it was in a locked room a protected area and so it was relatively safe to use for the people that were using it so the what we called the semi automated one-time pad half floppy disk and half paper it became so popular that I had another customer happened to be u.s. special forces they were involved in a process similar where they had communications
where they relied on one-time pads and that and they would talk to their deployed teams their a teams out in the field via one-time pads and instead of on there and using one-time pads they had actually one-time tapes and these tapes which were produced by NSA that emulated the one-time pad which was in the field were running were run in a series of machines similar to the one in the middle there that would take it and convert it and so you would type a message into a machine that would produce a tape and you'd have to feed that tape and the key tape into another machine that would do the algorithm and combine it that output was
then converted to an artificial language voice and was recorded on reel-to-reel tape and sent to another machine slapped on and then it was broadcast over entire hemispheres of the world and I couldn't find a picture of the base station that they'd been using but they had one that was basically took the entire back the the semi an entire truck and you know it was something similar to what you see in that picture to the right there was lots and lots of radio equipment reel-to-reel tape recorders and they actually had a second truck that was just the power plant the the generators that and backup batteries and things like that to keep it running it was supposed to be mobile
but it turned out when they first deployed it and set it up it took so long and it was so sensitive because it was radios and antennas they found out that they really couldn't move it so they wanted to try it they were involved in a process of modernizing and they wanted to make it truly mobile and they were of course using this one-time pad with the Visionaire square and as a side light when I was working with them I had I did not I was not familiar and I wasn't practiced at doing the one-time pad algorithm so I had just been through the crypto classes learning about cipher wheels and I thought gee there ought to
be a way to make a cipher wheel that does the Visionaire squeen Visionnaire square so I came up and that is this with a prototype of what I called the Visionnaire wheel and I just did it for myself just to go out and as I was working with them you know have a little bit of an aid because it turns out that the Visionnaire square and I should I really should have a picture of the back of this this is an actual page that was the first page of a one-time pad that is the Visionnaire square but on the back it has a list of all the unique three-letter combinations that the Visionnaire square produces this is like
123 of them the Special Forces guys would memorize these so they could do the encryption and decryption in there I was a lot slower so I came up with the wheel first one I made was with graph paper and I used rubber cement sand buddy remember rubber cement I haven't seen it in probably 15 years glued it to some cardboard cut it out stuck it together took it to wherever I was going and I was working with this you know group of communications officers and turned my back on him turned around and they'd stolen it from me and I made a few more the next time I went out and they kept stealing them from me so
finally I said would you like these things and these things are really cool so this is a prototype we made like 15,000 of them and ship them out to Special Forces to this day whenever I run into somebody that's X Special Forces I ask him if they remember this thing somebody told me years ago that they they they certainly remembered it and they called it the whizz wheel or the wizzy wheel so I usually say hey do you remember a wizzy will and they're like yeah I remember that and I said oh I'm the guy that invented it and usually then they buy me a drink and then we talk war stories and and all sorts of
Special Forces type stuff which is kind of fun so anyway that's something that I did early on in my career there's the prototype here you're welcome to take a look at it afterwards but don't be like the Special Forces and try to walk away with it anyway I was competing apparently and I didn't know this for about a year with literally the office right next to me they were trying to do a machine version of and this was called a kale 43 the little bar that you can sort of see in the middle it's like a little LED screen and you would you would type in characters and they'd pop up with the little red LED lights across
the screen and it may be gosh maybe it was 30 characters wide but it was it was designed to do encryption but she had to type the message in and then hit enter and it would do the encryption automatically and send it off and then in the reverse it would come back and it would automatically do the decryption and you could read her across the screen what I was working on was taking instead of one time tape you guessed it we put the key on a floppy disk and put most of that operation into a series of laptop computers that took a to basically two semi-trucks worth of gear and reduced it I think there's seventeen transit cases
those cases are about two foot by two foot square that reduced the whole base station to that primarily because they started using computerized technologies laptops and they replaced the recording equipment that had the one time tape with a floppy disk so it was didn't seem like a big deal to me but it was revolutionary and and in as far as I know they used it for a while so that was the first chapter in my life at NSA after a couple years in that office I moved on to become make what was called a crypt analysis intern and if they had intern programs where you could get accelerated learning and trading and diversity and and it was a it was it was
kind of similar to their like this at you the CISSP you kind of have to have it to advance you know it's one of those thresholds that you don't get beyond unless you do this compulsory thing so I ended up being an intern so I went over to the other side of the house the operations side which is what most people are familiar with and I happen to be there during this little skirmish and in the desert that they called the first Gulf War so I was there during that time which was kind of cool because it was it was you know I was a young kid and naive and I thought were was a thing of the
past and you know all the stuff that NSA did kind of went into production and we were doing it for real at that time and we actually did a really good job of it shortly after that and if you can find this article in Wired I think it came out in 2013 it says you know there was a group of cryptanalysis interns mmm where have you heard that before went on a field trip to CIA found this statue in the courtyard has anybody heard of or seen the statute the crypto statue and you know fast forward I was one of those interns that's a copy of a printout of the the content of the statue which is
the crypto it's just a portion of it but you can see the date stamp there it's 1991 but we were kind of mad that in this and it's all captured in this wired article it's actually very accurate we were kind of mad that this statue was at CIA because we were NSA were the creepies what CIA got to do with it so we took it upon ourselves to try to break the thing well this article came out a few months after another article that said some guy at CIA had solved the puzzle you know like in in the late 90s or something like that and you know before anybody else had and then this follow-up
article came out and said oh we found out that NSA solved it years before so yeah that's the guy from CIA ever did so interesting reading if you want to find it online but I was one of those interns I was one of the people that was kind of offended and we were like finding scraps of paper and pencil and everybody took a quadrant and wrote the stuff down and we took it back and if you're interested there's four messages in the statue three of the messages have been solved the fourth one has never been solved and what was described to us was it's in a courtyard where there's different statuary and simba symbols and there's
supposed to be this whole big overarching message of the whole courtyard the whole thing was designed by this artist that thought it would be cool to put this secret code in and he's given a couple clues I think he just put out another clue and within the last couple months because he's getting older and he would kind of like to see it solved before he dies again so if you're interested it's still out there the fourth the fourth the fourth message has yet to be solved to my knowledge nobody has solved the solved it part of the problem is is so short you know all the frequency analysis and stuff is only so good and it's and it works better the
more data you have obviously so take a stab at it one of the things I had to do was write a paper doing a cryptographic attack I actually tried to look at the Park Hill and come up with you know is it still secure even after all these years of use so I had to do a technical paper that wrote a wrote about my analysis of the Park Hill and I became certified as a crypt analyst it's my one industry certification if you will that I hold to this day my last tour was actually back on the InfoSec side of the house in an office called fielded systems evaluations where we were looking at systems that we produce because turns
out the way NSA does a lot of what it does is relies on people and see if this sounds familiar and applies to the modern world people not changing default settings people finding shortcuts people not following the instructions following workarounds basically you know one time key being used for a week or a month you know just basically not following the directions user error you know we just saw somebody decided gee if we do that to them how do we know they're not doing it to us we produce these great systems but how do we know our people that you know radio operators in the military tend to be 1819 years old and they're trying to get the
message across and trying to get their job done and you know lo and behold people find shortcuts and workarounds people don't follow the instructions so we had a whole office that evaluated how our systems were used in the field and I was there about the time this whole internet thing was happening in the World Wide Web the first browser came out so we had a division called networked systems that very quickly became focused on the internet so they formed what was called the systems and network attack center I became a part of that we're supposed to be a worldwide center of excellence smarter than everybody else have more resources than everybody else and was going to find all the vulnerabilities
out there before anybody else and so on and so forth got into penetration testing vulnerability assessment red teaming and we actually wrote a paper a group of us that basically was a paper talking about how to break into our own network and we had an award for it but we had to split it four ways so it wasn't much has anybody heard of this book came out earlier this year dark territory there's a chapter four titled eligible receiver one of my buddies Senate sent a picture of this a couple months ago when he was reading the book there's a section in there I can read it to you I'll let you read it but you know blah blah blah NSA had a
red team worked up at fan X and they did their most sensitive work in the pit this is the fan X complex up near BWI Airport the pit was right there I was part of the pit the pit was my office the guys that wrote that paper we worked in this office called the pit how it turned into this legend of the very super secret chamber I don't know but I'll live with it it makes us famous for a few minutes but more on that later we're talking crypto not pen testing today so I might have a talk on that next year so how does this all apply to modern cryptography you know I'm still
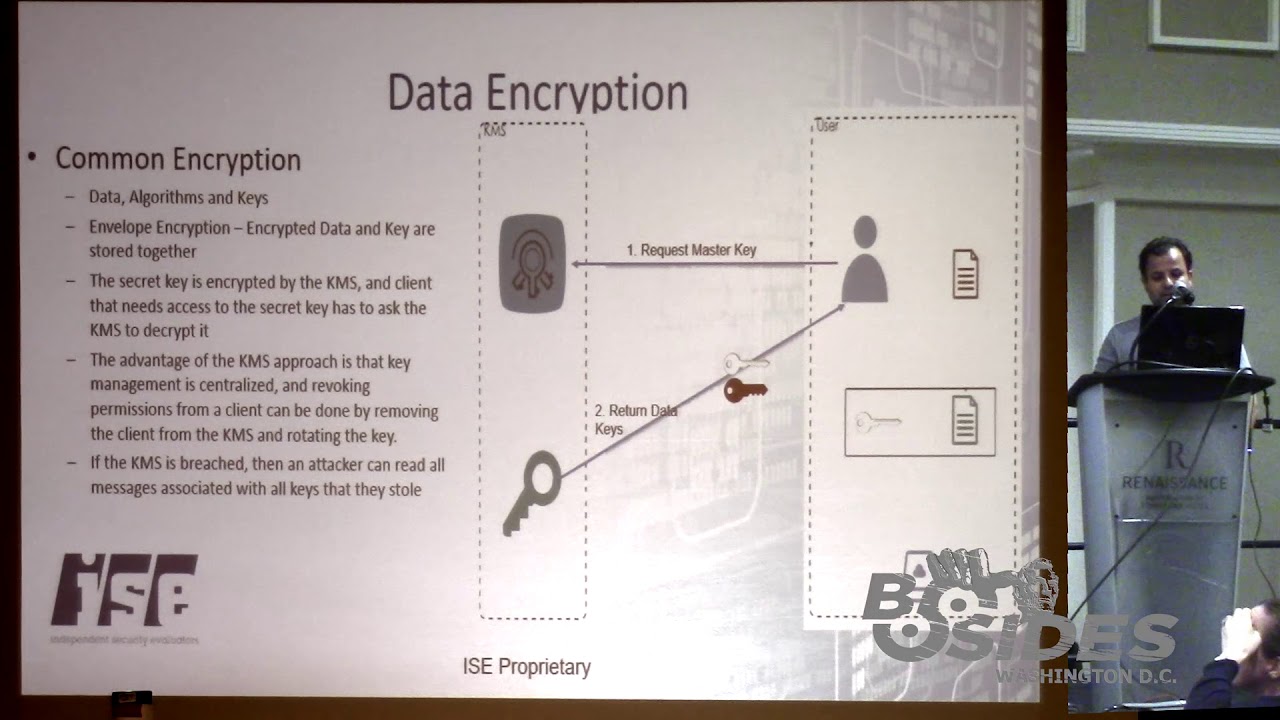
interested in crypto because crypto has certainly changed in terms of computers you know obviously there's crypto in the internet you know certainly web traffic is probably the most common thing VPN traffic private connections you know I used to have fun be in the early days trying to crack passwords because there was a lot of people that tried to make their own random password generators that never were and they thought that there are really cool ways of producing really good passwords they never were crypto is really hard to do and hard to do it well you know the application of cryptography today hashing functions obviously passwords file integrity web traffic and so on and so forth and
this new thing that came along public key cryptography which has really enabled the web to do what it does symmetric key is really like a one-time pad you you only do it in one direction and in theory both sides have the same key so the key that's used to encrypt is also the key that's used to decrypt and the big difference then with asymmetric cryptography not getting into all the science and math about it but the big thing is you've got two different sets of keys and they're and they're one-way only so you have a public key that everybody can have access to that does the encryption that can only be decrypted by the secret side and in fact
this is how Special Forces use their one-time pads they they carried two sets of one-time pads and they used them in one direction only so they essentially did public key cryptography with one-time pads they just didn't call it that back then there's there's exceptions to this but for the most part the way modern cryptography graphic systems are broken is by brute forcing you figuring out how many different combinations there are figuring out shortcuts figuring out ways to try all possibilities and the and relying on the probability of it doesn't take all the tries to get there that statistically you're gonna get the right guess at some point while you're trying them all so it's very math heavy
but there's other ways to break modern crypto and that's attacked the end point so sooner or later the message the data the traffic has got to be decrypted so you could try that in or it's got to be encrypted in the first place there's there's a before and after and those are those are attack targets so don't even touch the crypto just try to get to the data on either end or find out a way to steal the keys so it's all about the keys modern cryptography relies very much on key management key distribution schemes the keys having to be big enough that they can't be broken in a reasonable amount of time and so on and so forth
pause that's my real rough how it all ties on today any questions comments yes
these days a lot and I'm not a math person I used to work with math people and I can sort of understand what they're saying but it got beaten you know I like to I still like doing the puzzles in the paper but I'd say math is essential these days any other questions yes
I've given this talk twice and I had that question the first time no I can't well the other question was phrased differently is what algorithm was used and it wasn't there it was not machine generated man-made algorithm any type of math that created the random in there's one time death and I can't tell you honestly how they did it I mean I know how they did it I can't tell you how they did it where they might come after them but it's not machine generated which is a big difference in a lot of modern computer cryptographic systems that rely on a generated algorithm algorithmic ly based which is why math becomes important algorithms because if
you can duplicate it if you can recreate it if you can predict what the key is and any man-made key essentially if it's being created it can be recreated if you can figure out how to do it or steal the steal the algorithm and that type of thing which is interesting because when we were building crypto systems and even devices back in the day our basic assumption was the adversary knows everything about the system they've gotten the hold of a copy of the system whether it's hardware or software they've reverse engineered it they've got the schematics the designs they know everything about the system and we still have to make sure it's secure the way
you do that is you protect the key and you make sure that the key cannot be gained you know not be stolen it's got to be protected in distribution it can't be tampered with the device it can't be stolen electronically technically protect the key it's still a secure system whereas these days when you've got companies that are producing cryptographic systems they very much rely on will its proprietary we're not to tell you how we're doing it you know it's a secret it's a real different mindset in the commercial world these days and it drives an old-timer like me crazy because I'm like I want to know exactly how you've done it so there's a lot of cryptographic systems that are
out there especially in the PCI world in the payment space and and I have yet to see a company that's producing any of those systems I won't name names that are upfront with ya this is how we're doing it and we've had it tested and we've had it verified by a third party and they've looked at our Nath and they've done all the testing and they say yeah it's good as far as I'm concerned it's not good until it may be the best thing around but until they have some sort of in what we used to call the independent verification and validation have somebody look at it and put you through the paces and test it
and see yeah you're good that's that's not done a lot today other questions yes sir
not a whole lot because I was in I was in the paper shop the manual shop most of what I knew about from the machine systems and the voice systems was either I used them or like I was the custodian and had to send the key out for the stuff occasionally but I know I didn't do a whole lot with that sorry any other questions yes sir
yes
Wow so historically it all used to be what we called the offense the operations side of the house trying to break crypto and message steal messages and communications of our adversaries when I was there there was this defensive side that was it was I think maybe 10 or 20% of the mission in terms of budget and people and things like that so it was always kind of an afterthought and we always had this collective feeling of being The Forgotten you know bastard stepchild everybody focused all the money and everything went to the operations the offensive side what's happened fast forward is I went to a happy hour or a couple months ago they have basically dissolved what it was the
defensive side of the house because of you know the changing climate that you know everything going to the internet and and networking and everything going cyber so they have now a Cyber Command but the mission is sort of blended into one so that they finally just just dissolved what was the defensive side the InfoSec so we went to a happy hour to just kind of toast the death of our where we all used to work and so officially it's back to one mission now so was it political over the years always there was always budget battles and things like that there was a question up here yeah
subject for another talk maybe key management talk so my favorite
frankly I would start with the history you know because most of the principles like if you've had to do the CISSP exam and have to read the chapters on the deal with cryptography they talk a lot about key management and they've got a lot of classical terminology and phrases and methods and and pretty much they're all taken from what used to be done as a manual method and applying the principles into the electronic world so it might be over simplistic and maybe it's because I'm a chroma Jian but starting with the foundation of where we've come from and what are the principles of separation the principles of split key split knowledge dual control all those types of things and
then extending it into the electronic world how do you do that electronically and do it well I think that's a good place to start I have no idea how we're doing on times you guys will throw something at me or hit the sticks more questions but we're good yes sir
of NIST [Applause] so that other talk that I haven't given that I just gave you a teaser for I could talk more about NIST NIST historically at least when I was there 20 years ago was responsible for the unclassified world and obviously they put out the standards and things like that but you know there were some pretty clear lines of separation back in those days the classified networks the classified world and the unclassified world within the government within the DoD civil agencies and so on and so forth so NIST had the purview for the unclassified world and in theory they did what we did and to say more than that I'd probably piss people off from
this and I'm sure it's evolved but they've today they are sort of the standards body and you know the industry follows them or doesn't depending on who you talk to you it's not a good answer probably but it's a whole another talk time's up okay thank you all very much and again and I'll bring this stuff to the back maybe